- Free Edition
- Quick Links
- Active Directory Auditing
- Active Directory auditor
- Active Directory monitoring
- Account lockout analyzer
- Login monitoring software
- Active Directory change notifier
- User logon audit reports
- AD logon logoff tracker
- User logon failure auditing
- Login history tracking tool
- AD change auditor
- Insider threat detection software
- Permissions change auditing
- Entra ID reporting
- Privileged user monitoring
- User behavior analytics tool
- Active Directory security monitoring
- Group Policy auditing tool
- GPO change auditor
- Entra ID auditing
- Audit user account management
- OU change auditor
- Audit group membership changes
- Active Directory auditing and reporting tool
- GPO reporting tool
- Remote desktop monitoring software
- PowerShell logging and auditing
- Azure password protection auditing
- Azure sign-in risk detection
- File Server Auditing
- Windows Server Auditing
- Employee Tracking
- Workstations Auditing
- Compliance Auditing
- Other features
- SIEM Integration
- Windows DNS - Schema Auditing
- Windows security event log monitoring
- SIEM audit solution
- Schedule Active Directory change reports
- Reports from Archived Data
- Aggregated summary reports
- AD new/old attribute changes
- Audit trail
- Audit Active Directory LAPS
- Scheduled Reports & Alerts
- Account lockout examiner
- Industry
- Documents
- Success Stories
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Kerberos auditing
Gain complete visibility into Kerberos logons, authentication failures, and user behavior, all in one place. Detect anomalies and uncover kerberos-based attacks before they impact your network.
Audit Kerberos authentication service with ease
Audit Kerberos activity across domains
Monitor the usage of ticket-granting tickets (TGT) and service tickets across all AD domains, ensuring no blind spots in Kerberos authentication events.
Track user logons in real time
Track Kerberos authentication service audit failures, uncover account lockouts, and resolve them quickly.
Detect network compromise at the earliest
Get instantly alerted on high volume logon attempts, logons during unusual times, and remote accesses by unusual users to detect potential security threats.
Drill deep into Kerberos events
Analyze every Kerberos event with detailed event data such as user name, event ID, host name, event type, failure reason, and more—all from a unified dashboard.
Stop Kerberos-based attacks before they spread
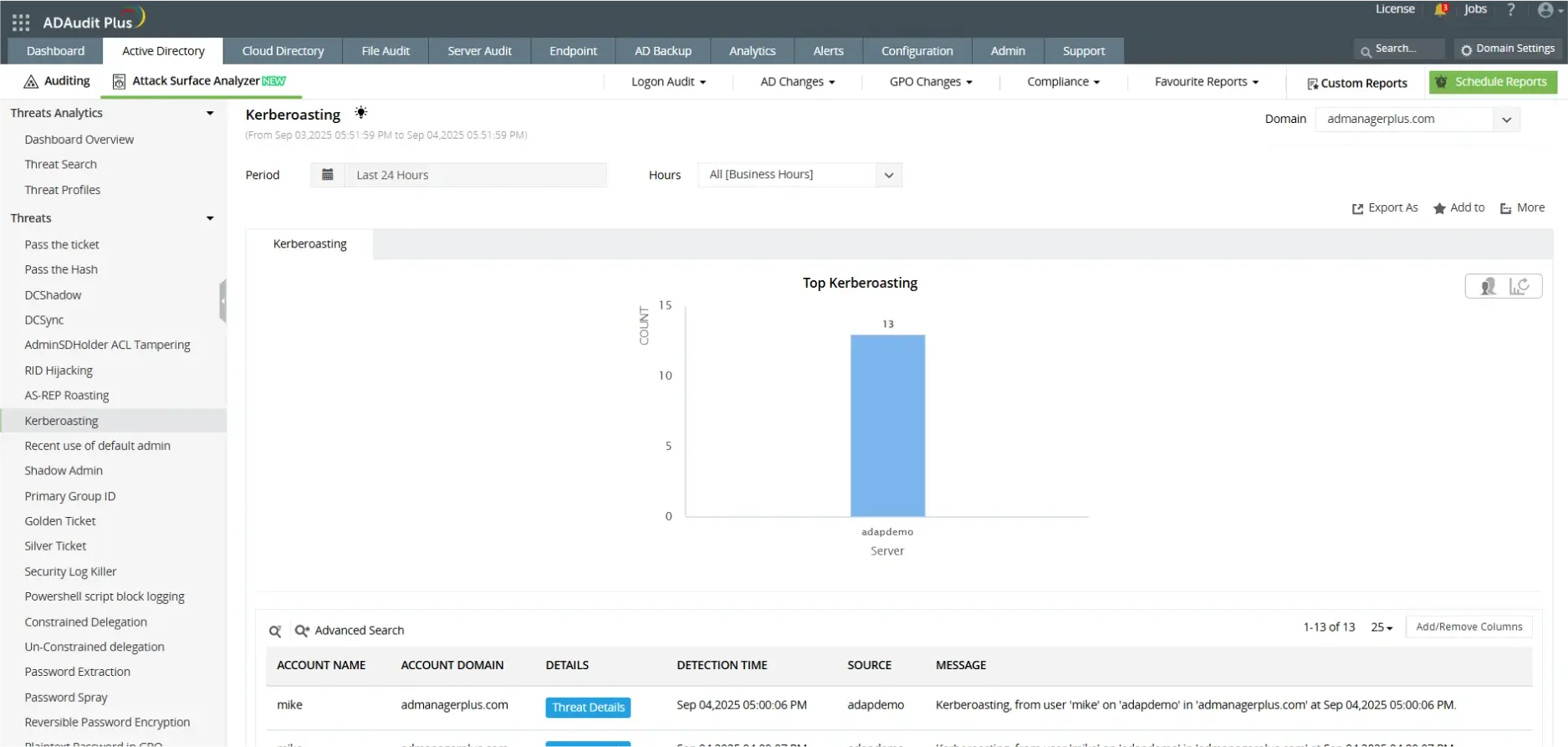
Detect Kerberoasting attempts early
Spot unusual TGS ticket requests for service accounts that may indicate attackers attempting to extract and crack encrypted credentials offline.
Block Golden and Silver ticket abuse
Identify forged Kerberos tickets designed to provide attackers persistent access and stop unauthorized lateral movement across your AD environment.
Uncover AS-REP roasting and pre-auth abuse
Find accounts with pre-authentication disabled, and detect any attempts to disable Kerberos pre-authentication and prevent brute-force password cracking.
Detect credential theft techniques
Catch pass-the-ticket and pass-the-hash attacks by monitoring Kerberos events for anomalous patterns such as unusual ticket usage, ticket reuse, long-lived tickets, or logon anomalies.
Enable Kerberos auditing and prevent Kerberos-based attacks with ADAudit Plus
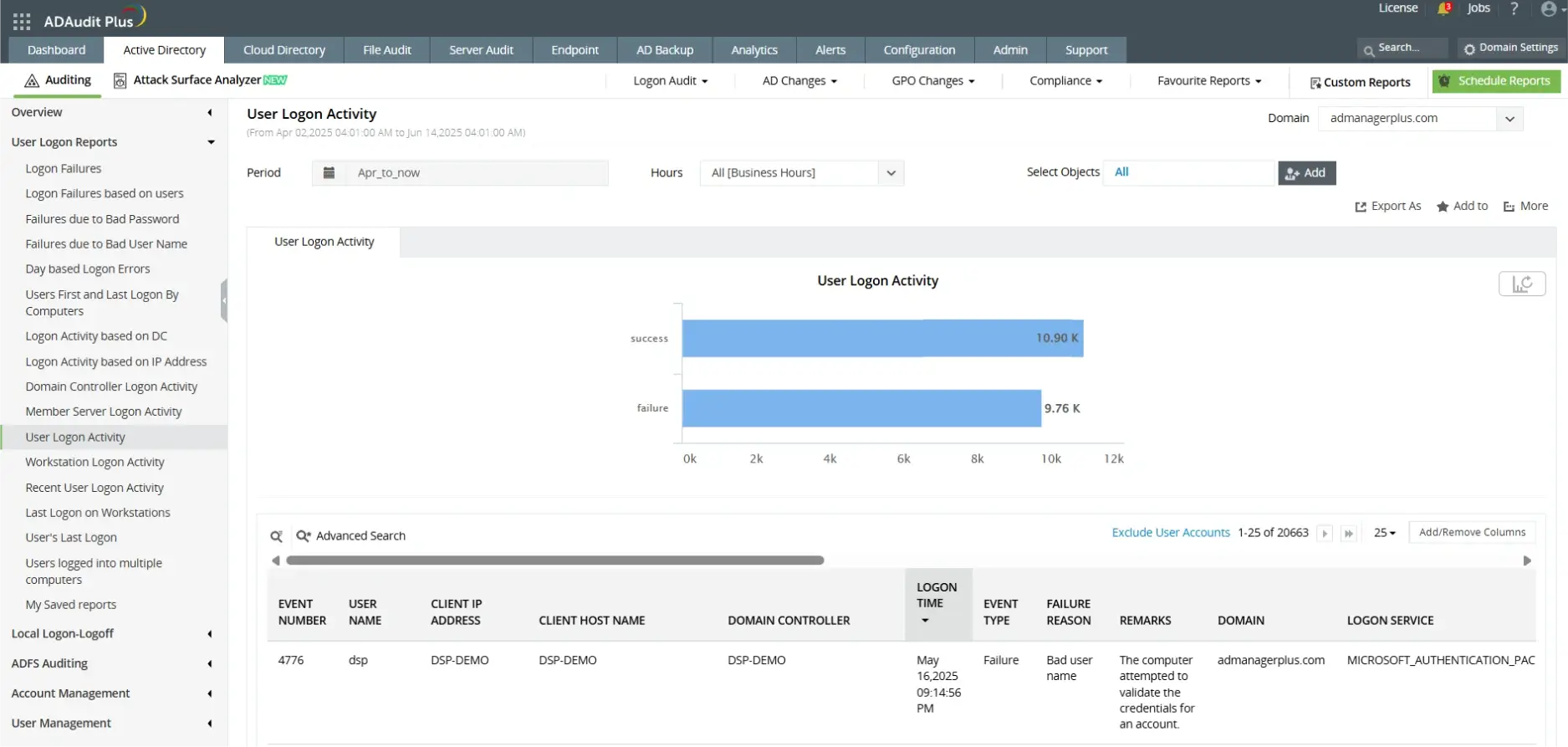
- Audit user logon activity
- Uncover Kerberoasting attempts across servers
Frequently asked questions
Kerberos is the default authentication protocol used in AD environments. It uses tickets and strong encryption to securely verify identities between users and services, reducing the risk of credential theft compared to older methods like NTLM.
In most modern AD environments, Kerberos is enabled by default. You can verify this by checking domain controller security policies, monitoring event logs for Kerberos ticket-granting events (Event IDs 4768, 4769, etc.), or reviewing network traffic to confirm Kerberos ticket exchanges.
NTLM is an older challenge-response authentication protocol that relies on password hashes. Kerberos is more secure and efficient, using tickets issued by a trusted Key Distribution Center (KDC). Unlike NTLM, Kerberos supports mutual authentication, delegation, and stronger encryption standards.
Common Windows Security Event IDs for Kerberos include:
- 4768 – A Kerberos authentication ticket (TGT) was requested
- 4769 – A Kerberos service ticket (TGS) was requested
- 4770 – A Kerberos service ticket was renewed
- 4771 – Kerberos pre-authentication failed
- 4776 – NTLM authentication (useful for spotting NTLM vs Kerberos usage)
Other solutions offered by ADAudit Plus
File permissions auditing
Audit all file and folder permission changes. Know who made those changes, when, and from where.
File change monitoring
Gain instant visibility into all modifications and failed access attempts made to your critical files.
Forensic analysis
Investigate security incidents faster with actionable and accurate audit data.