- Cloud Protection
- Compliance
- Data Leak Prevention
- Bring your own device
- Copy protection
- Data access control
- Data at rest
- Data in transit
- Data in use
- Data leakage
- Data loss prevention
- Data security
- Data security posture management
- Data security breach
- Data theft
- File security
- Incident response
- Indicators of compromise
- Insider threat
- Ransomware attack
- USB blocker
- BadUSB
- USB drop attack
- Data Risk Assessment
- File Analysis
- File Audit
- Threat Glossary
Cybersecurity risk assessment
Key takeaways
- Cybersecurity risk assessment is the process of analyzing an organization’s IT and digital infrastructure to identify potential threats and vulnerabilities.
- Cybersecurity risk assessments should be conducted periodically and whenever there are significant changes such as product updates or modifications to business workflows.
- A cybersecurity risk assessment serves multiple purposes, including identifying vulnerabilities, minimizing the risk of data breaches, and ensuring adherence to compliance requirements.
- The assessment process involves inventorying IT and digital assets, analyzing and prioritizing risks, and creating a comprehensive risk catalog.
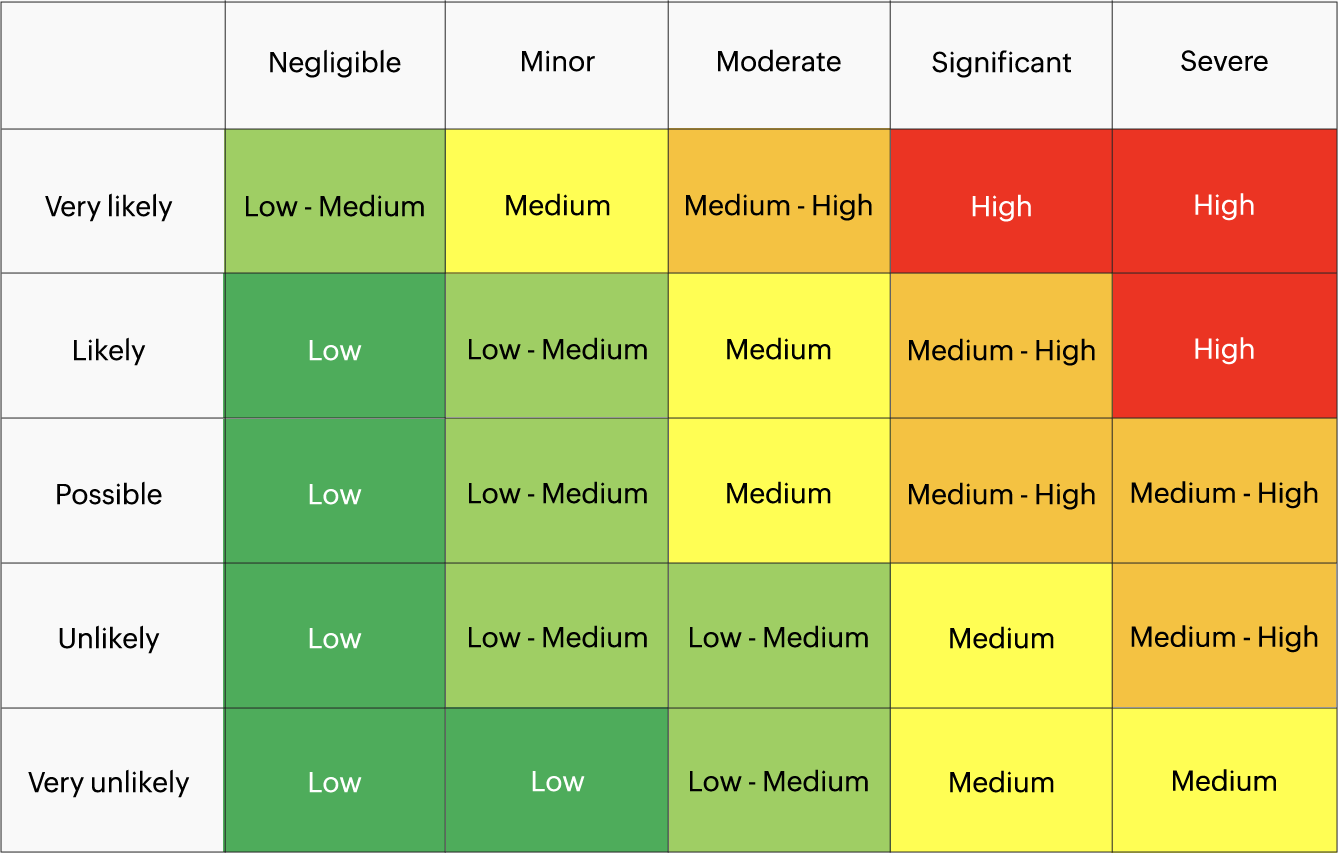
- The 5x5 risk assessment matrix provides insights into the severity and likelihood of risks, helping organizations prioritize their mitigation efforts.
Common frameworks used by organizations for conducting risk assessments include Factor Analysis of Information Risk (FAIR), the Operationally Critical Threat, Asset, and Vulnerability Evaluation (OCTAVE), and Threat Agent Risk Assessment (TARA).
What is a cybersecurity risk assessment?
A cyber risk assessment is the process of analyzing your organization's IT and digital infrastructure, such as laptops, mobiles, and software applications for potential threats. Similar to a maze, cybercriminals identify a vulnerable endpoint and make their way up to the sensitive data in servers. With cyber risk assessments, you gain insights into your network's maze-like structure, starting from vulnerable endpoints and extending to critical servers. This information will help you stay on track with your security posture. This is why performing a periodic risk assessment is imperative.
When should a risk assessment be carried out?
Cyber risk assessments must be carried out during product launches, after changes are made to existing business workflows, and on a periodic basis. Certain data compliance regulations also have requirements stating the intervals at which risk assessments must be performed. For example, HIPAA requires organizations storing PHI to perform annual risk assessments.
Why is cybersecurity risk assessment important?
The importance of conducting periodic cybersecurity risk assessments is multifold. The most critical benefits include:
- Identifying vulnerabilities in your environment: Periodic risk assessments help uncover weaknesses across your networks, endpoints, applications, cloud services, and user behavior. By gaining early visibility into misconfigurations, excessive permissions, and insecure practices, organizations can address issues before they are exploited by attackers.
- Adhering to regulatory compliance: Many data protection and cybersecurity regulations mandate regular risk assessments. Conducting them consistently helps ensure compliance with industry standards, supports audit readiness, and demonstrates due diligence in safeguarding sensitive data, while also strengthening your overall security posture.
- Reducing the risk of a data breach: By proactively identifying and prioritizing risks, organizations can close security gaps that could otherwise lead to unauthorized access, data leakage, or service disruption. This preventive approach significantly lowers the likelihood and impact of cyber incidents.
- Mitigating the financial implications of incidents: Cyber incidents often result in significant financial losses due to downtime, recovery efforts, legal penalties, and reputational damage. Regular risk assessments help detect and mitigate risks early, reducing the cost of remediation and preventing avoidable expenses down the line.
Cyber risk assessment process
A cyber risk assessment is a five-step process, from meticulously curating IT and digital infrastructure—including networks, endpoints, identities, applications, and data—to assessing and securing them against potential threats. The steps include:
- Curating IT and digital infrastructure: As organizations embrace technology by expanding their IT arsenal, performing organization-wide risk assessments can get complex. To combat this, risk assessments are carried out by curating IT and digital infrastructure specific to a business unit, location, or department.
- Detecting threats and vulnerabilities: This includes identifying suspicious files, unauthorized access, and other unusual incidents that could compromise your network security.
- Analyzing the risks: The next step is to analyze the associated risks after you have identified potential threats and vulnerabilities. This involves assessing the likelihood of the vulnerabilities being exploited and the severity of the potential impact.
- Develop a risk catalog: Developing a risk catalog, periodically reviewing the changes in severity of known risks, and identifying new risks as they pop up can keep you on track with your organization's security goals. The database must highlight risk scenarios, identification dates, security controls, and risk levels.
- Prioritizing the risks: Prioritizing the risks by accounting for factors like the likelihood of exploitation and potential impact can help you with a high level understanding of your organization's risk landscape. The 5x5 risk matrix, or a grading of risks on a scale of 0 to 100, could be a great mechanism to prioritize risks.
Cybersecurity 5x5 risk assessment matrix
The 5x5 risk assessment matrix includes five rows and columns, with the columns representing the severity of the risk and the rows representing the likelihood of its occurrence. Risks can be categorized into 25 different cells, based on the severity of the risk and its likelihood. The spectrum varies from unlikely and not severe to highly likely and severe.
Cyber risk assessment framework
A risk assessment framework outlines an organization's approach to identify, assess, and manage risks to their IT and digital infrastructure. Depending on their network environment, organizations can opt to have their own custom-built framework or adopt industry standard frameworks. A few widely followed frameworks include:
- FAIR: The Factor Analysis of Information Risk is a quantitative framework that measures, manages, and communicates information risk.
- OCTAVE: The Operationally Critical Threat, Asset, and Vulnerability Evaluation framework defines a risk-based strategic assessment technique for security.
- Threat agent risk assessment (TARA): The Threat Agent Risk Assessment framework identifies, assesses, prioritizes, and controls cybersecurity risk based on threats.
Cybersecurity risk assessment checklist
- Define the assessment scope: Clearly define the IT environment to be assessed, including on-premises systems, cloud services, endpoints, applications, and third-party integrations.
- Identify and classify digital assets: Discover and classify critical systems and sensitive data based on business value, sensitivity, and regulatory requirements.
- Identify threats and vulnerabilities: Analyze potential threat vectors, known vulnerabilities, and security misconfigurations that could expose your organization to risk.
- Evaluate existing security controls: Assess the effectiveness of current technical, administrative, and procedural controls, and identify control gaps.
- Assess the impact of risks: Determine the likelihood and potential business impact of each identified risk.
- Strategize risk mitigation: Define strategies to reduce, transfer, accept, or avoid risks based on organizational risk tolerance.
- Implement security controls: Deploy and enforce appropriate controls to address prioritized risks.
- Monitor and reassess continuously: Continuously monitor the risk environment and reassess controls to address emerging threats and changes.
- Report findings and drive improvement: Document results, track remediation progress, and continuously improve your risk management program.
- Validate compliance alignment: Map risks and controls to applicable regulatory and compliance requirements to support audit readiness.
How can DataSecurity Plus prioritize and prevent cyber risk?
DataSecurity Plus provides a data risk assessment solution that identifies sensitive data across the network, analyzes the risks associated with the data identified, and prioritizes the risks, by assigning a risk score.
DataSecurity Plus is a solution equipped with features to:
- Generate reports on sensitive data, their type, location, and the amount of sensitive data across the network with data discovery.
- Analyze and assign risk scores to users and servers with security violations.
- Prioritize and classify risks with data classification.
- Adhere to the GDPR and HIPAA risk assessment guidelines with the GDPR risk assessment tool and HIPAA risk assessment software.
Try DataSecurity Plus' data risk assessment solution with a free, fully functional, 30-day trial.
Download the free trialFrequently asked questions
1. What should be the objective of an effective cybersecurity risk assessment?
The objective of an effective cybersecurity risk assessment is to provide clear visibility into an organization’s security risks by identifying critical assets, evaluating potential threats and vulnerabilities, and determining the likelihood and impact of exploitation. This enables organizations to prioritize risks, allocate resources effectively, and implement targeted controls that reduce exposure while aligning security efforts with business goals.
2. How often should you perform a cybersecurity risk assessment?
Cybersecurity risk assessments should be performed on a regular schedule and treated as an ongoing process rather than a one-time exercise. Even in the absence of major organizational changes, periodic assessments help account for evolving threat techniques, newly discovered vulnerabilities, and shifts in business priorities, ensuring that risk management efforts remain effective over time.
3. What are the key steps in a cybersecurity risk assessment?
The key steps in a cybersecurity risk assessment include identifying and cataloging IT and digital assets, assessing potential threats and vulnerabilities, evaluating the likelihood and impact of risks, prioritizing risks based on severity, and defining mitigation or remediation measures. The process also involves documenting findings and reviewing risks periodically to account for changes in technology, business processes, and the threat landscape.
4. How much does a cybersecurity risk assessment cost?
The cost of a cybersecurity risk assessment varies based on the size of the organization, the complexity of its IT environment, and the scope of the assessment. For small to mid-sized businesses, costs typically range from a few thousand to tens of thousands of dollars, while large enterprises or highly regulated organizations may incur higher costs due to broader infrastructure, compliance requirements, and in-depth analysis. Some organizations also use automated tools or internal resources to reduce costs.
5. What is the difference between a risk assessment and a vulnerability assessment?
A vulnerability assessment focuses on identifying and evaluating security weaknesses within systems, networks, or applications. In contrast, a risk assessment goes a step further by analyzing how those vulnerabilities could be exploited, the likelihood of such events, and the potential business impact. While vulnerability assessments highlight what is wrong, risk assessments help organizations understand which issues matter most and how to prioritize remediation efforts.
6. How do I prevent drive-by downloads effectively?
Keep your system, browsers, and plug-ins updated. Use advanced URL filtering, cloud app control, and CASB tools to block malicious downloads and stop drive-by exploits before they start.
