ADSelfService Plus in action
How to protect ePHI and meet HIPAA password requirements with ADSelfService Plus
On-premises applications | Cloud applications
According to a study by the Ponemon Institute, every healthcare record stolen in 2017 cost the victim organization $380 on average. The financial impact, loss of patients’ trust, and HIPAA violations that come with losing electronic protected health information (ePHI) all make healthcare organizations rethink their strategy on dealing with data security threats like weak passwords.
Ensure healthcare information security with strong password policies
It's common knowledge that most healthcare organizations rely heavily on passwords to secure access to their sensitive data, including ePHI. Hackers only need one compromised credential to get into an organization's network and wreak havoc. One challenge of HIPAA compliance is ensuring that doctors and other medical staff use strong passwords to secure their accounts. Organizations need an ePHI security solution that ensures data security by improving password complexity requirements.
How to protect ePHI and comply with HIPAA
Section § 164.308(a)(5)(ii)(D) of HIPAA mandates that admins enforce "procedures for creating, changing, and safeguarding passwords." The HIPAA security rule is vague, calls password management "addressable," and gives no specific details on password complexity, so we look to the Department of Health and Human Services Office for Civil Rights for guidance. They ensure that their employees' passwords:
- Include American Standard Code for Information Interchange (ASCII) characters.
- Be between eight and 64 characters.
- Not follow any particular pattern or be easy to guess (e.g. "1234567"). Learn more about weak passwords.
- Not be identical to a user’s 10 previous passwords (the password history rule).
Password Policy Enforcer
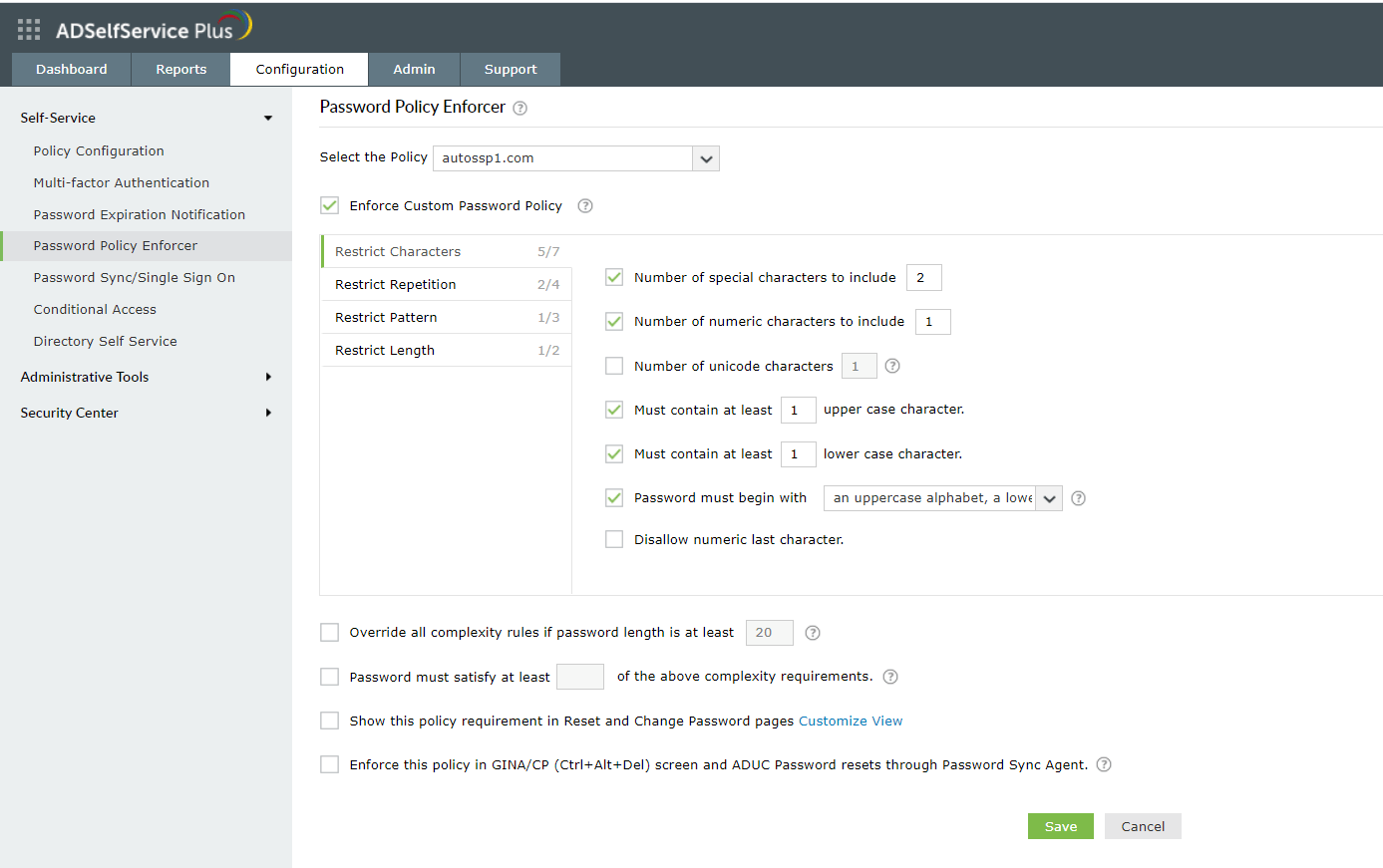
ADSelfService Plus, a password management solution, offers the Password Policy Enforcer that provides advanced password policy settings and helps ensure healthcare data security. Admins can create multiple custom password policies based on users’ privileges, and enforce these policies based on OUs and groups.
How to configure advanced password policy settings with ADSelfService Plus
- Log in to the ADSelfService Plus admin portal.
- Navigate to the Configuration tab. Under the Self-Service section, select the Password Policy Enforcer.
- Enable Enforce Custom Password Policy.
- In this section, the administrator can manage:
- Characters: Restrict the number of special characters, numbers, and Unicode characters that users can use.
- Repetition: Enforce a password history check during password reset, and restrict the consecutive repetition of a specific character from the username (e.g. “aaaaa” or “user01”).
- Patterns: Restrict keyboard sequences, dictionary words, and palindromes.
- Length: Specify the minimum and maximum password length.
- Admins can also enable users to bypass complexity requirements when the password length exceeds a predefined limit (say, 20 characters).
- Enter the number of policy settings the user’s password must comply with during self-service password reset and password change operations.
- Enforce the configured password policy settings during password resets from the ADUC console and the change password screen.
- To help users create passwords that comply with the enforced policy settings, admins can display the password policy requirement on the reset and change password pages.
Tip: Offer visual feedback on user password strength by employing the Password Strength Analyzer. To enable it, open the Configuration tab → Self-Service section → Policy Configuration. Click Advanced. In the window that opens, go the Reset & Unlock tab. Enable Password Strength Analyzer.
Highlights
-
1Ban common passwords
-
2Enforce your organization’s security stance
-
3Perform OU and group-based enforcement
-
4Help users set strong passwords
Ban common passwords:
Enforce a custom password policy with advanced password policy controls to ban common passwords, patterns like "@123", and more.
Enforce your organization’s security stance:
Apply a centralized password policy to both on-premises and cloud apps in your organization.
Perform OU and group-based enforcement:
Implement different levels of password controls to different sets of users.
Help users set strong passwords:
Display the enforced password rules on the password reset and change screens.
Comply with HIPAA password requirements. Protect ePHI from cyberattacks.
Get Your Free Trial Fully functional 30-day trial