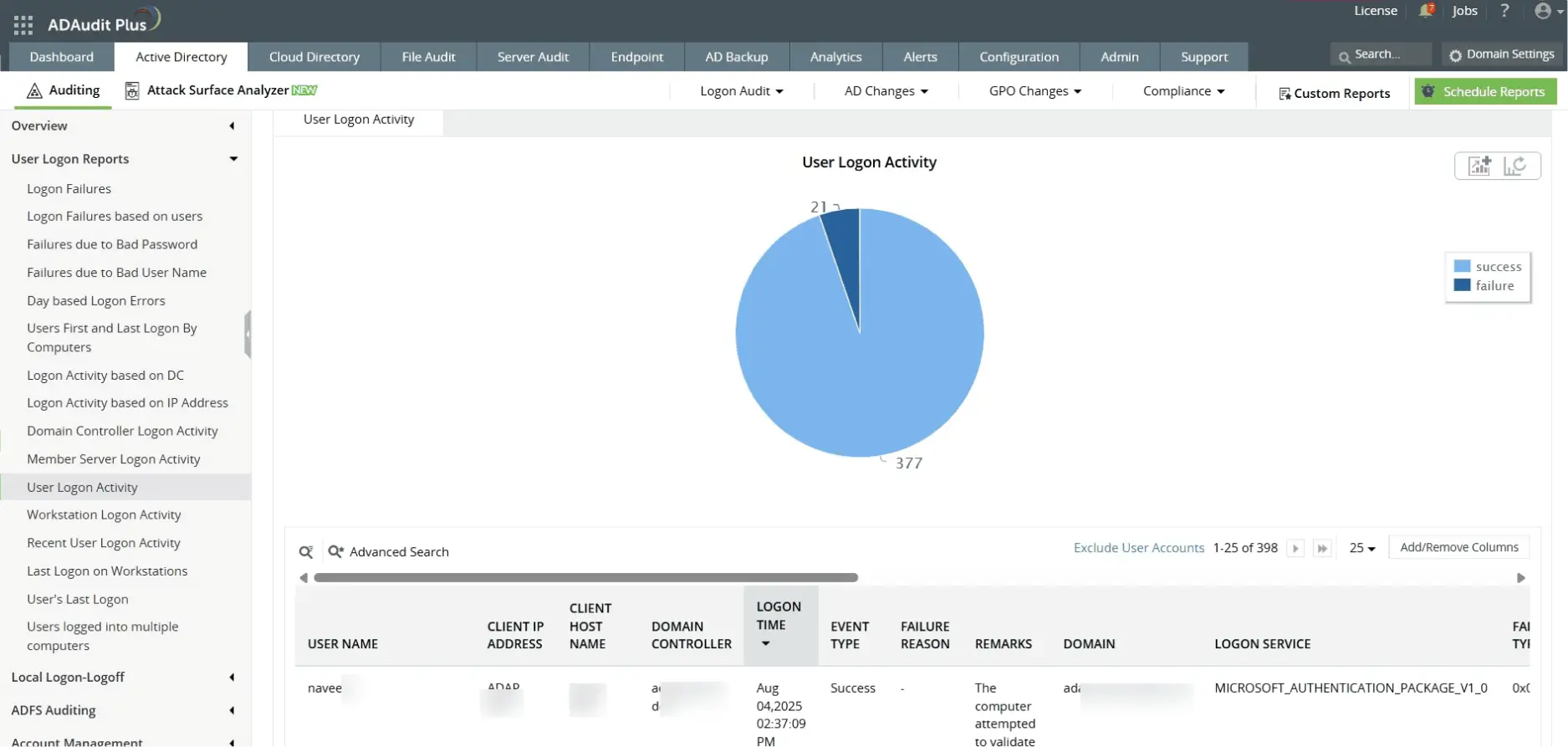
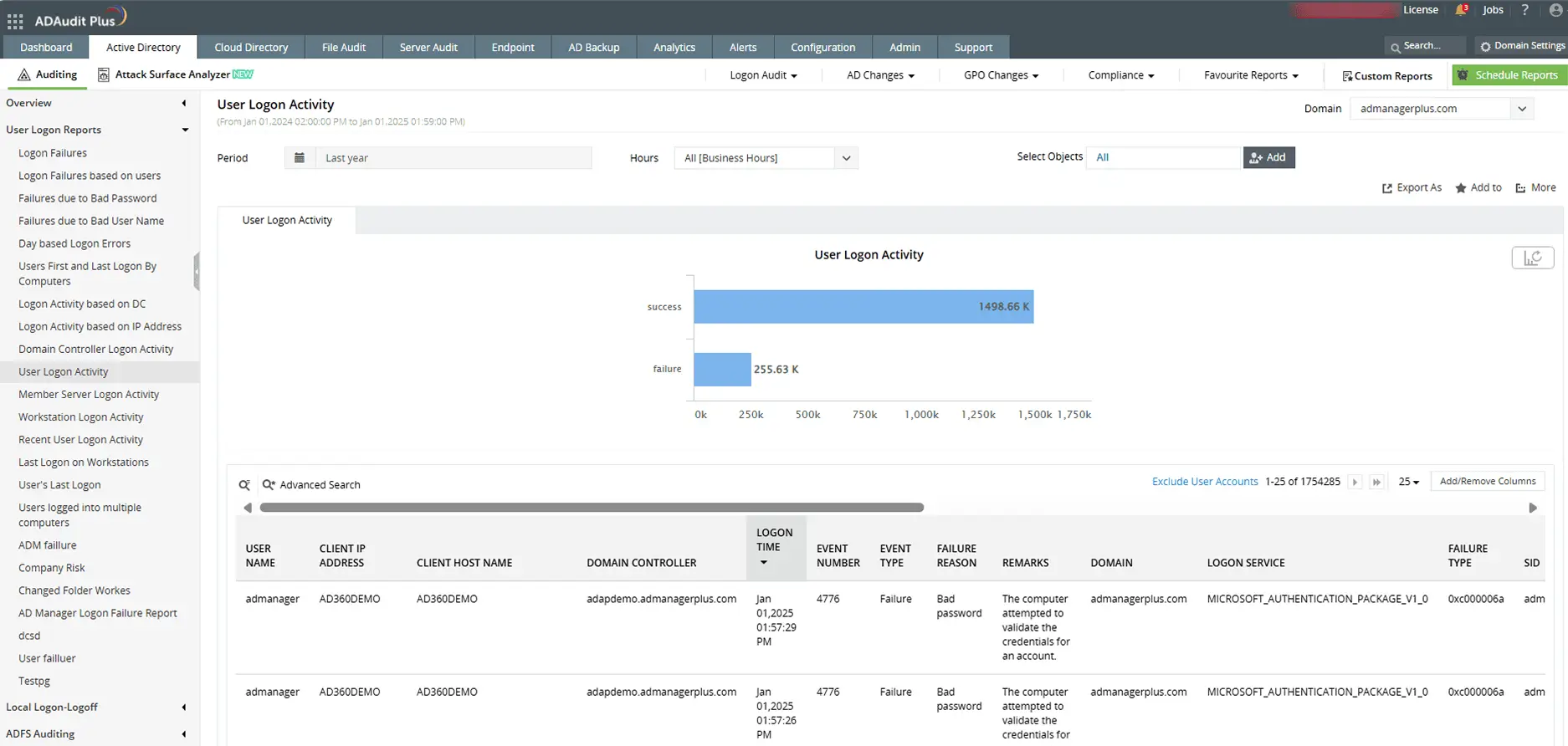
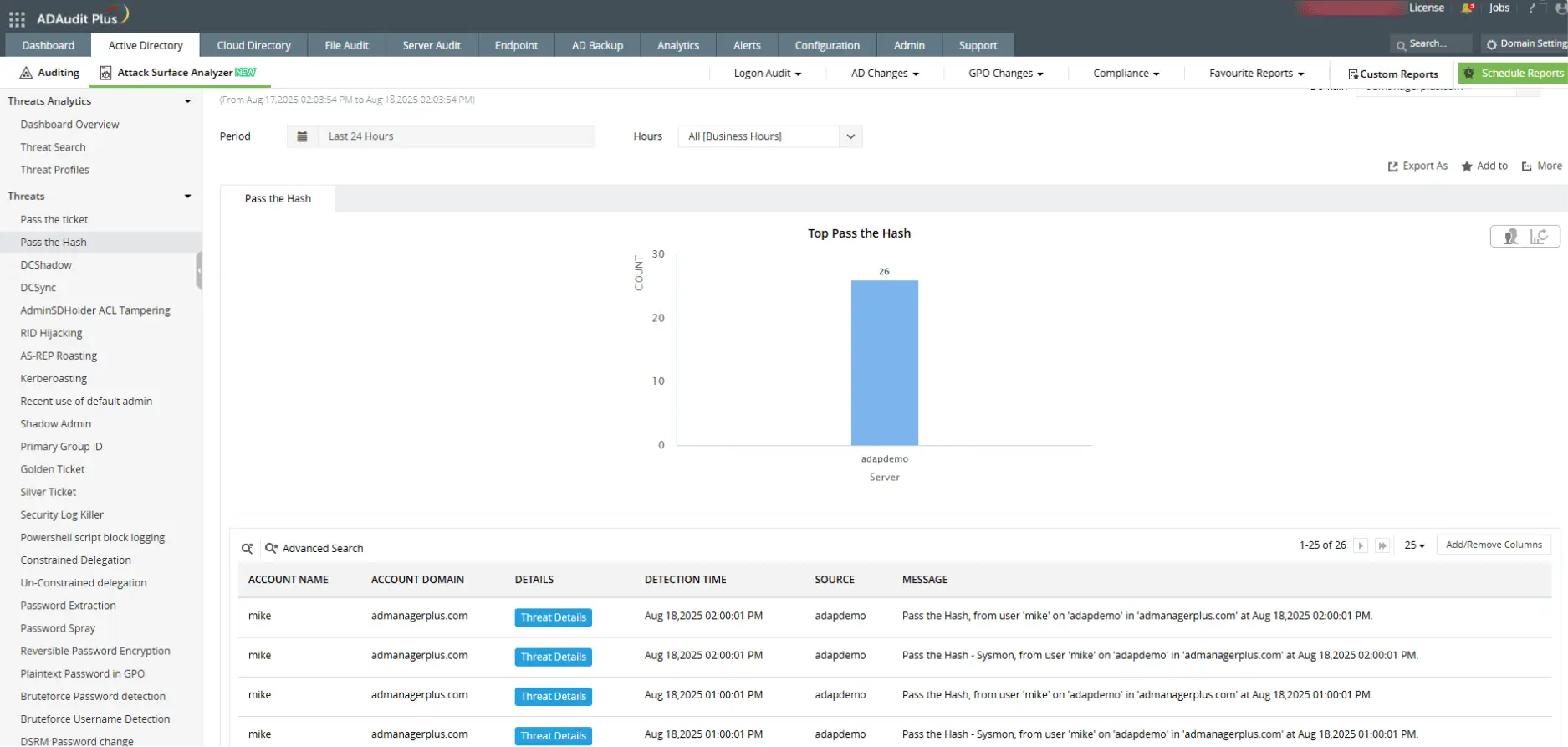
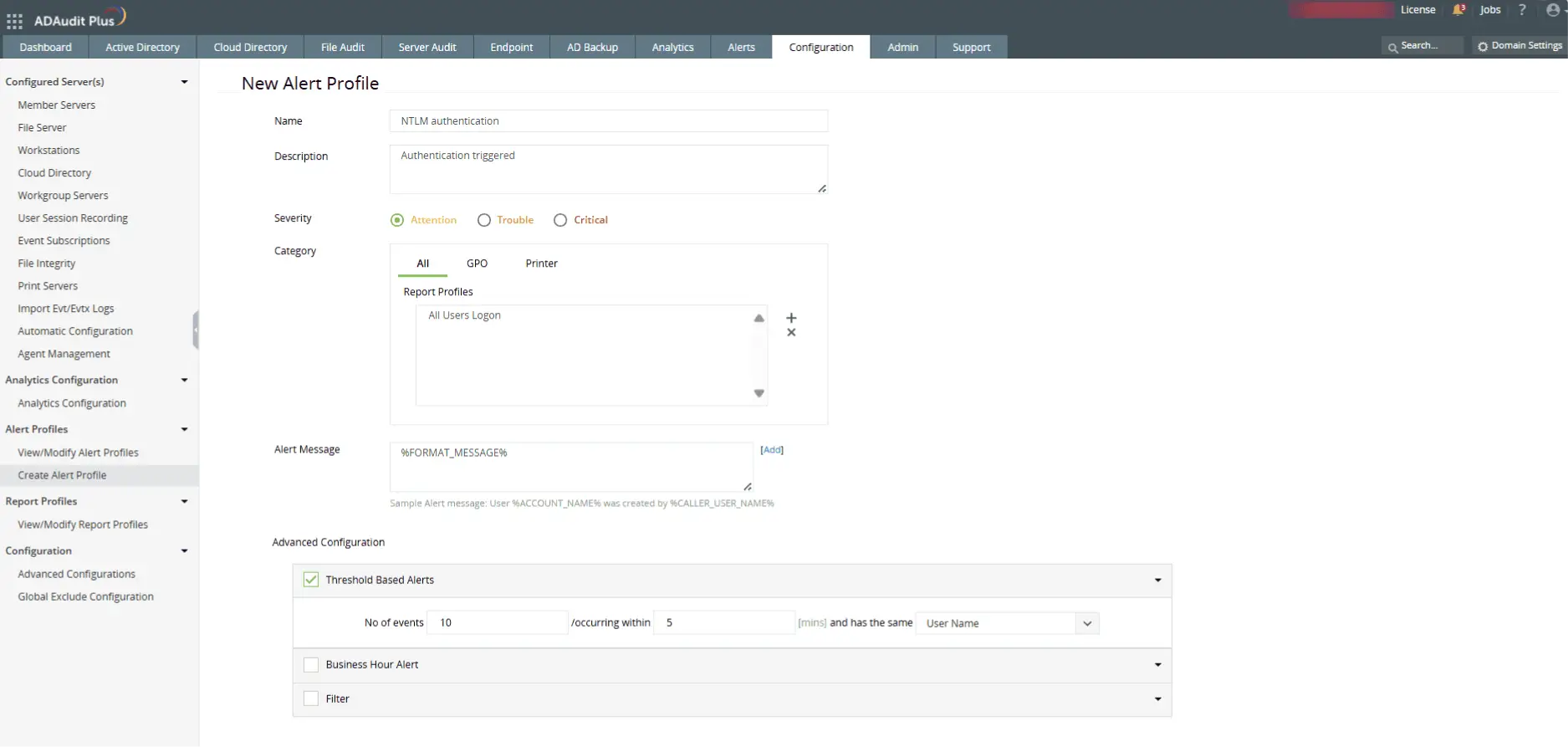
NTLM (NT LAN Manager) is a legacy Windows authentication protocol used to validate credentials during user logons. It relies on challenge-response mechanisms and is still used in environments where Kerberos cannot function, such as with local account authentication or across untrusted domains.