In the cybersecurity landscape, attack surface expansion isn't a new concept. Organizations with a digital presence have been contending with this challenge for a long time. Much like software developers continually update their code to stay ahead of vulnerabilities, cyberthreats undergo constant adaptations, expanding their digital frontier.
The annual 7 top trends in cybersecurity for 2022 by Gartner® shows that attack surface expansion remains a persistent concern for organizations already well-versed in the intricacies of digital defense.
This blog aims to provide insights into:
- What drives the expansion of attack surfaces in cybersecurity?
- Common attack vectors in expanding attack surfaces
- Real-time cyberthreats
- How does a SIEM solution help with attack surface reduction?
- Strategies to minimize attack surface expansion
What drives the expansion of attack surfaces in cybersecurity?
Amidst the dynamic evolution of technology, the growth of attack surfaces is a critical concern. As our reliance on complex systems and networks deepens, this expansion introduces a multitude of new and evolving threats. Here are some key factors contributing to the expansion of attack surfaces:
Rapid technological advancements: Technological innovation brings a continuous stream of new devices, software, and systems. While these innovations bring convenience and efficiency, they also introduce vulnerabilities. Cyber attackers often exploit these emerging technologies, seeking weaknesses and exploiting them. For instance, the rush to adopt new technologies can lead to inadequate security measures, making them attractive targets.
Proliferation of IoT devices: The widespread deployment of internet-connected devices, from smart home gadgets to industrial sensors, has created a vast attack surface. Many of these devices prioritize functionality over security, making them susceptible to exploitation. As the number of connected devices continues to grow, so do the opportunities for cybercriminals to breach networks.
Remote work and BYOD policies: The shift toward remote work, accelerated by global events like the COVID-19 pandemic, has stretched traditional security boundaries. Employees now use personal devices and unsecured networks to access company resources. This diversity of endpoints creates numerous potential entry points for cyberattacks. Furthermore, the security of employees' personal devices may not be as robust as that of company-owned devices, making them attractive targets for attackers.
Complex IT environments: Organizations are increasingly adopting complex IT infrastructures, including cloud computing, diverse software platforms, and third-party services. While these technologies offer scalability and flexibility, they also introduce additional vulnerabilities. Each new component of the IT environment potentially becomes an entry point for attackers. Third-party dependencies, if not properly managed, can also expose organizations to supply chain risks.
Common attack vectors in expanding attack surfaces
- Phishing and social engineering: Deceptive tactics that trick individuals into revealing sensitive information or compromising security through emails and psychological manipulation.
- Malware and ransomware attacks: Malicious software that infects systems, disrupts operations, and may demand ransom for decryption keys.
- Zero-day vulnerabilities and exploits: Undisclosed software vulnerabilities that attackers exploit before developers release patches. These vulnerabilities can be particularly dangerous as there are no known fixes at the time of exploitation.
- Supply chain attacks: Compromising trusted software or hardware components before reaching users, potentially affecting multiple organizations.
- Insider threats: Risks arising from individuals within organizations who may intentionally or inadvertently expand attack surfaces, jeopardizing security.
Real-time cyberthreats
In April 2022, Block, the parent company of Cash App, reported that a formerly disgruntled Cash App employee managed to access and steal information from over eight million users of Cash App Investing, a separate service for stock trading. The stolen data included customer names, brokerage account numbers, stock portfolios, and trading activity. While more sensitive information like Social Security numbers remained safe, this breach highlighted a failure in implementing access control policies, particularly for ex-employees, and went undetected for four months. Cash App is now facing multiple class-action lawsuits for inadequately safeguarding user data.
Another massive data breach occurred in August 2022. Plex, a media streaming platform, required all of its 20 million users to reset their passwords because an unauthorized third-party accessed emails, usernames, and encrypted passwords. While users' payment info wasn't included in the breach, the event exposed a security weakness. When users tried to reset their passwords, Plex's servers were overwhelmed. This situation underscores the importance of strong passwords to stay safe online, even when encryption is in place.
How does a SIEM solution help with attack surface reduction?
ManageEngine Log360 is a comprehensive security information and event management ( SIEM ) solution designed to reduce attack surface by providing organizations with the insights needed to proactively identify and mitigate potential security threats.
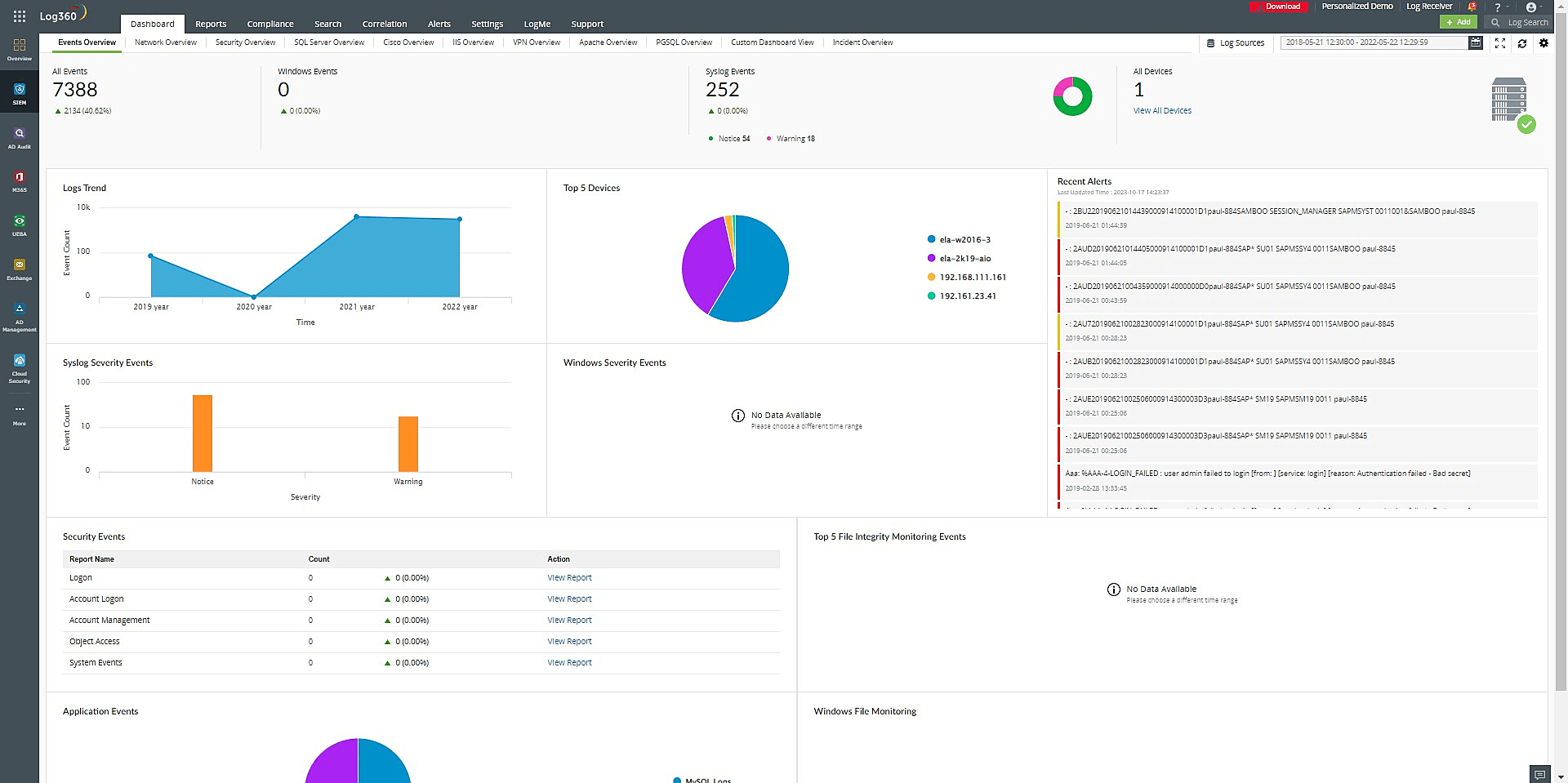
Here are some ways ManageEngine Log360 contributes to attack surface reduction:
- Log collection and analysis: Log360 collects and analyzes log data from various sources within an organization's IT environment, including servers, applications, network devices, and more. By aggregating and correlating this data, it helps security teams gain visibility into potential vulnerabilities and attack vectors.
- Real-time monitoring: The solution offers real-time monitoring capabilities, allowing security professionals to detect suspicious activities or anomalies as they occur. This proactive approach enables quick responses to security incidents, reducing the window of opportunity for attackers.
- Threat intelligence integration: Log360 integrates with threat intelligence feeds, providing up-to-date information on known threats and vulnerabilities. This integration helps organizations identify and prioritize potential risks based on external threat data.
- User and entity behavior analytics (UEBA): Log360 employs UEBA to establish baseline user and entity behavior. By continuously monitoring deviations from these baselines, it can detect insider threats, compromised accounts, or unusual access patterns, reducing the attack surface caused by internal vulnerabilities.
- Incident response automation: Log360 offers incident response automation, enabling organizations to define and execute predefined responses to common security incidents. This reduces the time it takes to mitigate threats and limits the damage they can cause.
- Compliance and reporting: Compliance reports and dashboards in Log360 help organizations ensure that their security policies and configurations align with industry standards and regulatory requirements such as HIPAA, PCI DSS, GDPR, FISMA, SOX, SOC 2 and others. This, in turn, reduces the risk of non-compliance-related vulnerabilities.
Strategies to minimize attack surface expansion
- Regularly identify and fix system weaknesses.
- Prioritize security in development and coding.
- Restrict unnecessary access and privileges.
- Keep systems updated with security patches.
- Educate users on security best practices.
- Use SIEM and IDPS for real-time threat detection.
- Integrate threat intel for proactive defense.
- Have a robust incident response plan.
- Monitor user and entity behavior for anomalies.
What's next?
Proactively detect and respond to access token manipulation with Log360.
- What drives the expansion of attack surfaces in cybersecurity?
- Common attack vectors in expanding attack surfaces
- Real-time cyberthreats
- How does a SIEM solution help with attack surface reduction?
- Strategies to minimize attack surface expansion