How NetFlow Analyzer’s Security Analytics keeps yournetwork one step ahead
Spot threats before they spread
Catch suspicious activity early with flow-based, ML-driven analysis that keeps watch over your network 24/7.
See the full story behind every event
Get complete context who’s involved, what happened, where it came from, and how it unfolded, so nothing slips through the gaps.
Cut through the noise
Adaptive learning helps reduce false positives and repetitive alerts, letting your team focus only on what really matters.
Focus on what’s truly risky
Dynamic scoring and time-weighted severity classify the events that pose the greatest danger, so you know where to act first.
Connect incidents to real-world attack tactics
Every detected threat is mapped to the MITRE ATT&CK framework, giving you clear visibility into the attacker’s playbook.
Identify devices that don’t hide behind IPs
Track assets reliably with persistent identifiers, ensuring accurate detection.
Fortify your network's security posture
In today’s environment where network threats and inefficiencies creep in from anywhere. With NetFlow Analyzer’s refurbished Security feature, you get the information you need at the right time, so you can respond before series of small disturbances become big disasters.
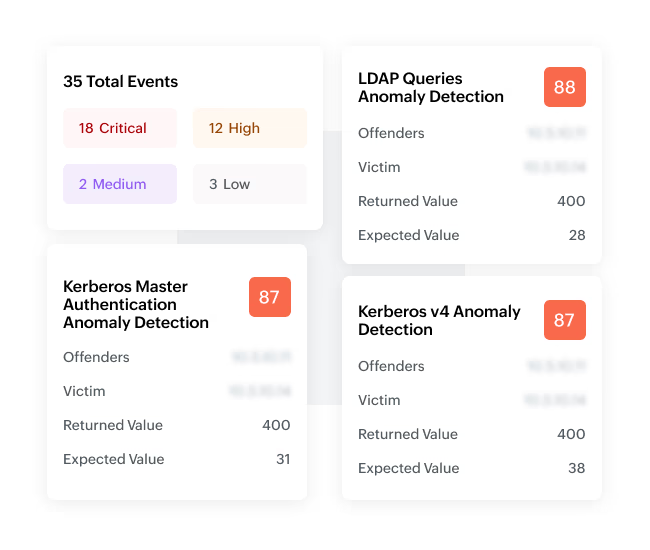
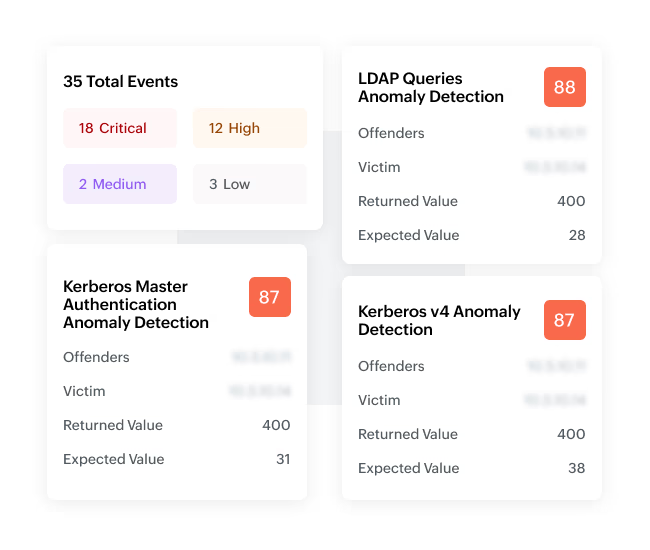
01. Contextual event classification and prioritization
NetFlow Analyzer's Security Analytics module identify events that might become attacks, assigning severity levels to prioritize actions. This classification provides a thorough detail about the problem, including network port, protocol, application, and more, enabling quick identification and corrective action.
02. Seamless integration with MITRE ATT&CK framework
The integration of NetFlow Analyzer with the MITRE ATT&CK framework allows security teams to map network anomalies and threat behaviors to known attacker tactics and techniques. This alignment helps in better detecting, understanding, and responding to attacks, enhancing the overall security posture.

03. Agentless, centralized data collection
The Security Analytics module offers agentless, centralized traffic data collection, analysis, and management. This approach simplifies deployment and reduces overhead, providing seamless visibility into both external and internal security threats without the need for additional agents.

04. Faster Troubleshooting with advanced forensic reports
When spikes or outages hit your network, knowing what’s happening isn’t enough, NetFlow Analyzer’s forensic report lets you rewind time, examine packet-details, and isolate the users, applications, protocols, and conversations behind anomalies. With this deep insight, you’ll uncover the root cause of performance issues, prevent future surprises.

Understand what’s really happening under the hood of your network in real time
Experience a tool trusted by 1 million IT admins across the globe.
NetFlow analyzer, it speaks for itself. It gives us a good insight into what's happening on the network. The security team and network team use it quite extensively. It's a great product, easy to use.
Australian
Community Media
NetFlow Analyzer boasts a rich set of features that align well with its intended purpose. The ability to collect, monitor, and analyze NetFlow, sFlow, J-Flow, and other flow data from various devices. The tools provide in-depth traffic analysis, top talkers, application protocols, and overall network performance helping identify bandwidth hogs and potential bottlenecks.
Research And Development Associate
IT Services Industry
The tool best for real-time monitoring of network traffic to view bandwidth usage and network performance. Monitor traffic by protocol, allowing understanding of how different protocols are affecting the network. Source/Destination Analysis visibility into traffic patterns by source and destination IP addresses, aiding in identifying network congestion source.
Senior Quality Engineer
IT Services Industry

