How to analyze Linux login failures
Last updated on:User authentication is an important part of network security and auditing of user's login attempts is essential to identify suspicious user behaviors.
Login failures occur:
- When the user provides incorrect credentials
- When the user doesn't have permission to log in to a specific resource.
Login failure events occurring when a user attempts to connect remotely to a system using SSH or runs su command as a different user needs to be monitored as they are critical and could indicate an intrusion attempt.
This article elaborates the methods to view the SSH login failures.
Steps to view SSH login failures
A pluggable authentication module (PAM) logs these type of authentication events and helps to identify malicious and unusual logins.
Here's an example of a failed logon attempt.
pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=10.0.2.2
Failed password for invalid user robert from 10.0.2.2 port 4791 ssh2
pam_unix(sshd:auth): check pass; user unknown
PAM service(sshd) ignoring max retries; 6 > 3
For effective troubleshooting, it is necessary to identify all such critical logins quickly and take steps accordingly.
Below are the steps to find all SSH failed login attempts.
- The basic command to list all SSH failed login attempts is # grep "Failed password" /var/log/auth.log. The same can be achieved by executing the cat command # cat /var/log/auth.log | grep "Failed password".
- In order to display extra information about the failed SSH logins, use the following command. # egrep "Failed|Failure" /var/log/auth.log
- To display the list of all IP addresses that attempted a login and failed to log in to the SSH server, use the following command. # grep "Failed password" /var/log/auth.log | awk ‘{print $11}’ | uniq -c | sort -nr
Even though analyzing the above event might look easy, manually performing all the operation is a time-consuming and tedious process. A log management solution can help you to analyze the failed SSH login attempts easily.
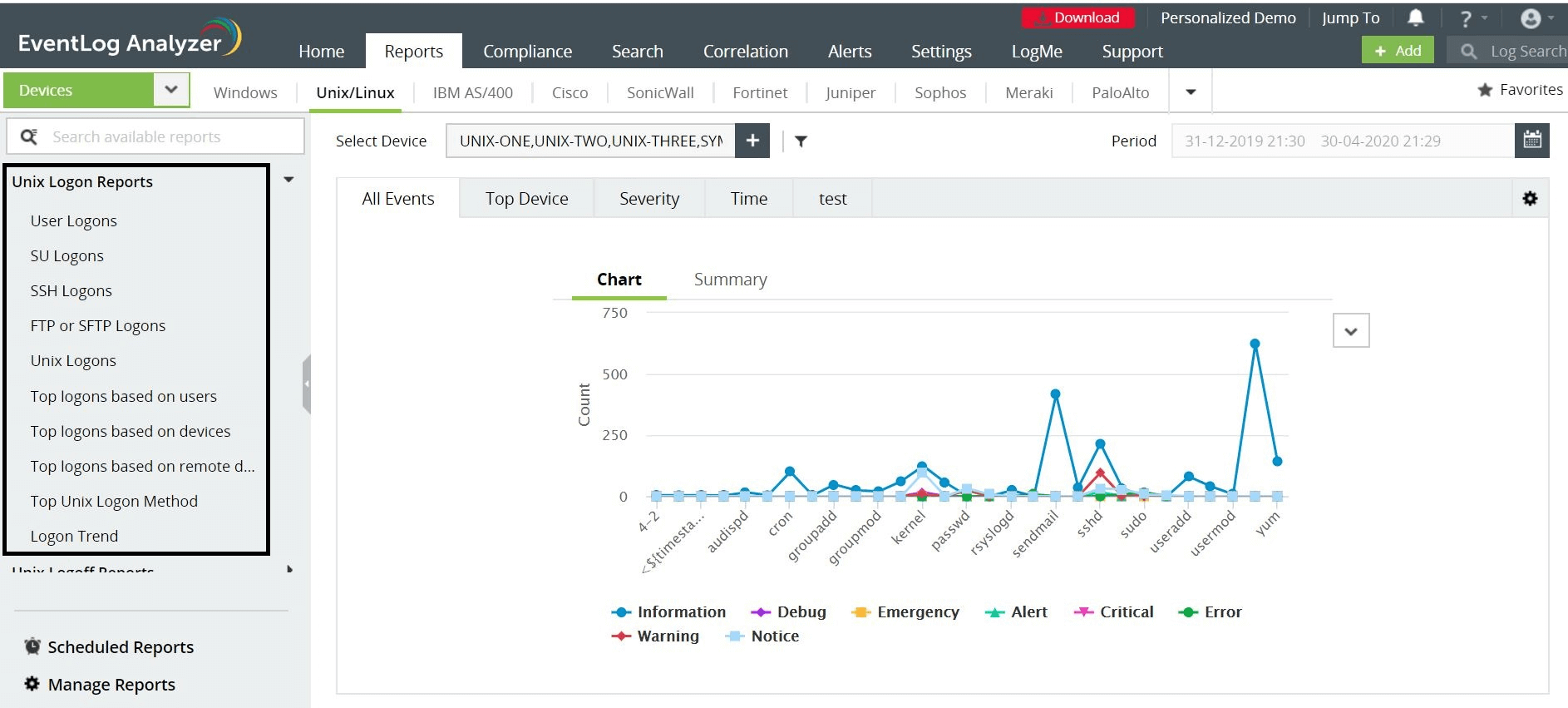
Getting insights on SSH login failures
EventLog Analyzer, a comprehensive log management solution, collects Syslogs from Linux devices, analyzes them automatically, and provides you with necessary insights such as failed SSH login attempts, SU logons, user logon trends, and more in the form of intuitive reports. Check out more about EventLog Analyzer's Linux log monitoring capability here.