Firewall Analyzer introduces insider threat detection to strengthen the network security. It collects the usage data of network users from firewall logs and presents the user activity information. It uses the Active directory user data and services/categories data. It groups the information based on users - websites accessed and bandwidth used, top users by cloud applications/categories, top cloud applications by service categories.
With Firewall Analyzer you can
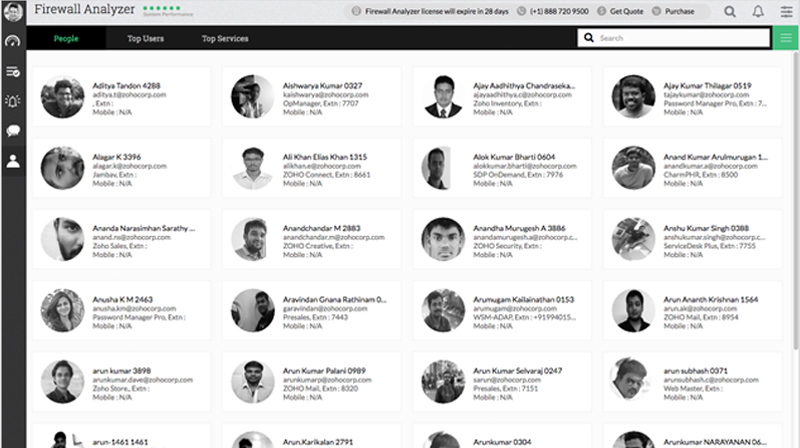
- Import network users from Active Directory
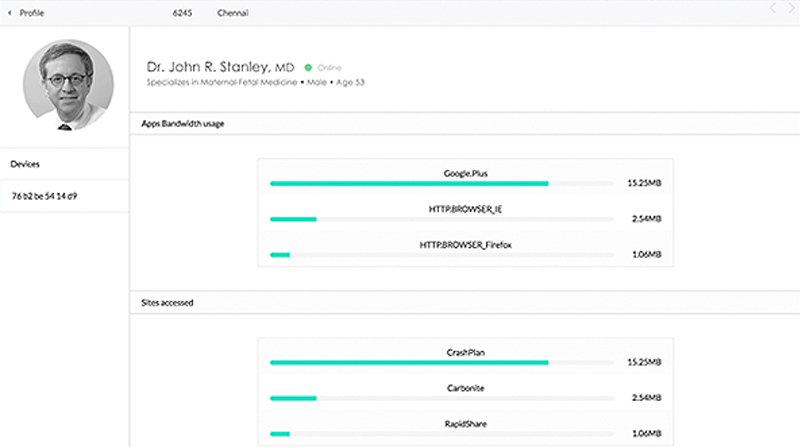
- Drill down to individual user web activity
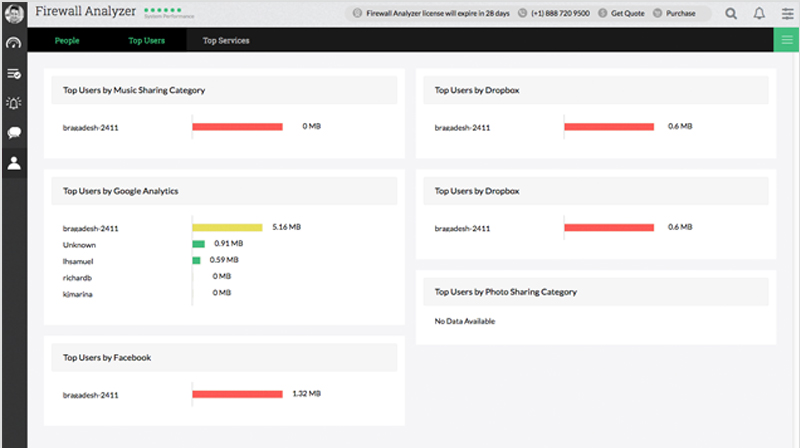
- Find top users across various service categories
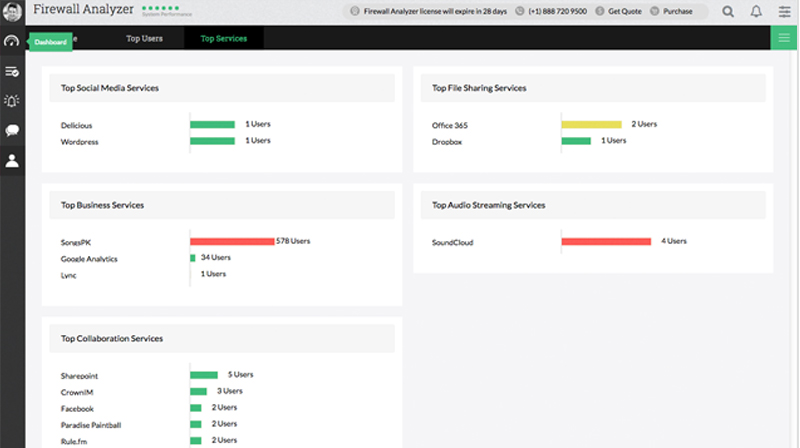
- Identify top web services attracting most users