Archive Firewall and Security Device Logs for Compliance Audit
Firewall Logs Archiving
Logs received from firewalls and squid proxy servers are archived at specific intervals. You can load these log archives into the database at any time, and generate reports for specific activity. However, log archiving takes up disk space, but it is required for forensic analysis and compliance audit requirements.
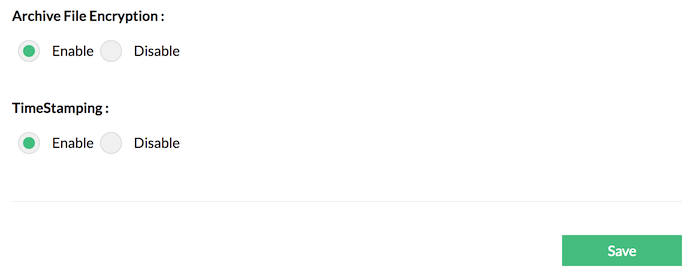
Encrypting Archived Log files
Now, Firewall Analyzer encrypts the Firewall log archive files to ensure the log data is secured for future forensic analysis, compliance and internal audits.
Hashing
The hashing of the archive log data files further secures the event log data.
Time stamping
The time stamping technique ensures that the archive data files are tamper proof. If there is a modification of file, this technique will reveal that the file has been tampered.
The three point security keeps the archive log data safe.
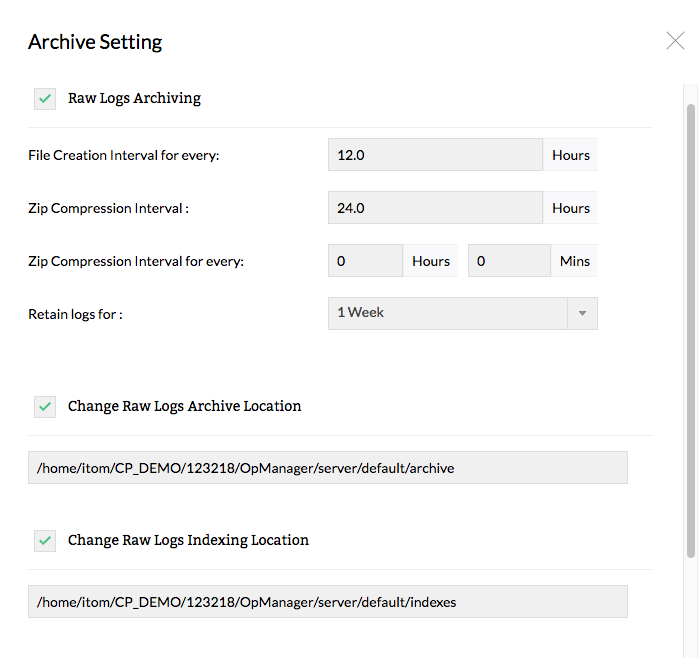
Configurable Log Archiving Intervals
The default log archiving interval creates a log archive file of the all the received raw logs every 24 hours. And these log archive files are then compressed (zipped) after every 7 days, to conserve hard disk space. You can configure the archive file creation and compressed file creation any time depending on how often you need to archive event logs. You can even disable log archiving entirely if needed.
Reports on Archived Event Logs
At any time, you can load Firewall log archive file into the Firewall Analyzer database and generate reports from the archived log data.
Detailed Event Log Archiving
Every log archive file that is created, is stored along with the time of archive creation, size of the archive, and the host whose event logs have been archived. This makes it easy to load and generate reports from archived logs.
Instant Firewall Log Archiving
Firewall Analyzer includes options to instantly generate log archives for all logs collected so far. All logs collected will be archived, irrespective of the log archiving interval defined. In this way, you can create and load archived files into the database at any time.
Thank you for your feedback!