How to secure communication of mobile/roaming users using Secure Gateway Server?
Description
This document explains the steps involved in securing the communication of roaming users using Secure Gateway Server. Secure Gateway Server can be used when roaming agents (on the mobile devices and desktops) access the server through the internet. It prevents the exposure of the server directly to the internet by serving as an intermediate server between the product server and roaming agents.This ensures that the product server is secure from risks and threats of vulnerable attacks.
For a step by step demonstration video on how to configure secure gateway server, click here.
Note: The Secure Gateway Server cannot be installed on the same machine as the product server, but it can be installed on the machine where the agent is located.
How Secure Gateway works?
Secure Gateway Server is a component that will be exposed to the internet. The Secure Gateway Server acts as an intermediate server between the managed roaming agents and the central server. All communications from the roaming agents will be navigated through the Secure Gateway. When the agent tries to contact the central server, Secure Gateway server receives all the communications and redirects to the central server. Please note that you will have to install and setup Secure Gateway Server in a different machine and not in the machine where Endpoint Central Server/Distribution Server/Failover Server is installed.
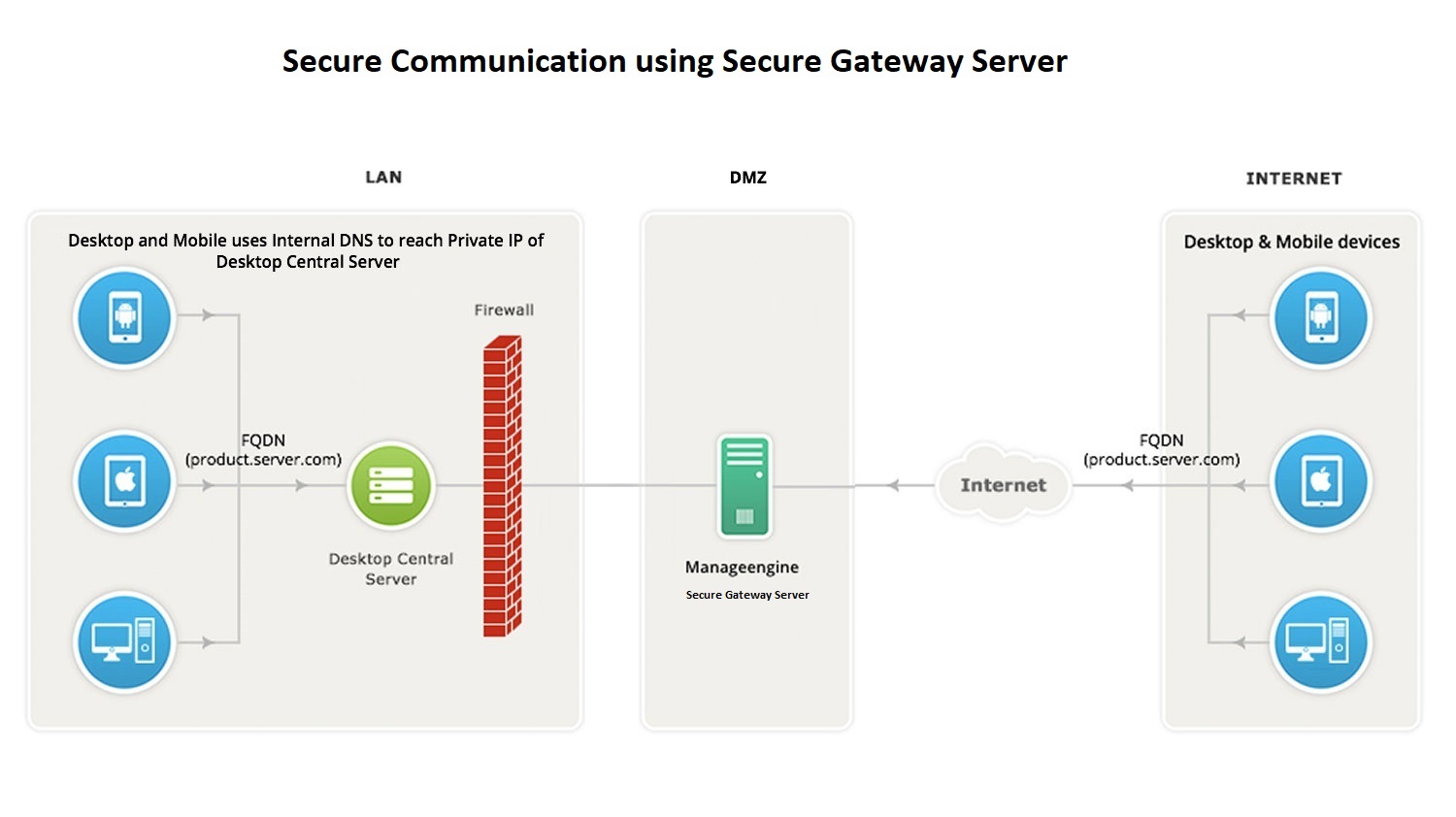
Note: Map your Secure Gateway's public IP address and product server's private IP address to a common FQDN in your respective DNS. For example, if your FQDN is "product.server.com", map this to both your Secure Gateway and central server IP address. By this mapping, the WAN agents of roaming users will access the central server via Secure Gateway (using internet) and the agents within the LAN network will directly reach central server, hence leading to quicker resolution.
Software requirements for Secure Gateway Server
You can install Secure Gateway Server on any of these Windows operating system versions:
- Windows 7
- Windows 8
- Windows 8.1
- Windows 10
- Windows 11
- Windows Server 2008
- Windows Server 2008 R2
- Windows Server 2012 R2
- Windows Server 2016
- Windows Server 2019
- Windows Server 2022
Hardware requirements for Secure Gateway Server
The hardware requirements for Secure Gateway Server include the following :
1 to 5000 computers
| Server |
Parameter |
Requirement |
| Secure Gateway Server |
Processor information |
Physical Machine: Intel Core i3 (2 core/4 thread) 2.9 Ghz 3 MB cache
Virtual Machine: 4 virtual processors 2.9 GHz 3 MB cache |
| RAM size |
4 GB |
| Hard disk space |
40 GB* |
| Network requirement |
Network card speed |
Minimum 1 GBPS Network Interface Card (NIC) |
| Bandwidth |
Minimum 1 MBPS (T1 connection) |
* May increase dynamically according to the frequency of scanning
5001 to 9000 computers
| Server |
Parameter |
Requirement |
| Secure Gateway Server |
Processor information |
Physical Machine: Intel Core i5 (4 core/8 thread) 2.3 GHz
Virtual Machine: 8 virtual processors 2.3 GHz |
| RAM size |
4 GB |
| Hard disk space |
80 GB* |
| Network requirement |
Network card speed |
Minimum 1 GBPS Network Interface Card (NIC) |
| Bandwidth |
Minimum 1 MBPS (T1 connection) |
* May increase dynamically according to the frequency of scanning
9001 to 15000 computers
| Server |
Parameter |
Requirement |
| Secure Gateway Server |
Processor information |
Physical Machine: Intel Core i7 (6 core/12 thread) 3.2 GHz
Virtual Machine: 12 virtual processors 3.2 GHz |
| RAM size |
4 GB |
| Hard disk space |
120 GB* |
| Network requirement |
Network card speed |
Minimum 1 GBPS Network Interface Card (NIC) |
| Bandwidth |
Minimum 1 MBPS (T1 connection) |
* May increase dynamically according to the frequency of scanning
15001 to 18000 computers
| Server |
Parameter |
Requirement |
| Secure Gateway Server |
Processor information |
Physical Machine: Intel Xeon E5 (8 core/16 thread) 2.6 GHz
Virtual Machine: 16 virtual processors 2.6 GHz |
| RAM size |
8 GB |
| Hard disk space |
150 GB* |
| Network requirement |
Network card speed |
Minimum 1 GBPS Network Interface Card (NIC) |
| Bandwidth |
Minimum 1 MBPS (T1 connection) |
* May increase dynamically according to the frequency of scanning
18001 to 25000 computers
| Server |
Parameter |
Requirement |
| Secure Gateway Server |
Processor information |
Physical Machine:Intel Xeon E5 (12 core/24 thread) 2.7 GHz
Virtual Machine: 24 virtual processors 2.7 GHz |
| RAM size |
8 GB |
| Hard disk space |
200 GB* |
| Network requirement |
Network card speed |
Minimum 1 GBPS Network Interface Card (NIC) |
| Bandwidth |
Minimum 1 MBPS (T1 connection) |
* May increase dynamically according to the frequency of scanning
Steps
To introduce Secure Gateway based communication to Endpoint Central, follow the steps given below:
- Modify Endpoint Central Settings
- Install and configure Secure Gateway
- Infrastructure recommendations
Modify Endpoint Central Settings
Enter Secure Gateway IP address instead of Central server IP address under Endpoint Central server details while adding remote office. This is to ensure the WAN agents and Distribution Server communicate through the Secure Gateway.
Enable secured communication(HTTPS) under DS/WAN agent to Central server communication.
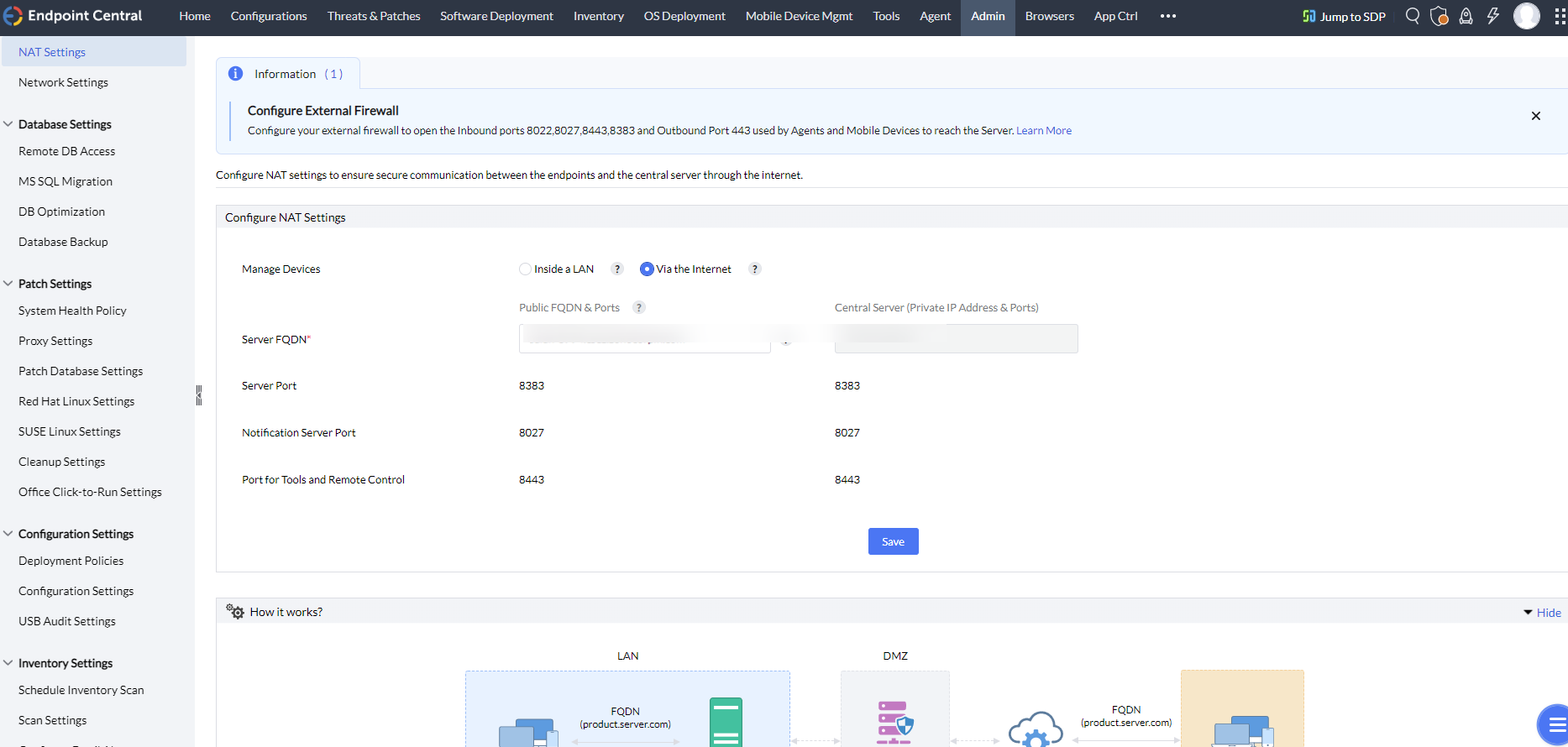
Configure NAT settings using the Secure Gateway's public FQDN/IP address.
- On the product console, click on Admin tab -> Server Settings -> NAT Settings
- Choose to Manage Devices Via the Internet
- Add the FQDN of the Secure Gateway Server against the Public FQDN under NAT settings as shown below
Install and configure Secure Gateway
- Download and install Secure Gateway on a machine in Demilitarized zone.
- Enter the following details under Setting up the Secure Gateway window, which will open after the installation process.
- DC Server Name: Specify the FQDN/DNS/IP address of the DC server. Or specify virtual IP address if Failover server is used.
- DC Https Port: Specify the port number that the mobile devices use to contact the DC server (eg: 8383). It is recommended to use the same port 8383(HTTPS) for Central Server in secured mode.
- DC Notification Server port: 8027 (to perform on-demand operations), this will be pre-filled automatically
- Web Socket Port : 8443(HTTPS), this will be pre-filled automatically.
- Username & Password: Enter Endpoint Central user's credentials with administrative privilege.
Infrastructure recommendations
Ensure that you follow the steps given below
Secure Gateway's public IP address with the port 8383(https) should be provided to the Central server for accessibility verification.
Using a public IP address is recommended for configuring non-AD machines.
Configure Secure Gateway in such a way, that it should be reachable via public IP/FQDN address configured in NAT settings. You can also configure the Edge Device/Router in such a way that all the request that are sent to the Public IP/FQDN address gets redirected to the Endpoint Central Secure Gateway.
It is mandatory to use HTTPS communication
You will have to ensure that the following port is open on the firewall for the WAN agents to communicate the Endpoint Central Secure Gateway.
| Port |
Type |
Purpose |
Connection |
| 8383 |
HTTPS |
For communication between the WAN agent/Distribution Server and the Central server using Secure Gateway. |
Inbound to Server |
| 8027 |
TCP |
To perform on-demand operations |
Inbound to Server |
| 8443 |
HTTPS |
Web socket port used for remote control, chat, system manager etc. |
Inbound to Server |
You have now secured communication between Central server, WAN agents and roaming users.
Check this video for a step by step demonstration on how to configure the secure gateway server.