How to detect and delete Ghostscript?
Description
Widely used page description languages such as Adobe Systems' PostScript, Portable Document Format (PDF) and image manipulation software such as Image Magick and GIMP primarily use Ghostscript, an open-source software, for file format conversions and rasterization of images. It has an in-built -dSAFER protection option for thwarting malicious PostScript operations from being executed. However, a critical vulnerability has been discovered that enables Remote Code Execution (RCE) in Ghostscript. This would allow an intruder to take control of the vulnerable systems in your network by sending a malformed PDF file which, upon reaching the interpreter, executes malevolent program.
Steps to combat Ghostscript vulnerability with Endpoint Central
Ghostscript could be omnipresent in your network. Since no patch has been released for this vulnerability, Endpoint Central provides a custom script that helps in automating the process of detecting and uninstalling Ghostscript. Follow these steps to detect and uninstall Ghostscript, thereby proactively safeguarding the systems in your network.
- Navigate to Configurations tab and click on Script Repository.
- Under templates tab , look out for the script and add this to the repository. Refer this image.
- Windows : GhostscriptVulnerabilityForWindows.exe
- Mac : GhostscriptVulnerabilityForMac.sh
- Debian-based Linux OS : GhostscriptVulnerabilityForLinuxDeb.sh
- RPM-based Linux OS : GhostscriptVulnerabilityForLinuxRpm.s
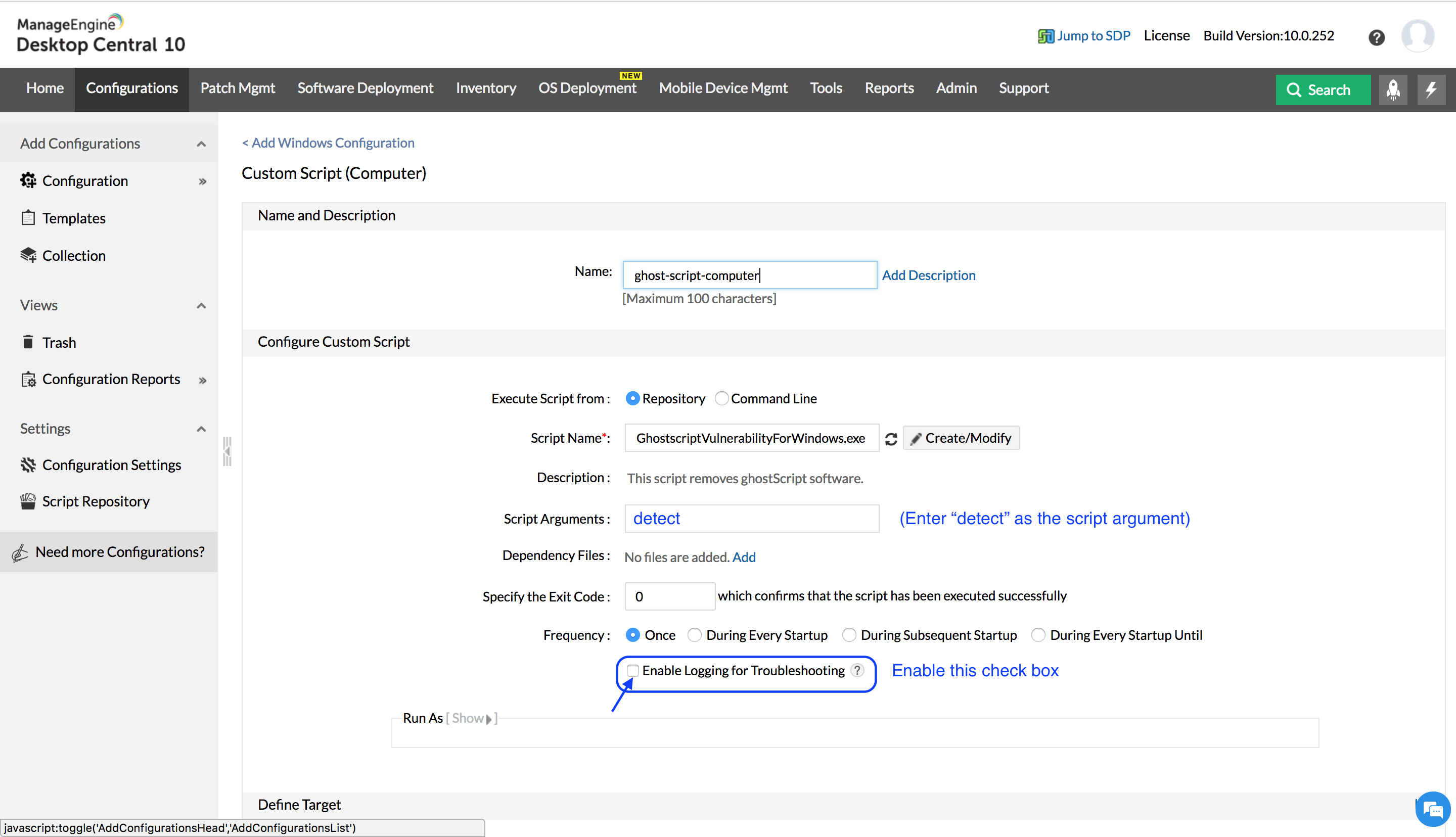
- Create and deploy a Custom Script configuration using this script.
- If Ghostscript has been uninstalled successfully, the script will return a success message. In case of failure during the uninstallation process , the script will return a failure message.
- If you want to refrain this process to detection of Ghostscript, provide an argument detect while executing the script.
- The script will yield a success message in the presence of Ghostscript and will yield a failure message otherwise.




