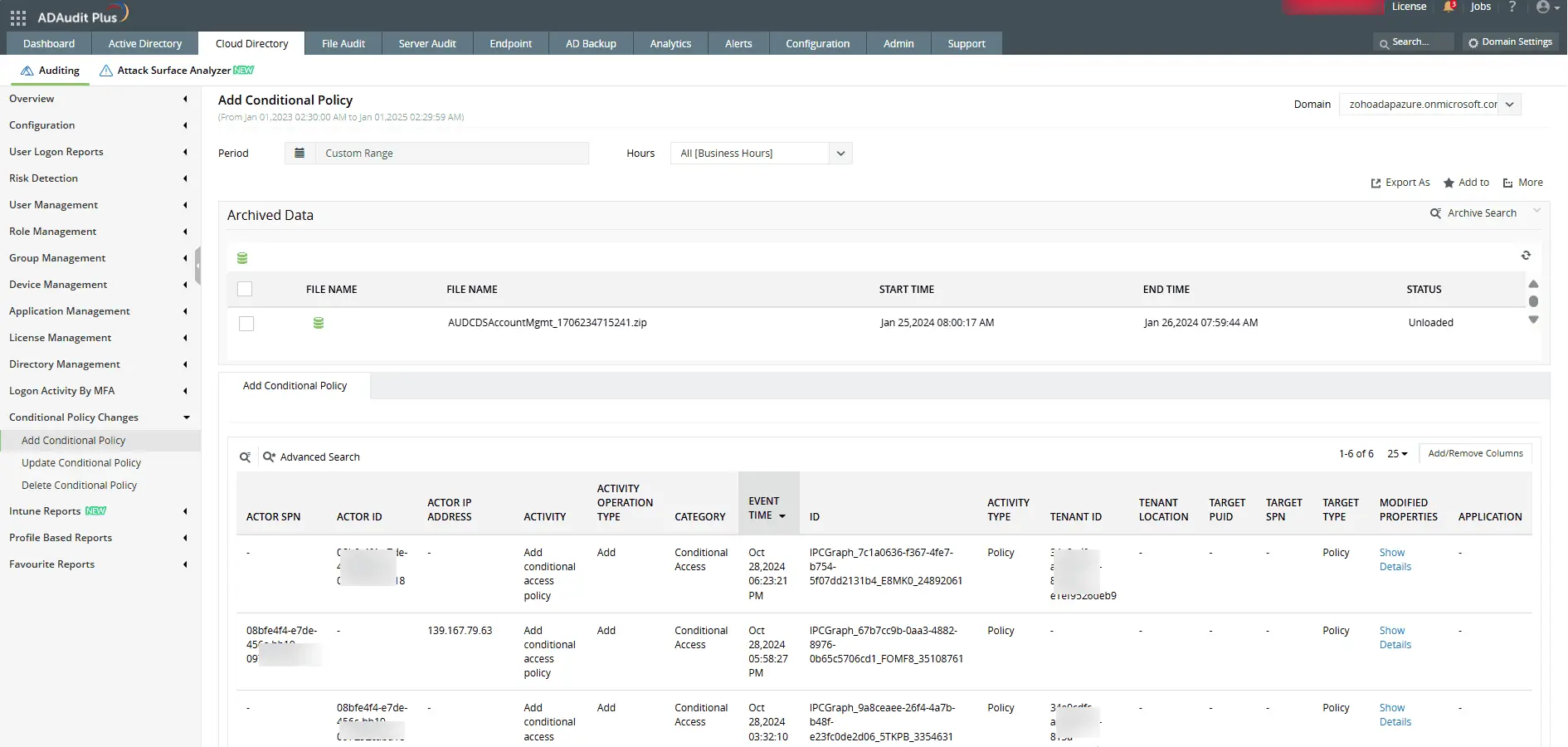
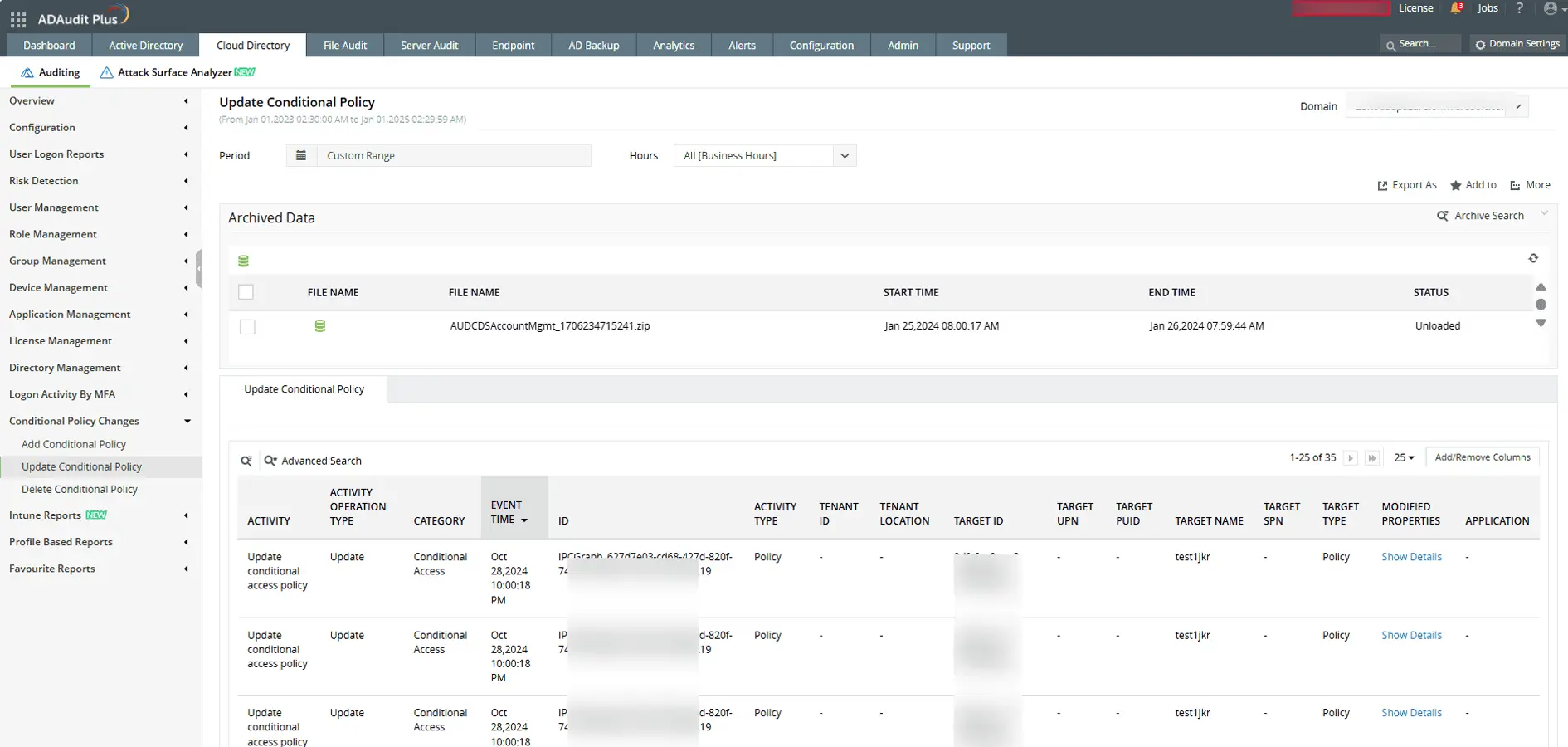
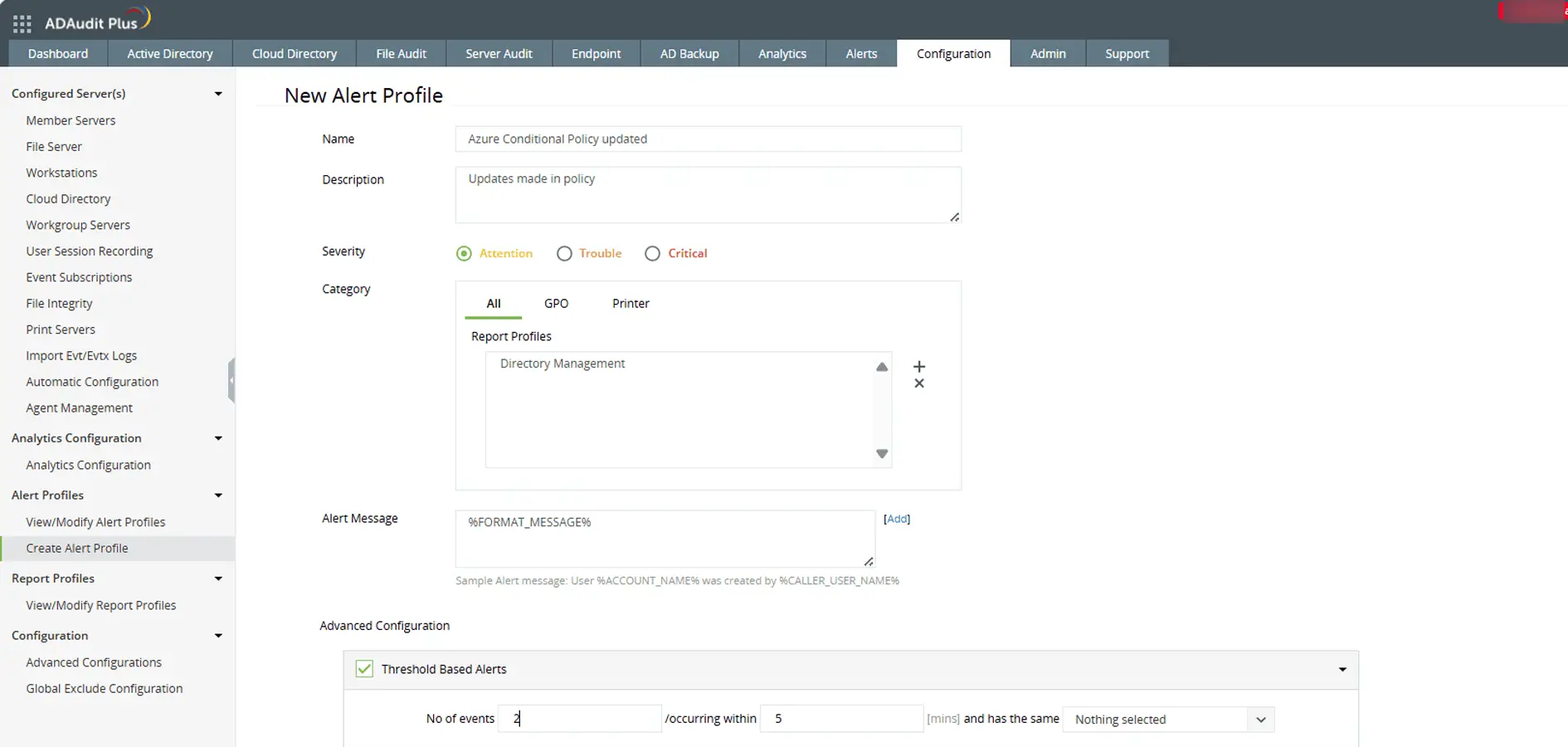
A Microsoft Entra Conditional Access policy (formerly Azure AD Conditional Access policy) is an automated access control rule that determines how and when users can access cloud apps and services. These policies evaluate conditions such as user risk, device compliance, location, and app sensitivity, then enforce access decisions like requiring MFA, blocking access, or limiting session duration.