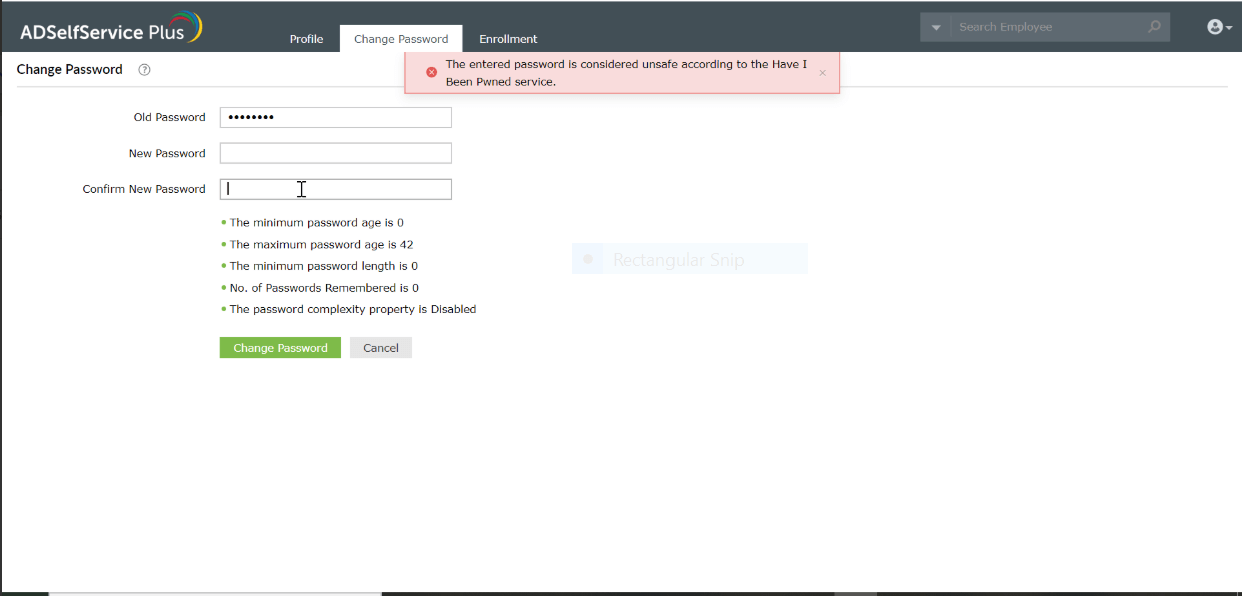
The PowerShell script given below will inform whether the password provided has been breached before during cyberattacks. ADSelfService Plus, an Active Directory self-service password management and single sign-on solution, offers an integration with the 'Have I Been Pwned?' service to inform users if the new password provided during the password reset or change has been breached before. Here is a comparison between identifying whether a password has been breached or not using PowerShell and ADSelfService Plus.
The Get-PwnedPassword PowerShell package, when installed and run, can identify if the password provided has been breached or not. Run the below script to install the Get-PwnedPassword package:
Install-Script -Name Get-PwnedPassword Once the package has been installed, run this script to determine if the password you provide has been breached or not.
Get-PwnedPassword <enter the password> 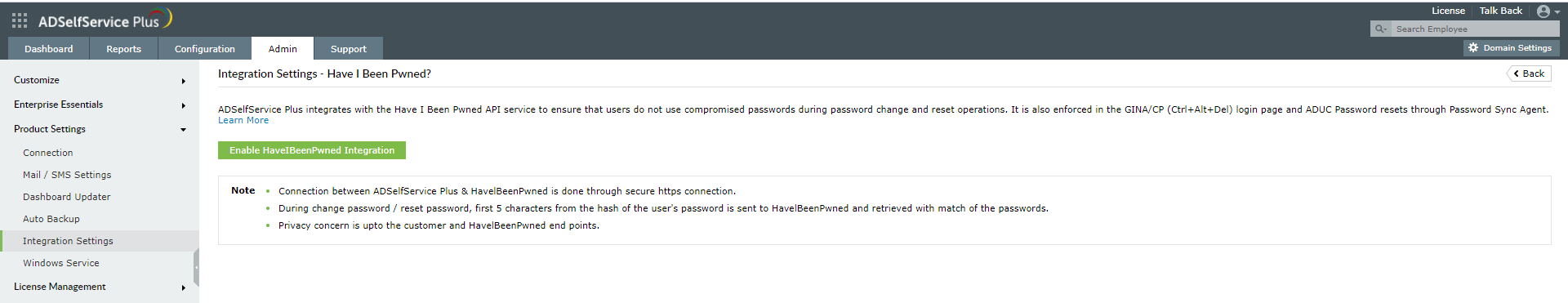
Ensure you have the necessary PowerShell module installed. The script below installs a module that checks passwords against breached databases.
Install-Module -Name HaveIBeenPwned -Scope CurrentUserTo protect privacy, convert the password into a SHA1 hash.
$Password = "UserPassword123!"
$PasswordHash = (ConvertTo-SecureString -AsPlainText $Password -Force) | Get-FileHash -Algorithm SHA1Query the Have I Been Pwned API. The script below returns the number of times the password has appeared in breaches.
$PwnedCount = Invoke-RestMethod -Uri "https://api.pwnedpasswords.com/range/$($PasswordHash.Substring(0,5))"If the password is found in the breach database, prompt a reset. The script below notifies users if their password is exposed.
if ($PwnedCount -gt 0) { Write-Host "Warning: This password has been compromised $PwnedCount times. Choose a new one!"
} else {
Write-Host "Password is safe."
}A password found in a data breach is considered "pwned" and should be changed.
Use the Have I Been Pwned API by running the script below:
Invoke-WebRequest -Uri "https://api.pwnedpasswords.com/range/5BAA6" -UseBasicParsingYes, use custom scripts to compare passwords against a breached password list and notify the users using breached passwords.