How to set up Secure Gateway Server in a Demilitarized Zone?
Demilitarized Zone (DMZ) secures the computers of your enterprise from data breaches and vulnerabilities by creating an additional layer of security to your in-house computers. A DMZ acts as a buffer and prevents the direct exposure of Endpoint Central's server to the internet.
How DMZ works?
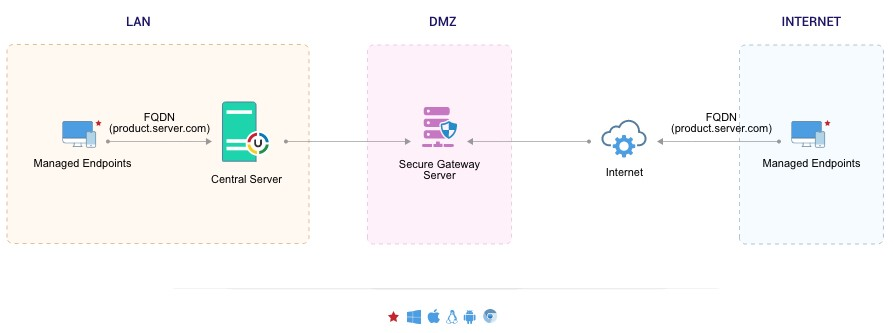
When a secure gateway server is placed in a DMZ, sandwiched between one or two firewall(s), Endpoint Central's internal network is secured from external access. DMZ provides an additional layer of security by restricting remote access to internal servers containing valuable/sensitive information. The agents of various remote offices and roaming users trying to reach Desktop Server will seamlessly parse the information without reaching the local network.
Securing communication with Secure Gateway Server.
Endpoint Centra Secure Gateway Server acts as a secure gatekeeper to the Endpoint Central Server. The configured Secure Gateway Server will be directly exposed to the internet and serves as an intermediate between the Endpoint Central's Server and computers of various branch offices or roaming users (WAN). All communications from the roaming agents will be routed through the Secure Gateway. When the agent tries to contact the Endpoint Central server, the Secure Gateway server receives all the communications and redirects it to Endpoint Central's Server.
Why deploy secure gateway server in DMZ network?
Placing a secure gateway server in a DMZ has many advantages. By configuring Endpoint Central secure gateway server, you can
- Secure your local network from vulnerabilities without exposing Endpoint Central Server directly to internet.
- Secure the communication between the computers in WAN and the Endpoint Central Server.
- Reduce the risk of attack/breach from external sources by restricting remote access to internal servers.
Know more on configuring Secure Gateway Server and how it works here.




