Computer Configurations
Computer configurations are configurations deployed by an administrator to maintain the computers of a network in a schematic and consistent way. Computer configurations fast-track certain routine and essential activities like implementing policies, patching and lot more. This document comprises the system configurations that can be applied to computers belonging to Windows domain. These configurations are applied either during system startup or refresh interval. Ensure that you have defined the scope of management before executing the configurations.
Importance of computer configurations
Computer configurations help IT administrators automate some of the routine tasks like, patching windows and other third-party software, implementing security policies, and so on. We have many predefined Computer configurations available at your disposal.
To create and deploy a computer configuration:
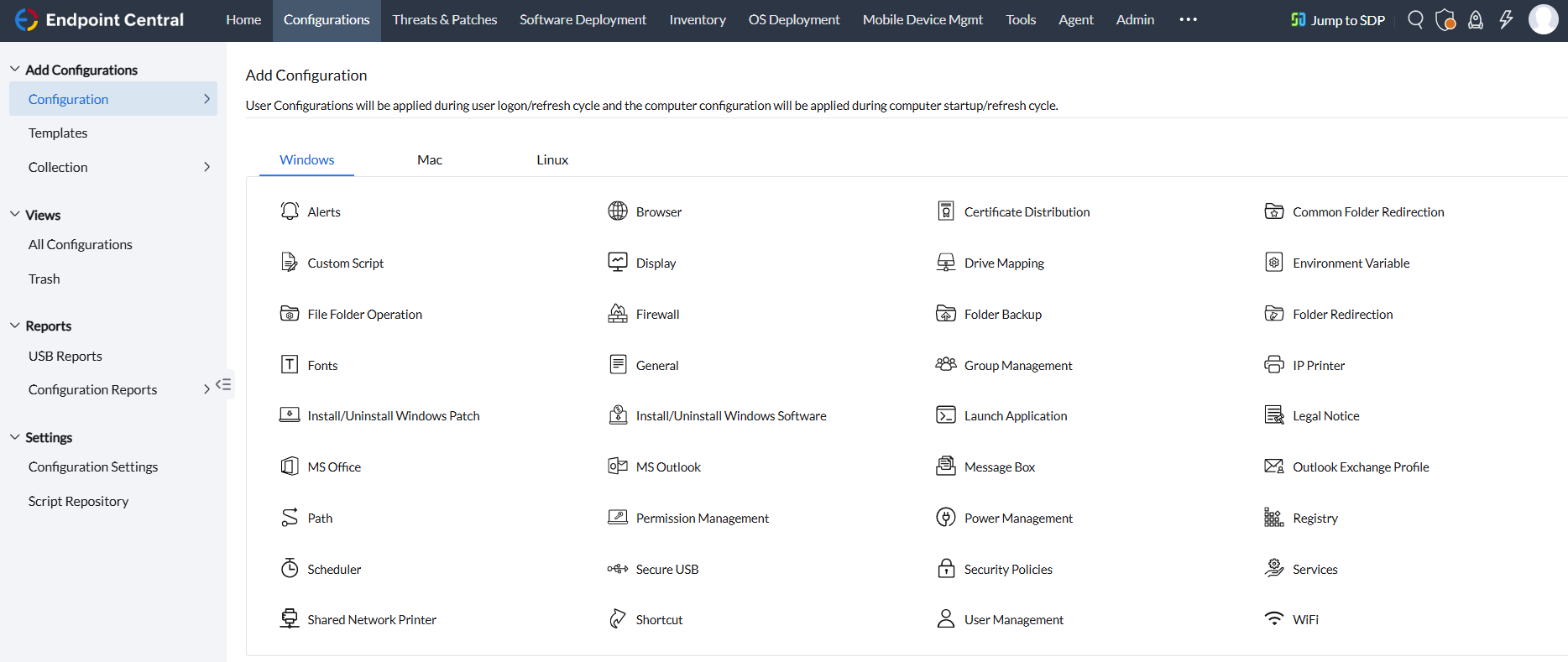
- Navigate to the Configuration tab. Select the Create Configuration and choose the Windows Operating system.
- This will list all the supported configurations for computers (Windows) and users as well.
- Select and desired configuration and click computer
- Configure the requirements and select the target based on Remote office or Domain
- Note: you can exclude computers if you wish do so.
- You can choose the configuration to be either deployed or saved.
Automate computer configurations
Manually searching each computer to identify poor compliance, security or consistency can be a daunting task. Custom scripting also gets complicated given the multitude of other admin activities. This is why automating these configurations is the key. Our product helps you automate the whole of your configuration management. You can choose among the 30+ pre-definded configurations suitable for your network, choose a deployment window of your choice and also target the computers of your choice. These configurations greatly helps you save your time and efforts.
Endpoint Central supports the below mentioned configurations that cover the functionalities of 4 major categories extensively:
Security Configuration
Hardening the security of your endpoints using the following security configurations:
- Certification Distribution - Distribute digital certifications used in Windows machines.
- Firewall - Configure firewall profiles/rules.
- Install/Uninstall Patch - Install or uninstall Windows patches from a central location
- Permission Management - Grant or revoke permission on the files, folders and registry.
- Secure USB Devices - Block or unblock the use of the USB devices.
- Security Policies - Security settings to manage restrictions.
Productivity Configuration
Amp up the productivity of your network by deploying the following computer configurations to all the computers in your network.
- Custom Scripts - Write and run your own scripts them to configure machines.
- Environment Variables - Add, modify, or remove a system environment variable.
- IP Printer - Add or delete the IP Printer connection in computers.
- Install/Uninstall Software - Install or uninstall MSI or EXE softwares.
- Path - Add path prefixes that certain applications, utilities, and functions use for searching an executable file.
- Power Management- Adjust computer's power settings to save energy.
- Registry - Change the values in the registry in the workstations.
- Scheduler - Schedule any program, task or a script to run at a specified time.
- Services - Change the settings for the services available.
- Shortcut - Add shortcuts to the computers from a central point.
- WiFi - Configure Wif-Fi profiles for all your systems.
Desktop Configuration
Desktop configurations can be applied to suit one's requirements. Deploy the below mentioned computer configurations & save ample amount of time in managing the desktops.
- Common Folder Redirection - Change the location of the All User Shell folders that are shared by all the users.
- Display - Configure the display settings of Windows desktops by customizing according to your preference.
- File Folder Operation - Copy, move, rename, delete files and folders in computers.
- Fonts - Install fonts for computers.
- General - General settings of the computers in your network.
- Group Management - Add, modify, or delete local groups from the computers.
- Legal Notice - Display announcements or legal notices when the user logs in.
- Message Box - Display warning or error message on system startup
- User Management - Add, modify, or delete local users from the computers.
Application Configuration
Use the following computer configuration to launch an application during start up or before shutdown of computers in your network:
- Launch Application- Launch an application during startup or shutdown of the computer.




