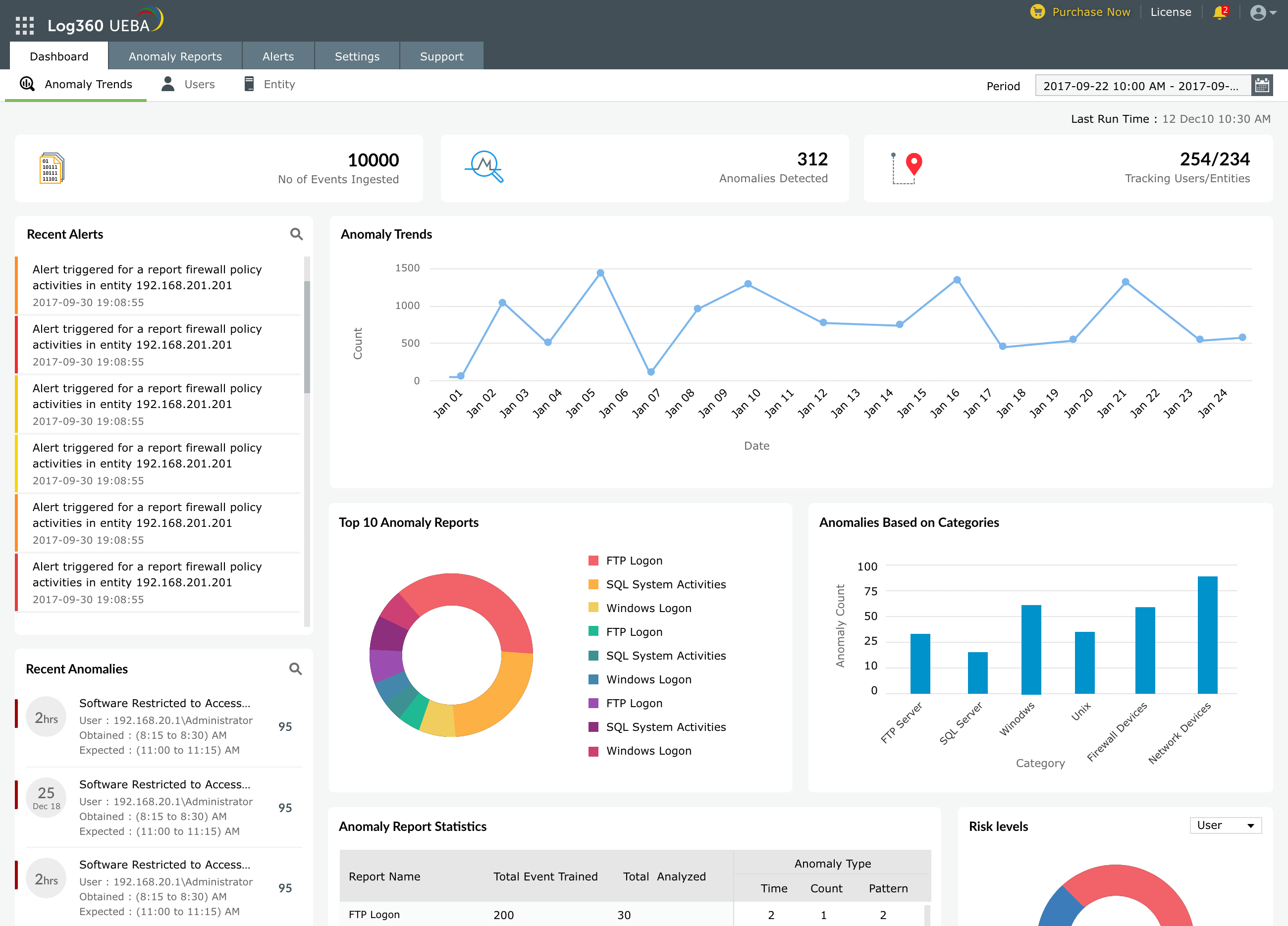
Dashboard
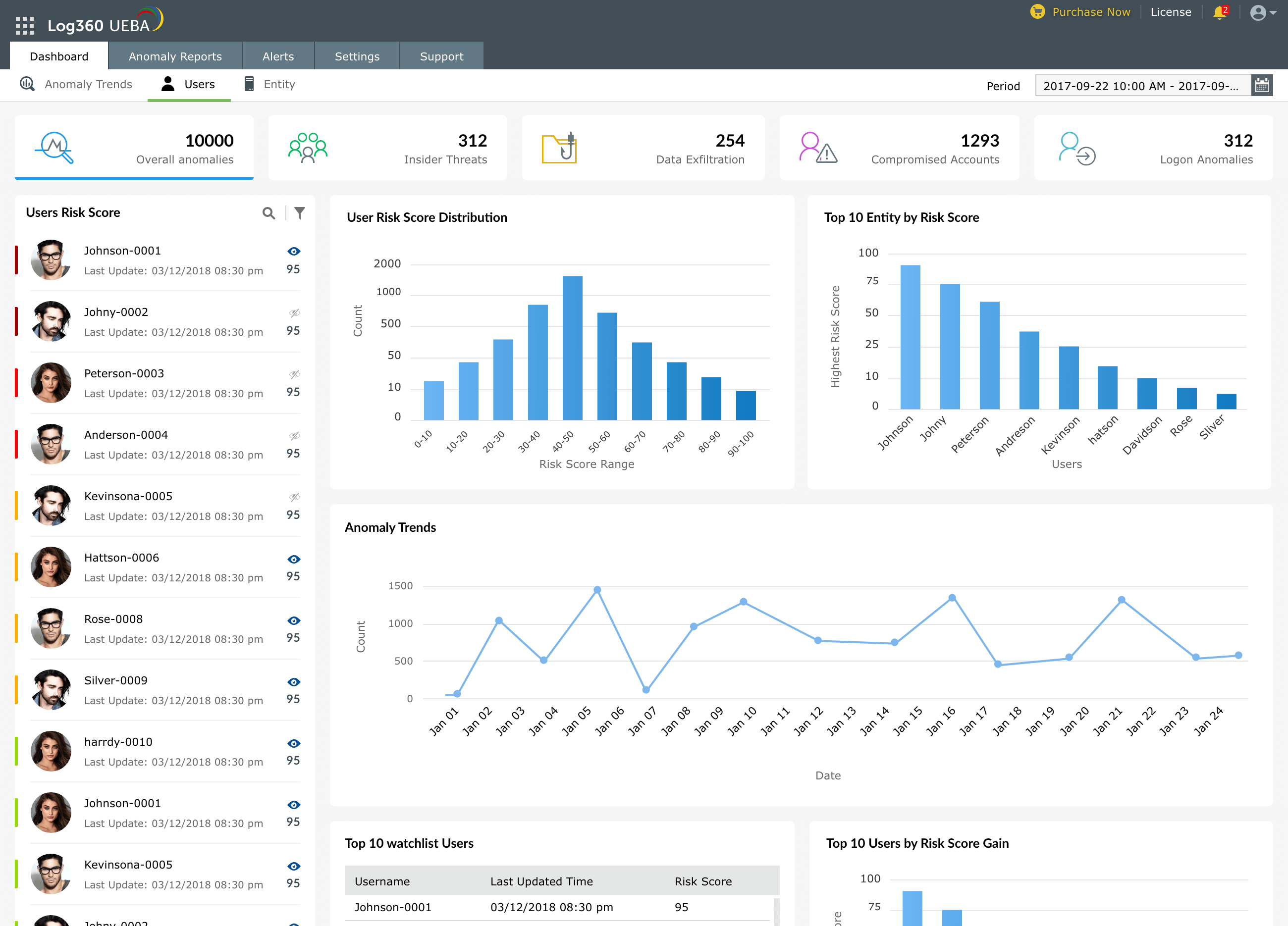
The dashboard provides a brief overview of anomalous behavior based on users and entities in the network. Since it gathers multiple data sources into a single interface, administrators can quickly check upon the status of their organization's security posture.
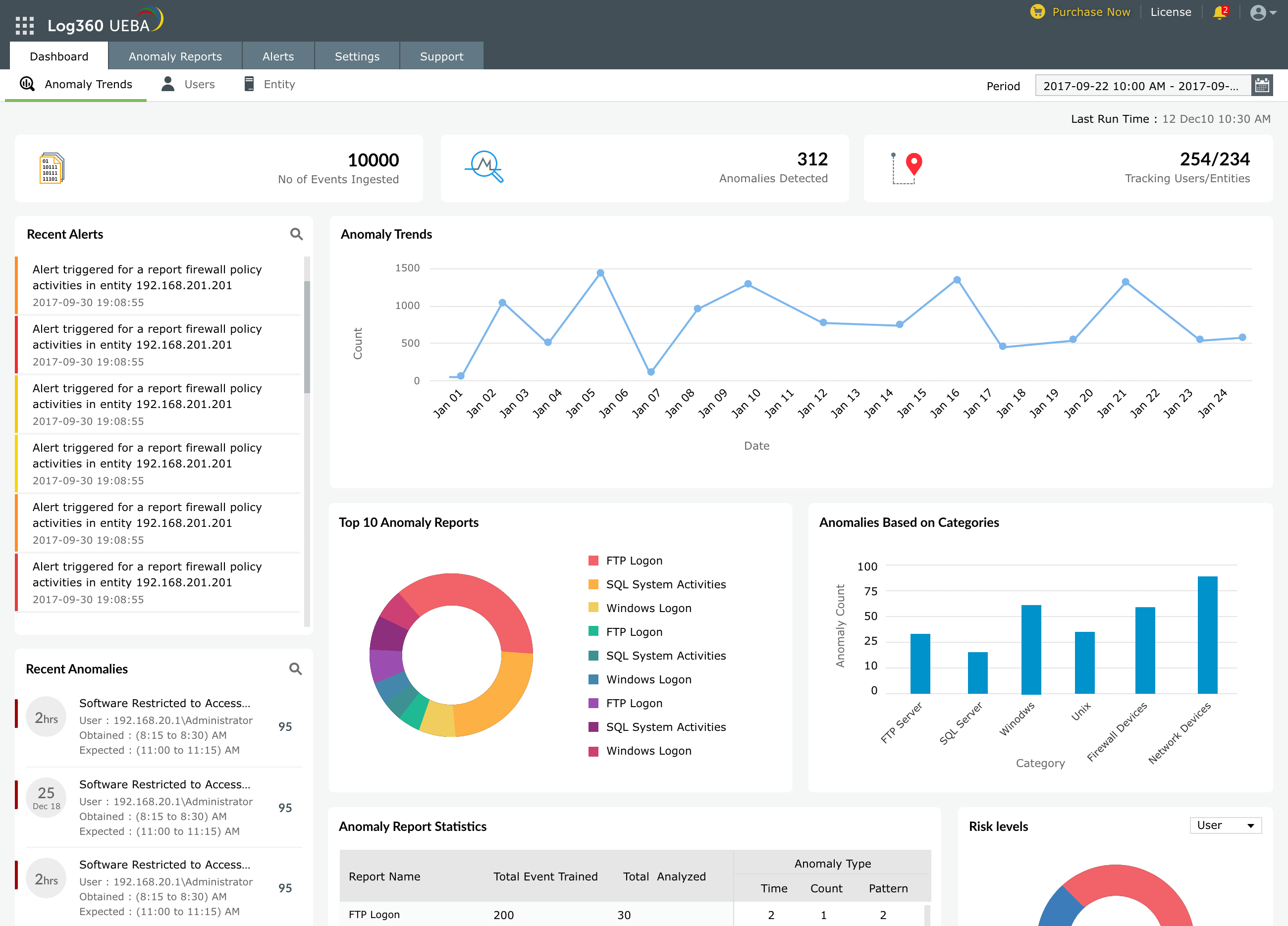
Anomalous user behavior
- A cumulation of all the anomalies based on user behavior including, data exfiltration, compromised accounts, and insider threats.
- A list of the most dangerous users based on their risk scores.
- A list of all watchlisted users.
- A list of users with the highest risk score gain.
- The users' photo will be shown along with their risk scores due to a sync with Active Directory.
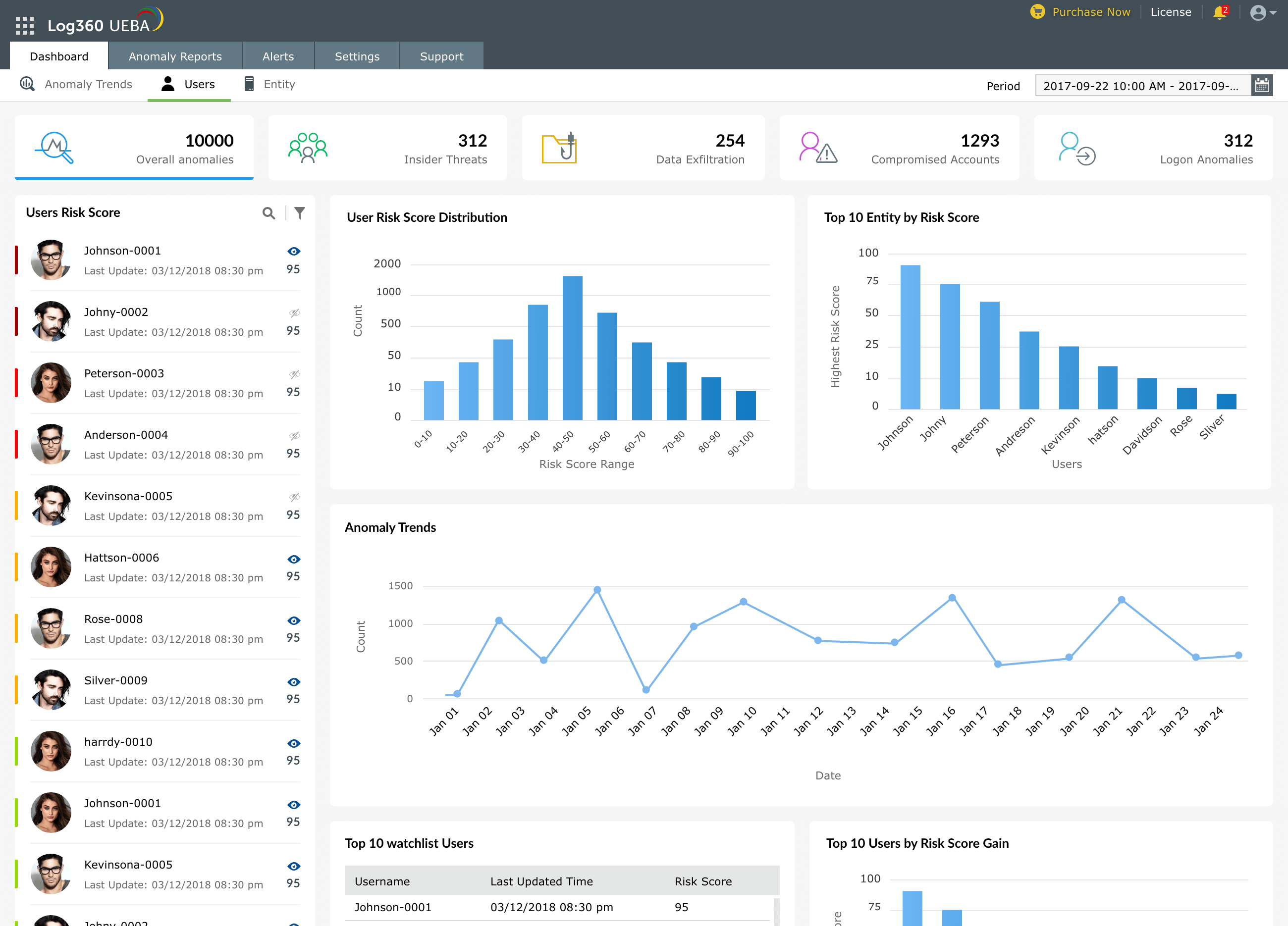
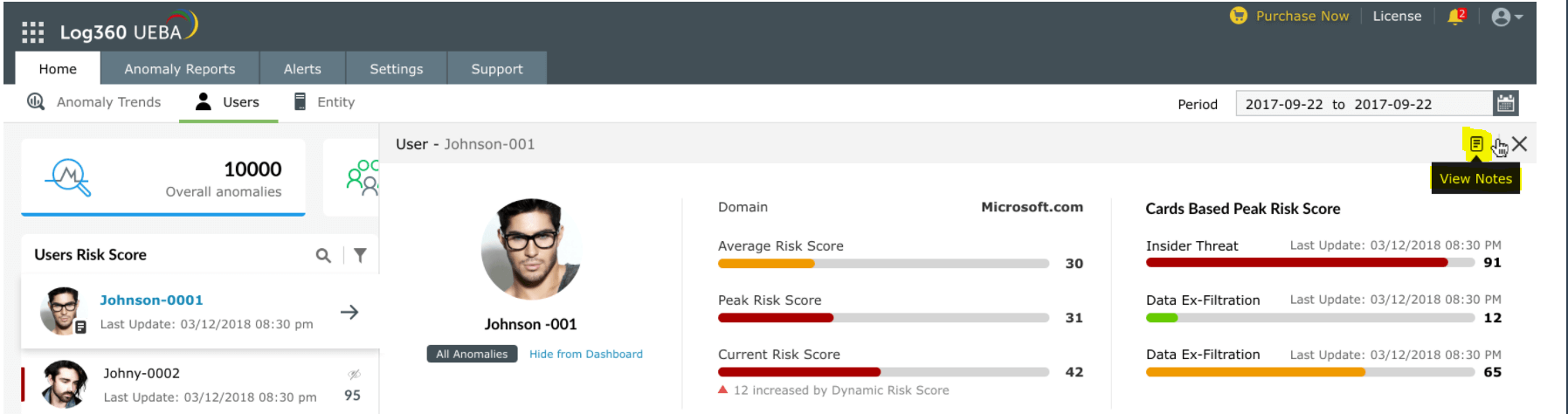
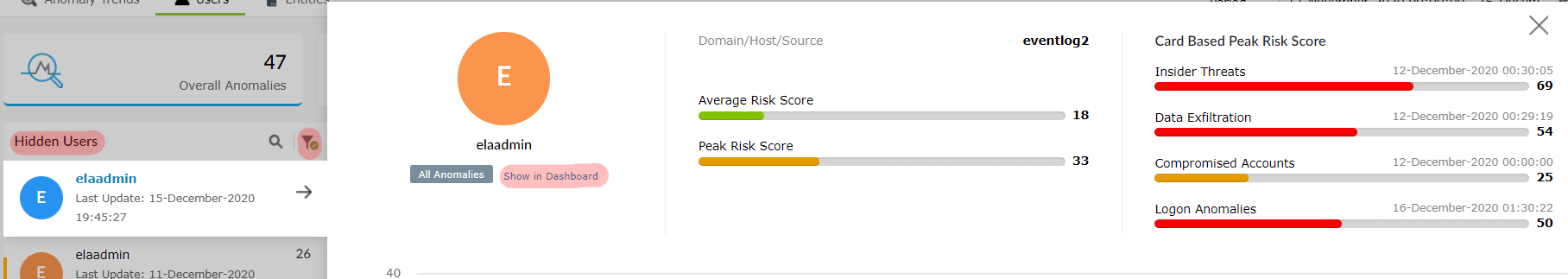
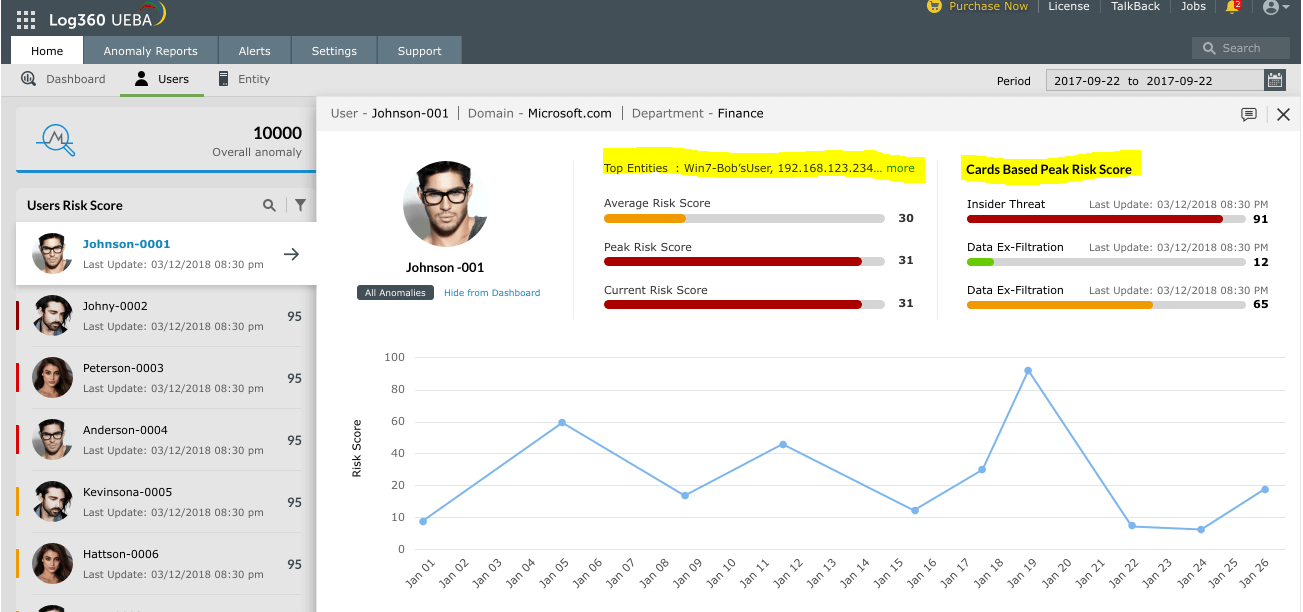
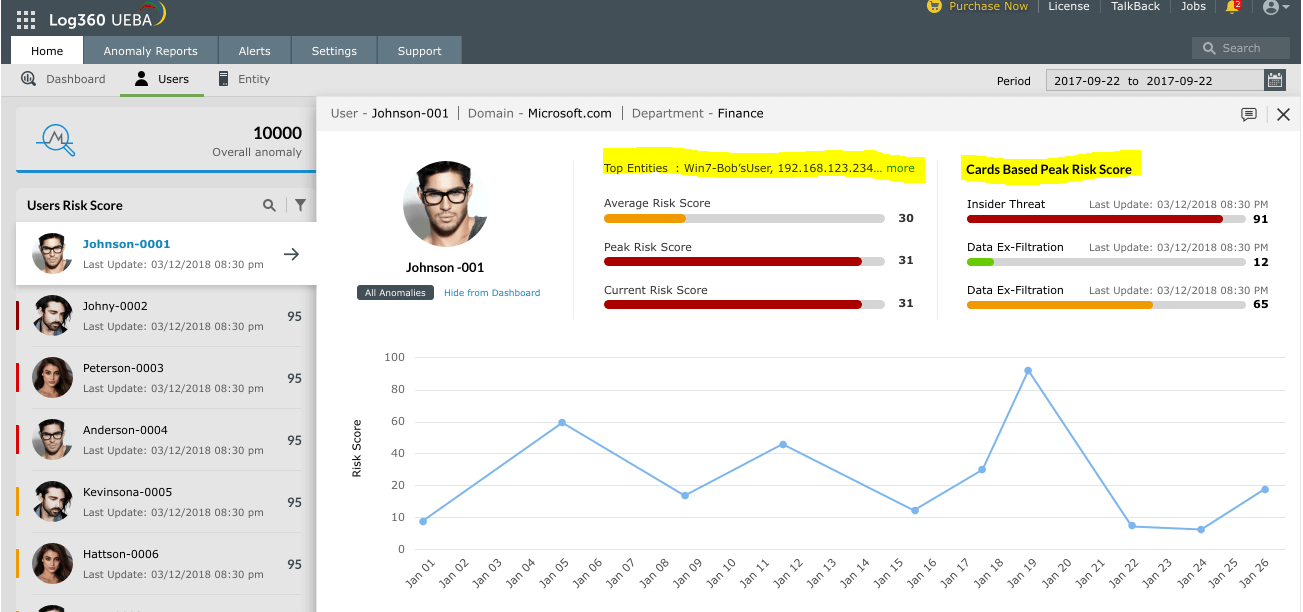
To get complete details about the anomalous activities performed by every user on the network:
- Navigate to Users' dashboard.
- A pane on the left hand side will display every user on the network and their associated risk score.
- Click on the user whose details you wish to see.
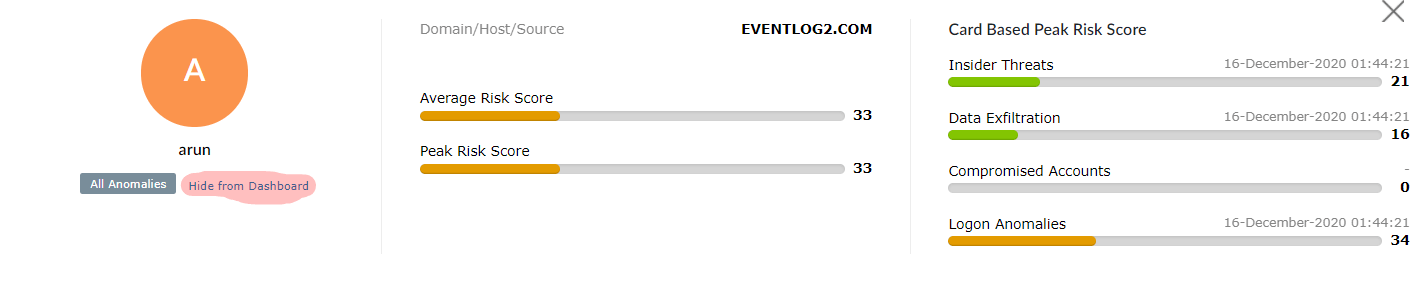
- A widget will open to show the user's Average Risk Score, Peak Risk Score, and risk scores associated with four types of threats:
- Insider threats
- Data exfiltration
- Compromised accounts
- Logon anomalies
This widget will also show:
- the top entities that the user is known to be associated with.
- User's risk score trend over time.
- All anomalous activities performed by the user along with the time of such activity.
 User's anomalous activities and associated entities
User's anomalous activities and associated entities
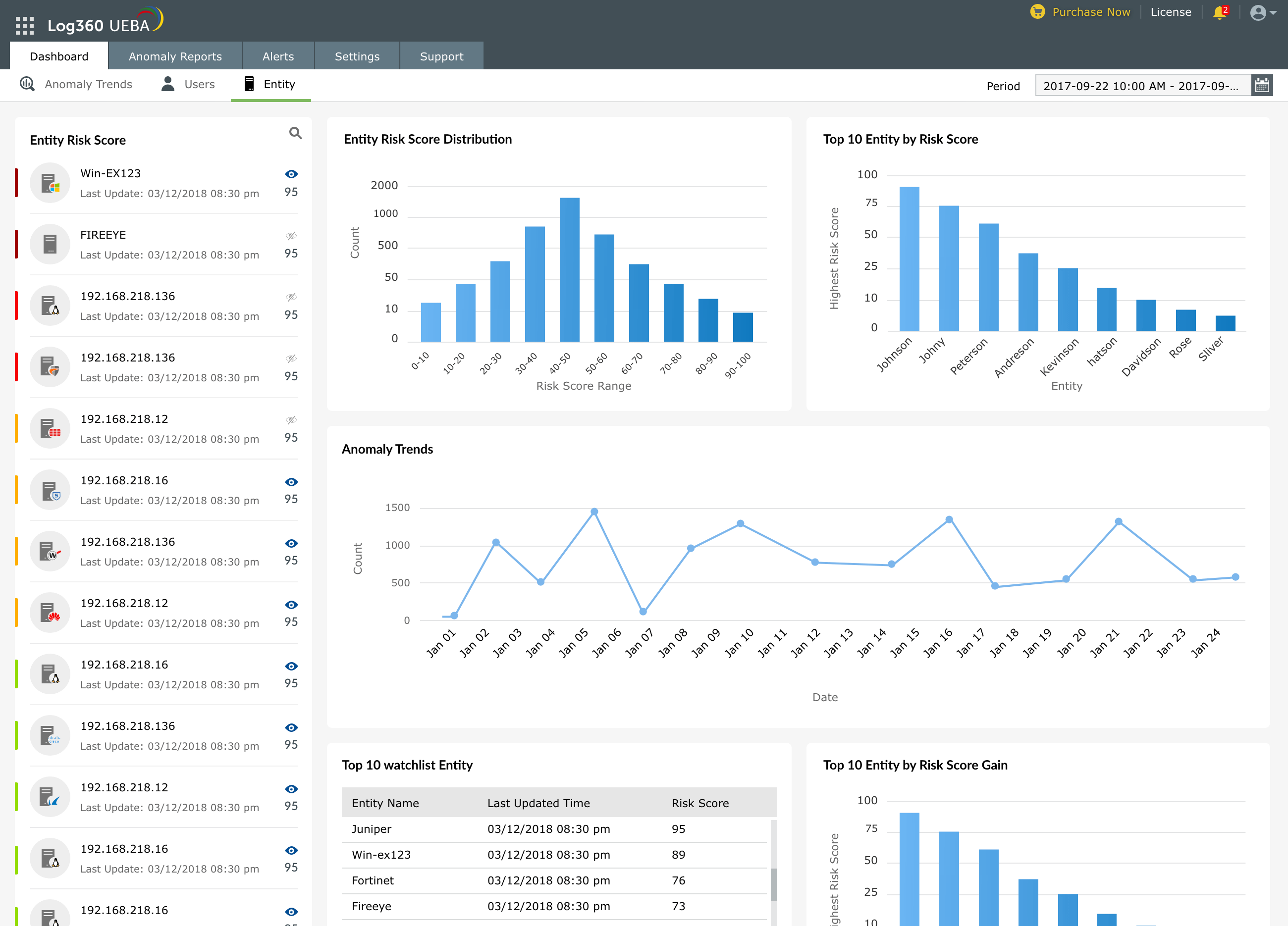
Anomalous entity behavior
Adding notes about users' and entities' anomalous activities
Technicians can select any user or entity from the Users' or Entities' Dashboard, and add or update notes about them. The technician entering the note and the timestamp will also be recorded. Notes help the security team to document and share their findings, and to collaborate efficiently.
To add a note about a user:
- Navigate to the Users' Dashboard
- Select a user and click on View Notes
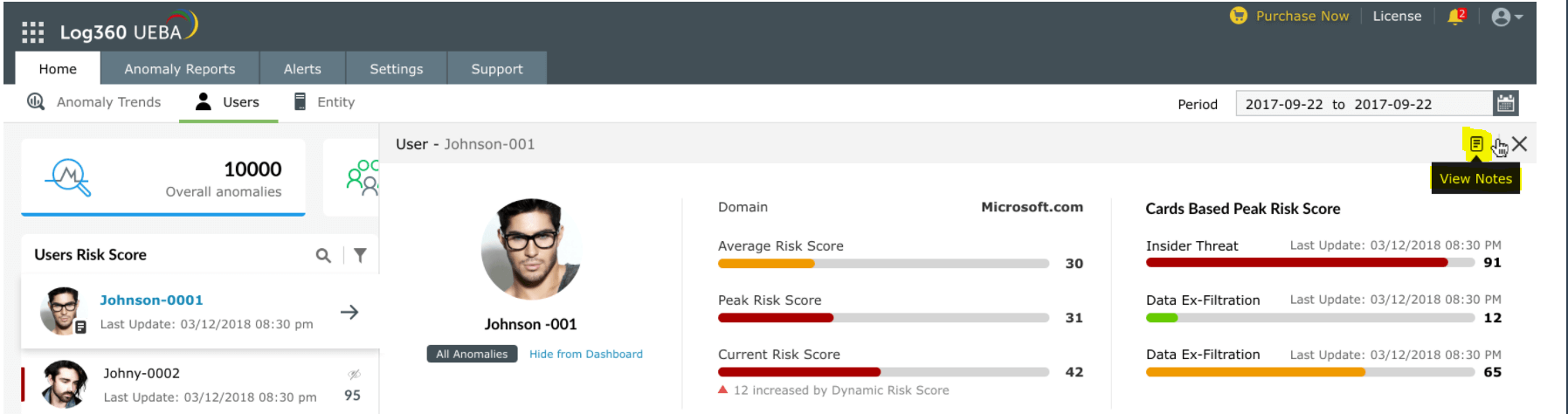
- Key in your notes and click on Add Note
Notes can also be updated or deleted when required. A similar process can be followed for adding or updating notes about entities.
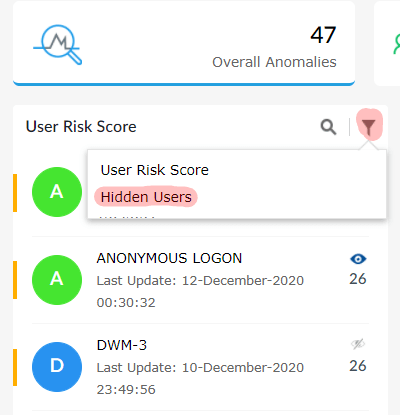
Hiding users and entities from dashboard
 User's anomalous activities and associated entities
User's anomalous activities and associated entities