Cybercrime has been industrialised. And the industry is booming. Today, malware is mass-produced, marketed, and sold online like any other product — off-the-shelf, not targeted, and more affordable than ever. This is just the beginning. Zero-day exploits, advanced persistent threats (APTs), malware-as-a-service, dark web marketplaces, and living-off-the-land attacks are raising the stakes even further.
The question is no longer whether your business needs a comprehensive cybersecurity strategy. It's whether your current one is enough. The reality is, no endpoint security tool can block 100% of threats. Even the most capable next-generation antivirus with high detection accuracy (99%) is a critical first line of defence, but stopping an attack from entering is very different from detecting and neutralising one that already has. That missed 1% is exactly what Endpoint Detection and Response (EDR) was built to address.
What is Endpoint Detection and Response?
Endpoint Detection and Response (EDR) is an endpoint security solution that continuously monitors and audit endpoint activity, leveraging behavioural analytics and advanced data analysis to spot suspicious activity in real time. Once a threat is spotted, an endless loop of questions arises, because you cannot quite solve something that you don't understand. What is it? How did it get in? When did it happen? How far has it spread? But detection is only half the story. When a threat is confirmed, EDR moves fast to contain it, neutralise it, and restore endpoints to a pre-attack state.
How does EDR work?
EDR is grounded in one core principle: Assume breach mindset. Not if a threat gets through, but when.
EDR continuously monitors endpoints in real time, alerting security teams to potential threats and equipping them to respond swiftly. It operates across three fundamental pillars: detection, investigation, and response.
Complete threat coverage

Real-time threat detection
In simple terms, detection is awareness. The awareness of every action, every process, and every event happening across your endpoints in real time. EDR does not look at events in isolation — it connects them, building a sequence that reveals the bigger picture and spot malicious behaviour before it has the chance to escalate.
- Real-time endpoint visibility
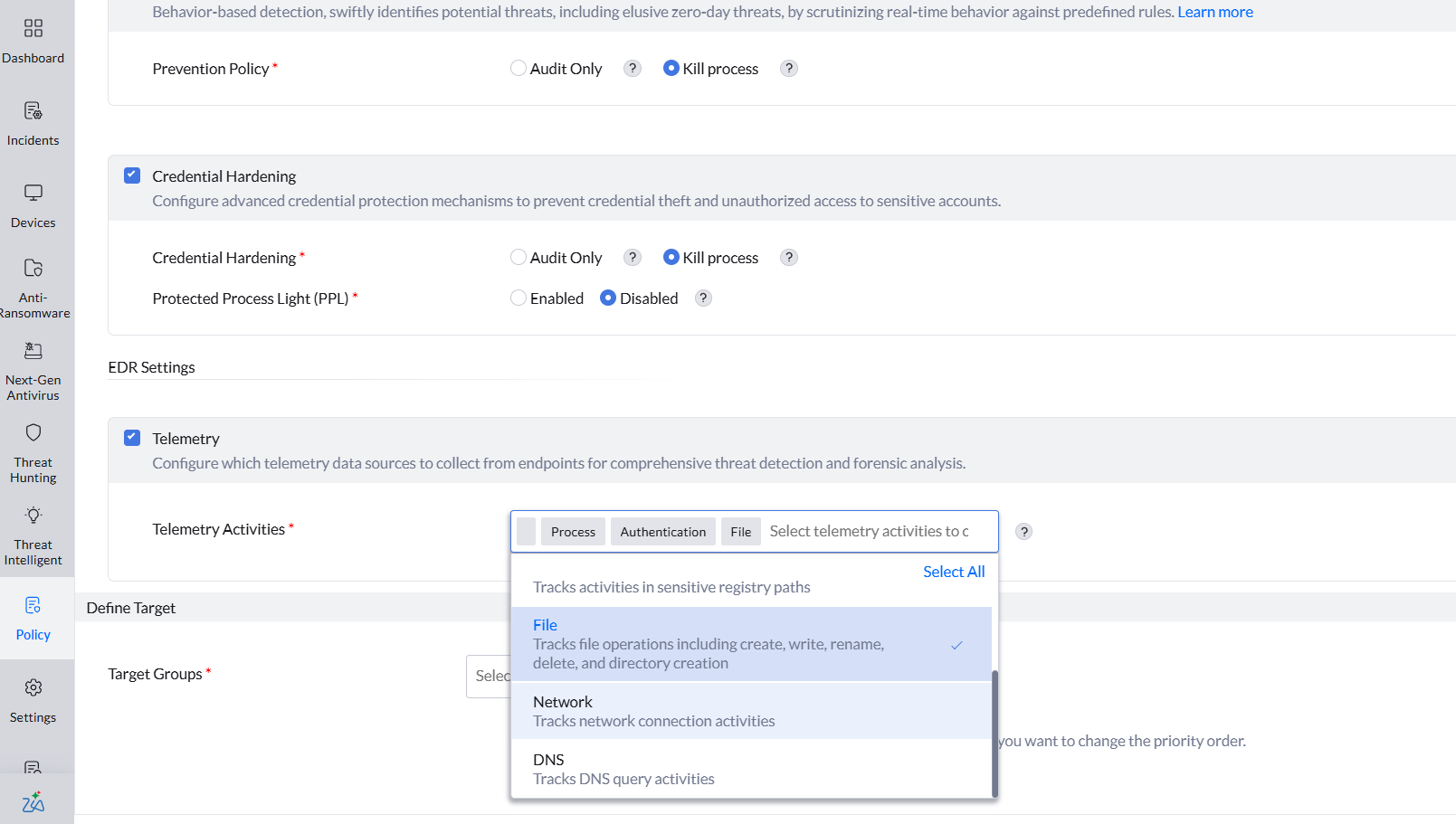
EDR monitors and records activity data across multiple dimensions of your organisation: users, endpoints, files, processes, and networks. Using behavioural analytics, Indicators of Attack (IoAs), Indicators of Compromise (IoCs), and MITRE ATT&CK framework, it continuously analyses endpoint activity to distinguish normal behaviour from suspicious activity and identify threats as they unfold.
- Searchable endpoint data
Endpoint Central EDR retains 30 days of endpoint activity, giving your security team the historical context needed to trace threats back to their origin. With Zia AI-driven incident search, you can hunt for threats in plain language. Custom IoA rules take it further, letting you define specific suspicious behaviours and trigger alerts using flexible query-based conditions.
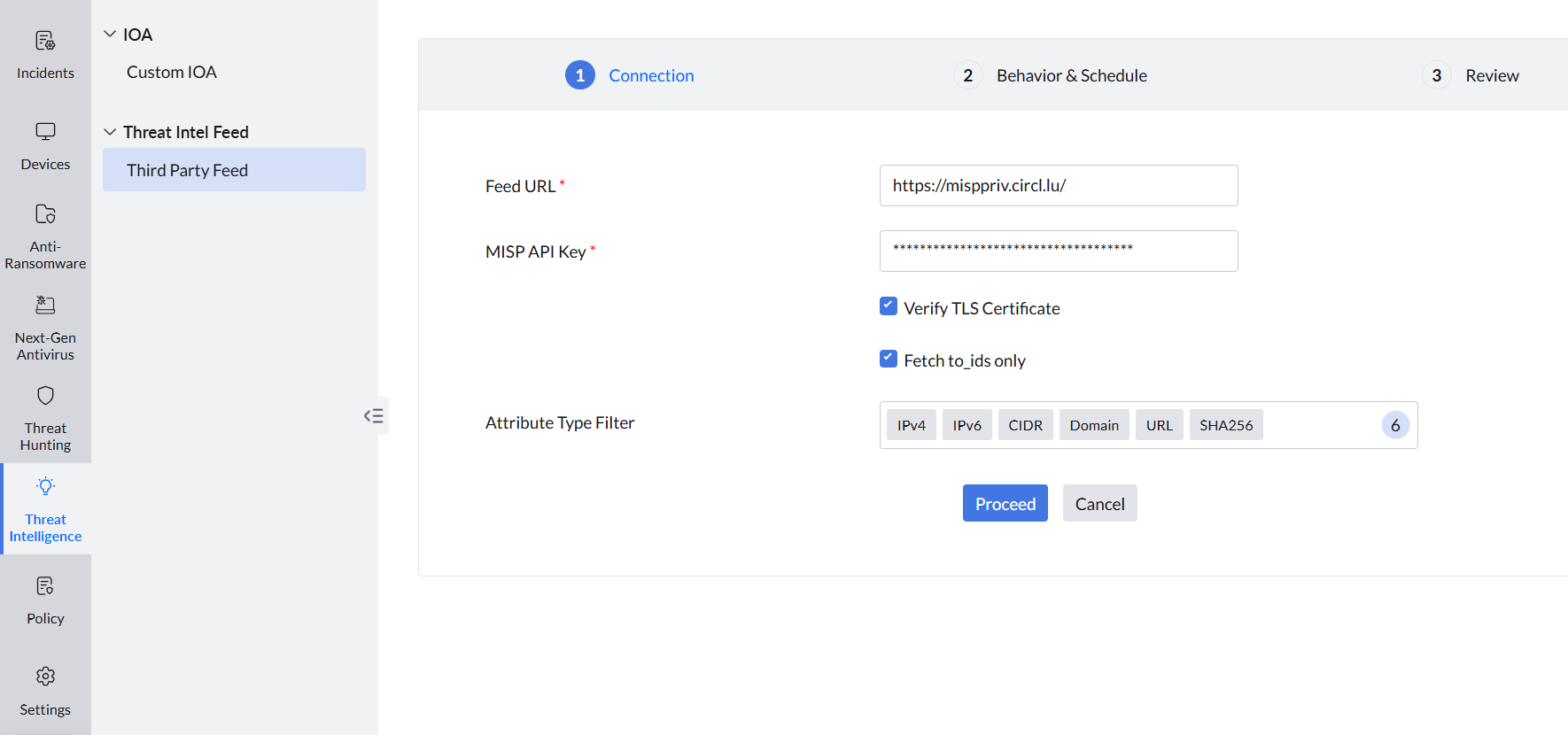
- Threat Intelligence integration
Being on top of the latest tactics, techniques, and procedures (TTPs) is critical to effectively surface threats. Endpoint Central EDR comes with a built-in Threat Intelligence database that keeps your defences updated in real-time as the threat landscape evolves. For broader coverage, it also supports third-party threat intelligence integrations that ingest external IoC feeds.
AI-powered threat investigation
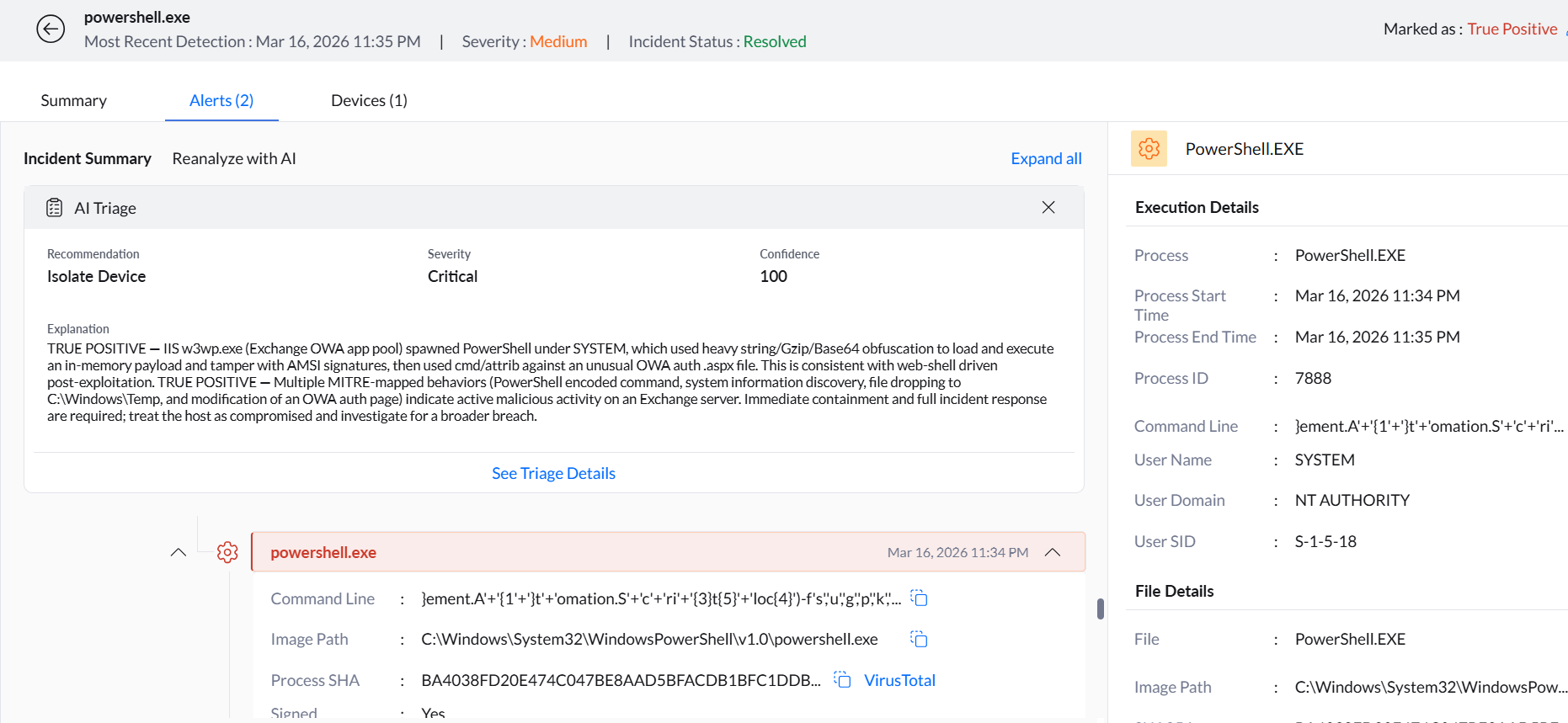
Every suspicious activity is flagged as an alert. When it's a few endpoints, sorting through alerts manually is possible albeit time-consuming. But imagine an enterprise with thousands of endpoints — the volume becomes overwhelming. It leads to alert fatigue, and alert fatigue leads to missed attacks, particularly the time-sensitive ones buried under a mountain of lower priority notifications.
The solution is a no-brainer: the age old method of prioritisation. Endpoint Central EDR employs Zia AI to triage and sort through all alerts, prioritising them based on criticality, potential risk, and time sensitivity. The most important alert that demands your attention is brought to the surface at the right moment.
Zia AI goes even further, reconstructing the complete attack timeline from the initial point of entry to the furthest point of impact. It identifies the root cause, maps the current progression, and arms your security team with everything they need to make the next right decision: severity, true positive confirmation, threat summary, and recommended remediation measures.
Containment and response
Detection tells you a threat is there. Investigation tells you what it is. Response determines what it costs you. How quickly and effectively you respond is the single factor that defines the impact a threat has on your enterprise.
- Network containment
Once infected endpoints are identified, it is critical to quarantine them before the threat spreads to the rest of the network. Endpoint Central EDR automatically isolates compromised endpoints, cutting off the attacker's ability to move laterally and containing the threat before it can cause further damage.
- Neutralise the attack
Most attacks have one thing in common: a malicious file operating silently in the background. Endpoint Central EDR completely removes malicious files from affected endpoints, neutralising the threat at its source and preventing re-execution.
- Data restoration
In the event of a ransomware attack or data extortion, the attacker may demand a ransom in exchange for your enterprise data. Endpoint Central EDR offers single-click restoration of your enterprise data, putting you back in control without giving in to the attacker's demands.
Why Endpoint Central EDR
The threats are not stopping. The question is whether your security strategy is built to handle all of them, not just most of them.
Most EDR solutions detect threats and hand you the information. Endpoint Central EDR hands you the solution. A threat traced back to an unpatched vulnerability? Endpoint Central identifies it, offers the patch, and helps you deploy it. An attack entering through an unauthorised USB device? Blocked. That is the difference between a standalone EDR tool and endpoint security enhanced by endpoint management.





"We not only gained threat intelligence on our endpoints but have also migrated away from existing MDM providers into one solution. Managing circa 10,000 endpoints has become a breeze."
Head of Information Security,
Review collected by and hosted on Gartner Peer Insights.