- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Automated incident response using incident workflows
When it comes to network security, organizations are engaged in a constant cycle of security incident detection, management, and response. A typical organization can encounter hundreds of incidents a day, and new types of attacks are evolving all the time. This makes incident response challenging, as you have to ensure all incidents are addressed while minimizing the damage to your organization.
Developing a comprehensive incident response system may seem like a challenge, but there's an easy way to tackle it; you can automate incident workflows. ManageEngine's EventLog Analyzer offers a complete security package with its vast range of features including advanced incident detection, incident management, and automated incident response using workflows.
Incident workflows in EventLog Analyzer
An incident workflow outlines the sequence of steps to be taken following a security incident. EventLog Analyzer enables you to define and associate incident workflows with security alerts; these workflows are automatically executed when alerts are triggered. By automating standard response measures through these workflows, you save a great deal of time and effort while also minimizing or eliminating potential damage.
Predefined incident workflows
EventLog Analyzer provides multiple built-in workflows for common response steps like disabling compromised computers and locking hacked or malicious users' accounts. To implement these, select the pre-built workflows when setting up security alerts in the product.
Custom workflow builder
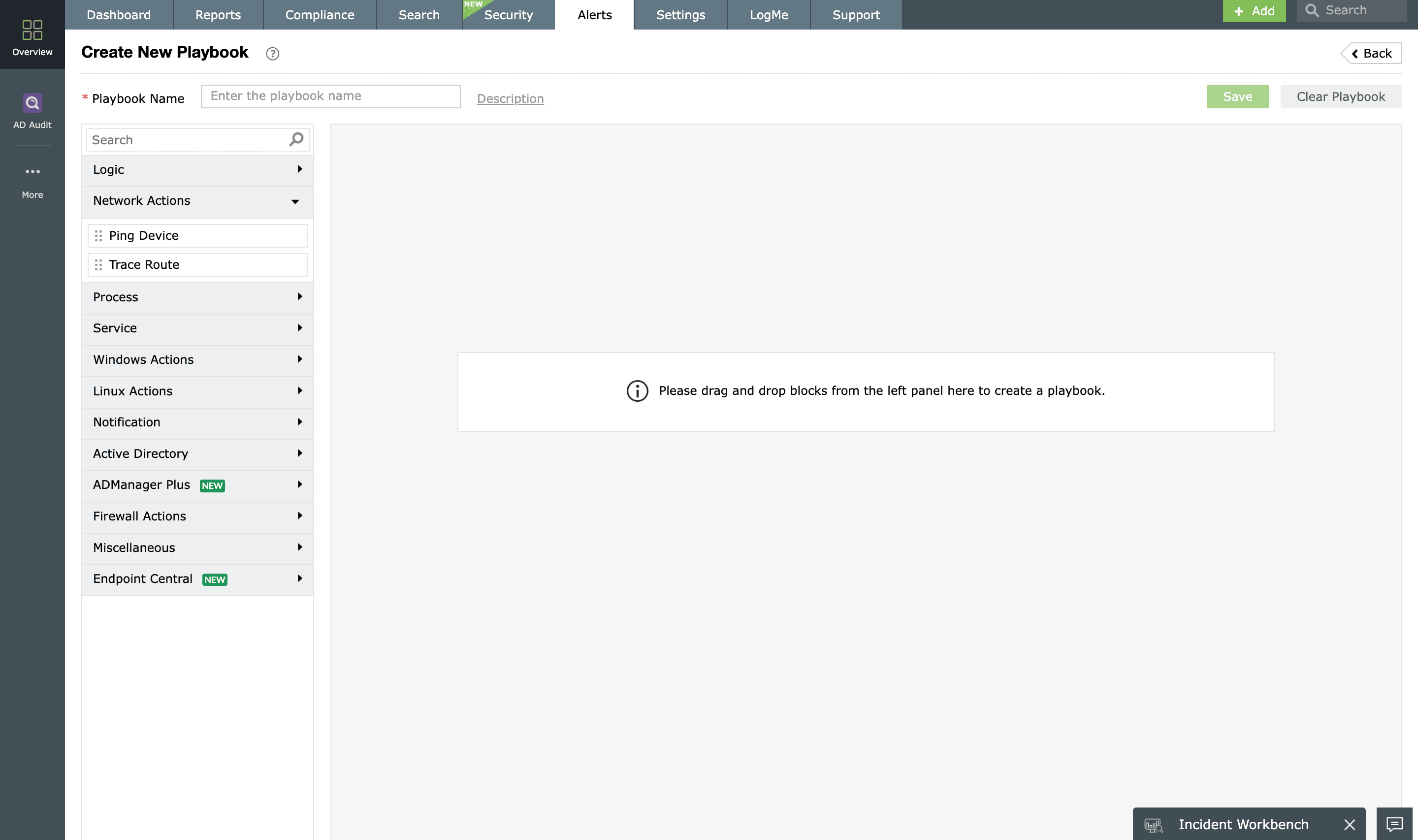
You can build custom incident workflows from scratch using EventLog Analyzer's flexible drag-and-drop workflow builder interface. Simply choose the actions from the left menu, specify their settings, and arrange them in the desired order. The intuitive interface makes it easy to build workflows to suit your requirements.
Manage and track workflows
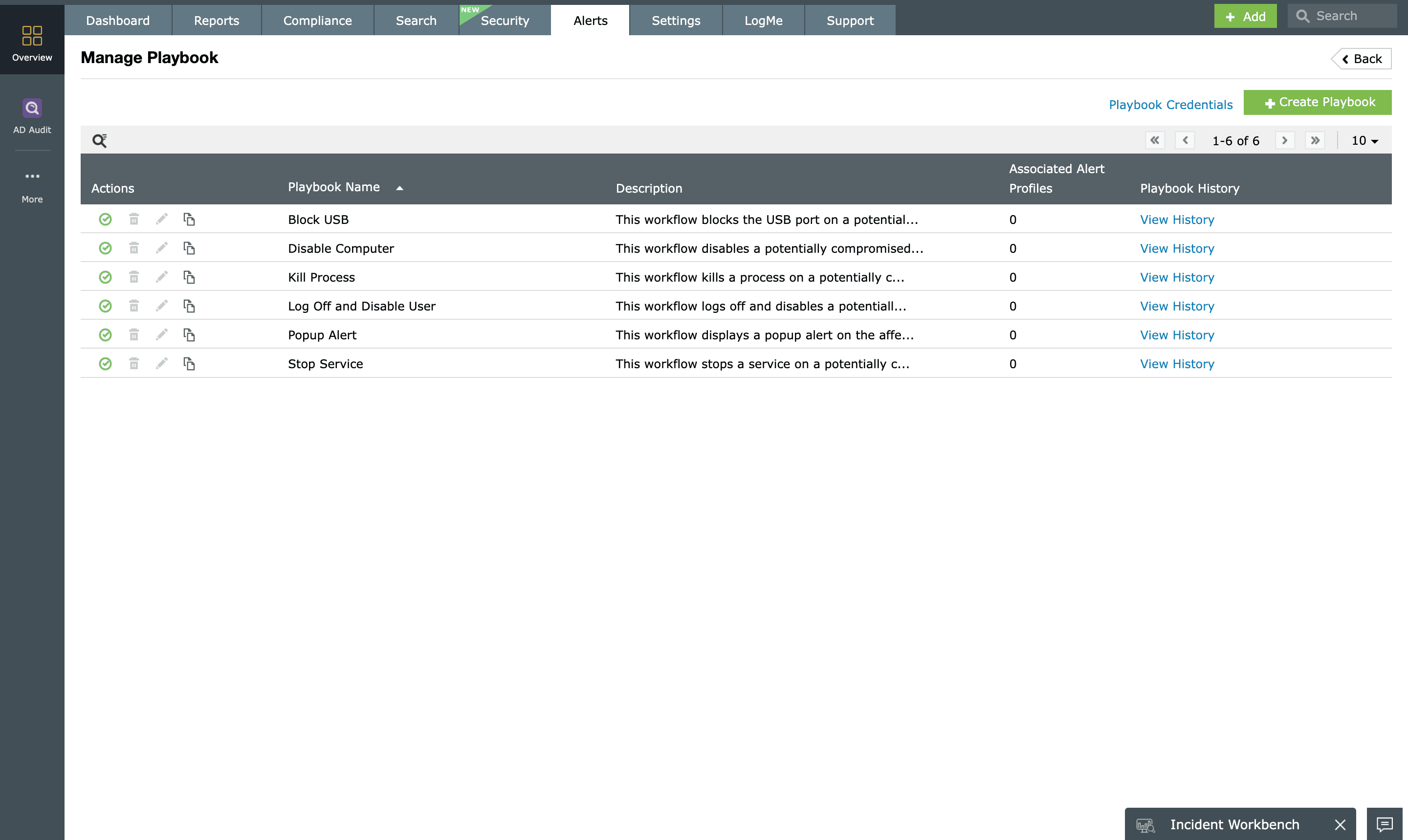
Automated workflows won't be effective if you can't track what happens each time they're executed. EventLog Analyzer tracks workflows with detailed reports of each workflow's execution history. The central workflow management page also allows you to enable or disable workflows, view the number of alerts associated with each workflow, and more.
With EventLog Analyzer's automated incident workflows, you can reduce the demand on your security team to perform mundane response tasks and greatly improve your organization's efficiency in resolving security incidents.











