- Knowledge base
- Active Directory management
- Active Directory reports
- Active Directoy integrations
- Active Directory automation
- Active Directory delegation
- Governance, risk, and compliance
- Microsoft 365 management and reporting
- AD migration
- Access certification
- Identity risk assessment
- Risk exposure management
- FAQs
- Pricing
- Online demo
- Request support
- Get quote
For teams working on VPN setups, Wi-Fi authentication, or access control architecture, the comparison between LDAP and Remote Authentication Dial-In User Service (RADIUS) comes up quickly.
Both LDAP and RADIUS authenticate users, integrate with directory systems, and are widely used in enterprise environments. In certain scenarios, their responsibilities appear to overlap.
So where do they differ?
The simplest way to understand it is this: LDAP interacts with identity data. RADIUS governs network access. They solve related problems, but not the same one.
What is LDAP?
LDAP was designed to communicate with directory services. In most enterprise environments, that means AD.
When an application needs to verify credentials, check group membership, or retrieve user attributes, it typically uses LDAP. A common action is the LDAP bind, where a client submits credentials to the directory for validation. Beyond authentication, LDAP also allows systems to search and modify directory information.
It is frequently used for:
- Application authentication
- User and group lookups
- Attribute-based access decisions
- Identity synchronization

What is RADIUS?
RADIUS was built to manage network access.
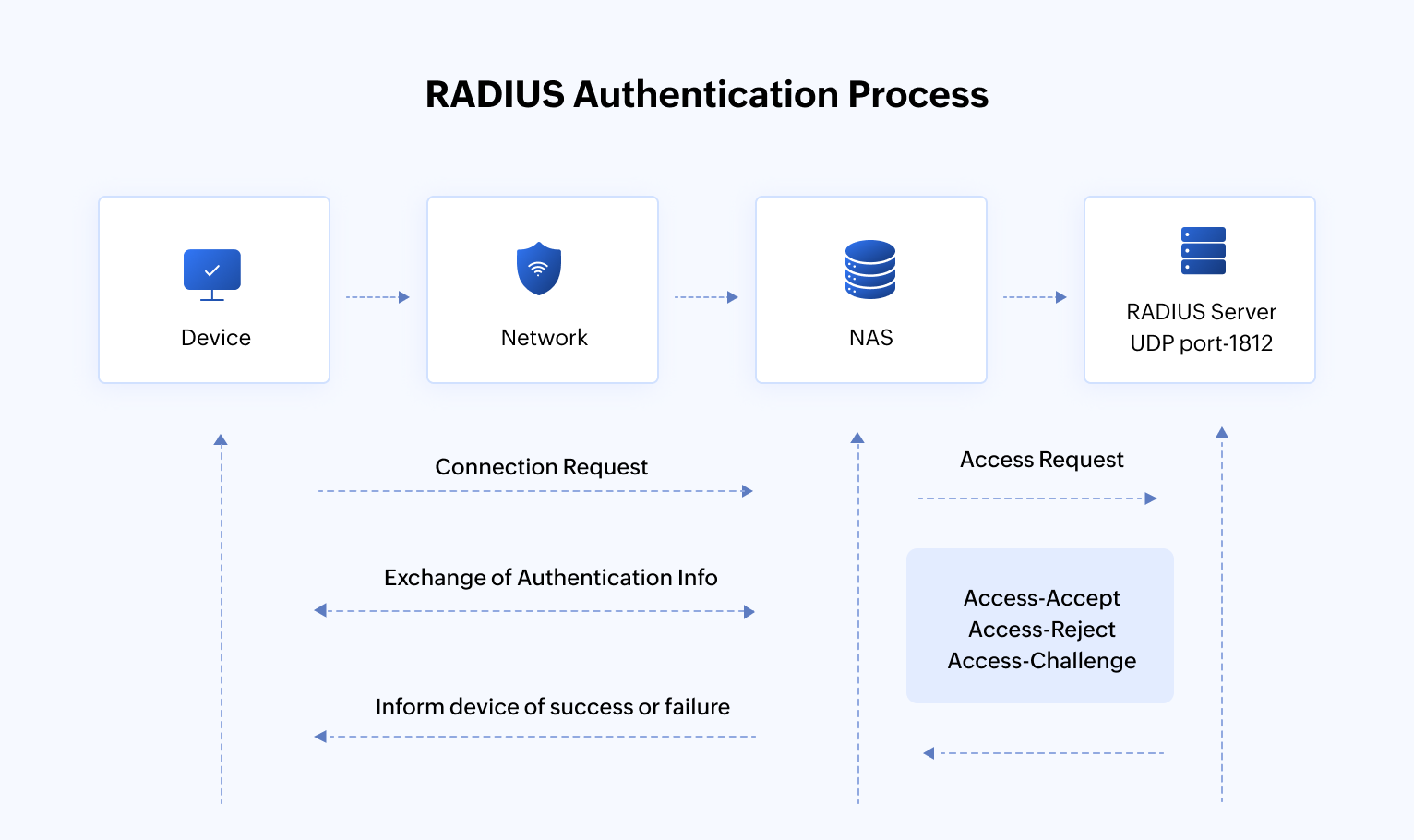
It operates as an AAA protocol, which is authentication, authorization, and accounting. When a user connects to corporate Wi-Fi, initiates a VPN session, or logs into a network device, the request is typically sent to a RADIUS server.
The RADIUS server validates credentials, often against AD, and determines whether access should be granted. Unlike LDAP, RADIUS logs session activity and can return attributes such as VLAN assignments or policy parameters.
It is commonly used for:
- VPN authentication
- 802.1X Wi-Fi access
- Network device login
- Firewall authentication
LDAP vs RADIUS: Core differences
| Aspect | LDAP | RADIUS |
|---|---|---|
| Primary role | Access and manage directory data | Authenticate and authorize network access |
| Layer | Directory layer | Network access layer |
| Authentication scope | Validates credentials against directory | Grants or denies network access |
| Authorization | Indirect (via group checks) | Direct (VLANs, policy attributes) |
| Accounting | Not supported | Supported (session tracking) |
| Dependency | Requires directory service | Often depends on AD/LDAP for validation |
| Common ports | 389 (LDAP), 636 (LDAPS) | 1812 (auth), 1813 (accounting) |
| Replace each other? | No | No |
Does RADIUS integrate with LDAP?
In many environments, both protocols are part of the same authentication flow.
- The user initiates a VPN connection and enters their credentials.
- The VPN appliance forwards the authentication request to a RADIUS server.
- The RADIUS server validates the credentials against AD.
- During validation, the directory may process an LDAP query (or use Kerberos) to verify identity and retrieve group membership.
- AD confirms whether the user exists and belongs to the appropriate security groups.
- Based on that response, the RADIUS server grants or denies network access.
- If access is granted, RADIUS may also assign session attributes such as VLAN placement or access policies and log the session for accounting purposes.
LDAP provides the identity data. RADIUS enforces the network decision.
This layered approach is common in hybrid work environments and distributed networks.
Real-world use cases
Use case 1:
Imagine a mid-sized company with hybrid employees. Everyone uses internal business applications hosted on-premises. Here's how LDAP and RADIUS show up in that environment.
An employee working from home opens their laptop and connects to the corporate VPN. The VPN appliance sends the authentication request to a RADIUS server. The RADIUS server checks the user's credentials against AD. If the credentials are valid and the user belongs to the allowed security group, access to the corporate network is granted. The session is logged for auditing.
That's RADIUS in action. It controls whether the user is allowed onto the network.
Now that the employee is connected, they open an internal HR application. The application needs to verify the user's identity and determine what they're allowed to see. It performs an LDAP bind against AD to validate credentials and then queries group memberships and attributes like department or role.
That's LDAP in action. It retrieves identity data and enables application-level access decisions.
Later, the same employee walks into the office and connects to corporate Wi-Fi. The wireless access point uses 802.1X authentication and sends the request to the RADIUS server. Based on the user's group membership in AD, the RADIUS server assigns them to the correct VLAN.
Again, RADIUS governs network access. LDAP provides the identity data behind the scenes.
Use case 2:
Does LDAP vs RADIUS still matter in 2026?
Yes, at the protocol level, both are mature and stable. They've been around for decades and continue to power enterprise authentication.
The real issue isn't the protocol. It's the identity layer behind it. Both LDAP and RADIUS depend entirely on directory integrity.
If a user remains in a privileged group after a role change, authentication will still succeed. If dormant accounts remain enabled, they can still be validated. If delegated permissions are misconfigured, network access may be broader than intended.
The protocols are doing their job. The risk lies in unmanaged identities.
In hybrid environments where VPN, Wi-Fi, and applications all rely on directory-backed authentication, small misconfigurations can quietly expand the attack surface.
That's why managing the directory layer matters just as much as configuring the authentication protocol itself.
Strengthen LDAP and RADIUS with ADManager Plus
ADManager Plus supports LDAP and RADIUS by providing centralized AD visibility and management over users, groups, permissions, and delegated access.
Administrators can search and locate objects across the directory, analyze group memberships, review delegated permissions, and detect inactive or over-permissive accounts.
By automating provisioning and deprovisioning, conducting access reviews, and identifying risk exposure, organizations ensure that authentication decisions enforced by LDAP and RADIUS reflect intentional, up-to-date access policies, not legacy configurations.
When governance is strong, LDAP and RADIUS operate predictably and securely.
FAQ
- Is LDAP outdated?
No. LDAP remains widely used in enterprise environments for directory access and application authentication, particularly in on-premises and hybrid infrastructures.
- Is RADIUS authentication still used?
Yes. RADIUS continues to be the standard for VPN, 802.1X Wi-Fi, firewall, and network device authentication.
- Is LDAP being deprecated?
No, LDAP is still supported and widely implemented in enterprise directory services, including AD.
- What are the disadvantages of LDAP?
- LDAP does not provide network-level accounting, VLAN assignments, or session control.
- LDAP focuses on directory communication rather than enforcing network access policies.
- LDAP relies heavily on accurate group memberships and attribute management.
- Poorly structured queries can impact domain controller performance in large environments.
- LDAP also requires secure configuration using LDAPS to protect credentials in transit and does not offer built-in visibility into privilege risk or dormant accounts.
- Is LDAP or RADIUS better?
Neither. They solve different problems.
LDAP is not a replacement for RADIUS. RADIUS is not a replacement for LDAP.
In enterprise architecture, it's whether each is configured properly and backed by clean identity data.














