Using PowerShell scripts, admins can check bad logon attempts by users and the resulting account lockouts. ADSelfService Plus, an AD self-service password management, MFA, and SSO solution, audits AD users' login attempts and authentication status. It also displays the list of users locked out of their domain accounts with its Locked Out Users Report. Here is a comparison between using PowerShell commands and ADSelfService Plus to obtain information on bad logon attempts and account lockouts.
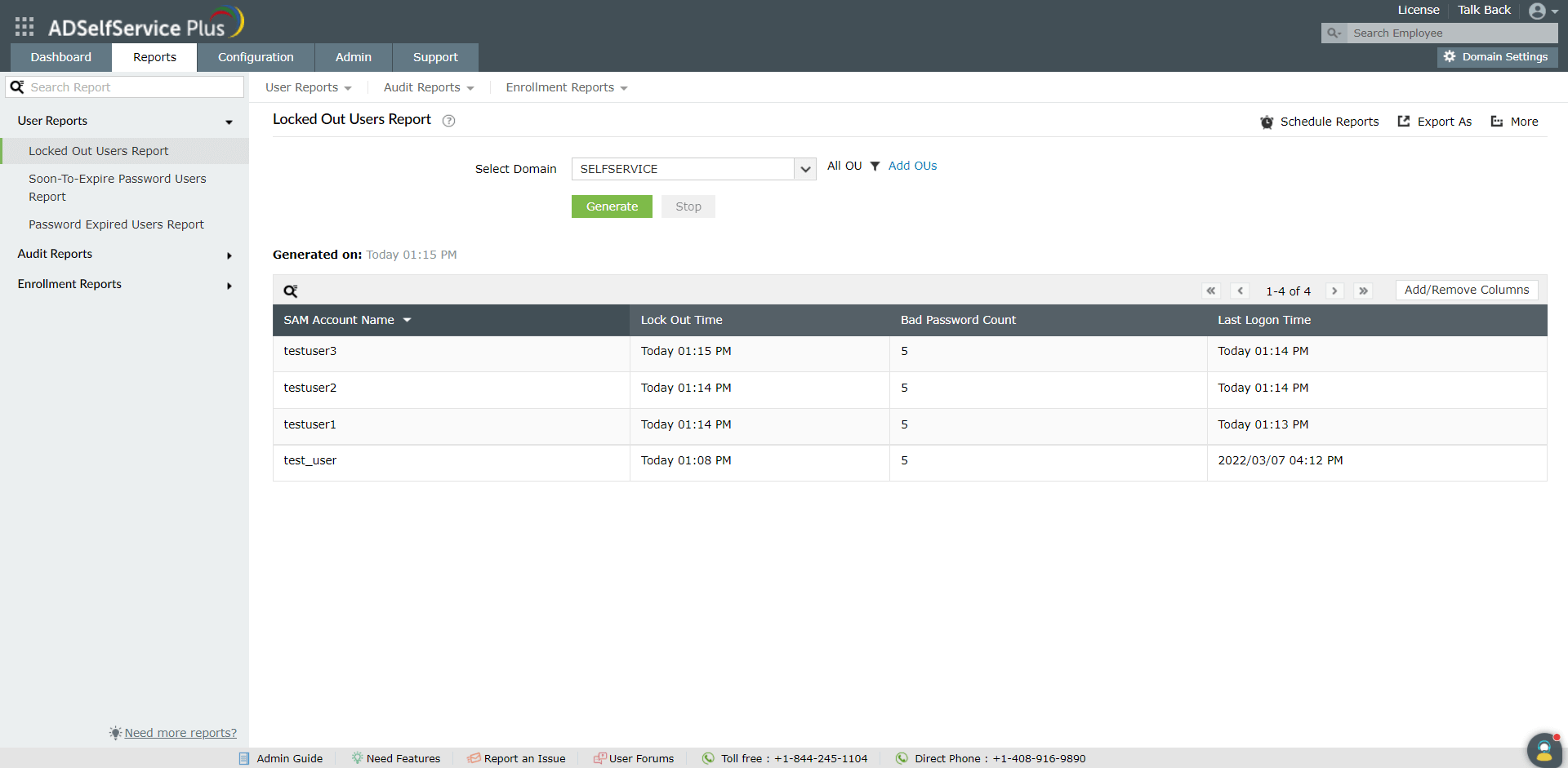
Run the following script to generate information on accounts locked out because of wrong password attempts:
Get-ADUser -Filter * -Properties AccountLockoutTime,LastBadPasswordAttempt,BadPwdCount,LockedOutTo access the Locked Out Users Report
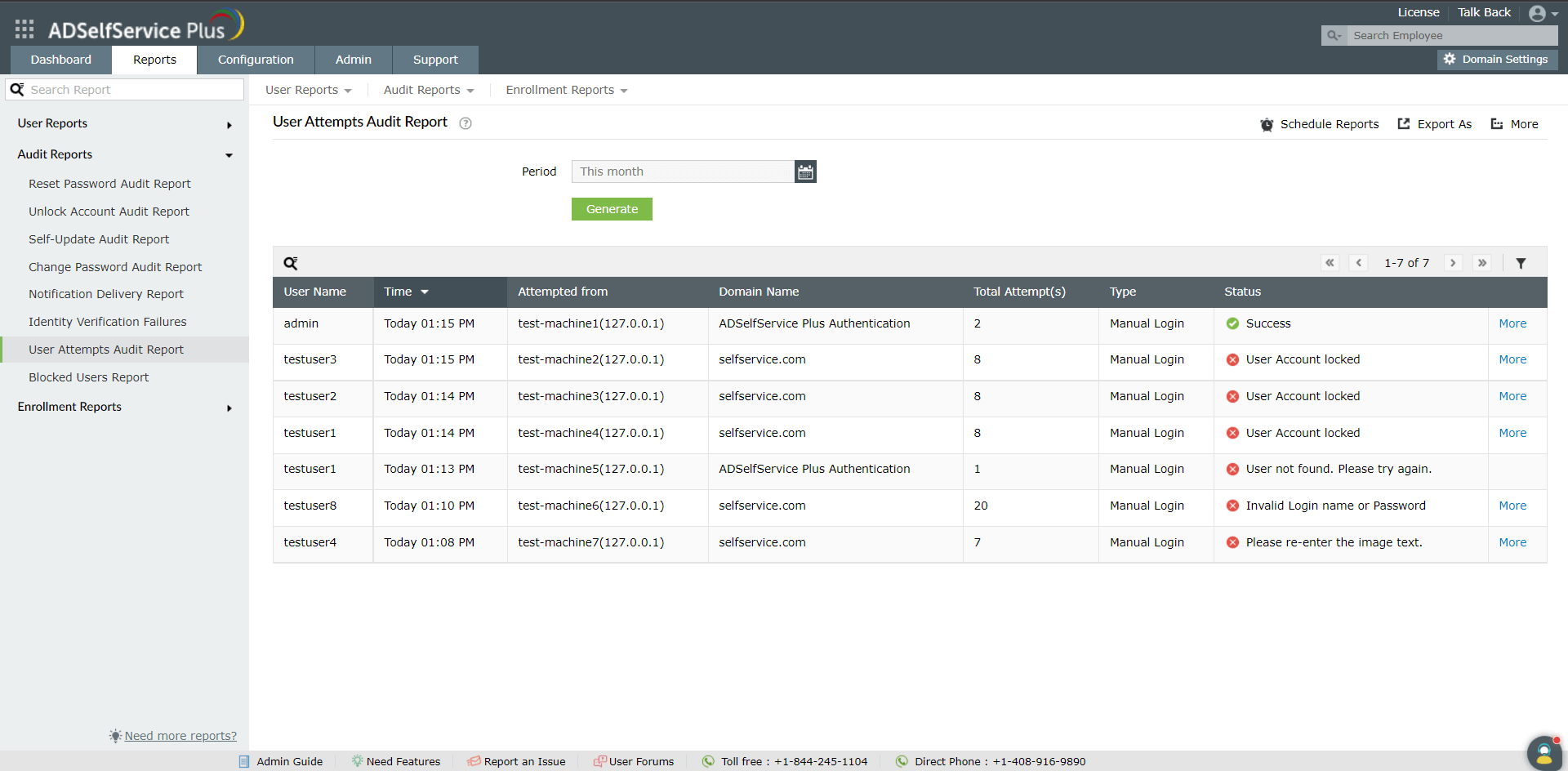
To access the User Attempts Audit Report
Report filtering and generation steps:
Run the script below to list the users with recent failed login attempts. This will list all accounts that are currently locked due to too many failed login attempts.
Search-ADAccount -LockedOut | Select-Object Name, SamAccountName, LockedOutUse event logs to find users with repeated incorrect passwords. Here, event ID 4625 indicates a failed login attempt. The output includes timestamps and detailed messages.
Get-WinEvent -LogName Security | Where-Object { $_.Id -eq 4625 } | Select-Object TimeCreated, MessageExport failed login attempts to a CSV file for auditing. The script below creates a CSV report of all failed login attempts.
$FailedLogins = Get-WinEvent -LogName Security | Where-Object { $_.Id -eq 4625 }
$FailedLogins | Select-Object TimeCreated, Message | Export-Csv -Path "C:\Reports\FailedLogins.csv" -NoTypeInformationSend an email alert if bad login attempts exceed a threshold. The script below will ensure IT security is alerted if more than 5 failed attempts occur within an hour.
$failedAttempts = (Get-WinEvent -LogName Security | Where-Object { $_.Id -eq 4625 }).Count
if ($failedAttempts -gt 5) {
Send-MailMessage -To "security@yourdomain.com" -From "admin@yourdomain.com" -Subject "Alert: Excessive Failed Login Attempts" -Body "More than 5 failed login attempts detected in the last hour."
}Use event logs to check failed login attempts in AD by running the script below:
Get-EventLog -LogName Security -InstanceId 4625Yes, you can track failed logins for a specific user by running the script below:
Get-EventLog -LogName Security -InstanceId 4625 | Where-Object {$_.Message -match "username"}Use Account Lockout Policy settings in AD to lock accounts after multiple failed attempts.