The proliferation of hybrid and multi-cloud environments, the fast uptake of SaaS-based applications, the advent of the metaverse, and positive feelings about remote work have all led to a paradigm shift in the way organizations serve their customers. At the same time, they've also expanded the attack surface in a world where cyber adversaries have upped their game. With almost everything going digital, work has become riskier.
Such a climate warrants organizations to invest in cybersecurity defense mechanisms that give weightage to both digital forensics and automated incident response. While effective digital forensics enables organizations to investigate and get to the root cause of a problem, automated incident response helps mitigate the problem as quickly as possible.
Imagine a scenario where an attacker has compromised a user's account from a remote location by exploiting a vulnerability in the RDP connection. The attacker then "lives off the land" by using PowerShell cmdlets, and conducts domain reconnaissance. They find out important details about the domain, such as the names of security groups and organizational units, and about the members within them. They also find out the names of network file shares and backup folders, and the password policy that is in effect. Instead of doing this quickly, they lie low and take their time so as not to arouse any suspicion. Then, they escalate privileges and move laterally, finding their way into the organization's cloud environment. And once they are here, they launch a ransomware attack.
An account compromise could lead to a ransomware attack.
This is just one example of the numerous ways an attacker's nefarious designs get executed. An organization's security analytics platform or SIEM solution should ideally be able to link these events together, conclude that this sequence of events is malicious, and alert the security team even though the attacker has taken efforts to minimize suspicion. It should be able to do this using capabilities such as advanced event correlation and anomaly detection, a.k.a user and entity behavior analytics, that analyze events that occur in different parts of a hybrid network in real time. The security team can then use digital forensics to understand what really happened and recommend a permanent solution.
For effective digital forensics, the security team should first be able to view all the events from across the network for a specified time range, all in one place. They should then be able to write queries connected to the alert they received to drill down to the root cause. Or better yet, they should be able to drill down using a click-based search, which allows them to click the event message or any variable contained within. For example, the image below could be an event that is logged:
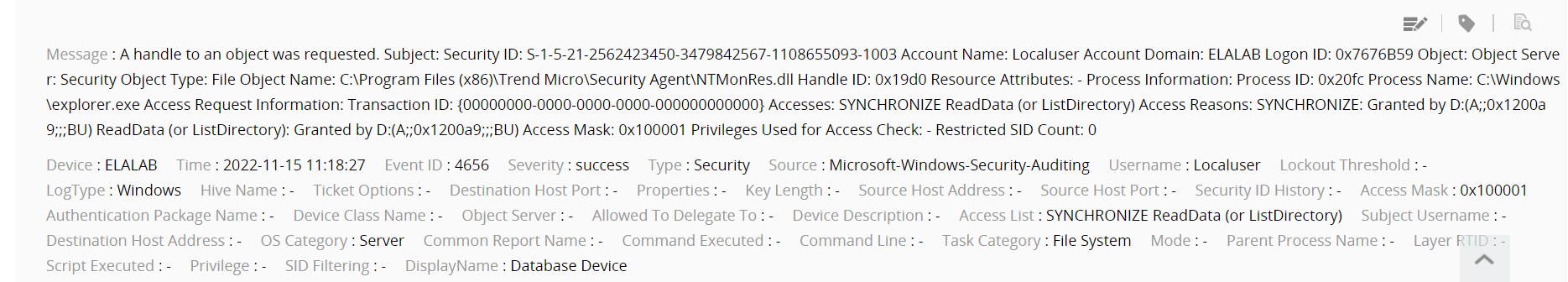
If the security analyst wants to know all the activities performed by the user called Localuser within that same time range, they would simply click Localuser. However, if they want a list of all users who triggered events during the time range, they would click Username. Please note that this is just an example; the way forensics works in different solutions will be different.
With the use of queries or a click-based search, the security analyst can ultimately get to the root cause of the problem. For example, they may finally find out the IP address, the host, and the process that were involved in the malicious initial access. They will also be able to build a complete time line of the attack kill chain and recommend a feasible policy change for better defense.
Automated incident response allows organizations to mitigate possible attacks quickly. The security analytics platform or SIEM solution should send an alert as soon as the tell-tale signs are noticed. At the same time, it should also be able to execute response actions automatically. These automatic response actions should be executed simultaneously as the security analyst performs the forensics analysis. This way, the first response is immediate and the attack can be contained.
For automated incident response to be effective, the security analyst should be able to associate alerts with predefined or custom response workflows. For example, they could have created a workflow to log off and disable the user involved in the alert, and then isolate their machine. As soon as the alert is triggered, this set of response actions will be performed. Besides this, several alerts can be automatically combined into one incident through an incident rule, and a particular security analyst can be automatically assigned to resolve it.
Effective incident response also means that there should be a provision for the SIEM solution to send the generated alerts as service tickets to a ticketing solution through an integration. The alerts can then be worked on and resolved from within the ticketing solution. This will lead to even more streamlined incident response.
Streamlining digital forensics and automated incident response is critical for organizations that want to improve their security maturity. It will also help improve analyst experience and enable the security team to make better decisions.
You will receive regular updates on the latest news on cybersecurity.
© 2021 Zoho Corporation Pvt. Ltd. All rights reserved.