AWS Elastic Load Balancing (ELB) distributes incoming network and application traffic to multiple EC2 instances. Load balancing in AWS ELB is carried out by by routing network traffic targeting healthy EC2 instances that have the bandwidth to handle incoming requests.
ELB requests are logged along with important details such as:
These logs will be present in the Amazon S3 bucket as ELB access logs. Log360 automatically aggregates these access logs from the S3 bucket and monitors them for:
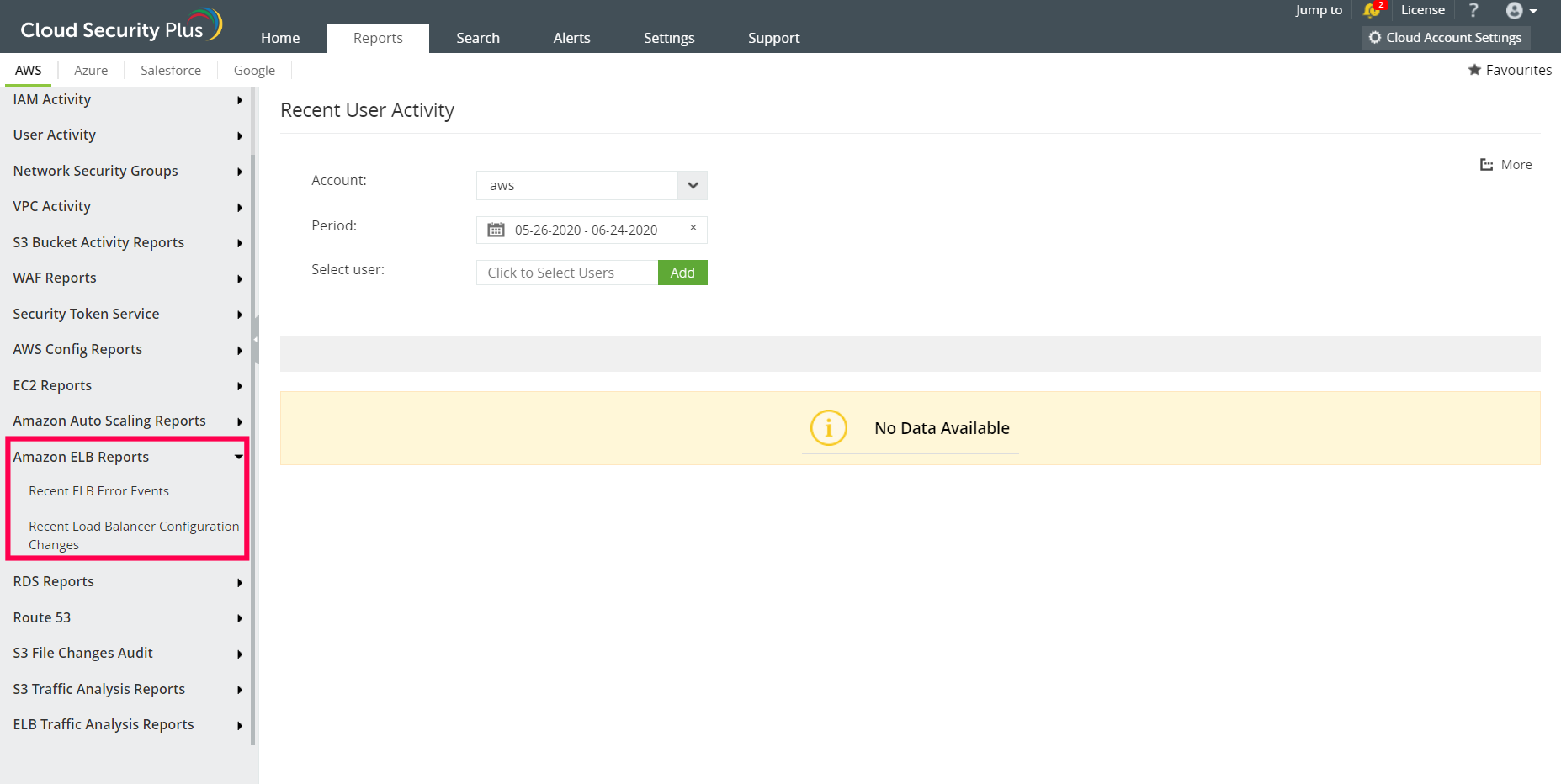
The error events and configuration changes are presented in the form of comprehensive reports for easy interpretation.
Log360 audits AWS ELB access logs to help enterprises comply with IT regulatory mandates. It analyzes the collected AWS ELB access logs and converts them into actionable data by generating intuitive reports. These reports give you insights on:
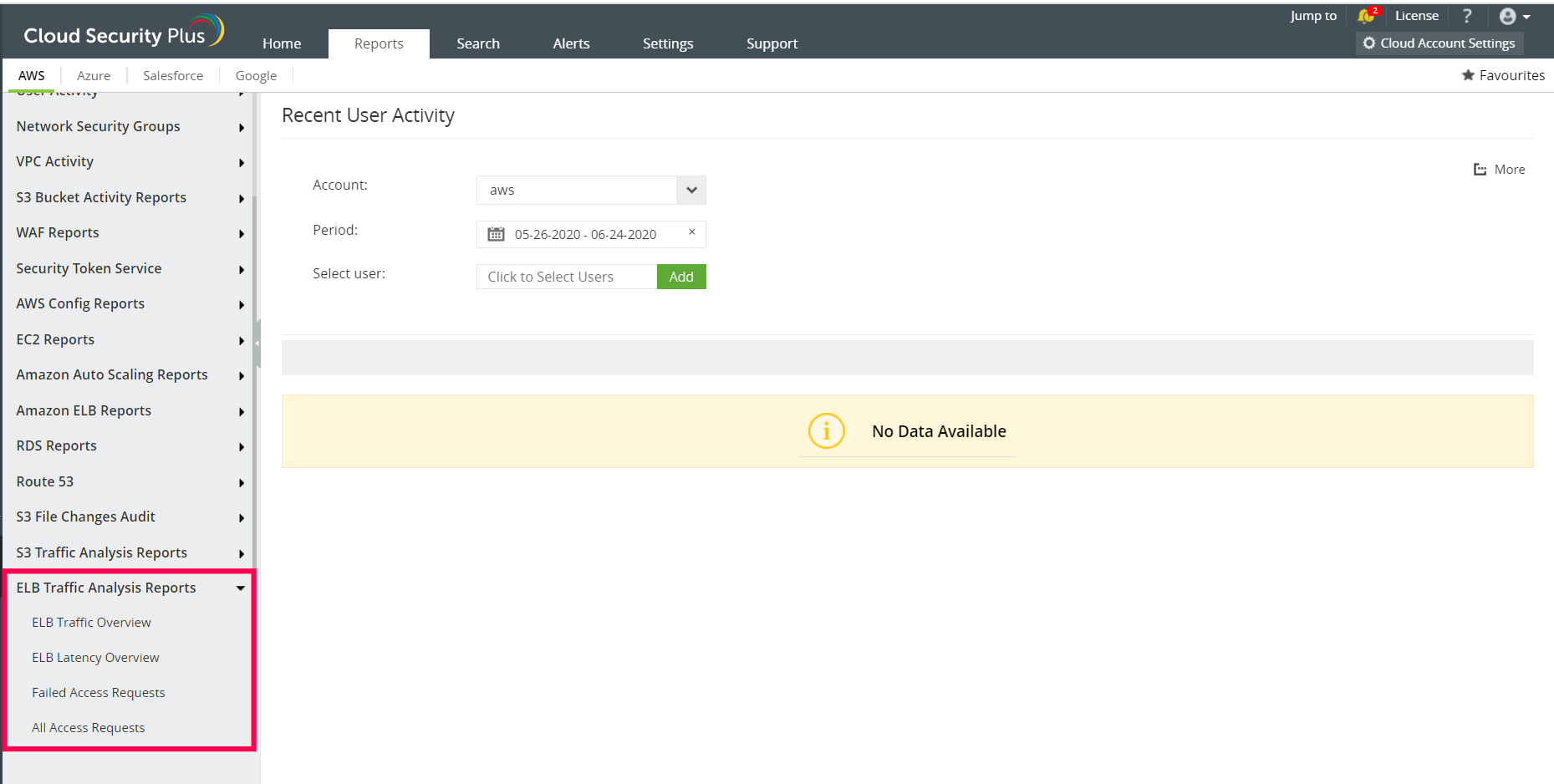
If there are several failed access requests from a particular IP address, this could indicate a potential threat, where either the user is attempting to gain unauthorized access to a critical resource or the user's system has been compromised by malicious actors who are carrying out unwanted activities. Log360 not only flags such incidents as threats, but also enables you to configure alerts for them.
Log360 uses its powerful correlation engine to identify malicious events taking place in any part of your cloud instance. It flags them as threats and allows you to configure real-time alerts to get notified via SMS and email in case of a breach or an attack. You can also enable incident response workflows, where a snippet executes automatically when a threat is spotted to mitigate it and prevent an attack.