- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
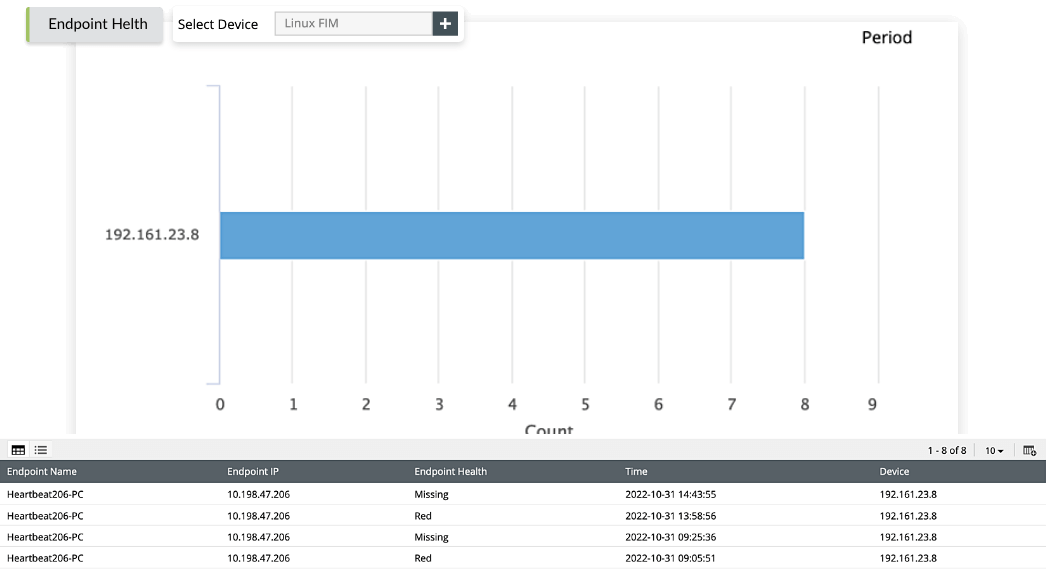
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
What is FISMA compliance?
The Federal Information Security Modernization Act (FISMA) is a United States federal law that requires federal agencies to develop, document, and implement an agency-wide information security program. FISMA was enacted in 2014 as an update to the Federal Information Security Management Act of 2002. FISMA mandates that federal agencies adopt effective information security practices and comply with regulations in order to protect sensitive government information from cyberthreats.
FISMA was developed to ensure appropriate security control such as access controls, data encryption, and network security measures to protect sensitive data. Non-compliance to FISMA might lead to loss of federal funding, reputational damage, and the loss of future contracts.
Who must comply with FISMA?
Federal agencies and organizations that utilize federal government data must adhere to FISMA compliance requirements. This includes contractors, state and local governments, universities, and other institutions that have access to federal information systems. FISMA mandates that federal agencies and federal contractors meet the guidelines set by NIST to ensure the confidentiality, integrity, and availability of federal information systems.
Related content
Discover how EventLog Analyzer streamlines the process of demonstrating FISMA compliance
Audit and Accountability (AU)
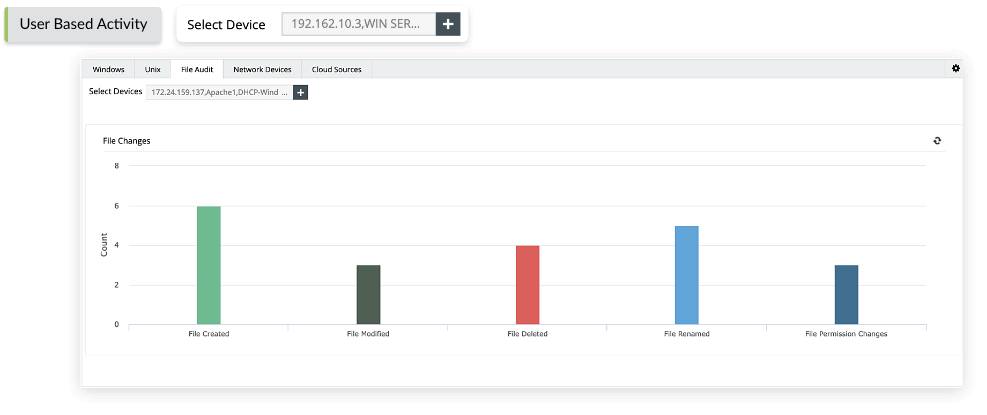
EventLog Analyzer's file integrity monitoring (FIM) audits changes made to files and folders in real time. The solution thoroughly checks files and folders containing confidential government data and generates instant alerts when critical changes are noticed. For instance, the File Changes audit report provides detailed information on object access, such as who accessed the object, changes made to it, along with the location, date, and time of the event. The solution also helps to document all the steps taken to protect federal government data and stay on top of FISMA audits.
Certification, Accreditation, and Security Assessments (CA)
Continuous log monitoring and regular audits of the organization's internal security framework are primary requirements of FISMA compliance. The CA guideline of FISMA necessitates monitoring of the services and applications running across the network to prevent unapproved installations of services or applications. To fulfill this requirement, EventLog Analyzer provides a Windows Services report that includes specific information about the date and device on which the service was launched. The solution generates real-time alerts upon the start of any unauthorized Windows service.
Contingency Planning (CP)
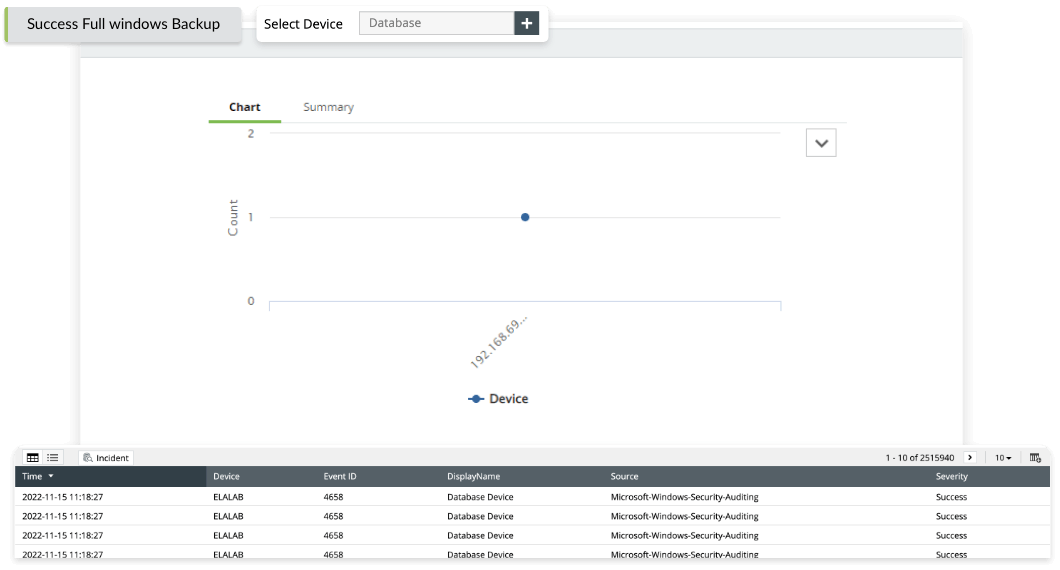
EventLog Analyzer's predefined Windows backup and restore reports help you identify and restore all the confidential data in a time of crisis. These reports include in-depth details about the backup and restore operations. EventLog Analyzer helps security admins and data protection officers submit final audit review reports with predefined FISMA compliance report templates.
Access Control (AC)
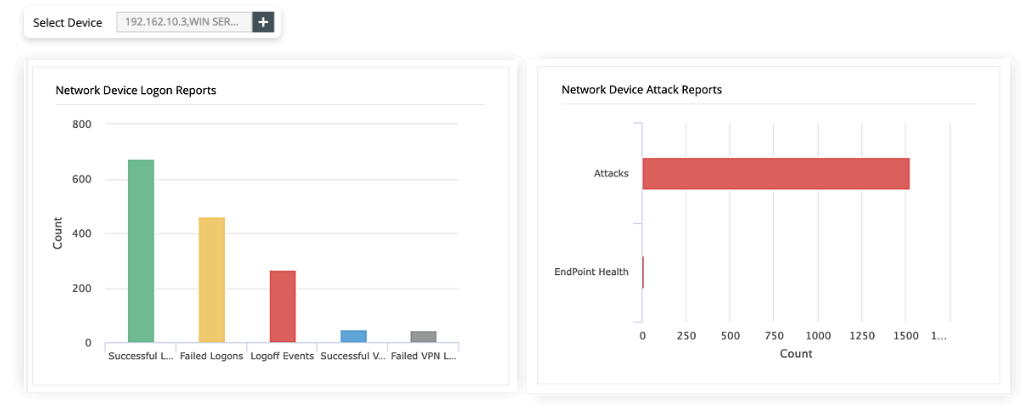
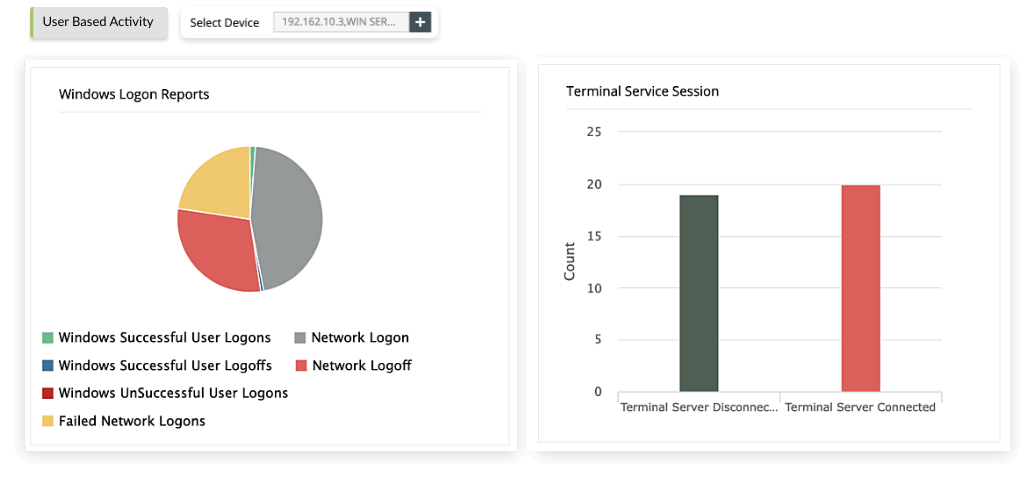
EventLog Analyzer helps monitor Linux and Unix servers, terminal servers, Windows workstations, network devices, and more. The solution also helps prevent unauthorized threat actors from moving around your organization's network to exploit vulnerabilities and escalate privileges. You can generate reports on Unsuccessful User Logons, Successful User Logons and Logoffs, and more. Additionally, it provides comprehensive information on Terminal service sessions, such as details on connection, disconnection, and reconnection, giving you better visibility on the remote access details of your network.
Identification and Authentication (IA)
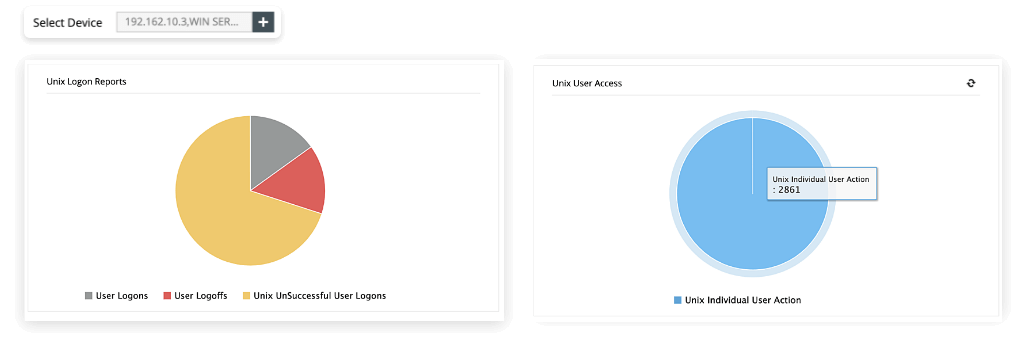
EventLog Analyzer helps you comply with the IA requirements of FISMA with its individual user action report. Gain a complete picture of a user's actions, like who accessed the information and when it was accessed. Identification and authentication controls ensure that only authorized users can access the federal information system. The solution helps protect confidential federal information from unapproved modifications, security threats, and data breaches.
Continuous security system monitoring
Federal agencies are required to conduct periodic risk assessments to ensure the adequacy of the implemented security controls and policies. Gain granular visibility and real-time insights into information assurance and control adherence. EventLog Analyzer provides detailed reports to help you monitor system changes like Windows software updates and upgrades or changes to critical security applications (for example, anti-malware and other business software).
Become FISMA compliance ready with EventLog Analyzer
| FISMA compliance | Reports by EventLog Analyzer |
|---|---|
| Audit and Accountability (AU) |
|
| Access Control (AC) |
|
| Certification, Accreditation, andSecurity Assessments (CA) |
|
| Contingency Planning (CP) |
|
| Identification and Authentication (IA) |
|
| Configuration Management (CM) |
|
| Information System Monitoring(SI-4) |
|
| Access Enforcement(AC - 3) |
|
What else does EventLog Analyzer provide?
Application log monitoring
Collect, analyze, and correlate log data from applications such as IIS, Apache, MS SQL, Oracle, and DHCP to identify anomalous user activities, application crashes, and security threats.
Learn moreCritical server monitoring
EventLog Analyzer analyzes the server logs to identify disrupting events. The solution keeps an eye on server performance 24/7 to accurately spot server threats and errors.
Learn moreAdvanced threat analytics
Detect and thwart security threats with the help of a global threat feed database which helps identify the list of all malicious IPs, URLs, and domains.
Learn moreAutomated incident response
EventLog Analyzer's real-time incident detection system instantly identifies security events and automatically assigns them to a security admin to take quick remediate action.
Learn more










