How to restore deleted Active Directory contacts
Last updated on:On this page
Active Directory (AD) computer objects represent workstations and servers within a network and are essential for authentication, Domain Name System (DNS) registration, and the application of Group Policies. When a computer object in AD is accidentally deleted, the trust relationship between the machine and the domain controller is severed, causing login failures and loss of access to network resources.
Deleted computer objects are not removed immediately from the directory. They are first moved to the Deleted Objects container. If the AD Recycle Bin is enabled, the object remains in a deleted state with all attributes intact, allowing full restoration. After the Deleted Objects lifetime, typically 180 days, it transitions to a recycled state where most attributes are removed. Once the Tombstone Lifetime expires, the object is permanently deleted during garbage collection. Efficiently restoring these objects with their SIDs and group memberships avoids the manual overhead of re-joining each machine to the domain.
This guide explains how to restore deleted AD computers using Active Directory Administrative Center (ADAC); PowerShell; and RecoveryManager Plus, a comprehensive AD backup and recovery tool.
- ADAC
- PowerShell
- RecoveryManager Plus
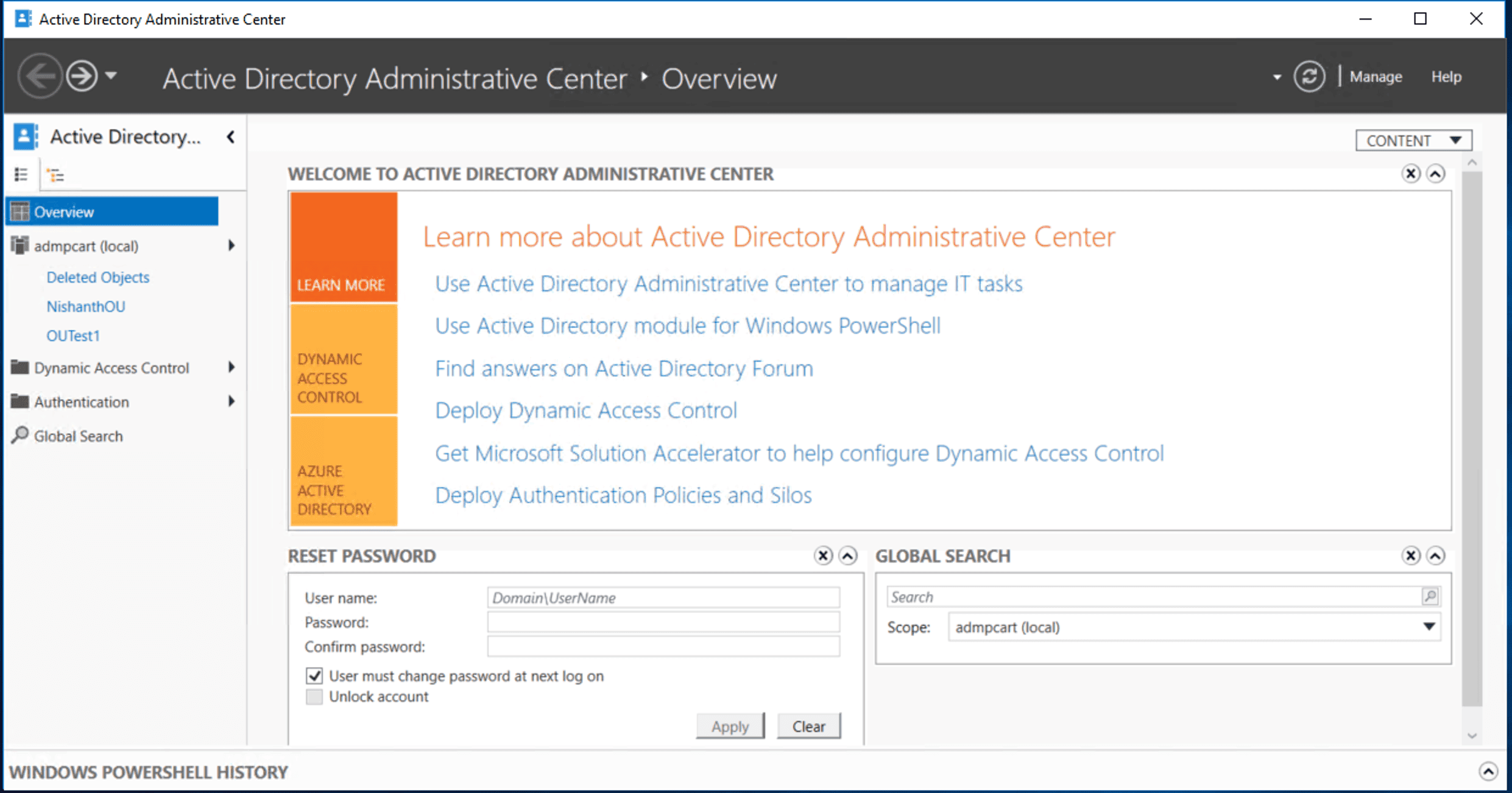
Method 1: Restore deleted AD computers using the ADAC
ADAC provides a graphical interface for locating and restoring a deleted computer object. Administrators can use this method if the Recycle Bin was enabled before the deletion.
Prerequisites
- The Recycle Bin must have been enabled prior to the deletion.
- You must have sufficient permissions to view and restore objects from the Deleted Objects container, such as Domain Admin or equivalent delegated permissions.
- If you're running ADAC on a client machine, Remote Server Administration Tools (RSAT) must be installed. To install RSAT on Windows 10 or Windows 11, use the script below:
Add-WindowsCapability -Online -Name Rsat.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0
Ensure the module is loaded using the script below:
Import-Module ActiveDirectory
This method applies to AD domains with a forest and domain functional level of Windows Server 2008 R2 or higher.
Steps
- Launch ADAC.
- On the left pane, select your domain and click the Deleted Objects container.
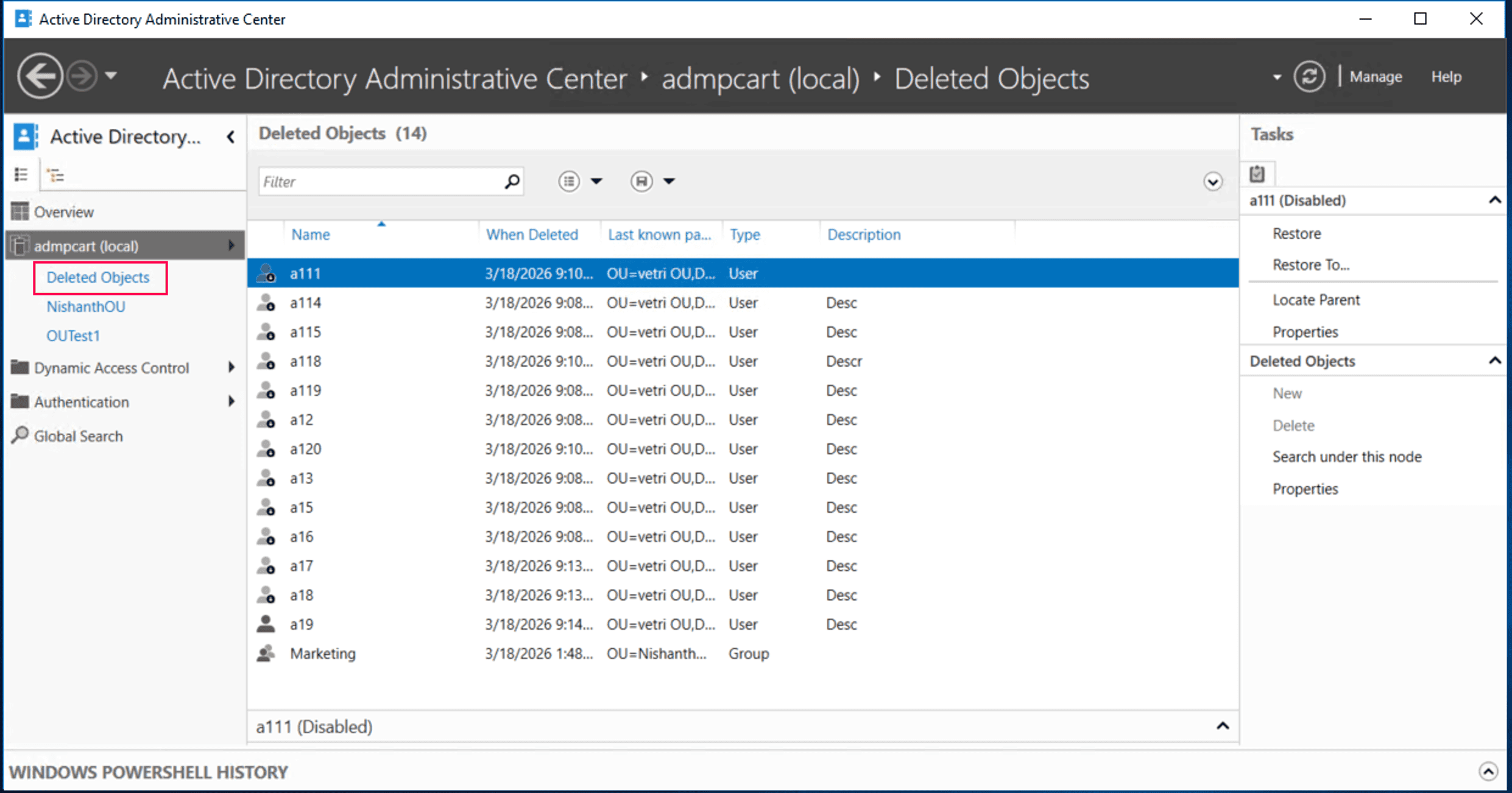
- Browse the list or use the search bar to locate the computer object.
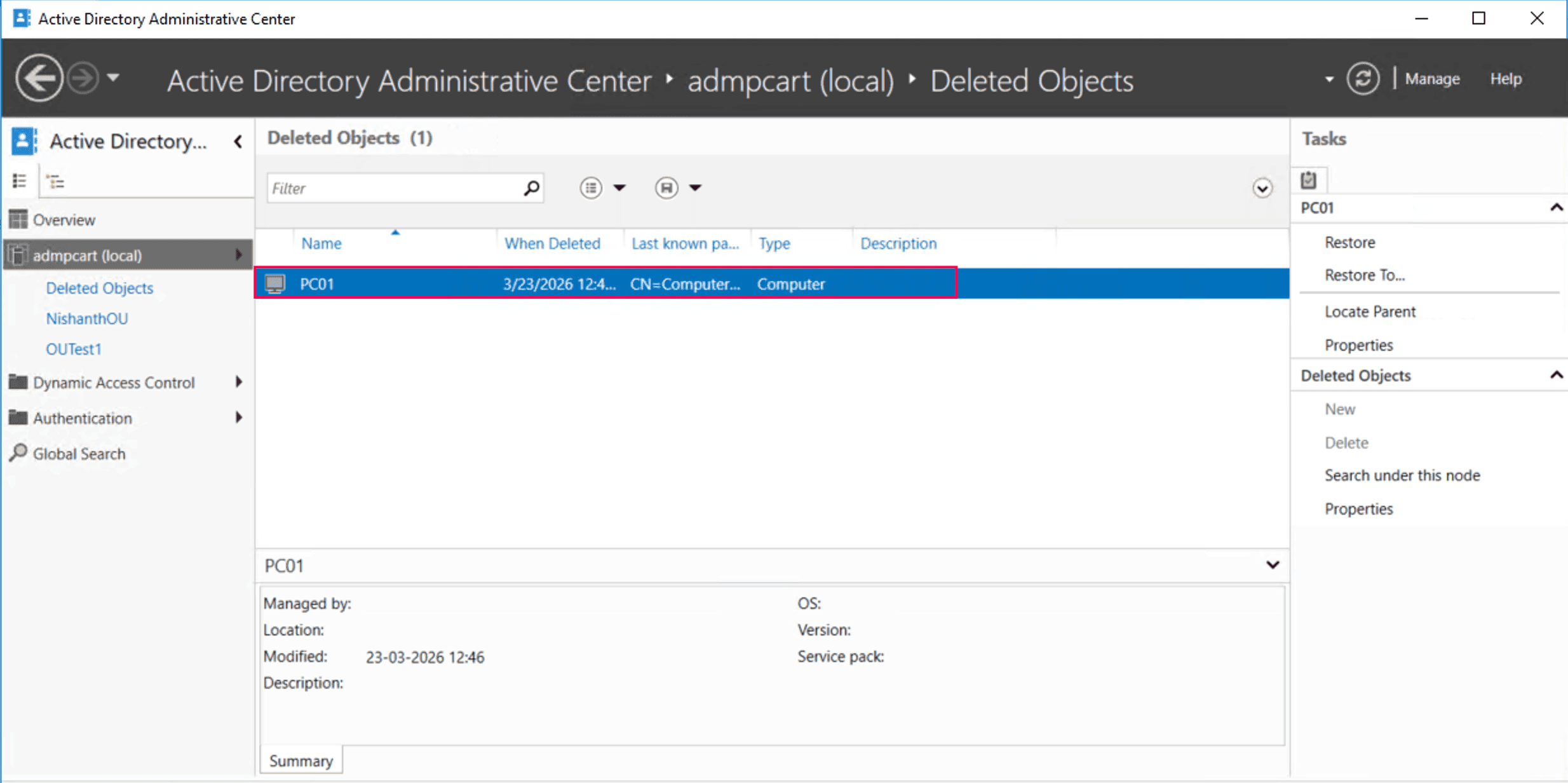
- Click Restore to return the computer object to its original OU, or click Restore To to specify a new location.
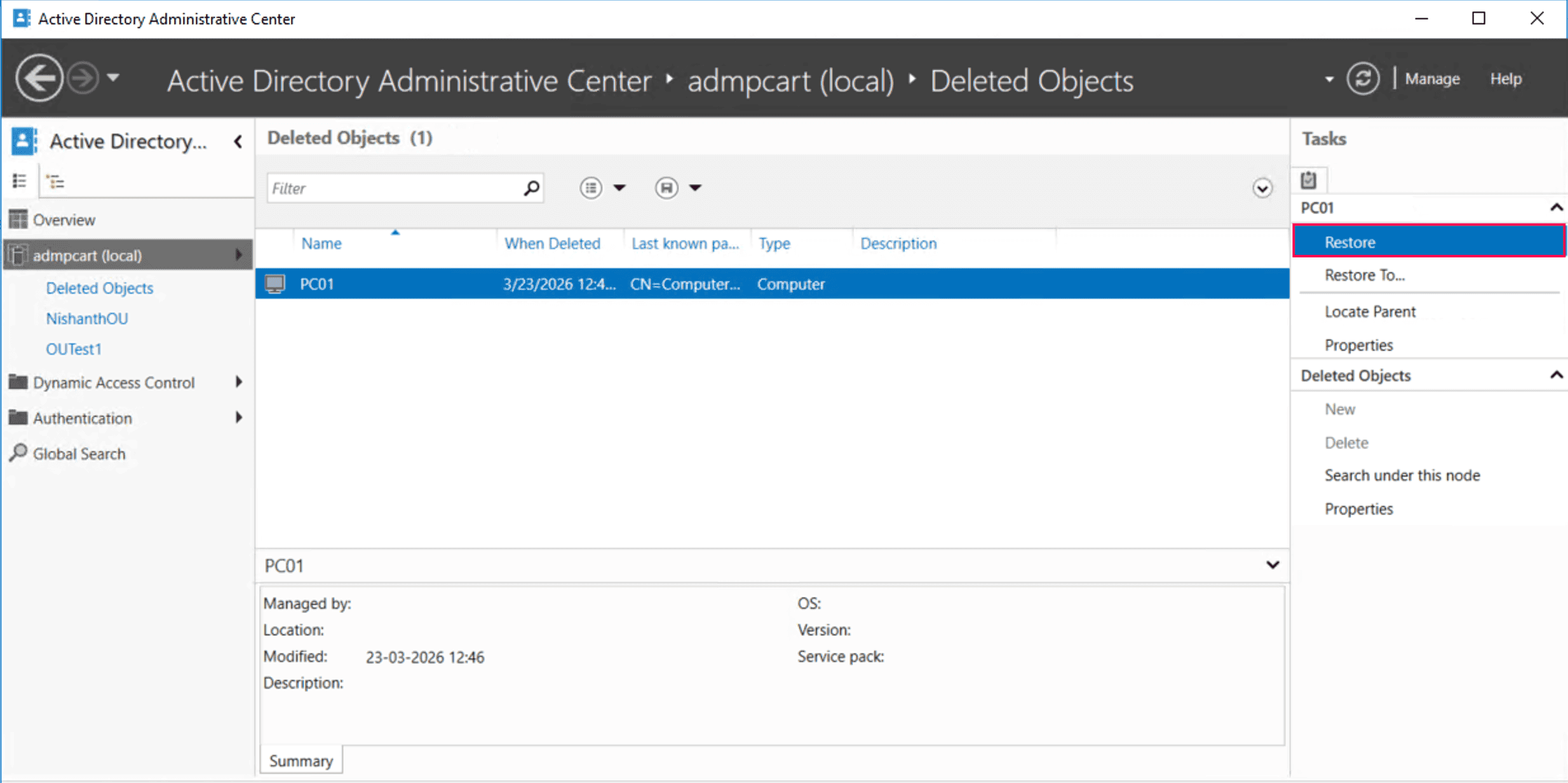
- Verify the object is visible in its target OU.
Limitations
- Requires the AD Recycle Bin to be enabled.
- You cannot restore objects after the Tombstone Lifetime expires.
- There is no preview of object attributes before restoration.
Method 2: Restore deleted AD computers using PowerShell
You can use PowerShell to restore deleted AD computers directly from the Deleted Objects container.
Prerequisites
- You must run PowerShell as an administrator with Domain Admin or delegated permissions.
- The AD PowerShell module must be installed. To install it on Windows 10 or Windows 11, run the script below:
Add-WindowsCapability -Online -Name Rsat.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0Ensure the module is loaded using the script below:
Import-Module ActiveDirectory
- Verify the Recycle Bin is enabled using the script below:
Get-ADOptionalFeature -Filter 'name -like "Recycle Bin Feature"' | Select-Object Name, EnabledScopes
If the EnabledScopes property is empty, the AD Recycle Bin is not enabled. If it is not enabled, deleted objects cannot be restored using this method and must be recovered using tombstone reanimation or authoritative restore approaches.
When the Recycle Bin is enabled
Restore the computer using the name
If you know the name of the deleted computer, run the following script:
Get-ADObject -Filter 'ObjectClass -eq "computer" -and Name -like "*PC01*"' -IncludeDeletedObjects | Restore-ADObject
Restore the computer using the GUID
To avoid errors with duplicate names, use the unique ObjectGUID:
Get-ADObject -Identity "a1b2c3d4-e5f6-7890-abcd-1234567890ef" -IncludeDeletedObjects | Restore-ADObject
Restore computers in bulk
Restore by deletion time:
To restore AD computers deleted within the last 24 hours:
$When = (Get-Date).AddDays(-1) Get-ADObject -Filter 'isDeleted -eq $true -and whenChanged -gt $When -and ObjectClass -eq "computer"' -IncludeDeletedObjects | Restore-ADObject
When the Recycle Bin is not enabled
When the AD Recycle Bin is not enabled, deleted computer objects are converted into tombstone objects. These objects retain only a minimal set of attributes, limiting the scope of recovery.
Tombstone reanimation using PowerShell can be performed, but it restores only the object. Group memberships are not preserved, and service principal name values are lost. In addition, DNS-related attributes often require manual reconfiguration after restoration.
Because of these limitations, Microsoft recommends performing an authoritative restore from a system state backup to fully recover the object with all its attributes. Tombstone reanimation should only be considered when an authoritative restore is not feasible.
Use this command to reanimate the computer:
Get-ADObject -SearchBase "CN=Deleted Objects,DC=domain,DC=com" -Filter 'Name -like "*PC01*"' -IncludeDeletedObjects | Restore-ADObject
Supported parameters
| Parameter | Description |
|---|---|
| -Filter | Specifies a query string to identify the specific object to retrieve. |
| -IncludeDeletedObjects | Searches the Deleted Objects container, which is hidden by default. |
| -SearchBase | Specifies the distinguished name of the container to search within. |
| -eq | Represents a logical operator standing for equal to. |
| -gt | Represents a logical operator standing for greater than, often used for timestamps. |
| ObjectGUID | Specifies the unique 128-bit identifier assigned to an AD object that never changes. |
| isDeleted | Represents a Boolean attribute that marks whether an object has been moved to the Deleted Objects container. |
Limitations
- This requires scripting knowledge.
- Group memberships must be manually rebuilt if the Recycle Bin is disabled.
- You cannot restore computers if the parent OU is deleted.
- There is a risk of restoring the wrong objects due to filter errors or typos.
- Bulk restore operations can lead to performance lags.
Method 3: Restore deleted AD computers using RecoveryManager Plus
Restoring deleted AD computers using native tools like ADAC or PowerShell can be complex and time-consuming. These methods require manual validation and scripting and do not allow you to preview objects before restoration.
ManageEngine RecoveryManager Plus is a comprehensive AD backup and recovery solution designed to eliminate these complexities. It allows administrators to recover objects efficiently with point-in-time and attribute-level restoration while providing clear visibility into all changes.
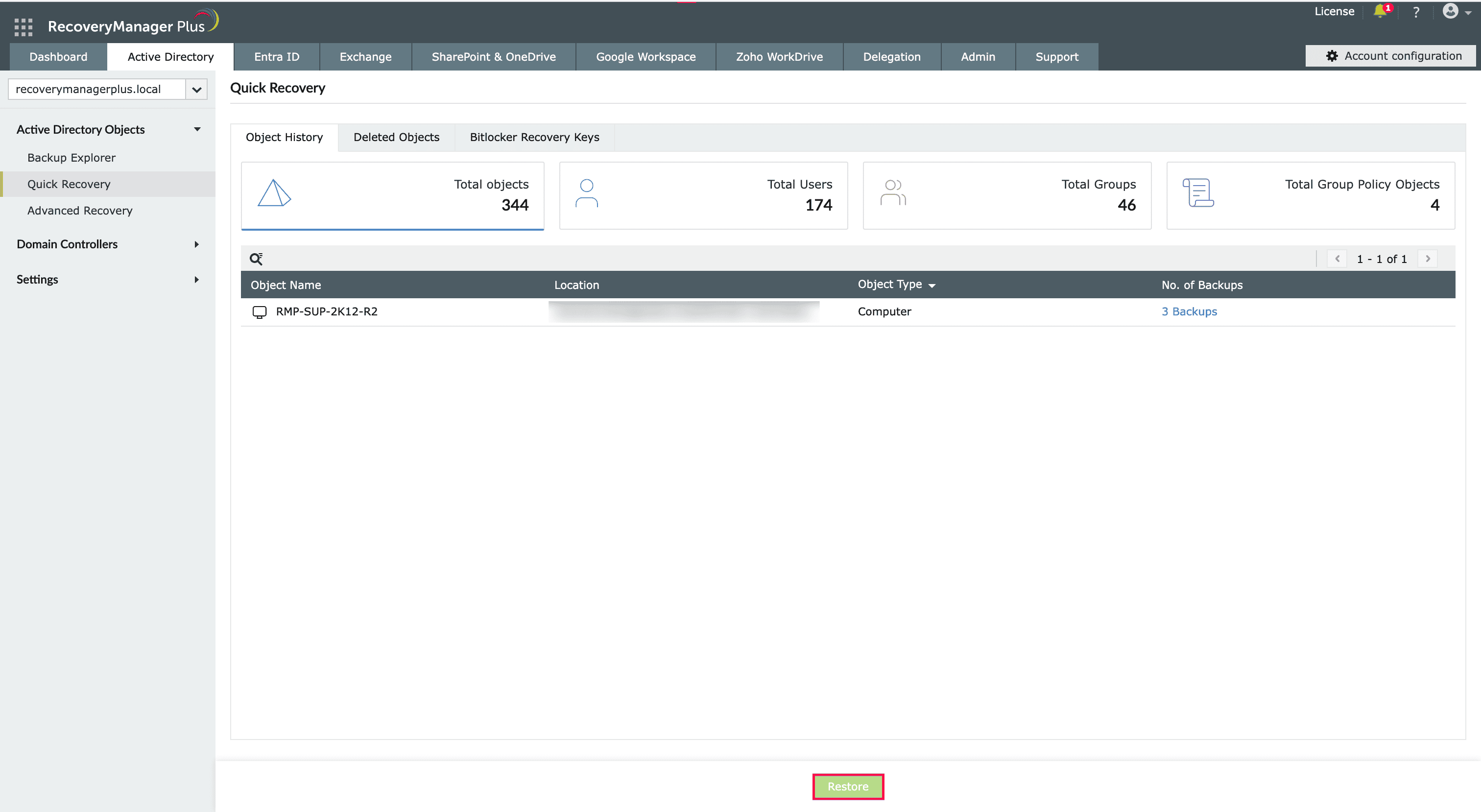
- In RecoveryManager Plus, navigate to Active Directory > Active Directory Objects > Quick Recovery > Deleted Objects.
- Select the computer you wish to restore and click Restore.
Why choose RecoveryManager Plus to recover deleted AD computers?
Native tools and PowerShell scripts that recover deleted AD computer objects have significant limitations. They require complex scripting for bulk recovery, provide no visibility into attribute changes before restoration, and may fail due to tombstone data loss or Recycle Bin dependencies.
ManageEngine RecoveryManager Plus overcomes these challenges by providing an intuitive web-based interface to back up and restore deleted computer objects. Administrators can restore data reliably, bypassing the limitations of the Recycle Bin and tombstone expiration.
Key features of RecoveryManager Plus include:
Domain controller backup
Back up domain controllers and restore them instantly in the event of a disaster.
Automated backups
Eliminate manual effort with scheduled backups that capture every change in your AD environment.
Granular restoration
Restore the entire domain, specific objects, or only the modified attributes.
Change tracking
Monitor changes made to AD objects and undo them instantly from a single dashboard.
Rollback
Roll back a computer object to any previous backed-up version, ensuring all attributes are intact.
Best practices for AD recovery
Follow these best practices to strengthen your AD recovery strategy and ensure deleted objects can be restored efficiently when needed.
Perform regular backups
Schedule frequent AD backups based on your organization's recovery point objective to ensure computers can be restored to their latest versions when required.
Use the 3-2-1 backup method
Maintain three backup copies, store them in two different storage types, and keep one copy off-site or isolated.
Implement least-privilege access
Ensure that only a limited number of administrators have the permissions required to delete objects.
Monitor critical OUs
Enable Protect object from accidental deletion on all high-privilege AD computers to prevent unauthorized deletion.
Perform testing regularly
Periodically test your backup and recovery processes to ensure they work as expected.
Frequently asked questions
No, you do not need to rejoin the machine if the computer object is restored within the password validity period and the secure channel remains intact. If the trust relationship is broken, you will need to reset the account or rejoin the machine.
If the computer object is restored within the default 30-day machine account password interval, the secure channel is usually preserved. If the trust relationship is broken, use Reset-ComputerMachinePassword in PowerShell to re-synchronize with the domain controller.

