- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
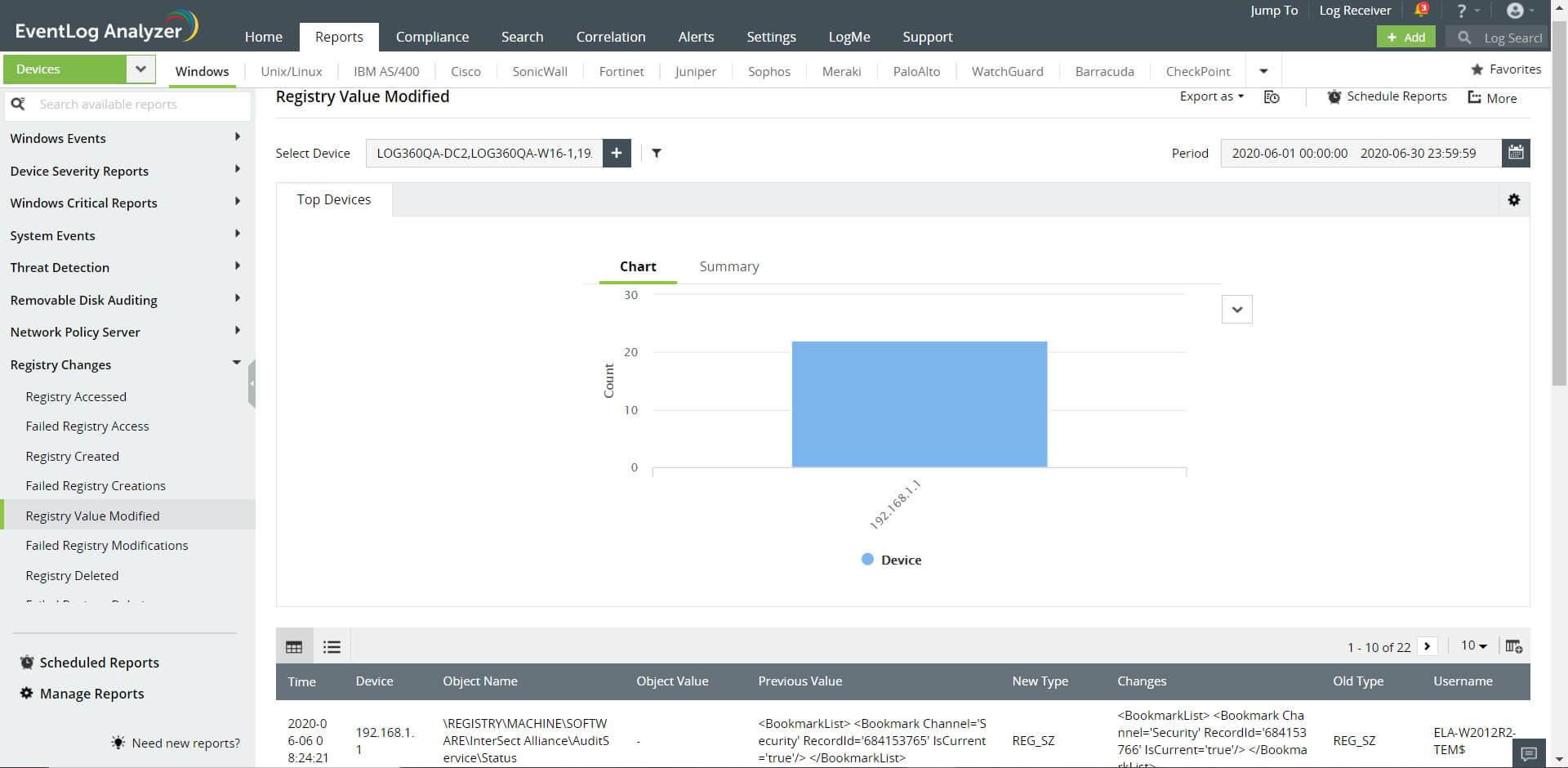
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Every second, your organization's firewalls generate huge amounts of log data. EventLog Analyzer is a firewall traffic analyzer that allows you to monitor firewall traffic with predefined reports and alert profiles to help you tackle this plethora of data, providing you with vital information such as traffic details, security attacks, VPN logon and logoff trends, and firewall rule changes. This out-of-the-box support is provided for multiple vendors, including Cisco, SonicWall, Palo Alto Networks, and Juniper.
Conduct firewall traffic analysis with EventLog Analyzer
- Analyze denied connections based on various criteria, such as users, servers, and firewalls, with EventLog Analyzer's intuitive Denied Connection reports.
- Identify highly active hosts on your network using real-time alerts on User Logons, Failed Logons, and Terminal Service Sessions.
- Discover potentially dangerous external traffic sources with reports on Denied Firewall Traffic. Identify the ports, protocols, source, and destination devices generating the highest amount of firewall traffic.
- Reveal unsafe applications and suspicious users with Individual User Action alerts. For instance, multiple denied connections on the port an application uses may point to a security threat.
- Detect anomalies in your network using Category-based Trend reports. View trends over hours, days, months, and years.
- Audit firewall VPN logs with EventLog Analyzer's VPN Logons Report, which helps you track critical VPN activities such as lockouts, subsequent unlocks, and the users with the most VPN lockouts.
Intrusion detection systems (IDSs) follow a granular approach to threat mitigation. EventLog Analyzer acts as a unified security console that can help accelerate responses to data breaches identified through your IDS.
Conduct forensic analysis on firewall logs
EventLog Analyzer’s efficient log search engine can process 25,000 logs per second. This high-speed search enhances the efficiency of security operations centers (SOCs) by helping security professionals conduct quick forensic analysis on firewall logs and pinpoint the exact log entry that contains information about a network intrusion. EventLog Analyzer's correlation engine also allows security administrators to correlate firewall traffic logs with server logs, and sends real-time notifications that help identify attack patterns, allowing any ongoing attack to be contained immediately.
EventLog Analyzer uses logs from various sources to perform forensic analysis, track users, identify vulnerabilities, audit firewalls, and get real-time information on security threats. With EventLog Analyzer, you can schedule and review traffic reports periodically to better understand your network's traffic. EventLog Analyzer's real-time alerts help in early detection of potential threats, prompting swift action and adjustment of firewall policies as needed.
Ease IT compliance audits
EventLog Analyzer provides audit report templates to help you meet the requirements of regulatory mandates such as HIPAA, GLBA, PCI DSS, SOX, FISMA, GPG 13, and ISO 27001. For instance, the Registry Changes Report provides information on the configuration and status changes in your local workstation, which helps you comply with the GPG's protective monitoring standards.