Password Manager Pro - Frequently Asked Questions
1. General
- Do I need to install any prerequisite software before using Password Manager Pro?
- What are the operating systems supported by Password Manager Pro?
- Can others see the resources added by me?
- Can I add my own attributes to Password Manager Pro resources?
- What happens if a user leaves the organization without sharing their sensitive passwords with anyone?
- How do I troubleshoot if importing users/resources from AD fails?
- How to make the Password Manager Pro application work with a MySQL database server installed in a separate machine (other than the one in which Password Manager Pro server is running)?
- Can I run custom queries to generate results for integration with other reporting systems?
- Does domain SSO work across firewalls/VPNs?
- Can I rebrand Password Manager Pro with my own logo and organizational information?
- How to fix the "Password Manager Pro detected harmful content in the data entered by the user and aborted the operation" error occurred while importing resources through csv/tsv file?
- Does Password Manager Pro record Password viewing attempts and retrievals by users?
- Why does the size of PostgreSQL wal_archive file increase at a rapid pace?
- What are the various syslog formats followed by Password Manager Pro?
- How do I run the Password Manager Pro service using a group Managed Service Account (gMSA)?
- Does Password Manager Pro alter the number of Windows CAL licenses?
- How do I troubleshoot when the PostgreSQL server fails to start?
- How to add a new Active Directory (AD) domain in Password Manager Pro?
- How to remove a domain from Password Manager Pro?
- How to fix “The list of Groups is too large to display ” or "The list of OUs is too large to display" error while importing from AD?
- Logs, Reports, and CAPTCHA are unreadable after upgrading to Password Manager Pro build 12000. How to fix this issue?
- How to handle the following exceptions that occur while upgrading Password Manager Pro version?
- How to perform version upgrade using the CLI mode?
- What are the standards to be followed for the CSV file used for bulk import?
- How to move a resource/user from one resource/user group to another?
- Does Password Manager Pro allow users to mention the '/admin' option on Windows resources?
- Having trouble upgrading Password Manager Pro from build 11300 to any higher versions?
- How many client organizations does the Password Manager Pro support?
- What are the JDBC drivers supported by Password Manager Pro for database communication?
2. Web Interface and Authentication
- Can I change the default port 7272 where Password Manager Pro is listening?
- How do I change the Password Manager Pro web portal access URL?
- Password Manager Pro is a web-based application that can be accessed via a web browser. Does that mean I can access it from anywhere?
- Can I change the IP address in which Password Manager Pro application is binding when I have multiple NIC cards and IP's available in the server?
- What if my users are not notified of their Password Manager Pro accounts?
- What are the authentication schemes available in Password Manager Pro?
- What are the user roles available in Password Manager Pro? What are their access levels?
- What if I forget my Password Manager Pro login password?
- Why do I sometimes see a security warning while accessing the Password Manager Pro console via the browser?
- How to enforce the users to provide a reason for password retrieval?
3. Browser Extension
- How to use Password Manager Pro browser extension to add website accounts but disable web browsers from storing it under their own password vault? And how to allow only the Password Manager Pro browser extension to store the passwords?
- Having trouble performing auto-logon sessions to the websites added in Password Manager Pro?
4. Security
- How secure are my passwords in Password Manager Pro?
- How secure are Application-to-Application and Application-to-Database password management done through Password Management APIs?
- Can we install our own SSL certificates? (Steps applicable from build 9700 onwards)
- How to generate signed SSL certificates? [OR] How to make the Password Manager Pro server trusted by web browsers and users?
- How do I generate a unique SSL certificate for MySQL server? (Steps applicable from build 6500 onwards)
- Can we create server certificates with SubjectAlternativeName (SAN)?
5. Password Synchronization
- Can I change resource passwords from the Password Manager Pro console?
- When do I use the agent and agent-less modes for password synchronization?
- Can I enable agent less password reset if I add my own resource type for other distributions of Linux ⁄ other versions of Windows?
- Is there a way to carry out remote password synchronization for custom resource types that do not come out of the box in Password Manager Pro?
- How do I troubleshoot when password synchronization does not happen?
- How do I reset domain passwords when Windows domain password reset fails with an error message: "The authentication mechanism is unknown"?
- What are the prerequisites for enabling Windows service account reset?
- Does domain SSO work across firewalls / VPNs?
- How and what are the steps that should be taken by the admin to restrict users from resetting the privileged account passwords from UI?
- How to manage the privileged account passwords of Oracle DB?
- How to handle the following exception that occured during Remote Password Reset?
- Why are the Agents deployed? What is the difference between Agent and Agent-less mode?
- Does Password Manager Pro support Oracle DB? If so, what versions of Oracle DB does the product support?
6. Backup and Disaster Recovery
- Can I move Password Manager Pro from one server to another?
- Why does the Password Manager Pro application fail to start after moving from one server to another?
- Can I setup disaster recovery for the Password Manager Pro database?
- Where does the backup data get stored? Is it encrypted?
7. Licensing
- How is Password Manager Pro licensed?
- What is the Licensing Policy for Password Manager Pro?
- Can I buy a permanent license for Password Manager Pro? What are the options available?
- How to apply my license in Password Manager Pro?
- I want to have a High Availability setup with multiple servers. Will a single license suffice for this?
- Can Password Manager Pro support more than 1000 administrators?
- How many resources and accounts can I manage from the Password Manager Pro application?
- Can I extend my evaluation to include more administrator users or for more number of days?
- Do I have to reinstall Password Manager Pro when moving to Premium or Enterprise Editions?
8. SSH Key Management
- Are there any differences in the way SSH user accounts and SSH service accounts are managed using Password Manager Pro?
- Is there any way to view SSH keys that were not rotated?
- Does Password Manager Pro support management of digital keys other than SSH keys and SSL certificates?
9. SSL Certificate Management
- Is there any certificate type that Password Manager Pro is incompatible with?
- Is it possible to automatically identify and update the latest version of certificates in Password Manager Pro' certificate repository?
- Does the Linux version of Password Manager Pro support certificate discovery from Active Directory and MS Certificate Store?
- Is it possible to track the expiry of certificates with the same common name in Password Manager Pro' certificate repository?
- How do I import private key for a certificate?
- How do I deploy a certificate to Certificate Store and map it to the application that uses the certificate?
- Does Password Manager Pro support subnet based certificate discovery?
- Does Password Manager Pro support automatic scheduling for certificate discovery from MS Certificate Store?
- Are certificate related alert emails generated for all versions of a certificate (the ones that show in "certificate history" also) or only for those certificates listed in Password Manager Pro' certificate repository?
- Are certificates issued by the company's internal Certification Authority (CA) counted for licensing?
- How do I import a root certificate into Password Manager Pro?`
10. High Availability
- Does Password Manager Pro support High Availability?
- How to handle the following exceptions that occur in High Availability?
11. Remote Sessions
- How do I restrict password users from launching RDP auto-logon sessions from Password Manager Pro using their local account?
- How to launch RDP connections over internet and what are the pre-requisites?
- How does RDP work in Password Manager Pro? What are the connection metrics?
- Are the recorded sessions actual videos, or are they compilations of screenshots? How large are these videos typically? How much storage does it typically use?
- What are the steps involved in launching RDP sessions using a domain user account?
1. General
1. Do I need to install any prerequisite software before using Password Manager Pro?
Apart from the standard system requirements (both hardware and software), the following elements are essential for the proper functioning of the Password Manager Pro server.
These are especially required if you are planning to make use of Password Manager Pro's account discovery and password reset provisions.
- An external mail server (SMTP server)for the functioning of Password Manager Pro server and to send various notifications to users.
- A service account [OR] a gMSA that has either domain admin rights or local admin rights in the Password Manager Pro server and in the target systems that you would like to manage.
- Microsoft .NET framework 4.5.2 or above must be installed in the server where Password Manager Pro is installed.
- Microsoft Visual C++ Re-distributable for Visual Studio 2015 and above (for Password Manager Pro's Account Discovery and Password Reset features).
To check if these software requirements are configured:
- Go to Support » Software Requirements and click Check Configuration.
In the pop-up box that opens, the configuration status will be displayed.
2. What are the operating systems supported by Password Manager Pro?
Password Manager Pro supports the following flavors of Windows and Linux operating systems:
| Windows: | Linux: |
|---|---|
Windows Server 2022 |
Ubuntu 9.x and above |
| Windows Server 2019 |
|
Windows Server 2016 |
Red Hat Linux 9.0 |
Windows Server 2012 |
Red Hat Enterprise Linux 7.x |
Windows Server 2012 R2 |
Red Hat Enterprise Linux 6.x |
Windows 8 |
|
| Windows 10 |
- |
3. Can others see the resources added by me?
Except for super administrators (if configured in your Password Manager Pro set up), no one including admin users, will be able to see the resources added by you. However, if you share your resources with other administrators, they will be able to see them.
4. Can I add my own attributes to Password Manager Pro resources?
Yes, you can extend the attributes of the Password Manager Pro resource and user account to include details that are specific to your needs. Refer this document for more details.
5. What happens if a user leaves the organization without sharing their sensitive passwords with anyone?
If an administrative user leaves the organization, they can transfer the resources they own to other administrators. By doing so, they'll have no access to those resources themselves, unless they transfer the resources to themselves. Refer this document for more details.
6. How do I troubleshoot if importing users/resources from AD fails?
- Check if the user credentials are correct.
- If you are trying with an admin user and it fails, try entering the credentials of a non-admin user. This is just to verify if connection could be established properly.
If the above verifications fail, please contact passwordmanagerpro-support@manageengine.com.
7. How to make the Password Manager Pro application work with a MySQL database server installed in a separate machine (other than the one in which Password Manager Pro server is running)?
It is always recommended to run the Password Manager Pro application (built over Tomcat web server) and the MySQL database in the same machine for better security. We have configured the bundled MySQL database so as it is not visible outside the machine in which it is installed (it will accept connections requested only from localhost) and you will lose this aspect when you separate them. If there is a pressing need to run MySQL elsewhere, follow the procedure detailed below:
- Shutdown Password Manager Pro server if it is already running.
- Install MySQL server in a different machine and create a database named 'PassTrix' (the casing is important, particularly in Linux).
- Start the MySQL server and make sure you are able to connect to the database from remote (using the MySQL command line client).
- Make the following configuration changes in Password Manager Pro:
- Go to <PMP_Install_Dir>\conf\Persistence folder.
- Open the file persistence-configurations.xml and search for the entry 'StartDBServer' and set its value to 'false' (default will be 'true'). Save the file.
- Go to <PMP_Install_Dir>\conf folder.
- Open the file database_params.txt and make the following changes:
- In the URL property, change the entries 'localhost' and '5768' to the hostname and port number corresponding to the remote MySQL server.
- If you want to connect as root, leave the username property as it is., else, make appropriate changes to that property. Note that Password Manager Pro requires root privileges in MySQL.
- If you have set a password in the remote MySQL server specify it against the password property. Otherwise remove or comment out that line.
- Save the file.
- Now start the Password Manager Pro server again and it should work with the remote database (which should be already running).
8. Can I run custom queries to generate results for integration with other reporting systems?
Yes, you can. Please contact us at support@passwordmanagerpro.com with your specific request and we will help you with the relevant SQL query to generate XML output.
9. Does domain SSO work across firewalls / VPNs?
The domain Single Sign On (Windows-integrated authentication) is achieved in the Windows environment by setting non-standard parameters in the HTTP header, which are usually stripped off by devices like firewalls / VPNs. Password Manager Pro is designed for use within the network. So, if you have users connecting from outside the network, you cannot have SSO enabled.
10. Can I rebrand Password Manager Pro with my own logo and organizational information?
Yes. Password Manager Pro provides you with the following options for customization and rebranding:
- Using your own logo for web interface the mobile app. (Recommended image size is 210*50 pixels)
- Setting a login page description for the product.
- Changing the default color of the user interface.
- Displaying a banner with customized legal content.
- Customizing a privacy policy content and display an acceptance button for the same.
To carry out the above functionalities:
- Navigate to Admin >> Customization >> Rebrand.
- Under the Logo and Theme section, set up a customized logo and a login page description, and change the default skin tone.
- Under Login Page Text, add policies and/or legal conditions to be displayed in the login page.
Note that at any point, this configuration can be disabled. Click here for more details.
11. How to fix the "Password Manager Pro detected harmful content in the data entered by the user and aborted the operation" error occurred while importing resources through csv/tsv file?
As a security measure, Password Manager Pro restricts certain characters such as HTML tags (< , >), "URL: HTTPS://" or "URL: HTTP://", security mark (?), end line and multiple spaces in the notes or any other fields in Password Manager Pro as it causes security violations in the product. If any of these characters are used in any other fields except password field then, then is causes a violation and the import fails.
To avoid this, verify your CSV/TSV file to ensure these characters are removed for a successful import.
Note: It is advisable to ensure that the resource & account descriptions do not exceed the max limit of 2000 characters.
12. Does Password Manager Pro record Password viewing attempts and retrievals by users?
Yes, Password Manager Pro records all operations that can be possibly performed by an user- including password viewing and copying operations. From audit trails, you can get a comprehensive list of all the actions and attempts by the users with password retrieval. Click here for more details.
13. Why does the size of PostgreSQL wal_archive file increase at a rapid pace?
This issue occurs when the backup location specified in Password Manager Pro is no longer accessible to save the backup file. In simple terms, whenever the PostgreSQL database backup fails, wal_archive folder size will start increasing.
Solution:
- Check if there is enough disk space available on the Password Manager Pro drive.
- If not, remove the logs directory and a few files present inside directory.
- You need to have only one or two backups to be present here.
- Login to Password Manager Pro and navigate to Admin >> Configuration >> Database Backup.
- Click on the 'Backup Now' button.
This will trigger an instant backup and automatically purge the wal_archive directory.
14. What are the various Syslog formats followed by Password Manager Pro?
The following are three different types of syslog formats that Password Manager Pro uses to send syslog messages to your syslog collector host:
i. Resource Audit
operatedName+":"+operatedIp operationType operatedDate statusMess resourceName+":"+accName+":"+reason
ii. User Audit
operatedName+":"+operatedIp operationType operatedDate statusMess auditUserName+":"+reason
SSL: <190> Parent_Domain: manageengine.com Included_Domain: kmp.com Days_to_Expire: 100 Expire_Date: 5.08.2020
SSH: <190> Key_Name:172.21.147.130_test123_id Days_Exceeded:0 Modified_On:2016-02-16 17:41:24.008
15. How do I run the Password Manager Pro service using a group Managed Service Account (gMSA)?
To know in detail about running the Password Manager Pro service using a group Managed Service Account, click here.
16. Does Password Manager Pro alter the number of Windows CAL licenses?
Generally, RDP sessions are invoked from the Password Manager Pro server and relayed to the end user's browser through a third-party component called Spark Gateway. This component comes bundled with Password Manager Pro and does not have any relation to Windows CAL licenses. Hence, Password Manager Pro does not affect the number of Windows CAL licenses in any way. Users need to purchase as many CAL licenses, as suggested by Microsoft.
17. How do I troubleshoot when the PostgreSQL server fails to start?
Error Scenarios:
- During Upgrade:
- While setting up HA:
- During Service Start up:
- Password Manager Pro service start failure after the upgrade.
- Password Manager Pro service start failure after updating the Password Manager Pro service account in Services console.
For the above two cases, do the following:
Open the <PMP-HOME>\logs\wrapper file with notepad/Notepad++ and move to the very bottom of the file (i.e. most recent time frame) and check if we get the 'Trying to start PostgresSQL server failed' error.
'Trying to start PostgresSQL server failed' error in the command prompt after choosing the PPM file.
'Trying to start PostgresSQL server failed' error in the command prompt after executing the HASetup.bat command.
Possible Causes:
The following causes are explained with respect to the above error scenarios:
The 'Trying to start PostgresSQL server failed' error occurs when,
- Password Manager Pro is unable to access few sub-folders inside Password Manager Pro (i.e appropriate permission not given).
- The PostgreSQL DB fails to start because of a background process that was not terminated properly.
- The instant DB port might be occupied by a different process.
Solution:
The solution given below applies to all the above error scenarios. To fix this issue, follow the below steps to provide permission,
- Start the Task Manager and kill all Postgres process (make sure "show process from all users" is selected - For Password Manager Pro).
- Update the Password Manager Pro service with a privileged account in the services console.
- Open command prompt using administrator and execute the below query:
- icacls "installation path" /q /c /t /grant Users:F
- installation path - Provide the Manage_Engine folder location.
- Users - Provide the Password Manager Pro service account in the following format: <DomainName\user name> or <username@domainname>.
- Example: icacls "C:\ProgramFiles\ManageEngine\PMP" /q /c /t /grant ManageEngine\svcpmp:F
- If the key is placed outside the Password Manager Pro folder, kindly provide permission for the key's locations using icacls command.
- In the same way, provide full control permission for <PMP>\pgsql\data folder.
- Check the <PMP_Installation_Directory>/pgsql/data folder and ensure if it has inherited that permission.
- Navigate to <PMP_Installation_Directory>/pgsql/data and open pg_hba.conf and search NULL. If you find any, remove the entire line that contains NULL.
- Rename the logs folder present inside the <PMP_Installation_Directory> as logs.old and create a new folder as logs.
- Rename the Patch folder present inside the <PMP_Installation_Directory> as Patch.old and create a new folder as Patch.
- Navigate to the <PMP_Installation_Directory>/bin directory and look for the files named .lock and lockfile. If present, move both these files to any other directory.
- Go to the <PMP_Installation_Directory>/pgsql/data directory and look for the file named postmaster.pid. If present, move this file to any other directory.
- Now, try to apply the PPM or configure HA or try starting the service.
If the issue still persists, zip and send us the logs from the <PMP_HOME> and also the <PMP-HOME>\pgsql\data\pg_log folder along with the above screen shots to passwordmanagerpro-support@manageengine.com.
18. How to add a new Active Directory (AD) domain in Password Manager Pro?
For Resource Discovery:
- Login as an Administrator and navigate to the Resources tab.
- Click Discover Resources.
- Now, click New Domain link against Select Domain Name.
- Enter the New Domain name and click Add to add the domain.
- Enter the NETBIOS name under New Domain and mention the Primary and Secondary Domain Controller.
- Now, select the connection mode as SSL or Non SSL and select the Supply Credentials.
- If you choose to Specify Username and Password Manually, mention the Username and Password.
- If you choose to Use an account stored in Password Manager Pro, select the Resource Name and Account Name.
- If you choose to Specify Username and Password Manually, mention the Username and Password.
- Click Save.
For User Discovery:
- Login as an Administrator and navigate to Admin >> Authentication >> Active Directory.
- Click Import Now. A pop-up appears on the screen.
- Now, click New Domain link against Select Domain Name.
- Enter the New Domain name and click Add to add the domain.
- Enter the NETBIOS name under New Domain and mention the Primary and Secondary Domain Controller.
- Now, select the connection mode as SSL or Non SSL and select the Supply Credentials.
- If you choose to Specify Username and Password Manually, mention the Username and Password.
- If you choose to Use an account stored in Password Manager Pro, select the Resource Name and Account Name.
- If you choose to Specify Username and Password Manually, mention the Username and Password.
- Click Save.
19. How to remove a domain from Password Manager Pro?
To remove a domain from Password Manager Pro, you have to remove the users that belong to this domain and then follow the below steps to remove the domain information:
- Navigate to Admin >> Authentication >> Active Directory.
- Click View Synchronization Schedules.
- Delete the required domain from the Domains pane on the left.
20. How to fix “The list of Groups is too large to display ” or "The list of OUs is too large to display" error while importing from AD?
To fix this, you will have to increase the number of OUs and groups allowed during the AD import. Follow the below steps:
- Stop the Password Manager Pro service.
- Navigate to the <Password-Manager-Pro-Installation-Directory>\conf folder and take a backup of system_properties.conf.
- Now, open system_properties.conf in Word Pad as an Administrator and do the following:
- Find domain.ou.limit=2500 and change the value to 25000.
- Find domain.group.limit=2500 and change the value to 25000.
- Find domain.ou.limit=2500 and change the value to 25000.
- Save the file and start the service.
21. Logs, Reports, and CAPTCHA are unreadable after upgrading to Password Manager Pro build 12000. How to fix this issue?
Check for the following:
- Open logs and check if you could find the following error:
- javax.servlet.ServletException: javax.servlet.ServletException: java.lang.Error: Probable fatal error:No fonts found.
- Check if you have installed dejavu fonts.
- To install the dejavu fonts, use the following commands:
- RHEL / Centos:
- sudo yum install fontconfig dejavu-sans-fonts dejavu-serif-fonts
- Ubuntu / Debian:
- sudo apt install fonts-dejavu fontconfig
- SLES:
- sudo zypper install dejavu-fonts fontconfig
- RHEL / Centos:
- Now, you have successfully installed the dejavu font in your machine.
- After installing, navigate to the <Password-Manager-Pro-Installation-Directory>/conf folder.
- Open wrapper_lin.conf file and add following property:
wrapper.java.additional.27=-Dsun.java2d.fontpath=<Font Dir Path>
- Copy all the ttf files and paste it under the <Password-Manager-Pro-Installation-Directory>/jre/lib/fonts folder.
- Restart the Password Manager Pro service.
[or]
22. How to handle the following exceptions that occur while upgrading Password Manager Pro version?
Exception #1: Caused by: java.lang.OutOfMemoryError: GC overhead limit exceeded.
- Stop the Password Manager Pro service.
- Take a backup of the <PMP_Installation_Directory> or a VM snapshot.
- Navigate to <PMP installation directory>\bin and open the file Updatemanager.bat using wordpad or notepad++.
- Search for the entry - $JAVA -Xmx100m $JAVA_OPTS -Dtier-type=BE -Djava.library.path=./lib/native -Dtier-id=BE1 -cp $CLASSPATH com.adventnet.tools.update.installer.UpdateManager -u conf $*
- Change the value to $JAVA -Xmx2048m $JAVA_OPTS -Dtier-type=BE -Djava.library.path=./lib/native -Dtier-id=BE1 -cp $CLASSPATH com.adventnet.tools.update.installer.UpdateManager -u conf $*
- Save the file.
- Start the Password Manager Pro service and try the upgrade.
If issue persists, please share your logs to passwordmanagerpro-support@manageengine.com
Exception #2: Trying to start PostgresSQL server failed
- Stop the Password Manager Pro service.
- Kill any Postgres or pmp.exe process using task manager.
- Exit the Password Manager Pro tray icon.
- Run Password Manager Pro service account using a privileged account. And give this account <Password-Manager-Pro-Installation-Directory> full and manage folder permission.
- Open command prompt using the privileged account.
- Proceed with the upgrade.
23. How to perform version upgrade using the CLI mode?
Windows:
- Stop the Password Manager Pro service.
- Open command prompt with administrator privileges.
- Navigate to <PMP_Installation_Directory>/bin and execute:
UpdateManager.bat -u conf -c -option i
- Mention the .ppm file location in the next line.
- Enter to proceed with the upgrade.
Linux:
- Stop the Password Manager Pro service.
- Open command prompt with administrator privileges.
- Navigate to <PMP_Installation_Directory>/bin and execute:
UpdateManager.sh -u conf -c -option i -ppmPath <Path_Of_The_ppm_file>
Eg: UpdateManager.sh -u conf -c -option i -ppmPath c:\pmp.ppm
- Enter to proceed with the upgrade
Click here for detailed upgrade pack instructions.
24. What are the standards to be followed in the CSV file used for bulk import?
All the lines in the CSV file should be consistent and have the same number of fields. The entries in the file should be comma separated values. Enter the attribute values for each user in separate lines in the same order. If you do not wish to specify the value for an attribute, add a comma and proceed.
25. How to move a resource/user from one resource/user group to another?
You cannot move resources/users from one resource/user group to another resource/user group. Alternatively, you can remove and add the resources/user from one group to another. To remove a resource from a resource group follow the below steps:
Note: A resource/user can be a part of multiple resource/user groups.
To add or remove resources from a resource group:
- Navigate to the Groups tab.
- Besides the desired resource group, click the Associate Resources icon.
- In the pop-up that appears, click Remove to remove the resources from that particular resource group or click Add to Group to add the resource to the resource group.
To add or remove users from a user group:
- Navigate to Users >> User Groups.
- Besides the desired user group, click the Associate Users icon.
In the pop-up that appears, click 'Remove' to remove the users from that particular user group or click 'Add to Group' to add the users to the user group.
26. Does Password Manager Pro allow users to mention the '/admin' option on Windows resources?
Yes, Password Manager Pro Console Session uses '/admin' option.
- Add an RDS server with the resource type "Windows". Make sure the RDS Server has some user accounts.
- Now, click the Open Connection icon beside the required account and select RDP Console Session.
27. Having trouble upgrading Password Manager Pro from build 11300 to higher versions?
Note: Always ensure that the Antivirus and Antimalware softwares are disabled while performing the upgrade.
- If you have any dedicated Password Manager Pro service account, log in to the Password Manager Pro machine using that service account and make sure the service account has full permissions over the Password Manager Pro folder.
- If the service account doesn't have full folder permission to Password Manager Pro folder, open command prompt as an administrator and execute the following command:
- icacls "<PMP installation directory>" /grant <PMPserviceaccountname>:(OI)(CI)F /T
- Example: icacls " C:\ManageEngine\PMP " /grant PMP-svc@domain.com:(OI)(CI)F /T
- If the service account doesn't have full folder permission to Password Manager Pro folder, open command prompt as an administrator and execute the following command:
- Open command prompt as an administrator, navigate to the <Password-Manager-Pro-Installation-Directory>\bin folder and execute,
- Navigate to <Password-Manager-Pro-Installation-Directory> and rename the Patch folder to Patch.old.
- Now, follow the steps in this document to continue with the Password Manager Pro upgrade.
28. How many client organizations does the Password Manager Pro support?
As of now, Password Manager Pro is equipped to support up to 900 client organizations.
29. What are the JDBC drivers supported by Password Manager Pro for database communication?
Microsoft's JDBC driver is the default driver selected during database configuration of Password Manager Pro and is recommended for most installations as it is compatible with the latest SQL server versions and features. The alternative JDBC driver for the Microsoft SQL server is jTDS, which supports specific compatibility features.
(Applicable from build 13100 onwards)
Note: By default, Microsoft's JDBC driver will act as the default driver for connection between MS SQL/Azure MS SQL server and database. If you have configured jTDS as the database driver earlier, perform the below steps:
- Navigate to the <Password-Manager-Pro-Installation-Directory>/bin folder and execute the ChangeDB.bat (Windows) command or sh ChangeDB.bat (Linux).
- In the pop-up that opens, read the Best Practices Guide and click the Continue with setup button to open the DB Change Configuration window.
- In the Host Name field, enter the hostname, i.e., the Common Name of the MS SQL server specified in the server certificate.
- In the Database Name field, enter the database name of the MS SQL server as specified in the database_params.conf file.
- Input all the remaining essential fields and click Test. To learn more about each essential field, refer to this help document.
- Upon a successful test result, click Save.
2. Web Interface and Authentication
1. Can I change the default port 7272 where Password Manager Pro is listening?
Yes, you can change the default port as explained below:
- Login to Password Manager Pro as an Administrator. Navigate to Admin >> Configuration >> Password Manager Pro Server.
- Enter the required port beside the Server Port field, and click Save.
- Restart Password Manager Pro for this configuration to take effect.
2. How do I change the Password Manager Pro web portal access URL?
- Login as an Administrator and navigate to Admin >> Settings >> Mail Server Settings.
- In the pop-up that appears, click the spectate icon beside the Access URL.
- Mention the Access URL and click Save.
3. Password Manager Pro is a web-based application that can be accessed via a web browser. Does that mean I can access it from anywhere?
Password Manager Pro is an on-premise tool installed in a physical server or virtual machines (VM). You can access Password Manager Pro web portal from any machine on the network connected to the same LAN network using the web browsers.
4. Can I change the IP address in which Password Manager Pro application is binding when I have multiple NIC cards and IP's available in the server?
Password Manager Pro comes bundled with a tailored version of TomCat webserver which allows users to access the webpage and also the JVM which performs the product operations. You can use the below steps to configure the Bind IP address for both these components.
Steps for changing webserver bind IP
- Stop the Password Manager Pro service.
- Navigate to <PMP installation folder>/conf directory and take a backup of the file named server.xml.
- Open Wordpad as an administrator and open server.xml under <PMP installation folder>/conf directory.
- Look for the port="7272" and add the entry address="<IP addresses of the application server>" next to it.
- Save the file.
- Start the Password Manager Pro service. This time the Tomcat webserver will start using the bind IP that you have specified.
- Stop the Password Manager Pro service.
- Navigate to <PMP installation folder>/conf directory and take a backup of the file named wrapper.conf.
- Open Wordpad as an administrator and open wrapper.conf under <PMP installation folder>/conf directory.
- Now, rename <PMP installation folder>/logs folder to logs_older and start the Password Manager Pro service.
- Connect to the login page and try using the product features such as Password reset. The source IP for these operations will be the IP Address that you have configured.
5. What if my users are not notified of their Password Manager Pro accounts?
In general, users are notified of their Password Manager Pro accounts only through emails. If a user does not get the notification emails, verify:
- if you have configured the mail server settings properly, with the details of the SMTP server in your environment.
- if you have provided valid credentials as a part of mail server settings, as some mail servers require the same for mails to be received.
- if the 'Sender E-Mail ID' is properly configured, as some mail servers reject emails sent without the From address or mails originating from unknown domains.
6. What are the authentication schemes available in Password Manager Pro?
You can use one of the following three authentication mechanisms out of Password Manager Pro:
- Active Directory: When enabled, the authentication request is forwarded to the configured domain controller and based on the result, the user is allowed or denied access into Password Manager Pro. The user name, password and the domain are supplied in the Password Manager Pro login screen. This scheme works only for users whose details have been imported previously from AD, and is available only when the Password Manager Pro server is installed on a Windows system.
- LDAP Directory: When enabled, the authentication request is forwarded to the configured LDAP directory server and based on the result, the user is allowed or denied access into Password Manager Pro. The username, password and the option to use LDAP authentication are supplied in the Password Manager Pro login screen. This scheme works only for users whose details have been imported previously from the LDAP directory.
- Password Manager Pro Local Authentication: The authentication is done locally by the Password Manager Pro server. Irrespective of AD or LDAP authentication being enabled, this scheme is always available for the users to choose in the login page. This scheme has a separate password for users and the AD or LDAP passwords are never stored in the Password Manager Pro database. However, for security reasons, we recommend that you disable the local authentication for users after enabling AD/LDAP authentication. For more information on this, refer to the 'User on-boarding and management' section in our best practices guide.
- Entra ID: Once you integrate Password Manager Pro with Entra ID in your environment, you can allow users to use their Entra ID credentials to log in to Password Manager Pro in both Windows and Linux platforms. To use this authentication, Password Manager Pro should first be added as a native client application in your Microsoft Azure portal
- Smartcard Authentication: Enabling this feature will mandate users to possess a smartcard, and also know their Personal Identification Number (PIN). Note that smartcard authentication will bypass other first factor authentication methods like AD, LDAP or Local Authentication.
- RADIUS Authentication: You can integrate Password Manager Pro with RADIUS server in your environment and use RADIUS authentication to replace the local authentication provided by Password Manager Pro. The users who will be accessing Password Manager Pro using their RADIUS server credentials will have to be added as users in Password Manager Pro first. When you do so, you need to ensure that the "username" in Password Manager Pro is the same as the username used for accessing the RADIUS server.
- SAML SSO: Password Manager Pro acts as the Service Provider (SP) and it integrates with Identity Providers (IdP) using SAML 2.0. The integration basically involves supplying details about SP to IdP and vice-versa. Once you integrate Password Manager Pro with an IdP, the users have to just login to the IdP and then, they can automatically login to Password Manager Pro from the respective IdP's GUI without having to provide the credentials again. Password Manager Pro supports integration with Okta, AD FS, and Entra ID SSO.
Note:
For SAML SSO authentication, the Assertion Consumer URL is the hostname of the server, by default. To update the Assertion URL, follow the below steps:
- Go to Admin >> Settings >> Mail Server Settings.
- Under Access URL, update the required URL and click Save.
Now, the Assertion Consumer URL under Service Provider Details will be updated.
7. What are the user roles available in Password Manager Pro? What are their access levels?
Password Manager Pro comes with five pre-defined roles:
Apart from these default roles, any administrator can be promoted as a "Super Administrator" with the privilege to view and manage all the resources. Click here for details on the access levels of the default roles.
8. What if I forget my Password Manager Pro login password?
Note: Show 'Forgot Password' option in the login screen should be enabled under Admin >> General Settings >> User Managerment.
If you were already given a valid Password Manager Pro account,
- Click the 'Forgot Password?' link available in the login page to reset your password.
- In the pop-up that appears,
- Enter the Username and the corresponding Email Id.
- Click Reset to send a password reset link to the configure Email.
- Open your email and find the email containing the password reset link and click on the link.
- Now, Password Manager Pro will send a One Time Password (OTP) to the configured email.
- Use this One Time Password along with the Username and choose Local Authentication in the Domain name drop down menu to login.
- Password Manager Pro will prompt you to reset your password. Mention the One Time Password under Old Password and enter the New Password.
- Click Save.
You have successfully reset your Password Manager Pro password.
9. Why do I sometimes see a security warning while accessing the Password Manager Pro console via the browser?
The Password Manager Pro web console always uses the HTTPS protocol to communicate with the Password Manager Pro server. The Password Manager Pro server comes with a default self-signed SSL certificate, which the standard web browsers will not recognize, thereby issuing a warning. You can ignore this warning while you're testing or evaluating the product. However, if you're rolling it out in production, we recommend that you install an SSL certificate bought from an authorized Certificate Authority (CA) that is recognized by all standard web browsers. Know More
10. How to enforce the users to provide a reason for password retrieval?
Global level settings:
- Navigate to Admin >> Settings >> General Settings.
- Check the option "Enforce users to provide reason for password retrieval" and click Save.
User group level settings:
- Navigate to Users >> User Groups.
- Select the required user group and click Actions >> User Group Privileges.
- Under Password Retrieval, select the checkbox "Enforce users to provide reason for password retrieval" and click Save.
Note: If the user is the part the multiple user group, you will have to enable this option in all the other user groups.
3. Browser Extension
1. How to use Password Manager Pro browser extension to add website accounts but disable web browsers from storing it under their own password vault? And how to allow only the Password Manager Pro browser extension to store the passwords?
To disable the browser from prompting to save the passwords, you have to configure settings in the add-on end and also turn this OFF in your browser's settings.
In Chrome:
- Open Chrome menu and navigate to Settings >> Autofill >> Passwords.
- Turn off Offer to save passwords.
In FireFox:
- Open the Firefox menu and navigate to Settings >> Privacy & Security.
- Disable Ask to save logins and passwords for websites.
Password Manager Pro Browser Extension:
- Login to Password Manager Pro add-on and click Settings at the top right corner.
- Enable Prevent browser from prompting to save passwords.
- Disable Prevent Extension from Prompting to Add Accounts and click Save.
2. Having trouble performing auto-logon sessions to the websites added in Password Manager Pro
To allow auto fill & auto submit of web site accounts, please make sure the below options are enabled in the Password Manager Pro UI.
Global Settings:
- Log in as an administrator and navigate to Admin >> Settings >> General Settings >> User Management.
- Enable Allow website auto-fill actions using browser extensions and Allow website auto-logon actions using browser extensions.
User Group level settings:
- Navigate to the Users tab and click the User Groups option at the top.
- Now, click on the Actions icon against the user group and select User Group Privileges.
- In the pop up window that appears, Enable Allow website auto-fill actions using browser extensions and Allow website auto-logon actions using browser extensions are checked.
Note: We do not support Auto fill and Auto Login for a flash based websites, some internal websites, web pages that uses basic authentication and websites with .hta access authentication.
4. Security
1. How secure are my passwords in Password Manager Pro?
Ensuring secure storage of passwords and offering solid defense against intrusion are the top priorities of Password Manager Pro. The following measures ensure high level security for your passwords:
- Passwords are encrypted using Advanced Encryption Standard (AES), and stored in the database. AES is currently the strongest encryption algorithm known, and has been adopted as an encryption standard by the U.S. Government.
- The database which stores all the passwords accepts connections only from the host that it is running on, and is not visible externally.
- Role-based, fine-grained user access control mechanism ensures that users can view and access passwords only based on the permissions granted to them.
- All transactions between the Password Manager Pro console and the server take place through HTTPS.
- Password Manager Pro's in-built password generator helps you generate strong passwords.
For detailed information, refer to our Security Specifications document.
2. How secure are Application-to-Application and Application-to-Database password management done through Password Management APIs?
Password Manager Pro offers RESTful APIs and SSH-based CLI APIs that can be used for Application-to-Application/Database password management. The applications connect and interact with Password Manager Pro through HTTPS. An application's identity is verified first by verifying the validity of its SSL certificate, and then by verifying the source IP/hostname in which it resides. Each application/database must be registered as an API User in Password Manager Pro. During this registration, the hostname/IP of the application server has to be supplied and a unique authentication token that uses the REST API will be generated. This token needs to be sent along with the API requests for authentication. In addition to these security checks, each application/database can only access the information that are explicitly delegated to them by an administrative user. Refer to this document to know more about sharing/delegating passwords.
3. Can we install our own SSL certificates?
Password Manager Pro uses Tomcat web server and it supports only certificates with the following formats - .keystore / .pfx/ .p12. If your certificate is in one of the above formats, please make use of the below steps to apply the certificate:
Note: The below steps are applicable for builds 9700 and above only.
- Navigate to Admin >> Configuration >> Password Manager Pro Server.
- Choose the Keystore Type as JKS, PKCS12 or PKCS11, whichever you chose while generating the CSR.
- Browse and upload the Keystore File.
- Enter the same Keystore Password, you entered while generating the CSR.
- Modify the Server Port, if required.
- Hit Save. Restart the Password Manager Pro service once, for the certificate change to take effect.
If you are able to access the Password Manager Pro login page without any warning from the browser, you have successfully installed your SSL certificate.
Note: The below steps are applicable for builds below 9700 only.
In older versions, to install a SSL certificate, the changes have to be done on two different files:
server.xml:
- Place the certificate file inside <PMP_Home>/conf folder.
- Open the file server.xml under <PMP_Home>/conf using Wordpad/Notepad++.
- Search for the entry keystoreFile which has default value set to conf/server.keystore.
- Change the value to conf/<Name_Of_SSL_Certificate>.
- Update the Keystore type (JKS for .keystore file, PKCS12 for .p12 & .pfx file)
- Enter the keystore password and save the file.
gateway.conf:
- Open the file gateway.conf under <PMP_Home>/conf using a wordpad/ notepad++.
- Search for the entry Djavax.net.ssl.keyStore and enter the SSL certificate path.
- Search the value Djavax.net.ssl.keyStorePassword=passtrix and replace passtrix with the actual keystore password created while configuring the SSL certificate.
- Search the value wrapper.java.additional.23=-Djavax.net.ssl.keyStoreType=JKS and type in Keystore Type (JKS for .keystore file, PKCS12 for .p12 & .pfx file ).
- Enter the Keystore Filename as server.keystore and the keystore password.
- Restart the Password Manager Pro service.
You have successfully installed your SSL certificate in Password Manager Pro.
4. How to generate signed SSL certificates?
[OR]
How to make the Password Manager Pro server trusted by web browsers and users?
Password Manager Pro runs as a HTTPS service. It requires a valid CA-signed SSL certificate with the principal name as the name of the host on which it runs. By default, on first time startup, it creates a self-signed certificate, which will not be trusted by the user browsers. Thus, while connecting to Password Manager Pro, you need to manually verify the certificate information and the host name of Password Manager Pro server carefully and should force the browser to accept the certificate.
To make the Password Manager Pro server trusted by web browsers and users:
- Obtain a new signed certificate from a CA for the Password Manager Pro host. [OR]
- Configure an existing certificate obtained from a CA with wild-card principal support for the Password Manager Pro host.
There are different ways to generate the signed SSL certificates:
- By using the "Certificate Management" module of Password Manager Pro.
- By using the OpenSSL or Keytool (bundled with Java) to create your certificates, get them signed by a CA and use them with Password Manager Pro.
- By installing a wild card certificate.
You can decide the mode of generating the signed SSL certificates based on what your security administrators recommend. The detailed steps for using each of the above methods are provided under the links below.
Note: If you already have a certificate signed by a CA, then we recommend using OpenSSL to create the keystore and configure it in Password Manager Pro (steps 4 and 5 in the instructions below).
- Generating Signed SSL certificates using the Certificate Management module of Password Manager Pro
- Generating Signed SSL certificates using OpenSSL
- Generating Signed SSL certificates using Keytool
- Generating Signed SSL certificates by installing a wild card certificate
1. Generating Signed SSL certificates using the Certificate Management module of Password Manager Pro
You can generate signed SSL certificates through the Certificate Management module of Password Manager Pro and also apply the certificate changes (Certificate Keystore) directly from the Password Manager Pro console. This involves three processes:
1.1 Generating a Certificate Signing Request (CSR):
To request and acquire certificates from a Local CA through Password Manager Pro, you need to first generate a Certificate Signing Request (CSR). Here are the steps for the same:
- Navigate to the "Certificates >> Create CSR".
- Click the Create button. The Create CSR page is displayed.
- Select either of the options Create CSR or Create CSR From KeyStore, based on whether you want to create a new CSR or create a CSR from an already existing private key, respectively.
- If you have selected Create CSR, fill in the details, such as Common Name, SAN, Organization Unit, Organization Location, State, Country, Key Algorithm and Key Size. Select the Key Algorithm and Keystore Type. Enter the Validity and Store Password.
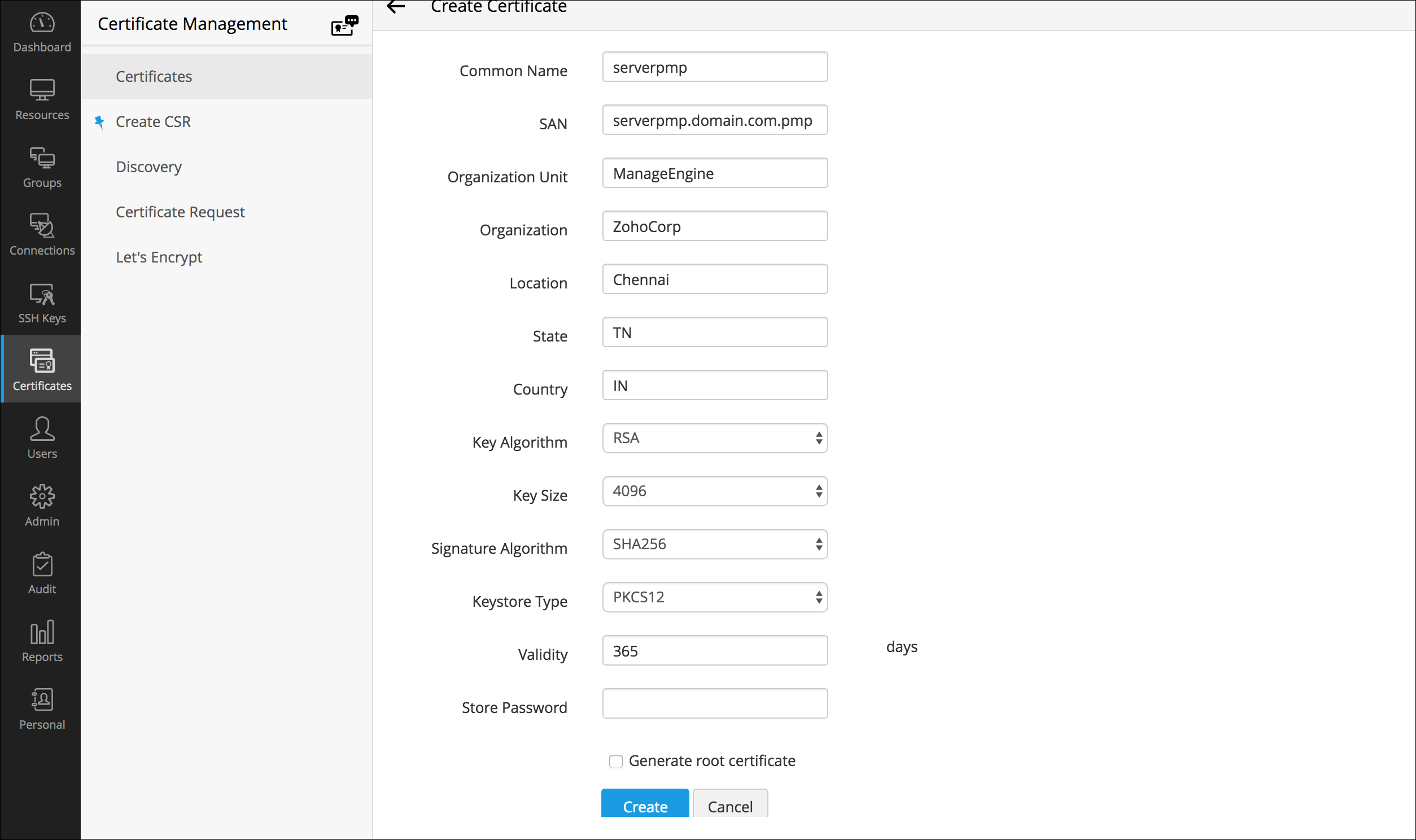
- If you have selected Create CSR From KeyStore, browse and attach the required private key file along with the Private Key Password.
- If you have selected Create CSR, fill in the details, such as Common Name, SAN, Organization Unit, Organization Location, State, Country, Key Algorithm and Key Size. Select the Key Algorithm and Keystore Type. Enter the Validity and Store Password.
- Click the Create button. You will be redirected to a window where the CSR content is displayed. You can copy the CSR content or export it to a mailbox.
- Email – Select this option to send the certificate file via email to the specified mail id.
- Export CSR / Private Key - Select this option to export the CSR or the corresponding private key alone based on your requirement.
- View the saved CSRs under Certificates >> Create CSR.
Note: The 'show passphrase' eye icon corresponding to each CSR allows the administrators to view the KeyStore passwords of the CSR files.
1.2 Signing the Certificate:
Password Manager Pro provides the option to sign and issue certificates to all clients in your network either from your Microsoft Certificate Authority or using a custom root CA certificate that is trusted within your environment.
Note: Remember, you should have generated a valid Certificate Signing Request (CSR) before getting your certificate signed from the local CA.
Follow the below steps to sign the certificate:
- Navigate to Certificates >> Create CSR.
- Select the required CSR from the table and click Sign from the top menu.
- In the pop-up window displayed, provide the name of the server that runs the internal certificate authority, CA Name and choose the certificate template based on your requirement. Click Sign Certificate. The CSR is signed now and the issued certificate can be viewed under "Certificates >> Certificates".
1.3 Applying the Certificate Keystore for Password Manager Pro web server:
To apply the certificate Keystore, first you need to create it.
- Navigate to Certificates >> Certificates. Click the signed certificate link under the heading Common Name. In the certificate details page displayed, click the Export icon present at the top right corner of the screen. The certificate file will be downloaded to your local machine.
- Now, navigate to Certificates >> Create CSR.
- Click the Import Certificate icon corresponding to the CSR of the signed certificate. Browse and choose the certificate file downloaded in your local machine and click Import. Now, the certificate will be bonded with the private key to form a Keystore.
- Now navigate back to Certificates >> Certificates and click the certificate link under the heading Common Name. In the certificate details page displayed, scroll down and click the Export link. This will download the certificate Keystore to your local machine.
- The final step is to navigate to Admin >> Configuration >> Password Manager Pro Server and do the following:
- Choose the Keystore Type as JKS, PKCS12 or PKCS11, whichever you chose while generating the CSR.
- Browse and upload the Keystore File.
- Enter the same Keystore Password, you entered while generating the CSR.
- Modify the Server Port, if required.
- Hit Save. Restart the Password Manager Pro service once, for the certificate change to take effect.
OpenSSL mostly comes bundled with the Linux distributions. If you are using the Windows server and do not have OpenSSL installed, download it from http://www.slproweb.com/products/Win32OpenSSL.html. Make sure the 'bin' folder under the OpenSSL installation is included in the 'PATH' environment variable.
2.1 Create the public-private key pair that will be used for the SSL handshake
- Open the command prompt.
- Execute 'openssl genrsa -des3 -out <privatekey_filename>.key 1024'
- You will be prompted to enter a pass-phrase for the private key. Enter 'passtrix' or a pass-phrase of your choice. (Though it is not documented, Tomcat has issues with passwords containing special characters, so use a password that has only alpha characters)
- A file will be created in the name <privatekey_filename>.key in the same folder.
<privatekey_filename> is the filename you specify to store the private key.
2.2 Create a Certificate Signing Request (CSR) for submission to a certificate authority to create a signed certificate with the public key generated in the previous step
- Execute 'openssl req -new -key <privatekey_filename>.key -out <certreq_filename>.csr'
- <privatekey_filename>.key is the one used in the previous step.
- <certreq_filename>.csr is the filename you specify to carry the certificate creation request to the CA (certificate authority).
- You will be prompted to enter a series of values that are part of the distinguished name (DN) of the server hosting Password Manager Pro.
- Enter values as required. Importantly, for the Common Name supply the fully qualified name of the server hosting Password Manager Pro (with which it will be accessed through the browsers).
- A file will be created in the name <certreq_filename>.csr in the same folder.
2.3 Submit the CSR to a Certificate Authority (CA) to obtain a CA signed certificate
Some of the prominent CAs are Verisign, Thawte, RapidSSL. Check their documentation / website for details on submitting CSRs and this will involve a cost to be paid to the CA. This process usually takes a few days time and you will be returned your signed SSL certificate and the CA's root certificate as .cer files. Save them both in the same working folder where files from steps 1 and 2 are stored
2.4 Import the CA-signed certificate to a keystore
- Open command prompt and navigate to the same working folder.
- Execute 'openssl pkcs12 -export -in <cert_file>.cer -inkey <privatekey_filename>.key -out <keystore_filename>.p12 -name Password Manager Pro -CAfile <root_cert_file>.cer -caname Password Manager Pro -chain'
where,
- cert_file.cer is the signed SSL certificate with the .cer extension.
- privatekey_filename.key is the private key file with a .key extension.
- keystore_filename.p12 name is the keystore that will be generated with a .p12 extension.
- root_cert_file.cer is the CA's root certificate with a .cer extension.
- When prompted for a password, enter the same password, you used in step 1 for the private key. This requirement is due to an inherent limitation in tomcat, which requires the two passwords to match.
- Now, a keystore file in the name <keystore_filename>.p12 will be generated in the same folder.
2.5 Configure the Password Manager Pro server to use the keystore with your SSL certificate
This is the final step in generating Signed SSL certificates using OpenSSL.
- Copy the <keystore_filename>.p12 generated in step 4 to the <Password Manager Pro_Install_Folder>\conf folder.
- Open command prompt and navigate to the <Password Manager Pro_Install_Folder>\conf folder.
- Open the file server.xml and do the following changes:
- Search for the entry 'keystoreFile', which will have the default value set to 'conf/server.keystore'. Change the value to 'conf/<keystore_filename>.p12'.
- Starting from version 9700, the keystore password is encrypted and cannot be updated directly in the server.xml file.In order to manuallyupdate the keystore password in the .xml file, disable the encryption first,bychanging the value'keystorePassEncrypted=true'to 'keystorePassEncrypted=false'.
Note: This step is applicable for builds 9700 and above only.
- Now, set the value of 'keystorePass' to "passtrix" or the password you specified in the previous step while creating the keystore.
- Add a new entry keystoreType= PKCS12 or PKCS11 next to the keystorePass entry.
- Save the server.xml file.
- Restart the Password Manager Pro server and connect through the web browser. If you are able to view the Password Manager Pro login console without any warning from the browser, you have successfully installed your SSL certificate in Password Manager Pro.
3. Generating Signed SSL certificates using Keytool
3.1 Create the public-private key pair that will be used for the SSL handshake
- Go to the <Password Manager Pro_Home>/jre/bin folder.
- Execute the command:
For Windows:
.\keytool -genkey -alias PasswordManagerPro -keyalg RSA -sigalg SHA256withRSA -keypass <privatekey_password> -storepass <keystore_password> -validity <no_of days> -keysize 2048 -keystore <keystore_filename>
For Linux:
./keytool -genkey -alias PasswordManagerPro -keyalg RSA -sigalg SHA256withRSA -keypass <privatekey_password> -storepass <keystore_password> -validity <no_of days> -keysize 2048 -keystore <keystore_filename>
where,
<keystore_password> is the password to access the keystore, <privatekey_password> is the password to protect your private key. Note that due to an inherent limitation in tomcat, these two passwords have to be the same. (Though it is not documented, Tomcat has issues with passwords containing special characters, so use a password that has only alpha characters)
<no_of_days> is the validity of the key pair in number of days, from the day it was created - The above command will prompt you to enter details about you and your organization.
- For the 'first and the last name', enter the FQDN of the server where Password Manager Pro is running.
- For other fields, enter the relevant details.
- A keystore file will be created in the name <keystore_filename> in the same folder, with the generated key pair.
3.2 Create a Certificate Signing Request (CSR) for submission to a certificate authority to create a signed certificate with the public key generated in the previous step
- Go to the <Password Manager Pro_Home>/jre/bin folder.
- Execute the command: "keytool -certreq -keyalg RSA -alias PasswordManagerPro -keypass <privatekey_password> -storepass <keystore_password> -file <csr_filename> -keystore <keystore_filename> -ext san=dns:<hostname.domain.com>,dns:<hostname>,dns:<alias.domain.com>".
Note: The <csr_filename> that you choose should have the .csr extension.
- A CSR file in the name <csr_filename> will be created in the same folder.
3.3 Submit the CSR to a Certificate Authority (CA) to obtain a signed certificate
Some of the prominent CAs are Verisign (http://verisign.com), Thawte (http://www.thawte.com), RapidSSL (http://www.rapidssl.com). Check their documentation / website for details on submitting the CSRs. Please note that this is a paid service. This process usually takes a few days of time. You will receive your signed SSL certificate and the CA's certificate as .cer files. Save both the files in the <Password Manager Pro_Home>/jre/bin folder.
3.4 Import the CA-signed certificate to the Password Manager Pro server
- Go to the <Password Manager Pro_Home>/jre/bin folder using command prompt.
- If you have a single file as the certificate bundle(p7b), then run the below command:
"keytool -import -alias PasswordManagerPro -keypass <privatekey_password> -storepass <keystore_password> -keystore <keystore_filename> -trustcacerts -file <your_ssl_bundle.p7b>"
where,
- <boundlessness> is the certificate bundle obtained from the CA, a .p7b file saved in the previous step. The <privatekey_password>,<keystore_password> and <keystore_filename> are the ones used in the previous steps.
- If you have 3 files, the root, the intermediate and the actual certificates in .cer format, then you need to import each one of them using the below commands.
- "keytool -import -alias root -keypass <privatekey_password> -storepass <keystore_password> -keystore <keystore_filename> -trustcacerts -file <rooter>"
- "keytool -import -alias inter -keypass <privatekey_password> -storepass <keystore_password> -keystore <keystore_filename> -trustcacerts -file <inter.cer>"
- "keytool -import -alias Password Manager Pro -keypass <privatekey_password> -storepass <keystore_password> -keystore <keystore_filename> -trustcacerts -file <your_ssl_cert.cer>"
- Now, copy the <keystore_filename> to the <Password Manager Pro_Home>/conf folder.
3.5 Configure the Password Manager Pro server to use the keystore with your SSL certificate
This is the final step in generating Signed SSL certificates using Keytool.
- Go tothe <Password Manager Pro_Home>/conf folder.
- Open the fileserver.xml.
- Search for the entry 'keystoreFile', which will have the default value set to "conf/server.keystore". Change the value to "conf/<keystore_filename>", where <keystore_filename> is the one used in the previous steps.
- Starting from version 9700, the keystore password is encrypted and cannot be updated directly in the server.xml file.In order to manually update the keystore password in the.xml file, disable the encryption first, bychanging the value 'keystorePassEncrypted=true' to 'keystorePassEncrypted=false.
Note: This step is applicable only if you're using the version 9700 or above.
- Set the value of 'keystorePass' to "passtrix" or the password you specified in the previous step while creating the keystore.
- Restart the Password Manager Pro server and connect through the web browser. If youare able to view the Password Manager Pro login console without any warning from the browser, you have successfully installed your SSL certificate in Password Manager Pro.
Note: Tomcat, by default, accepts only the JKS (Java Key Store) and PKCS #12 format keystores. In case, the keystore is of PKCS #12 format, include the following option in the server.xml file along with the keystore name, keystoreType="PKCS12? This notifies tomcat that the format is PKCS12. Restart the server after this change.
4. Generating Signed SSL certificates by installing an existing wild card supported SSL certificate:
- Go to the <Password Manager Pro_Home>/conf folder.
- Open the file server.xml.
- Search for the entry keystoreFile, which will have the default value set to conf/server.keystore. Change the value to "conf/<keystore_filename>" where <keystore_filename> belongs to the existing wild-card certificate.
- Also search for the entry keystorePass (found next to the keystoreFile), which will have the default value set to "passtrix". Change the value to <keystore_password>, where <keystore_password> protects the existing wild-card certificate keystore.
- Restart the Password Manager Pro server and connect through the web browser console. If you are able to view the Password Manager Pro login console without any warning from the browser, you have successfully installed your SSL certificate in Password Manager Pro.
Note: Please refer your CA's documentation for more details and troubleshooting.
5. How do I generate a unique SSL certificate for MySQL server?
(Steps applicable from build 6500 onwards)
Follow the steps below to generate SSL certificate for MySQL Server. (If you want to have a self-signed key, follow all the steps. If you are using a CA signed certificate, skip steps 1, 2 and 5.)
Step 1 Create certificate authority key
- Open a command prompt
- Execute the command openssl genrsa -out ca.key 1024
- This will create a key named ca.key
Step 2 Create a self-signed certificate authority certificate
- Execute the command openssl req -new -x509 -days 365 -key ca.key -out CAcert.pem
- Here ca.key is the file you created in step 1
- This will create a file named CAcert.pem
Step 3 Generate private key
- Open a command prompt
- Execute the command openssl genrsa -out ServerKey.key 1024
- This will create a file named ServerKey.key
Step 4 Generate a certificate request
- Execute the command openssl req -new -key ServerKey.key -out server.csr
- Here, ServerKey.key is the file you created in step 3
- This will create a file named server.csr
Step 5 Create a Certificate Signing Request (CSR) for submission to a certificate authority (perform this step only if you are using a self-signed certificate. Otherwise, proceed to step 6)
- Execute the command openssl x509 -req -days 365 -in server.csr -CA CAcert.pem -CAkey ca.key -set_serial 01 -out ServerCer.cer
- Here, server.csr is the file you created in Step 4; CAcert.pem is the file created in Step 2; ca.key is the file created in Step 2
- This will create a file named ServerCer.cer
Step 6 Generate .p12 file
- Execute the command openssl pkcs12 -export -in ServerCer.cer -inkey ServerKey.key -out PMPKeyStore.p12 -name pmp -CAfile CAcert.pem -caname pmp -chain
- Here, ServerCer.cer is the file you created in Step 5. If you are using a CA signed certificate, enter the signed SSL certificate with .cer extension; ServerKey.key is the one you created in Step 3; CAcert.pem is the file created in Step 2
- This will create a file named PMPKeyStore.p12
- Here, you will be prompted to enter 'Export Password'. The password specified here has to be entered in Password Manager Pro configuration file in wrapper (in Windows installation) and wrapper_lin.conf (in Linux installation) as explained below.
Open wrapper (in Windows installation) and wrapper_lin.conf (in Linux installation) and search for the following line:
wrapper.java.additional.22=-Djavax.net.ssl.keyStorePassword=passtrix
In the above, replace passtrix with the password you have entered above.
Step 7 Configure the Password Manager Pro server to use the keystore with your SSL certificate
- By executing the above steps, you would have got four files namely CAcert.pem, ServerKey.key, ServerCer.cer and PMPKeyStore.p12. You need to copy and paste these files into <PMP-Installation-Folder>/conf directory
Step 8 Import CAcert.pem into Password Manager Pro
- Navigate to <PMP-Installation-Folder>/bin directory and execute the following command:
In Windows: importcert.bat <absolute path of the CAcert.pem file created in step 2>
In Linux: sh importcert.sh\bat <absolute path of the CAcert.pem file created in step 2>
Step 9 Put these files into MySQL
CAcert.pem to be renamed as ca-cert.pem
ServerKey.key to be renamed as server-key.pem
ServerCer.cer to be renamed as server-cert.pem
- Then, put the renamed files into the <Password-Manager-Pro-Installation-Directory>/mysql/data folder.
Important Note: If you are having High Availability setup, execute the steps 7, 8 and 9 in Password Manager Pro secondary installation also.
6. Can we create server certificates with SubjectAlternativeName (SAN)?
Yes, you can create a certificate using SAN with an alias name and apply it in Password Manager Pro. Follow the below steps:
1. Creating a CSR using Password Manager Pro's SSL certificate management module, and submitting it to any CA for signing
1.1 Create a Certificate Signing Request (CSR)
- Login to Password Manager Pro as an administrator.
- Navigate to Certificates >> Create CSR.
- Click on the 'Create' button.
- Here, provide a name for your certificate.
- The Subject Alternative Name (SAN) will be auto-filled when you click on it after providing the common name. You can include additional SANs in the text field.
- Provide the other details including your organization details, location, validity, and a password.
- Click on 'Create'.
- Once done, you will find the option to export the certificate and the private key, or send the CSR to an email address that you specify.
After creating the CSR, the next step is get the CSR verified and signed by a CA. There are two options to do this:
- You can export the CSR file and manually send it to a third party CA to get it signed.
- You sign and issue certificates to all clients in your network either from your Microsoft Certificate Authority or using a custom root CA certificate that is trusted within your environment. To do this, navigate to Certificates >> Create CSR, select a certificate, and click on 'Sign'. Refer to this document for more details on certificate signing.
Once signed, you can view the certificate under 'Certificates'.
1.3 Import the CA-signed certificate to the Password Manager Pro server
To import the certificates in your network:
- Navigate to Certificates.
- Click on 'Add'.
- Choose the required option:
- File Based Certificate – Browse and import the required certificate file directly from your system.
- Content Based Certificate – Copy the content of the required certificate file and paste it in the text box.
- Keystore Based – Import all individual certificates available in keystore simultaneously. Upload the required keystore file and enter its corresponding password (if any).
- Click on the 'Add' button.
2. Creating a certificate with SAN using Microsoft internal CA
Make sure you follow the below mentioned steps to create server certificate with SubjectAlternativeName using Microsoft Internal CA. Also, in Additional Attributes, specify the 'san:dns=<The URL which you use to access Password Manager Pro>', and then try creating the certificate.
- Connect to the server where Microsoft Certificate Service is running.
- Open a command prompt and execute certutil -setreg policy\EditFlags +EDITF_ATTRIBUTESUBJECTALTNAME2
- Then, restart Microsoft Certificate Service(certsvc).
Create the private key using the below command,"./keytool -genkey -alias Password Manager Pro -keyalg RSA -keypass <privatekey_password> -storepass <keystore_password> -validity <no_of days> -sigalg SHA256withRSA -keysize 2048 -keystore <keystore_filename>" - Here, when it prompts for first and last name, specify the name which you use to access Password Manager Pro.
- Create the Certificate Signing Request(CSR) using the below command: 'keytool -certreq -keyalg RSA -alias Password Manager Pro -keypass <privatekey_password> -storepass <keystore_password> -file <csr_filename> -keystore Password Manager Pro.keystore'
- Submit CSR request to Microsoft Internal CA:
- Open IE and go to your CA's certificate request page.
- Request advanced certificate.
- Submit a certificate request.
- Copy and paste content of <csr_filename>.cer file.
- Certificate template should be Web Server.
- In "Additional Attributes", enter 'san:dns=passwordmanager&dns=passwordmanager.tcu.ad.local' and click on 'Submit'.
- Download the certificate chain in base64 format as Password Manager Procert.p7b.
- Import the downloaded 'Password Manager Procert.p7b' file into the Password Manager Pro.keystore "keytool -import -alias Password Manager Pro -keypass <privatekey_password> -storepass <keystore_password> -keystore Password Manager Pro.keystore -trustcacerts -file Password Manager Procert.p7b"
Notes:
- If you receive the error message "Failed to establish chain from reply" with the above command, it means the root and intermediate certs of your CA are not available in the trusted store of the Password Manager Pro. So, before importing the actual certificate, you have to import the root certificate with a different alias and then import the actual certificate. Also, if you have multiple root certificates, then you have to import them one by one with the different alias names. For example,
./keytool -import -alias root1 -keypass Password123 -storepass Password123 -keystore Password Manager Pro.keystore -trustcacerts -file root1.cer./keytool -import -alias root2 -keypass Password123 -storepass Password123 -keystore Password Manager Pro.keystore -trustcacerts -file root2.cer
Based on the number of root or intermediate root certificates, you have to execute the above command with different alias names and then continue with the actual certificate.
- The actual certificate should be in .cer or .crt format.
- If you receive the error message "Failed to establish chain from reply" with the above command, it means the root and intermediate certs of your CA are not available in the trusted store of the Password Manager Pro. So, before importing the actual certificate, you have to import the root certificate with a different alias and then import the actual certificate. Also, if you have multiple root certificates, then you have to import them one by one with the different alias names. For example,
- Applying the certificate keystore in Password Manager Pro.
- Login to Password Manager Pro as an administrator.
- Navigate to Admin >> Configuration >> Password Manager Pro Server.
- Choose PKCS12 or PKCS11 as the Keystore Type.
- Click on 'Browse' and select your PFX/P12 file.
- Provide the correct keystore password and save the configuration.
- Restart Password Manager Pro service to bring the certificate change into effect.
3. Creating certificate with SAN signed by third party vendor like GoDaddy, Verisign, Commodo, etc.
Make sure you follow the below mentioned steps to get SAN certificate signed from the third party vendors.
- Create the private key using the below command, './keytool -genkey -alias Password Manager Pro -keyalg RSA -keypass <privatekey_password> -storepass <keystore_password> -validity <no_of days> -sigalg SHA256withRSA -keysize 2048 -keystore <keystore_filename>"'
Here, when it prompts for first and last name, specify the name which you use to access Password Manager Pro.
- Create the Certificate Signing Request(CSR) using the below command: 'keytool -certreq -keyalg RSA -alias Password Manager Pro -keypass <privatekey_password> -storepass <keystore_password> -file <csr_filename> -keystore Password Manager Pro.keystore'
- Submit CSR request to third party signing tool and ensure to get the certificate signed using SAN name. Download the certificate chain in base64 format as Password Manager Procert.p7b
- Import the downloaded 'Password Manager Procert.p7b' file into the Password Manager Pro.keystore keytool -import -alias Password Manager Pro -keypass <privatekey_password> -storepass <keystore_password> -keystore Password Manager Pro.keystore -trustcacerts -file Password Manager Procert.p7b .
Note: If you receive the error message "Failed to establish chain from reply" with the above command. Then, the root and intermediate certs of your CA are not available in the trusted store of the Password Manager Pro. So, before importing the actual certificate, you have to import the root certificate with a different alias and then the actual certificate. Also, if you have multiple root certificates, then you have to import them one by one with different alias names. For example,
./keytool -import -alias root1 -keypass Password123 -storepass Password123 -keystore Password Manager Pro.keystore -trustcacerts -file root1.cer./keytool -import -alias root2 -keypass Password123 -storepass Password123 -keystore Password Manager Pro.keystore -trustcacerts -file root2.cer
Based on the number of root or intermediate root certificates, you have to execute the above command with different alias names and then continue with the actual certificate.
- Applying the certificate keystore in Password Manager Pro.
- Login to Password Manager Pro as an administrator.
- Navigate to Admin >> Configuration >> Password Manager Pro Server.
- Choose PKCS12 or PKCS11 as the Keystore Type.
- Click on Browse and select your PFX/P12 file.
- Provide the correct keystore password and save the configuration.
- Restart Password Manager Pro service to bring the certificate change into effect.
5. Password Synchronization
1. Can I change resource passwords from the Password Manager Pro console?
Yes. Password Manager Pro can remotely reset the passwords of various end points. Password Manager Pro supports both agent-based and agent-less modes of changing passwords. Refer this document for more information.
2. When do I use the agent and agent-less modes for password synchronization?
Let us first look at the requisites for both the modes:
The agent mode requires the agent to be installed as a service in each end point and run with administrative privileges to perform password reset operations. The agent uses one-way communication using outbound traffic to reach the Password Manager Pro server.
For the agent less mode, you must supply administrative credentials to perform the password changes. For Linux, you must specify two accounts- one with root privileges and the other with normal user privileges that can be used to login remotely. Telnet or SSH service must be running on the resources. For Windows domain, you must supply the domain administrator's credentials. For Windows and Windows Domain, Password Manager Pro uses remote calls, so relevant ports must be open on the resource.
Based on this, you can choose which mode you want for your environment, indicated by the following tips:
Choose the agent mode when:
- You do not have administrative credentials stored for a particular resource in Password Manager Pro,
- You do not have the required services running on the resource (Telnet / SSH for Linux, RPC for Windows),
- You run Password Manager Pro in Linux and want to make password changes to a Windows resource.
Choose agent less mode in all other cases as it is a more convenient and reliable way of doing password changes.
3. Can I enable agent less password reset if I add my own resource type for other distributions of Linux / other versions of Windows?
Yes, you can. As long as your resource type label contains the string 'Linux' or 'Windows', you can still configure agent less password reset for those resources.
Example of valid resource type labels to enable password reset:
Debian Linux, Linux - Cent OS, SuSE Linux, Windows XP Workstation, Windows 2003 Server
4. Is there a way to carry out remote password synchronization for custom resource types that do not come out of the box in Password Manager Pro?
Password Manager Pro supports remote password reset for custom resource types through SSH command sets, password reset plugins, and password reset listeners.
- SSH Command Sets: For SSH-based devices, you can build command-based executables directly from Password Manager Pro using a set of default or customized SSH commands. These command sets can then be associated with the respective SSH device accounts that do not come out of the box with Password Manager Pro to perform their password resets without the need for a CLI.
- Password Reset Plugin: You can build your own implementation class and run it via Password Manager Pro to enforce automatic password resets of custom resource types. With the plugin, you can also leverage access control for legacy accounts and automatically reset passwords instantly upon usage. This way, the passwords of these accounts will serve as one-time passwords that are reset after every use via the associated plugin.
- Password Reset Listeners: Listeners are custom scripts or executables that can be invoked for local password changes, as well as to reset the passwords of custom resource types for which remote password reset is not supported out-of-the-box by Password Manager Pro. You can configure listener scripts individually for each resource type including the custom ones.
5. How do I troubleshoot when password reset does not happen?
In the agent mode:
- Check if the agent is running by looking at the Windows active process list for the entry 'Password Manager ProAgent.exe' or the presence of a process named 'Password Manager ProAgent' in Linux.
- Check if the account in which the agent is installed has sufficient privileges to make password changes.
In the agent less mode:
- Check if the right set of administrative credentials have been provided and the remote synchronization option is enabled.
- Check if the necessary services are running on the resource (Telnet / SSH for Linux, RPC for Windows).
- Check if the resource is reachable from the Password Manager Pro server using the DNS name provided.
6. How do I reset domain passwords when Windows domain password reset fails with an error message: "The authentication mechanism is unknown"?
This happens when Password Manager Pro is run as a Windows service and the 'Log on as" property of the service is set to the local system account. Change it to any domain user account to be able to reset domain passwords. Follow the instructions below to effect that setting:
- Go to the Windows Services Applet (from Control Panel --> Administrative Tools --> Services).
- Select the 'ManageEngine Password Manager Pro' service, right-click --> choose 'Properties'.
- Click the 'Log On' tab and choose 'This Account' radio button and provide the username and password of any domain user - in the format <domainname>\<username>.
- Save the configuration and restart the server.
7. What are the prerequisites for enabling Windows Service Account Reset?
Before enabling windows service account reset, ensure if the following services are enabled in the servers where the dependent services are running:
- Windows RPC service should have been enabled.
- Windows Management Instrumentation (WMI) service should have been enabled.
8. Does domain SSO work across firewalls / VPNs?
The domain Single Sign On (windows integrated authentication) is achieved in the Windows environment by setting non-standard parameters in the HTTP header, which are usually stripped off by devices like firewalls / VPNs. Password Manager Pro is designed for use within the network. So, if you have users connecting from outside the network, you cannot have SSO this enabled.
9. How and what are the steps that should be taken by the admin to restrict users from resetting the privileged account passwords from UI?
- Log in to Password Manager Pro as an Administrator.
- Navigate to the Resources tab and click on the required resource.
- In the page that opens, besides the required resource, click the Account Actions icon and select Edit Account.
- Select Disable password reset for this account.
- Click Save.
Now, you have successfully restricted the user from resetting the privileged account password.
10. How to manage the privileged account passwords of Oracle DB?
First, check the ORACLE DB version. The inbuilt resource type in Password Manager Pro supports ORACLE DB versions 18c, 19c and 21c.
The next step is to add the ojdbc jar file that is compatible with the versions 18c, 19c and 21c. To manage passwords for the Oracle DB, download the "ojdbc6.jar" using the below link.
https://www.oracle.com/database/technologies/jdbc-drivers-12c-downloads.html
After downloading the jar file, please follow the below steps:
- Stop the Password Manager Pro service.
- Take a back up of "ojdbc5.jar" file under <PMP_Home>/lib and store it in a different location outside Password Manager Pro folder.
- Now, replace ojdbc5.jar with the downloaded "ojdbc6.jar" under the lib folder.
- Restart the service.
- Now trigger password reset for the Oracle DB account from Password Manager Pro.
Note: Make sure the passwords length does not exceed 30 characters. Because any ORACLE version below 12.2 does not support passwords with more than 30 characters in length.
11. How to handle the following exception that occured during Remote Password Reset?
Exception caught:
Error occured in listLocalService dll com.adventnet.passtrix.CppCsharpConnect.listLocalService(Ljava/lang/String;Ljava/lang/String;Ljava/lang/String;Ljava/lang/String;Ljava/lang/String;)Ljava/lang/String;|
Cause: Error occurs if prerequisite software is not installed.
Solution:
- Password Manager Pro uses .NET api calls (dll method) to manage Windows Password Reset, Account Discovery, Password Verification and etc..
- To make sure you have installed the prerequisite software, do the following:
12. Why are Agents deployed? What is the difference between Agent and Agent-less mode?
Password Manager Pro server establishes a direct connection to the target server/endpoints using the windows native WMI/RPC protocols to perform remote password resets. So, you have to allow certain WMI ports to establish connection from Password Manager Pro to the target devices. Agents are required only for the resources that reside behind the firewall or in a DMZ zone.
Here, the prerequisite is to allow access to the Password Manager Pro web console from the agent installed machine. To know more about agents, please refer to this link.
13. Does Password Manager Pro support Oracle DB? If so, what versions of Oracle DB does the product support?
Password Manager Pro supports only the following versions of the Oracle database: 18c, 19c, and 21c since Oracle extends support only to these versions as of August 2022. Refer to the Oracle Lifetime Support Policy Guide for more information.
6. Backup & Disaster Recovery
1. Can I move Password Manager Pro from one server to another?
Yes. you can migrate Password Manager Pro to another server by following the below steps:
- Stop Password Manager Pro service, exit tray icon.
- Make sure that the Postgres process is not running in Task Manager.
- Copy and move entire Password Manager Pro directory to the new server.
- Open command prompt with admin rights and navigate to <Password Manager Pro HOME>\bin directory. Execute the command Password Manager Pro.bat install. (This will install Password Manager Pro service.)
- Move the encryption key(Password Manager Pro_key.key) to the new server and specify the correct location of it in Password Manager Pro/conf/manage_key.conf file. Click here for more information about the encryption key.
- Go to services console, provide a service account and start Password Manager Pro service.
- If you want the tray icon, Go to the <Password Manager Pro HOME>, right click on Password Manager Pro.exe and select "Run as Administrator".
Now you should be able to access the Password Manager Pro web page using the new server name in the URL.
2. Why does the Password Manager Pro application fail to start after moving from one server to another?
From build 13140 onwards, this issue occurs when the server's hostname changes. A mismatch between the old and new host names can lead to DNS-related conflicts in the database, resulting in server startup failure. To resolve this issue, update the server's DNS information in the database. To do so, navigate to the <PMP_Installation_Directory>\bin folder and execute the following command:
Note: Replace <old-hostname> with the actual hostname used before migration.
This updates the server DNS details directly in the database, resolving the mismatch and allowing the server to start properly.
Additionally, ensure that the hostname specified in the server.conf file is updated correctly to match the current environment.
3. Can I setup disaster recovery for the Password Manager Pro database?
Yes, you can. Password Manager Pro can periodically backup the entire contents of the database, which can be configured through the Password Manager Pro console. Refer this document for more details.
4. Where does the backup data get stored? Is it encrypted?
All sensitive data in the backup file are stored in encrypted form in a .zip file within the <Password-Manager-Pro-Installation-Directory/backUp> folder. It is recommended that you backup this file in your secure, secondary storage for disaster recovery.
7. Licensing
1. How is Password Manager Pro licensed?
Password Manager Pro licensing is based on three factors:
- Number of Administrators.
- Type of Edition – Standard, Premium or Enterprise.
- Number of Keys (Optional Add-on).
Click here to know more about licensing in Password Manager Pro.
2. What is the Licensing Policy for Password Manager Pro?
There are three editions of Password Manager Pro:
Evaluation Edition - Evaluation Edition allows you to have two administrators for 30 days. You can manage unlimited resources and evaluate all features of the Enterprise edition. You can also get free technical assistance during this period.
Free Edition - The download option is always valid for this edition. It can support only one administrator. You can manage a maximum of 10 resources and you can access all the functionalities of the Standard edition.
Registered Version - You need to buy a license based on the number of administrators required and the type of edition- Standard/Premium/Enterprise:
- Standard - If your requirement is to have a secure, password repository to store your passwords and selectively share them among enterprise users, Standard edition would be ideal.
- Premium - Apart from storing and sharing your passwords, if you wish to have enterprise-class password management features such as remote password synchronization, password alerts and notifications, application-to-application password management, reports, high-availability and others, Premium edition would be the best choice.
- Enterprise - If you require more enterprise-class features like auto discovery of privileged accounts, integration with ticketing systems and SIEM solutions, jump server configuration, out-of-the-box compliance reports, and SQL server / cluster as backend database, the Enterprise edition will be ideal for you.
Note: Password Manager Pro comes with five user roles - Administrator, Password Administrator, Privileged Administrator, Password Auditor and Password User. The term 'administrator' denotes Administrators, Password Administrators and Privileged Administrators. So, licensing restricts the number of administrators as a whole, which includes Administrators, Password Administrators and Privileged Administrators. There is no restriction on the number of Password Users and Password Auditors. To get more details on the five user roles, refer this section of our help documentation.
Explore this document for more clarity on the features comparison.
3. Can I buy a permanent license for Password Manager Pro? What are the options available?
Though Password Manager Pro follows an annual subscription model for pricing, we also provide perpetual licensing option. The perpetual license will cost three times the annual subscription price, with 20% AMS from the second year. Contact sales@manageengine.com and support@passwordmanagerpro.com for more details.
4. How to apply my license in Password Manager Pro?
- Login as an Administrator and click on the My Account icon on the top right corner.
- Select License from the drop down menu.
- In the pop-up that appears, Browse and select the license file and click Upgrade.
You have successfully applied the license to Password Manager Pro.
5. I want to have a High Availability setup with multiple servers. Will a single license suffice for this?
Yes, if you buy a single Premium or Enterprise Edition license, you are entitled to have the High Availability setup. But, make sure you apply the same license on the Primary and the Secondary servers. Follow the below steps:
- Stop the Password Manager Pro service in the Primary server.
- Login Password Manager Pro using the Secondary server URL as an Administrator.
- Tap License under the User menu, at the top right corner of the console.
- Update the same license file, which you applied for the Primary server, to the Secondary server.
6. Can Password Manager Pro support more than 1000 administrators?
Yes, very much. If you want a license with more than 1000 administrator users, please contact sales@manageengine.com and support@passwordmanagerpro.com for more details.
7. How many resources and accounts can I manage from the Password Manager Pro application?
In Password Manager Pro licensing, there are no limitations on managing resources and accounts. You have the flexibility to add or import any number of resources, depending on the supported resource types, and you can manage accounts according to your needs without any restrictions.
8. Can I extend my evaluation to include more administrator users or for more number of days?
Yes. Fill in the required details in the website and we will send you the license keys.
9. Do I have to reinstall Password Manager Pro when moving to Premium or Enterprise Editions?
No. All the features of the Enterprise/Premium edition will automatically get activated when you apply the respective license over your current Password Manager Pro installation.
8. SSH Key Management
1. Are there any differences in the way SSH user accounts and SSH service accounts are managed using Password Manager Pro?
No. Password Manager Pro adopts the same approach for managing SSH user accounts and SSH service accounts. The only difference is that during resource discovery, if service / root account credentials are provided to establish connection with the resource, you acquire extended privileges to import and manage keys from all user accounts in the resource.
Whereas, when connection to the resource is established using user account credentials, you get key management privileges only for SSH keys present in that particular account.
2. Is there any way to view SSH keys that were not rotated?
Yes. We have a dashboard that displays the number of keys that were not rotated for the predefined time period as specified in the notification policy.
3. Does Password Manager Pro support management of digital keys other than SSH keys and SSL certificates?
Password Manager Pro houses a key vault called "Key Store" which facilitates the storage and management of any type of digital key. However, the option to discover and import is limited to SSH keys and SSL certificates only, and isn't available for other types of digital keys.
9. SSL Certificate Management
1. Is there any certificate type that Password Manager Pro is incompatible with?
No. Password Manager Pro supports all X.509 certificate types.
2. Is it possible to automatically identify and update the latest version of certificates in Password Manager Pro' certificate repository?
Yes. You can create scheduled tasks to perform automatic certificate discovery through which you can import and replace old certificates from target systems with their updated versions in Password Manager Pro' certificate repository. Click here for a detailed explanation on creating schedules.
3. Does the Linux version of Password Manager Pro support certificate discovery from Active Directory and MS Certificate Store?
No, it doesn't. The AD User Certificate and MS Certificate Store tabs appear only in the Windows version of Password Manager Pro.
4. Is it possible to track the expiry of certificates with the same common name in Password Manager Pro' certificate repository?
Password Manager Pro differentiates certificates by their common names and records certificates with same common names as a single entry in its certificate repository. We've designed it this way because Password Manager Pro licensing is based on the number of certificates and we don't want customers to spend many license keys for the same certificate.
However, if there's a need to manage both the certificates separately, you can do so by listing them as separate entries in Password Manager Pro' certificate repository. Once listed, the newly added certificate will be counted for licensing.
To add a certificate with the same common name as a separate entry in certificate repository,
- Navigate to the Certificates tab and click Certificates, and click the Certificate History icon beside the certificate.
- Click the 'Certificate Settings' icon beside the required version of the certificate and click on 'Manage Certificate'.
- The selected version is listed as a separate certificate in the certificate repository.
- In case you want to manage only one version of the certificate, click 'Certificate Settings' icon beside the required version and choose 'Set as current certificate' option.
5. How do I import private key for a certificate?
Follow the steps below to import a certificate's private key into Password Manager Pro.
- Navigate to the Certificates tab and click Certificates.
- Select the certificate for which you need to import the private key.
- Click the Import Keys option from the More drop down menu at the top.
Browse for the file that contains the private key, enter the keystore password, and click on 'Import'. The private key will be imported and attached to the selected certificate.
6. How do I deploy a certificate to Certificate Store and map it to the application that uses the certificate?
Password Manager Pro facilitates certificate deployment through which you can deploy certificates from its repository to target server's Microsoft Certificate Store.
Click here for step-by-step explanation on certificate deployment.
To map the certificate to its corresponding application, you've to manually restart the server on which the application is running for the change to take effect.
7. Does Password Manager Pro support subnet based certificate discovery?
No. Password Manager Pro currently doesn't support subnet based SSL certificate discovery.
8. Does Password Manager Pro support automatic scheduling for certificate discovery from MS Certificate Store?
No. Currently, Password Manager Pro doesn't support automatic scheduling for certificate discovery from MS Certificate Store.
9. Are certificate related alert emails generated for all versions of a certificate (the ones that show in "Certificate History" also) or only for those certificates listed in Password Manager Pro's certificate repository?
Email notifications are generated ONLY for certificates listed in Password Manager Pro's certificate repository and NOT for different versions of a certificate displayed in "Certificate History" section.
10. Are the certificates issued by the company's internal Certification Authority (CA) counted for licensing?
Yes. All types of SSL certificates, SSH keys and any other digital key being managed using Password Manager Pro are taken into account for licensing. There's a dashboard widget "License Details" that provides insights on the type and number of digital identities being managed using Password Manager Pro that will be taken into account for licensing.
11. How do I import a root certificate into Password Manager Pro?
To import a root certificate, open the Command Prompt and navigate to the <pmp_server_home>\bin directory and execute the following command:
For Windows:
importCert.bat <Absolute Path of certificate>
For Linux:
importCert.sh <Absolute Path of certificate>
10. High Availability
1. Does Password Manager Pro support High Availability?
Yes, refer the High Availability document for more details.
2. How to handle the following exceptions that occur in High Availability?
Exception #1: The driver encountered an unknown error: org.postgresql.util.PSQLException: FATAL: no pg_hba.conf entry for host "10.76.2.70", user "postgres", database "PassTrix", SSL on|
Cause: Missing secondary server IP address inside pg_hba.conf file.
Solution:
- Stop the Password Manager Pro services on both the primary and secondary server.
- In primary server, navigate to <PMP_Installation_Directory>\pgsql\data folder.
- Take a backup of the pg_hba.conf file and store it in a different location.
- Edit pg_hba.conf file with admin privileges.
- Scroll down to the bottom of the file and add the new entry,
host all pmpuser <SecondaryServerIP>/32 md5
example: 10.76.2.70 - Save the file.
- Now, start the Password Manager Pro service on both the servers and check the HA status.
Exception #2: no connection to 'right' database
Cause: This occurs when the primary to secondary server communication gets timed out during the replication process.
Solution:
To increase the replication timeout value, follow the below steps:
- Stop the Password Manager Pro service on both Primary and Secondary Servers.
- In the primary server, navigate to <PMP_Installation_Directory>\conf folder.
- Open the pmp_rr.conf file with admin rights.
- Search for entry config.options[:database_connection_timeout] = 60.
- Change the value of config.options[:database_connection_timeout] = 900 and save the file.
- Repeat the same steps in the secondary server by modifying the pmp_rr.conf file.
- Now start the Password manager Pro service in both the servers.
Exception #3: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
Cause: This exception occurs if there is an SSL handshake issue between both primary and secondary applications.
Solution:
Import root certificate of web servers inside the Password Manager Pro certificate trust store.
In Primary Server:
- Stop the primary Password Manager Pro service and access the secondary web portal.
- Click on the lock icon near the browser tab and select 'View Certificate'.
- Navigate to ''Details' tab and click on 'Copy to file' and export the file in Base64 encoded(.cer) format inside <PMP_Installation_Folder>\bin folder.
- Start the primary service, access the primary web portal and export the primary server certificate inside <PMP_Installation_Folder>\bin folder.
- Now, open the command prompt as administrator.
- Navigate to <PMP_Installation_Folder>\bin and execute the command - importcert.bat <Name of the Primary Server Certificate> (This will add the certificate of Password Manager Pro certificate store)
- Again execute, importcert.bat <Name of the Secondary Server Certificate>
In Secondary Server:
- Move both the exported primary and secondary certificate to the <PMP_Home>/bin folder of the secondary server.
- Open the command prompt as administrator.
- Navigate to <PMP_Installation_Folder>\bin and execute the command- importcert.bat <Name of the Primary Server Certificate> (This will add the certificate of Password Manager Pro certificate store).
- Again, execute importcert.bat <Name of the Secondary Server Certificate>
- Now, restart the services on Primary and Secondary Server and check the HA status.
Exception #4: [INFO]|[41]: rubyrep process error: Exception caught: The driver encountered an unknown error: org.postgresql.util.PSQLException: Connection refused. Check that the hostname and port are correct and that the postmaster is accepting TCP/IP connections.
Cause: Connection issue between primary and secondary server.
Solution:
Verify the following port details:
1. Check if the ports 2345 and 8282 (443) are open in between the primary and secondary Password Manager Pro servers. For a successful replication, we need these ports open. You can try to TELNET these ports from primary to secondary and then secondary to primary to see if they are open.
2. If the HA pack is created using FQDN then,
>> From secondary server: Telnet <primary_FQDN> 8282 & Telnet <primary_FQDN> 2345
>> From primary server: Telnet <secondary_FQDN> 8282 & Telnet <secondary_FQDN> 2345
Note: If IP address is used to create the HA pack, replace FQDN with IP address.
11. Remote Sessions
1. How do I restrict password users from launching RDP auto-logon sessions from Password Manager Pro using their local account?
- Navigate to the Resources tab.
- Select the server and click the Resource Actions icon.
- Choose Edit Resource from the dropdown.
- Enable Restrict RDP using local account and click Save.
This will prompt a prompt access restricted message when user tries to take RDP using his local account.
2. How to launch RDP connections over internet and what are the pre-requisites?
To access Password Manager Pro over internet, please make sure the web server port - 7272/ 443 and auto-logon gateway port 7273 is open and accessible from server which is connected to a different network.
Apart from ports, for a successful RDP connection there should be proper web socket re-direction. Make sure the web sockets are re-directed if you are using a proxy server or load balancer tool.
3. How does RDP work in Password Manager Pro? What are the connection metrics?
For establishing a RDP connection, Password Manager Pro server works exactly as same as MSTSC connections. It uses the port 3389 to initiate the RDP session from the Password Manager Pro server to the remote machines.
Therefore, from user machine to Password Manager Pro server, port 7273 should be open and from Password Manager Pro server to target system, the native RDP port 3389 should be opened for a successful RDP connection.
4. Are the recorded sessions actual videos, or are they compilations of screenshots? How large are these videos typically? How much storage does it typically use?
Recorded videos are series of actual images captured during the sessions in a proprietary format and played together in a specific logical sequence. When a user launches an RDP connection through the auto-logon gateway, the gateway will display every action (as images) the user is trying to do during the session. During remote sessions, we record only if there is any mouse movement or keystroke and we don't record stand still or ideal images. So the disc space occupied should be very less. For one minute of video, the disc space occupied will be approximately around 1MB. Only if you have a high definition or graphics application like 1080p video playing on the back end, the size will be 1MB for 1min. If it is a normal operation, the size will be 300 to 400 kb per minute and it will be stored in a proprietary video format. Since the recorded session size varies depending on the screen resolution, we don't have exact sizing metrics.
5. What are the steps involved in launching RDP sessions using a domain user account?
Password Manager Pro allows users to connect to the desired resource using either the appropriate Domain account or the currently logged in AD/Entra ID/LDAP account. To do this,
- Navigate to the Connections tab and hover over the required resource.
[or]
Navigate to the Resources tab and click the Remote Connection icon beside the required resource. - Choose Domain Account.
- In the pop-up that appears,
- You can choose to Use domain account or Use <account_name> Credentials (currently logged in AD / Entra ID / LDAP).
- Select Use Domain Account or Currently logged in AD account.
- If you choose to Use Domain Account, select the Resource Name and the Account Name.
- If you choose to Use <account_name> Credentials (currently logged in AD / Entra ID / LDAP), mention the account Password.
- Enter the Reason for establishing the connection (mandatory) and click Connect.
- You can choose to Use domain account or Use <account_name> Credentials (currently logged in AD / Entra ID / LDAP).
Now, you have successfully established a connection with that resource.