X
Your download is in progress. If you encounter any issues, please try downloading from this link.
Certificate life cycle management, automated with effortless ease.
Thousands of happy enterprises; millions of certificates and keys managed.
ManageEngine Key Manager Plus is a comprehensive SSL/TLS certificate management solution that's trusted by thousands of enterprises to automate essential certificate management and SSH key management tasks. From discovery to renewal, every action can be automated in a few clicks from one platform and one interface.
With shorter certificate validities come massive management overheads. Key Manager Plus’ comprehensive controls facilitate custom certificate management workflows that automate the entire process.
Discover every SSL and TLS certificate in your IT infrastructure. Key Manager Plus' automated scans discover and organize certificates from your critical servers, user directories, certificate stores, and third-party certificate authorities (CAs) periodically.
Beyond mere certificate expiry alerts, with Key Manager Plus, you can seamlessly automate certificate renewal and life cycle management through an automated certificate management environment. This requires no manual intervention and significantly minimizes overheads.
Orchestrate end-to-end certificate life cycle management with Key Manager Plus' extensive workflows. With one-time configuration, Key Manager Plus' single-touch workflows will automate every step of certificate procurement, deployment, and renewal for your enterprise.
With exhaustive integrations with popular CAs, such as Let's Encrypt, Digicert, and MSCA Integration, as well as built-in private CA capabilities, Key Manager Plus is the only platform you require to manage the complete life cycle of your digital certificates.
Common server vulnerabilities, such as the Heartbleed bug and POODLE SSL, can affect your critical certificates and, in turn, your business operations. With Key Manager Plus' proactive vulnerability scans, you can defend against critical vulnerabilities.
Leverage contextual integrations with ITSM and MDM solutions to seamlessly track and manage certificate operations using Key Manager Plus for reduced IT workload and improved security.
Discover every SSL and TLS certificate in your IT infrastructure. Key Manager Plus' automated scans discover and organize certificates from your critical servers, user directories, certificate stores, and third-party certificate authorities (CAs) periodically.
Beyond mere certificate expiry alerts, with Key Manager Plus, you can seamlessly automate certificate renewal and life cycle management through an automated certificate management environment. This requires no manual intervention and significantly minimizes overheads.
Orchestrate end-to-end certificate life cycle management with Key Manager Plus' extensive workflows. With one-time configuration, Key Manager Plus' single-touch workflows will automate every step of certificate procurement, deployment, and renewal for your enterprise.
With exhaustive integrations with popular CAs, such as Let's Encrypt, Digicert, and MSCA Integration, as well as built-in private CA capabilities, Key Manager Plus is the only platform you require to manage the complete life cycle of your digital certificates.
Common server vulnerabilities, such as the Heartbleed bug and POODLE SSL, can affect your critical certificates and, in turn, your business operations. With Key Manager Plus' proactive vulnerability scans, you can defend against critical vulnerabilities.
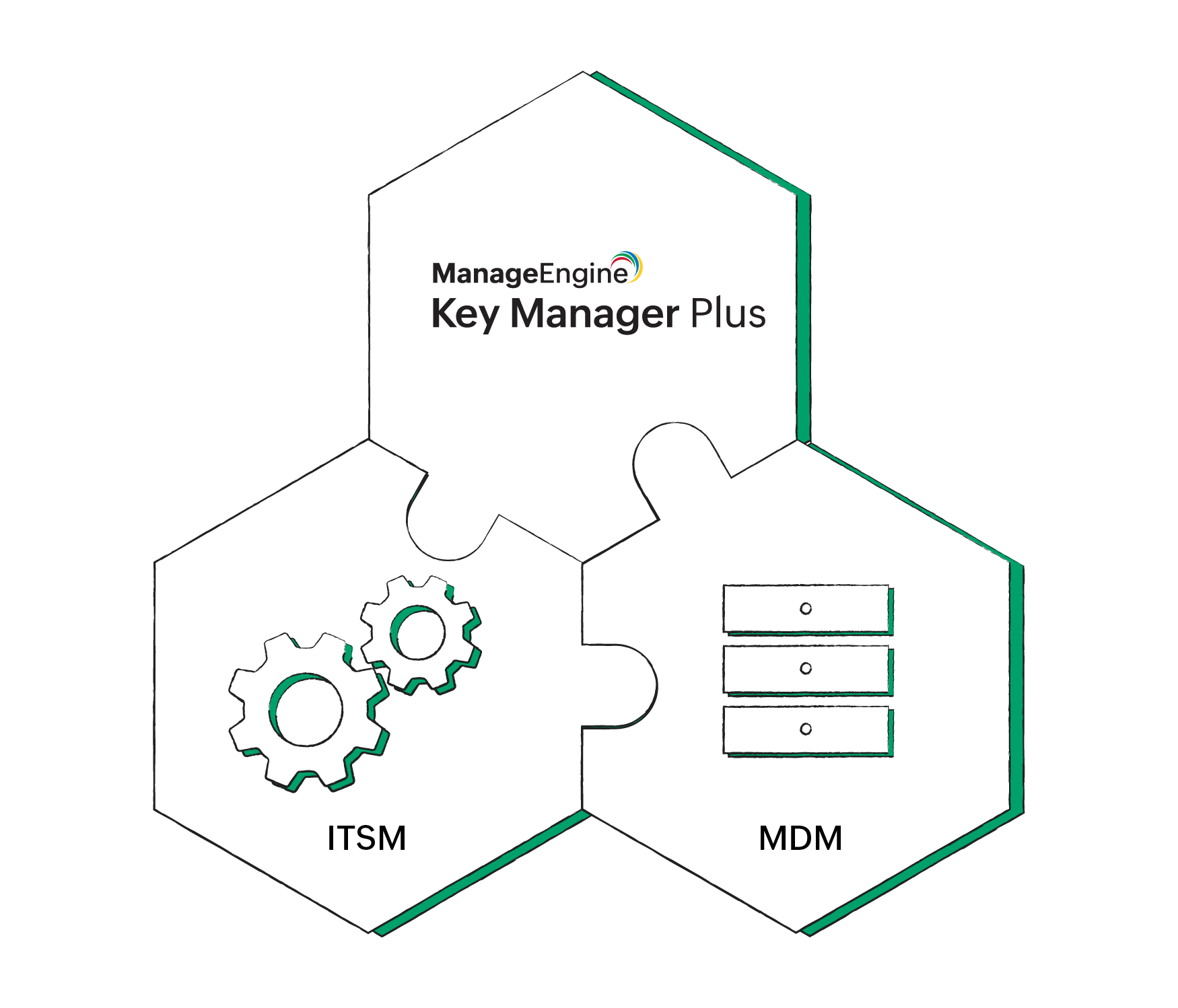
Leverage contextual integrations with ITSM and MDM solutions to seamlessly track and manage certificate operations using Key Manager Plus for reduced IT workload and improved security.
In addition to certificate management, Key Manager Plus offers core machine identity management capabilities to secure SSH keys, Pretty Good Privacy (PGP) keys, and other digital keys.
Create, deploy, recycle, and manage the entire life cycle of SSH keys with our built-in SSH key management tool. View key-user relationships in real time, generate fine-grained user access reports, and easily act on your findings periodically.
Create and manage PGP keys with ease. Assign operations for the key pair, set alerts for key expiry, track operations performed, and generate extensive reports for seamless auditing.
Get a dedicated vault for any digital key you manage. Store your key files safely and retrieve, update, or manage them all from one unified interface.
Beyond its vast capabilities, Key Manager Plus' customer-first approach, rapid time to value, and long-standing industry expertise act as standout factors for customers.
All ManageEngine solutions, including Key Manager Plus, are easy to deploy and adopt. You can deploy the product in your secure infrastructure and get started in as few as two days. Customers can also avail free onboarding assistance from dedicated product experts.
ManageEngine has been a leading certificate life cycle management vendor for over a decade with proven expertise in this space. Coupled with its tight integrations with third-party CAs, cloud platforms, and other IT security solutions, ManageEngine Key Manager Plus offers the complete enterprise experience for all.
We understand that every enterprise requires timely, proactive assistance through a channel of their preference. To facilitate this, Key Manager Plus offers around-the-clock technical assistance through email, phone, and virtual conference. For large-scale enterprises, we also offer on-site assistance.
ManageEngine has extensive partnerships with partners and system integrators across the globe to offer on-site implementations, proofs of concept, and customizations for enterprises. We also leverage our channel partners to offer localized technical assistance in a language of your preference.
Yes, Key Manager Plus is available as both a SaaS solution as well as an on-premise deployment.
Yes. Key Manager Plus offers both key and certificate management capabilities in a single interface. The SSH key management tool can be accessed as a separate module from within the Key Manager Plus interface.
Yes. You can leverage Key Manager Plus' RESTful APIs to facilitate certificate life cycle automation and SSH key management. Using the APIs, you can allow applications to create, fetch, and associate digital keys, and add, retrieve, or manage users programmatically.