Related content
Endpoint detection and response (EDR) and security information and event management (SIEM) are both cybersecurity tools that enable SOC teams to detect and respond to endpoint security threats. While both tools overlap in certain aspects, their scope and purpose are very different.
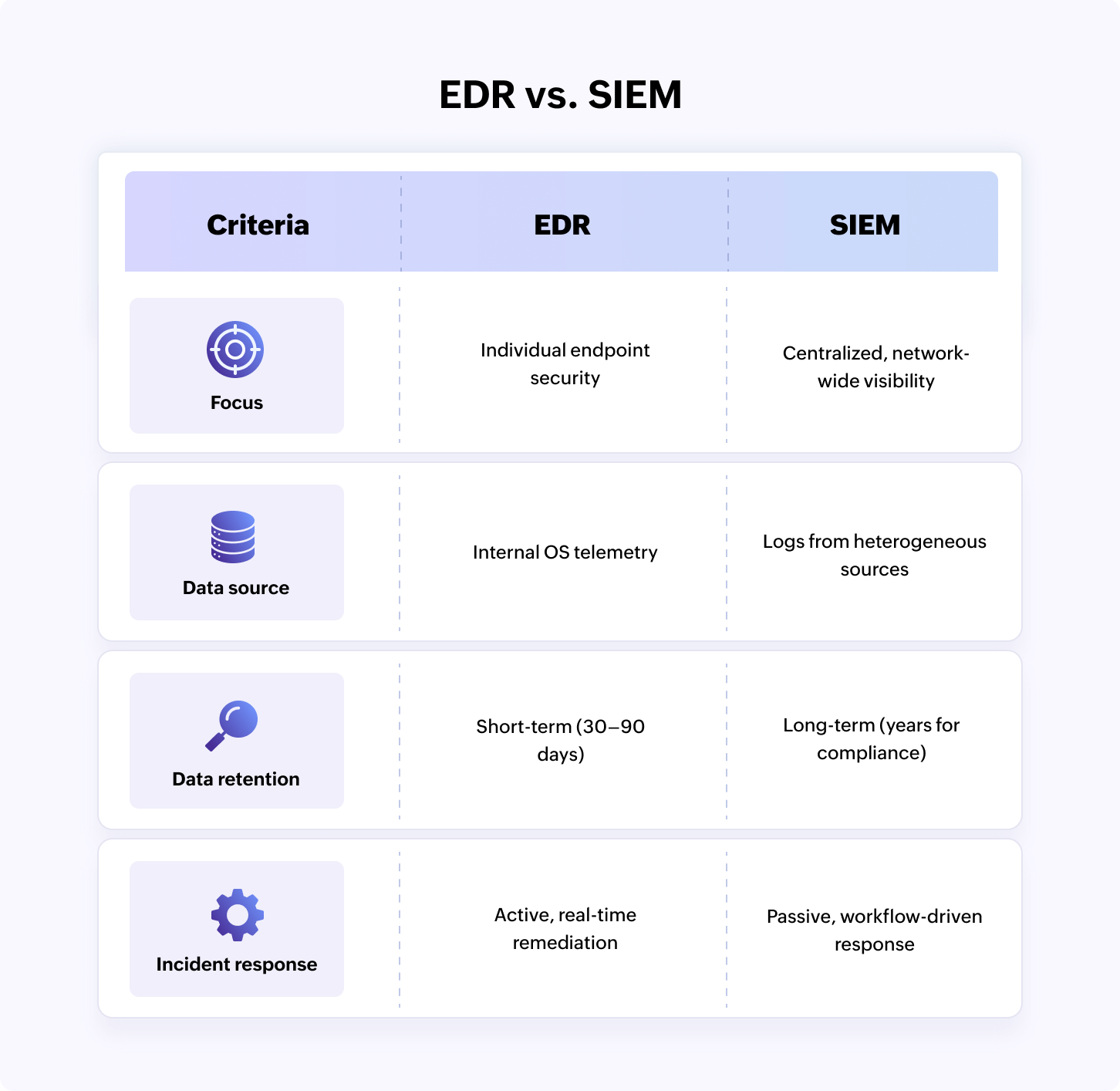
EDR vs. SIEM
In today's threat landscape, the choice between SIEM and EDR depends on your security focus: context versus containment.
SIEM is a centralized data hub that excels at long-term log retention and broad visibility. It pulls data from every corner of the network, including firewalls, servers, databases, and applications, to identify patterns that indicate a breach. It supports compliance reporting (e.g., for the PCI DSS and SOC2) and provides the massive data lake necessary for deep, historical forensic investigations.
EDR is a specialized tool for frontline defense that integrates deeply into individual devices or endpoints. It focuses on monitoring process execution, file changes, and memory activity to neutralize advanced threats like ransomware in real time. It trades the wide-angle lens of SIEM for surgical precision, offering automated isolation and remediation capabilities directly on the infected machine.
What is EDR?
EDR, also known as endpoint detection and threat response, is a security solution that focuses on endpoint security. By providing deep analytics on device behavior, EDR helps analysts flag suspicious activity and contain threats directly at the endpoint level before they can propagate to the network.
How EDR works: It collects and analyzes security telemetry from endpoints, such as workstations, servers, laptops, and mobile devices, to identify potential IoCs indicative of an attack and neutralizes them with instantaneous workflows.
Why use EDR: To accelerate endpoint threat detection and remediation and contain threats at the host level itself.
What is SIEM?
SIEM focuses on comprehensive visibility across the entire organizational infrastructure to identify complex attack patterns and generate alerts. By providing contextual data on user activity and entity behavior across the network, SIEM strengthens an organization's overall security posture.
How SIEM works: It collects logs from heterogeneous log sources, including endpoints, perimeter devices, servers, and applications, to analyze and correlate events to flag threats in real-time.
Why use SIEM: To gain comprehensive network visibility, carry out cross-layer correlation, and generate alerts and reports for regulatory compliance.
Related content
Core capabilities of EDR and SIEM
EDR capabilities
- Granular endpoint telemetry: EDR captures deep endpoint telemetry and kernel-level activity, including process executions, registry modifications, and memory injections. This high-fidelity telemetry allows analysts to reconstruct the exact sequence of a local compromise, providing visibility into sophisticated living-off-the-land attacks.
- Real-time execution control: EDR is fundamentally an action tool and is capable of immediately isolating infected hosts from the network or killing malicious processes. It provides surgical response capabilities that allow responders to neutralize a threat on a specific workstation before it can move laterally into the network.
- Local behavior analysis: EDR uses advanced machine learning (ML) and behavioral analysis to identify suspicious activity on a single host. It detects anomalies such as suspicious spawning, focusing on the how the attack originated rather than just matching known signatures.
- Direct host interaction: By residing directly on the operating system, EDR can block traffic before it leaves the host. This inside-out perspective is essential for flagging fileless malware attacks and unauthorized data exfiltration.
SIEM capabilities
- Universal data aggregation: SIEM prioritizes comprehensive data coverage, ingesting diverse logs from firewalls, cloud services, and even physical security systems. It normalizes disparate data formats into a unified format, enabling broad correlation to identify sophisticated attack patterns that span across the network.
- Threat detection and investigation: SIEM tools leverage high-performance correlation logic and detection rules to identify IoCs, behavioral patterns, and signature-based attacks. By analyzing data across the enterprise, SIEM solutions can trigger high-fidelity alerts in real time that instantly notify analysts of potential threats.
- Alert enrichment and response: SIEM alerts are enriched with contextual data, threat intel, risk scores, and MITRE ATT&CK® mapping. Thisprovides the necessary context to accelerate triage, simplify forensic investigation, and enable SOC teams reduce the time required to neutralize sophisticated breaches.
- Forensic archive and compliance: SIEM serves as the primary system of record, maintaining a long-term, tamper-proof archive of historical events. Its strength lies in conducting deep-dive forensic investigations and generating automated reports for regulatory compliance audits.
EDR vs. SIEM: Which platform is right for your organization?
Choose EDR: If you need deep, specialized protection for devices and immediate action against fast-moving threats like ransomware and direct visibility into processes, memory, and file changes on laptops, servers, and mobile devices.
Choose SIEM: If you need a central console for all security data, including logs from firewalls, cloud apps, and identity providers. It serves as a security data lake, providing the historical context needed for deep forensic investigations and proactive exposure management.
Key differences between EDR and SIEM
The below table helps differentiate EDR and SIEM in various aspects.
| Criteria | EDR | SIEM |
|---|---|---|
| Focus | EDR tools focus on providing visibility into workstations, servers, and mobile devices to detect malicious activities that bypass traditional signature-based detection software. | The scope of SIEM lies in aggregating data from heterogeneous data sources to provide a centralized pane of glass for monitoring the security posture of the network. |
| Data sources | It fetches internal OS telemetry, including registry changes, memory and disk activity, and local file modifications, from endpoint devices, such as servers, mobile devices, and laptops, to identify suspicious IoAs. | It ingests massive volumes of log data from network firewalls, cloud infrastructure, identity providers, and even EDR tools to correlate disparate events into a single, cohesive security incident. |
| Threat detection | Detection is centered on behavioral analysis at the execution level. It identifies exploit attempts by spotting abnormal system calls or unauthorized memory injections directly on the host machine. | Detection relies on cross-layer correlation of security events based on predefined detection rules. It identifies behavioral threats across entities using ML-based anomaly modeling. |
| Alerting | Alerts are triggered by behavioral analysis and AI models that identify abnormal user and endpoint activities that deviate from a standard baseline. | Alerting is driven by predefined alert profiles with ML-based dynamic thresholds. It also enables the creation of custom alerts for specific threats. |
| Incident response | EDR offers active incident response and immediate remediation. It allows security teams to remotely isolate an infected laptop from the network and terminate malicious processes in real time. | SIEM offers a passive response mechanism with basic incident response workflows. On integrating with a SOAR platform, it can initiate automated playbooks to respond to incidents. |
| Data retention | EDR usually stores telemetry data for 30–90 day windows. It prioritizes immediate investigation over long-term historical storage of every single process execution. | SIEM is designed for longevity, storing compressed logs for several years. This is critical for meeting regulatory compliance requirements and audits. |
| Forensic analysis | EDR acts as the black box of the device. It shows exactly what a user does, which files were accessed, and how a malicious script moved through system memory. This greatly helps analyze the root cause of the threat. | SIEM helps map the entire attack kill chain with process trees and threat investigation consoles. Its reporting and alerting capabilities help gather all evidence related to a particular attack for forensic investigation. |
| Agent deployment | EDR tools are agent-based, requiring a lightweight software sensor to be installed on every endpoint. This ensures the tool can probe into the operating system kernel for security monitoring. | SIEM solutions are typically agentless and collect log using APIs, syslog, forwarders, and connectors. In some cases, SIEM solutions also use an agent to collect logs from specific sources. |
| Integration | EDR tools have the flexibility to integrate with other cross-platform tools. It often feeds its high-fidelity alerts into SIEM or XDR platforms to provide the necessary host-level alerts. | SIEM tools can easily integrate with XDR and EDR tools to ingest alerts and automate response actions using SOAR integrations. This makes SIEM solutions highly flexible and agile platforms. |
Strategic implementation: Benefits and limitations of EDR and SIEM
Choosing between EDR and SIEM is a pivot between endpoint analytics and comprehenive security visibility. Below is the strategic breakdown of how these tools perform.
EDR implementation
EDR is designed for rapid, automated threat containment at the endpoint level and is suitable for enterprises with on-premises and hybrid networks.
| Benefits of EDR | Limitations of EDR |
|---|---|
|
|
SIEM implementation
A SIEM solution serves as the central lake for security data. It is the strategic choice for compliance-heavy industries and enterprises with diverse technology stacks.
| Benefits of SIEM | Limitations of SIEM |
|---|---|
|
|
Can SIEM and EDR work together?
EDR and SIEM can not only work together but also complement each other to build a synergy that converts analytics to actions. Here is a sample workflow of how these tools can collaborate.
Data ingestion: The process begins with EDR feeding high-fidelity telemetry like process hashes and command-line arguments into the SIEM tool.
Data enrichment: The SIEM solution then enriches this data with external threat intelligence and context from other logs, such as identity and location.
Contextual correlation: The SIEM solution correlates the various IoCs and IoAs to stitch together the attack story. For example, it links a suspicious VPN login (from network logs) to a specific file being modified on a laptop (from EDR telemetry), confirming a successful account takeover.
Automated response: When a SIEM solution detects a multi-stage attack pattern, it can trigger an automated SOAR playbook that instructs the EDR tool to isolate the infected host, preventing the threat from spreading further into the network.
EDR vs. SIEM decision matrix: Which caters to your needs?
Explore ManageEngine Log360's SIEM capabilities with a personalized walk-through.
Frequently asked questions
What is the difference between SIEM and EDR?
The core difference between SIEM and EDR lie in their focus and data source. EDR focuses on endpoint security, while SIEM focuses on overall network visibility.
| Feature | EDR | SIEM |
|---|---|---|
| Data source | Leverages deep telemetry from hosts such as laptops, servers, and workstations. | Aggregates logs from the entire network (firewalls, the cloud, and apps). |
| Core function | Stops active threats by killing processes or isolating devices. | Centralizes data for long-term storage, auditing, and correlation. |
| Visibility depth | Provides granular visibility into the operating system and endpoint activity. | Gives comprehensive visibility into the entire network and activities. |
Can SIEM and EDR be integrated?
Yes, SIEM and EDR are designed to be integrated. Modern SIEM platforms like Log360 use APIs to ingest high-fidelity telemetry from EDR tools, combining granular endpoint insights with network-wide logs to create a unified and powerful security ecosystem.
How do SIEM and EDR work together?
SIEM and EDR function together as a unified detection and response platform. SIEM serves as the centralized correlation engine that aggregates security analytics to identify multi-stage attack patterns, while EDR provides the granularity and execution flows required to contain an attack at the host level.
How do SIEM and EDR technologies overlap?
SIEM and EDR converge on endpoint monitoring, where both tools collect and analyze host-level telemetry to identify malicious activity. They overlap in threat detection capabilities, utilizing behavioral analytics and anomaly-based logic to identify IoCs.
EDR vs. SIEM: Which should I choose?
Choose SIEM if you need centralized logging for compliance and broad visibility across the entire enterprise, including legacy systems and network hardware. Choose EDR if you prioritize granular, process-level visibility and the ability to instantly quarantine infected devices to stop a breach in its tracks.
How do SIEM and EDR differ in scope?
EDR's scope is narrow but deep, focusing exclusively on managed endpoints like laptops and servers. SIEM's scope is wide, covering the entire infrastructure, including firewalls, cloud apps, and unmanaged devices that EDR cannot monitor.
- What is EDR?
- What is SIEM?
- Core capabilities of EDR and SIEM
- EDR vs. SIEM: Which platform is right for your organization?
- Key differences between EDR and SIEM
- Strategic implementation: Benefits and limitations of EDR and SIEM
- Can SIEM and EDR work together?
- EDR vs. SIEM decision matrix: Which caters to your needs?
- Frequently asked questions