Increasing data traffic, sophisticated attacks, and stringent compliance requirements make it critical to ensure the integrity of your firewall policiesand configurations. This is where ManageEngine’s Firewall Analyzer comes in—a comprehensive solution designed to help you monitor, audit, and analyze your firewall to ensure its security, compliance, and performance are optimized.
Firewall security manager: manage, monitor, and strengthen your firewall
A Firewall Security Manager plays a pivotal role in ensuring that your firewall is not only secure but also compliant with the various industry standards and best practices. ManageEngine Firewall Analyzer provides a holistic approach to firewall security management, empowering administrators to:
- Monitor firewall policies and manage changes.
- Audit firewall securityand adhere to compliance standards.
- Analyze anomalous incidents and ensure adherence to firewall best practices.
Monitor and manage firewall policies effectively
One of the critical aspects of a secure firewall is well-defined, clean, and optimized firewall policies. Firewall Analyzer enables you to not only monitor your existing policies but also analyze and modify them for improved security.
- Analyze and modify firewall policies:Over time, your firewall policies may accumulate redundant or outdated rules that may no longer be effective. Firewall Analyzer allows you to analyze your firewall rules easily and policies and modify them as needed. This process helps streamline your firewall’s rule set, ensuring that only valid and effective policies are in place.
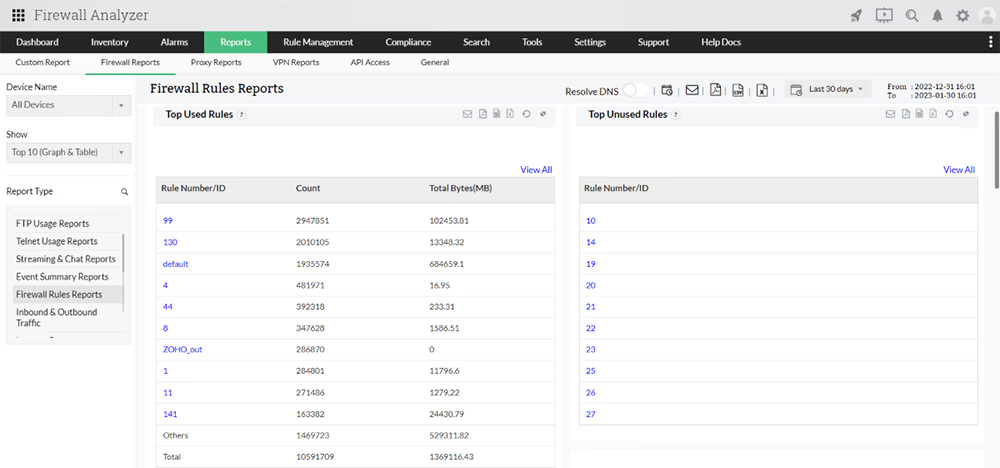
- Track usage patterns:By monitoring firewall policies, Firewall Analyzer gives you the ability to track usage patterns, identifying policies that are rarely used or entirely unused. This insight allows you to weed out unnecessary policies, reduce the potential attack surface, and improve firewall performance.
- Identify anomalies in policies:Often, network security loopholes are created by anomalies within firewall policies, such as misconfigurations, gaps in access controls, or conflicting rules. Firewall Analyzer helps you scan and identify such anomalies, enabling you to address them before they can be exploited by attackers.
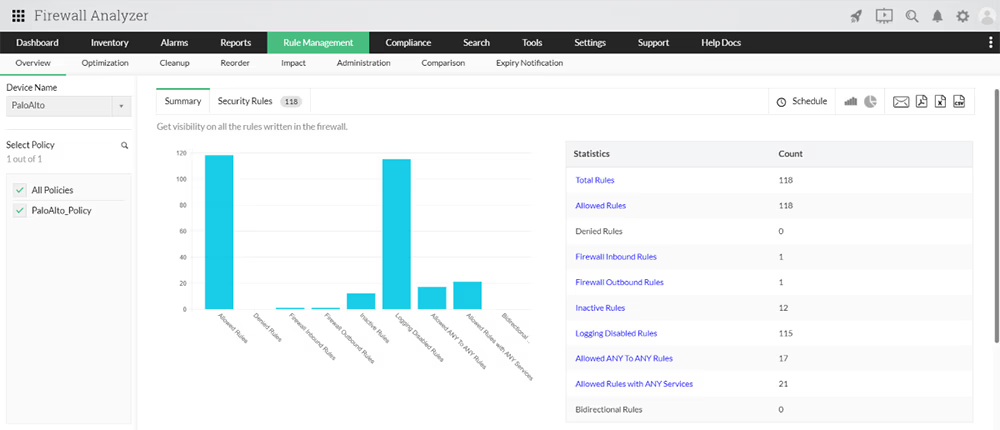
- Optimize firewall performance:By eliminating unnecessary or unused rules and fine-tuning the existing ones, Firewall Analyzer helps you improve your firewall’s performance. This optimization ensures your firewall operates efficiently, without burdening the system with redundant or outdated rules.
Manage policy changes with precision
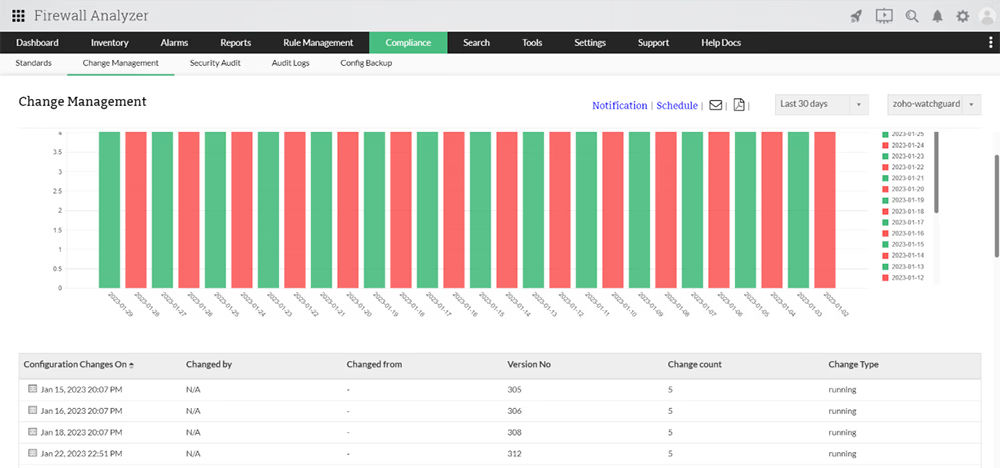
In a dynamic IT environment, firewall policies are subject to frequent changes. However, policy changes should only be made by authorized administrators, and the changes themselves must be monitored to ensure they do not introduce security risks.
- Ensure authorized changes:Firewall Analyzer helps ensure that only authorized administrators are allowed to make changes to your firewall policies. This feature is crucial for preventing unauthorized access and modifications, which could lead to security vulnerabilities.
- Track policy changes:With Firewall Analyzer, you can track the exact changes made to your firewall policies, providing a comprehensive audit trail. You can compare the firewall configurations before and after the changes to assess their impact on network security.
- Receive instant notifications:Stay ahead of potential risks by receiving instant notifications whenever a change is made to your firewall. These alerts ensure that you are always informed and can take quick action if a policy change jeopardizes your security posture.
Fortify your network with enhanced firewall management
- Monitor, modify, and analyze firewall policies with ease.
- Get instantly alerted about policy changes, from anywhere.
- Be ready for audits with periodic compliance reports.
Audit firewall security and ensure compliance
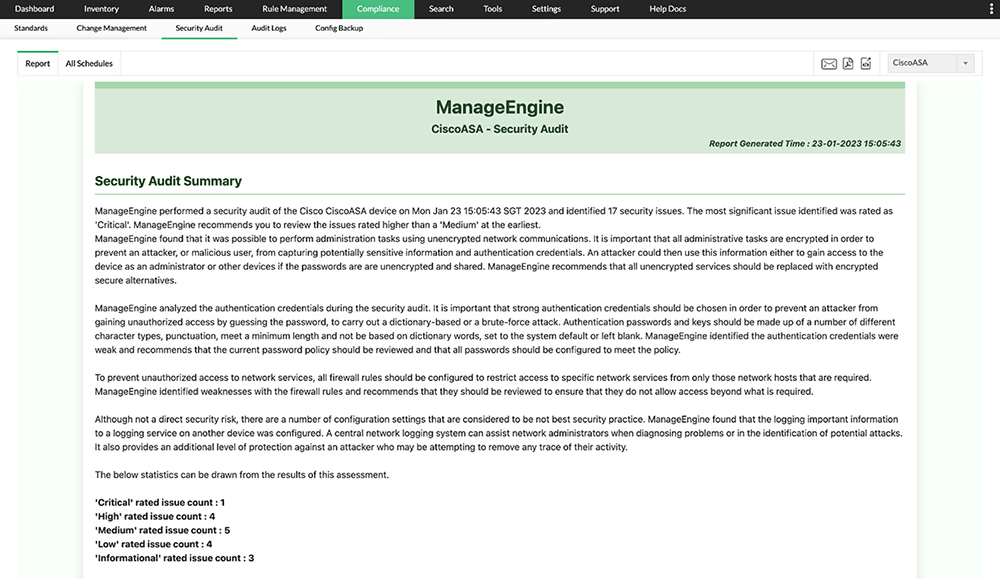
Maintaining firewall security involves regularly auditing your firewall’s configuration to identify potential vulnerabilities and compliance gaps. Firewall Analyzer offers in-depth security auditing capabilities to help you stay proactive in strengthening your firewall defenses.
- Analyze vulnerabilities and severity:Firewall Analyzer continuously monitors your firewall for vulnerabilities. The tool evaluates the impact and severity of each vulnerability and provides actionable insights on how to address them. This proactive approach helps you mitigate risks before they can be exploited.
- Recommendations for fixing vulnerabilities:Firewall Analyzer doesn’t just stop at identifying vulnerabilities; it also offers practical recommendations for fixing them. These actionable suggestions help you remediate potential threats quickly and efficiently.
- Adhere to security best practices:To ensure that your firewall remains strong and secure, Firewall Analyzer provides guidance on firewall security best practices. By following these best practices, you can strengthen your firewall’s defenses and stay ahead of evolving cyber threats.
- Continuous network compliance monitoring:Compliance is an essential aspect of firewall security. With Firewall Analyzer, you can ensure that your firewall is continuously adhering to critical industry standards and regulations. By conducting regular compliance audits and keeping tabs on your firewall’s configurations, you can ensure that your firewall is always audit-ready.
Adhere to industry compliance standards
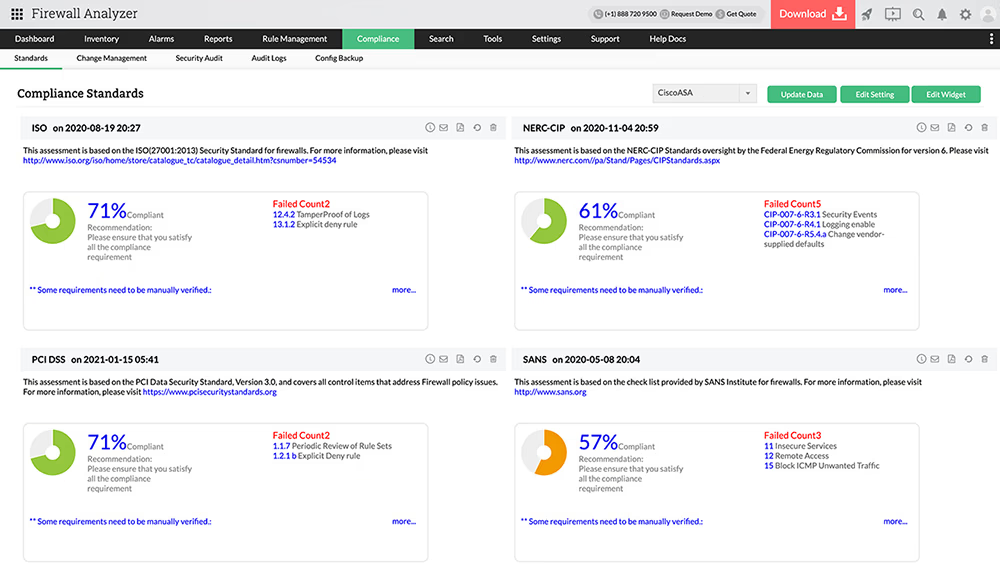
Compliance with industry regulations such as PCI DSS, ISO 27001, NIST, and NERC CIP is a critical requirement for many organizations. Failure to adhere to these standards can result in legal penalties, security vulnerabilities, and loss of customer trust. Firewall Analyzer makes it easy to stay compliant and prepared for audits.
- Ensure adherence to compliance standards:Firewall Analyzer helps ensure that your firewall complies with important security standards and frameworks, including PCI DSS, ISO 27001, NIST, SANS, and NERC CIP. The tool continuously checks your firewall against these standards, ensuring that your organization meets all necessary requirements.
- Periodic compliance reports:Preparing for an audit can be a time-consuming task. Firewall Analyzer simplifies this process by generating periodic compliance reports that highlight your firewall’s adherence to key standards. These reports help you prepare for audits and ensure that your organization remains compliant year-round.
Analyze anomalous incidents and ensure firewall best practices
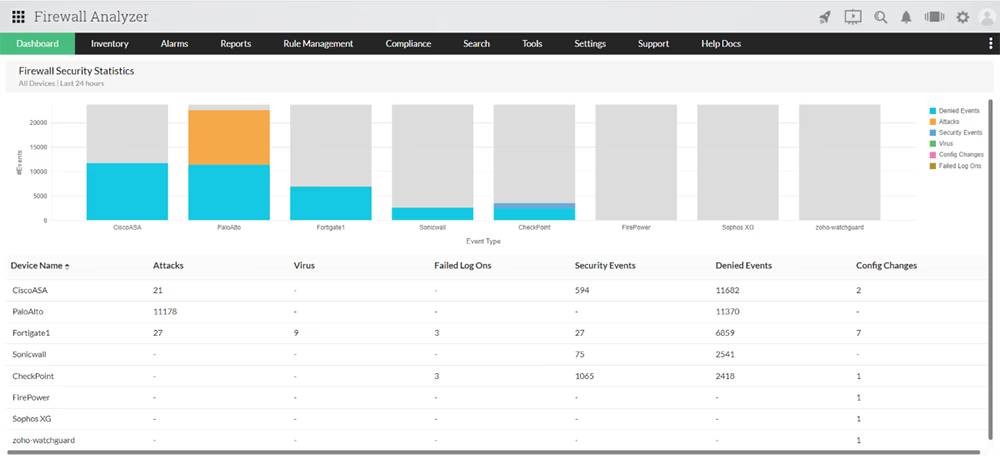
Incident analysis is a vital part of maintaining firewall security. By analyzing logs, bandwidth usage, and administrator behavior, Firewall Analyzer helps you identify anomalies and mitigate potential security risks.
- Identify anomalies in firewall logs:Firewall Analyzer continuously monitors firewall logs for any unusual activity, such as abnormal bandwidth usage or security events. By analyzing these logs, you can detect any suspicious activity or potential security breaches and take action before they escalate.
- Monitor administrator behavior:Firewall administrators play a crucial role in managing firewall policies and configurations. Firewall Analyzer helps you monitor the behavior of firewall administrators, ensuring that their actions align with your organization’s security policies. This monitoring helps detect any unauthorized or inappropriate actions that could compromise the firewall’s integrity.
To know more about security standards compliance, refer Firewall Security Standardspage.
FAQs - Firewall Security Management
What is Firewall Security Management?
+How does Firewall Security Management help?
+What are the best practices for firewall security management?
+Thank you for your feedback!