Advanced Security Anaytics Module (ASAM)
NetFlow Analyzer's ASAM module offers actionable intelligence to detect a broad spectrum of external and internal security threats as well as a continuous overall assessment of network security. With flow-based security analytics and anomaly detection, you can identify the top offenders and targets for an attack by its IP address. ASAM displays a list of grouped threats/anomalies as problems and further categorize them into four major problem classes - Bad Src-Dst, DDoS, Suspect Flows and Scan/Probes. ASAM has predefined the threshold for every problem class and its classification. It is possible to edit thresholds for each problem type from Settings.
Please refer the below link to enable data collection for ASAM in NetFlow Analyzer:
https://www.manageengine.com/products/netflow/help/how-to-enable-advanced-security-analytics-and-customize-events.html#enableASAM
The Security Snapshot of ASAM displays a list of problems along with its offender and target count, severity and the time it has occurred. On further drill-down, it displays a list of individual events/anomalies, of a specific problem, with detailed information collation for closer investigation. No. of unique connections and IP addresses of top offenders and targets will provide a detailed view for forensics.
The table below lists the set of classes used for classifying problems with a brief description:
| Class Name | Description |
|---|---|
| Bad Src – Dst | Either the Src IP or the Dst IP of the flow is suspicious |
| Suspect Flows | Some attribute(s) other than Src IP and Dst IP of the flow is suspicious |
| DoS | Denial of Service Attack |
| Scans and Probes | Flows are sent to a specific host using multiple ports or to multiple hosts on a single port. |
Refer the link to view a list of anomalies detected by the advanced security analytics module:
https://www.manageengine.com/products/netflow/help/attacks.html
Manage Algorithm
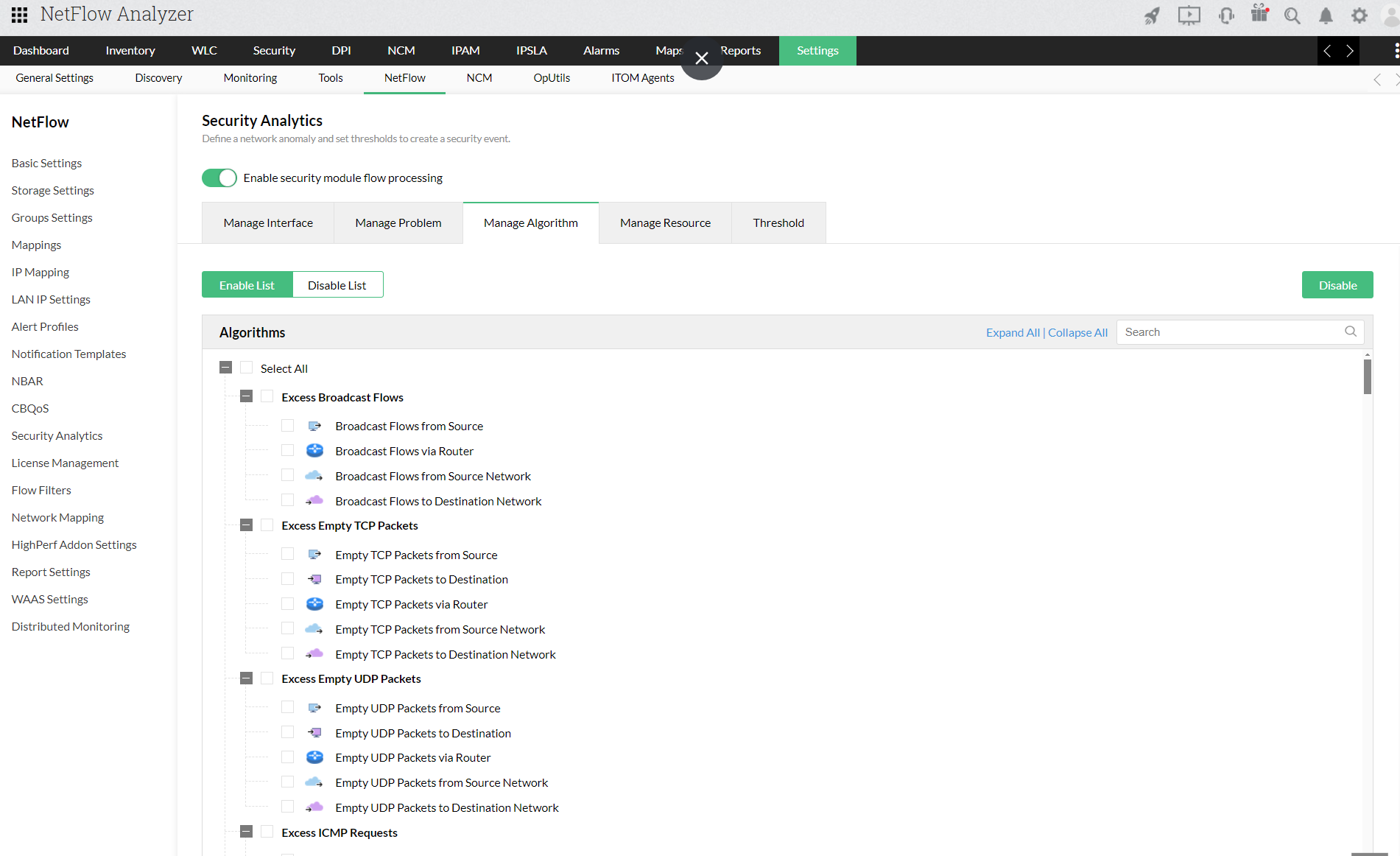
If you want to customize your problem events such as enable or disable unwanted problems under a particular class, refer the link below:
https://www.manageengine.com/products/netflow/help/how-to-enable-advanced-security-analytics-and-customize-events.html
If a specific algorithm is disabled, ASAM will not use the algorithm to generate events. For a base problem like TCP Syn Violations, you can manage three different algorithms like: TCP Syn Violations from Source (SourceAggregation), TCP Syn Violations to Destination (DestinationAggregation), TCP Syn Violations via router (RouterAggregation).
Threshold Settings
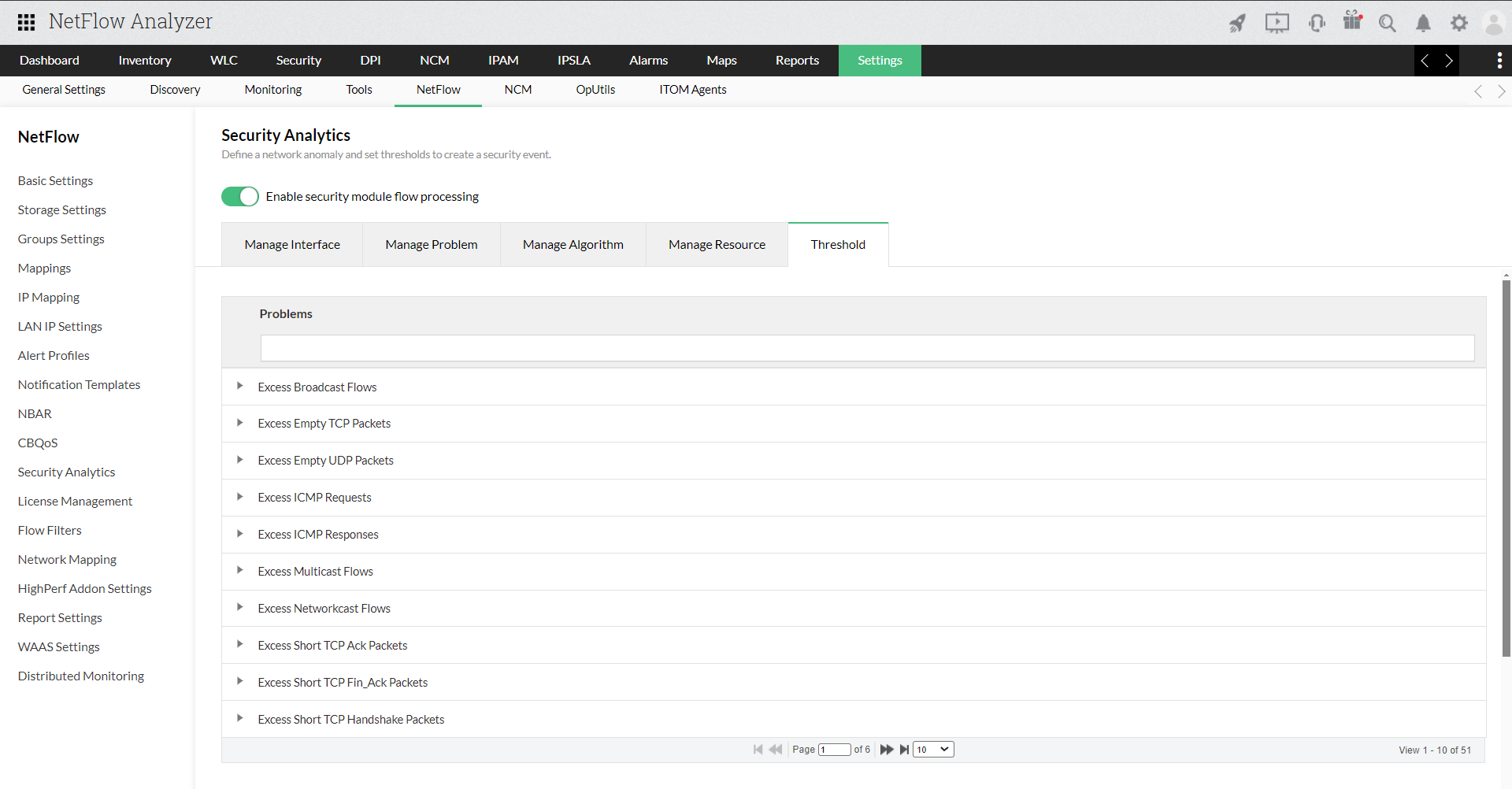
Allows you to set threshold values for an algorithm. Click "Threshold Settings" and set the upper threshold limit for an algorithm. You can also set the Heuristics threshold values for an algorithm using the Advanced Settings option. These updated threshold values are used to generate events.
Alert Profile
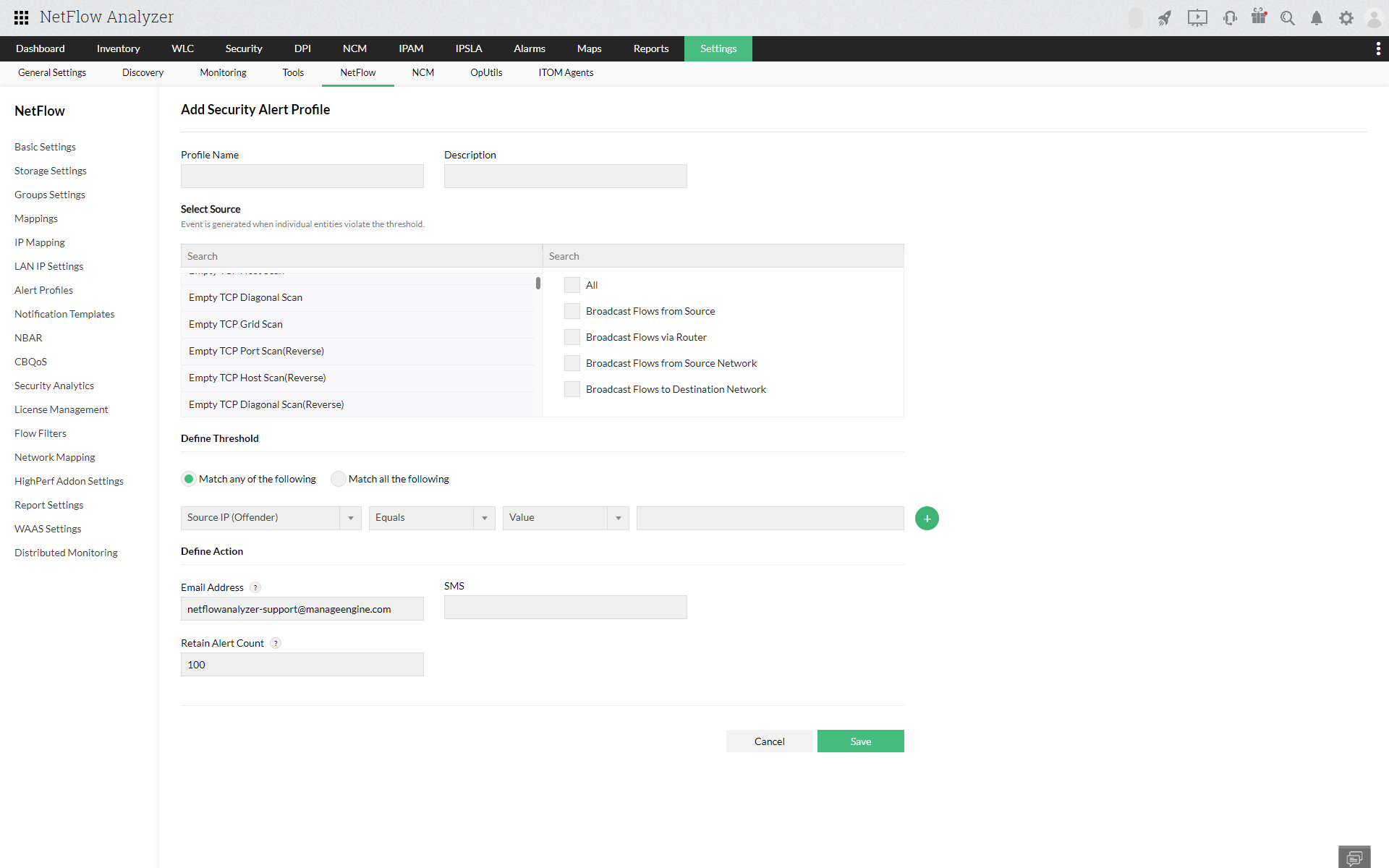
NetFlow Analyzer allows you to create alerts based on the ASAM security events that occur in the network. You can create Alerts based on the algorithm and the problem for the required criteria. Once the threshold is violated you will receive an alert and notification in real time. By default, there is no Alert profile created for ASAM. Click on Add button on the right top to create an Alert profile for ASAM.
Refer the steps below to create new alerts for ASAM:
Refer the steps below to create new alerts for ASAM: https://www.manageengine.com/products/netflow/help/how-to-enable-advanced-security-analytics-and-customize-events.html#alertProfileASAM