Virus, Attack, Security, and Spam Reports from Firewall Logs
Detailed Security, Virus, Attack and Spam Analysis
Firewall Analyzer includes instant reports on viruses, attacks and security breach in your network. These reports instantly show you the viruses active on the network, the hosts that have been affected, and more. With these reports it is easier for IT to do business risk assessment, detect problems and resolve them as soon as they are found.
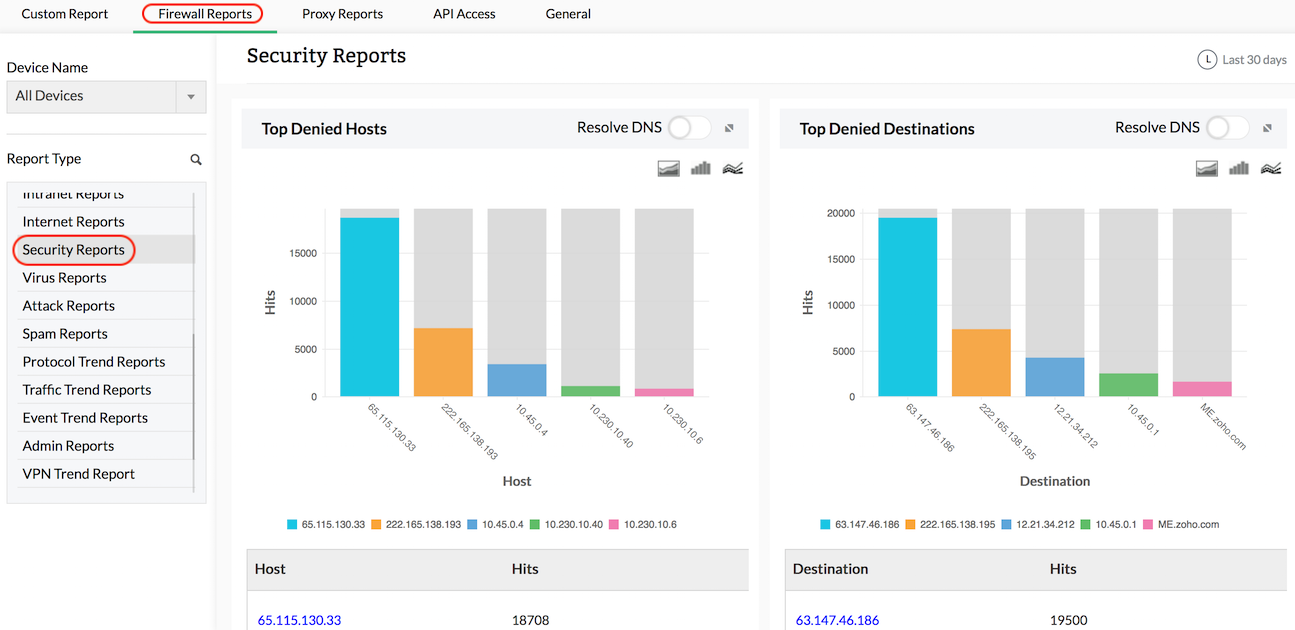
Security Reports
Security reports give detailed information on possible security threats to the network. Reports include information on top denied hosts, denied protocols, and top security events generated. These reports give more insight into possible security threats, and help IT determine if security policies across the network need to be revised.
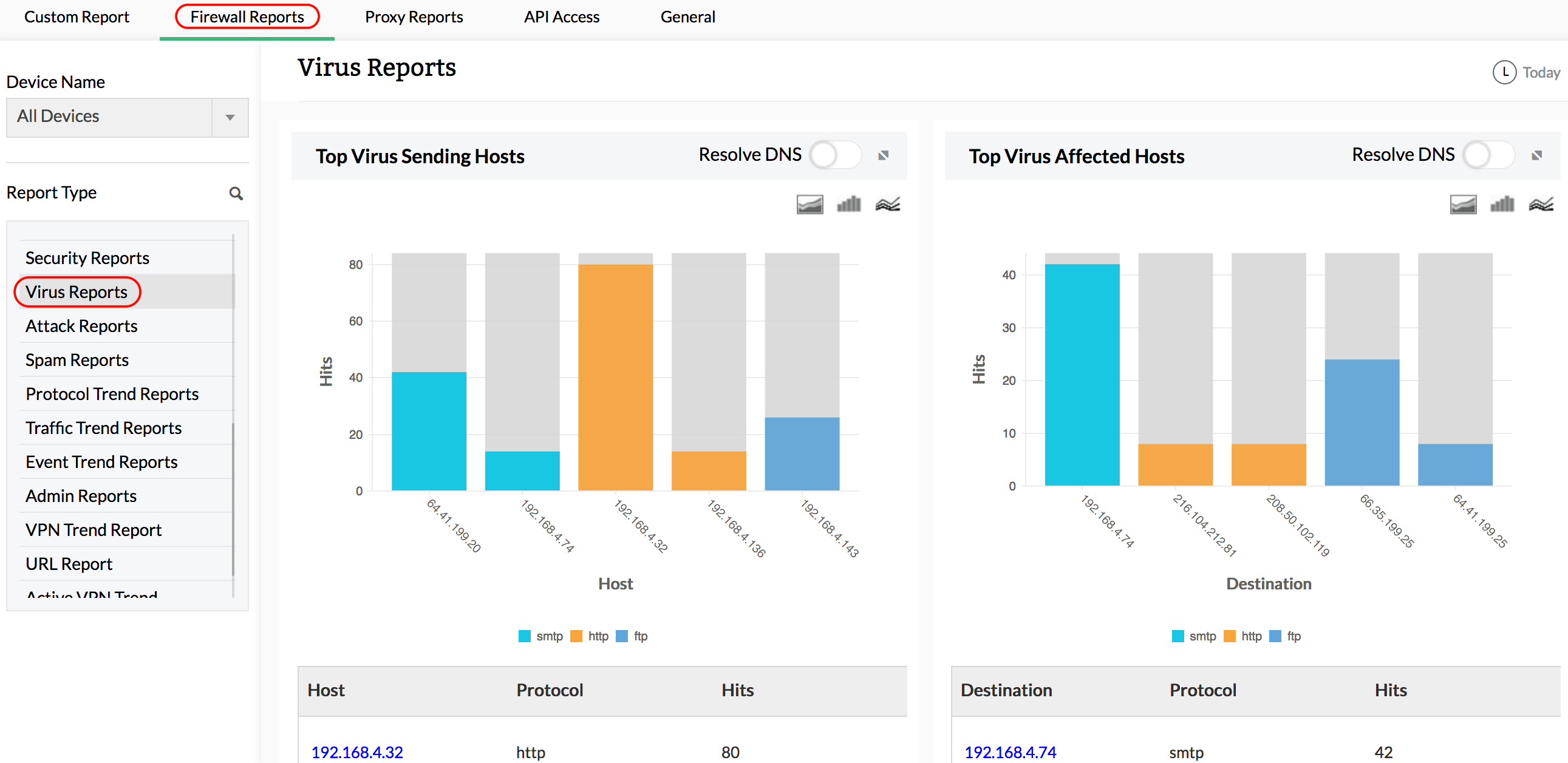
Virus Reports
Virus reports give in-depth information on virus attacks, hosts infected, severity of the attack, subtype, and more. With drillable details to the raw log level on top viruses and top protocols used by viruses, the complete details of the virus related raw log is available. The raw log message make troubleshooting and problem resolution faster and more efficient.
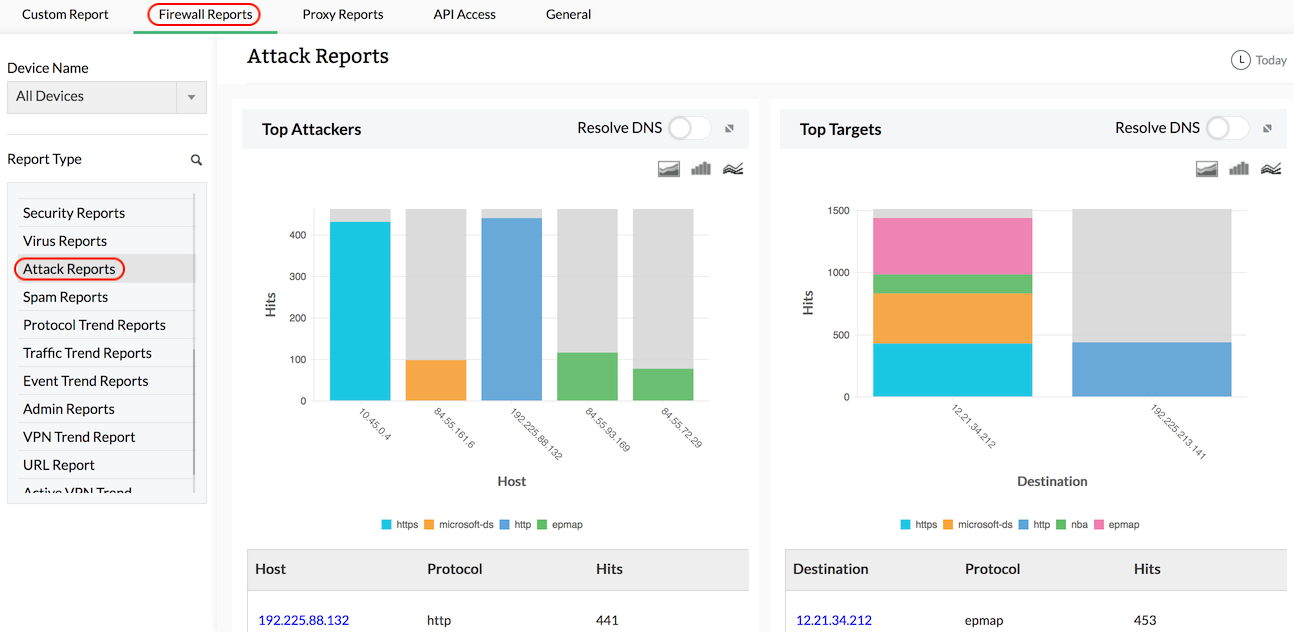
Attack Reports
Attack reports give detailed information on possible network attacks, peer-to-peer attacks, etc. Reports include information on top attackers, top targets, protocols used for the attack, etc. Top attackers report distinguishes between two scenario like, one user attacking large number of hosts (say 1000) with particular type of attack and one user attacking a single host with large number (say 1000) of particular type of attack. These reports gives the IT administrators with insight to counter such attacks.
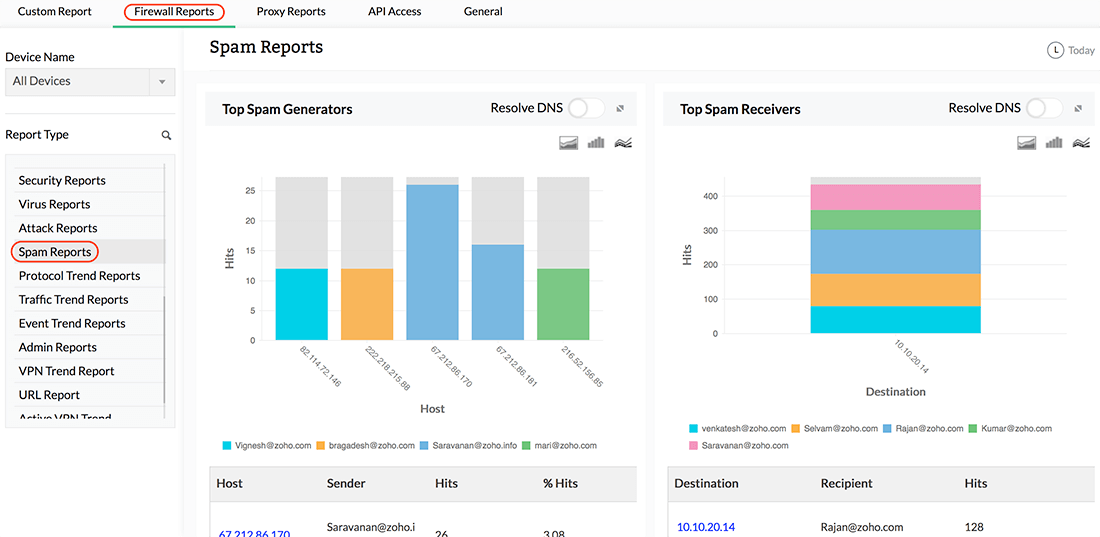
Spam Reports
Spam reports give detailed information on spam activity in the network. Reports include information on top spam generators, top spam receivers, and top rules allowing spam. These reports give more insight into possible spam threats, and help IT department control the spam activity across the network.
Stay updated on the cyber security incidents of your network with Firewall Analyzer's in-depth log-based reports. Signup for a personalized demo now or avail a free 30-day trial.
Featured links
Firewall Rule Management
Manage your firewall rules for optimum performance. Anomaly free, properly ordered rules make your firewall secured. Audit the firewall security and manage the rule/config changes to strengthen the security.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Log Management
Unlock the wealth of network security information hidden in the firewall logs. Analyze the logs to find the security threats faced by the network. Also, get the Internet traffic pattern for capacity planning.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Firewall Alerts
Take instant remedial actions, when you get notified in real-time for network security incidents. Check and restrict Internet usage if banwidth exceeds specified threshold.
Manage Firewall Service
MSSPs can host multiple tenants, with exclusive segmented and secured access to their respective data. Scalable to address their needs. Manages firewalls deployed around the globe.
Thank you for your feedback!