What is syslog monitoring?
Last updated on:In this page
- Syslog monitoring: An overview
- Why is it challenging to monitor syslog?
- Why is syslog monitoring critical?
- What is a syslog monitoring tool?
- Syslog monitoring: Architecture
- Functions of syslog monitoring
- How to choose a syslog monitoring tool
- Top syslog monitoring tools: A comparison
- Why choose EventLog Analyzer for syslog monitoring?
Syslog monitoring: An overview
Syslog monitoring is the centralized process of aggregating and analyzing logs that contain critical, time-stamped information about syslog devices, servers, and applications. It helps determine critical security information about the syslog device, such as the device status, operation status, system error, and device telemetry—all crucial for troubleshooting and identifying security threats.
The syslog monitoring process involves the collection and storage of syslog data on a central server for further log parsing and indexing to convert the raw logs into comprehensible reports. These reports serve as audit records of the network's IT infrastructure and aid in identifying suspicious activity like configuration changes, unauthorized access, and network bypass.
Why is it challenging to monitor syslog?
While critical, effective syslog monitoring faces significant technical and operational hurdles. Here are some factors to consider while implementing a syslog monitoring tool.
- Inventory management can be difficult: Maintaining an accurate, real-time inventory of every machine and application generating syslog is challenging, especially in dynamic, cloud-based environments. While configuring a new device, it is critical to ensure the device is configured for logging in the monitoring system as well. Otherwise, the newly added device might exist on the network as an unmonitored resource, generating unmonitored dark data and creating a security gap.
Tools with automatic device discovery and user-friendly configuration set up are crucial to ensure syslog coverage across the network.
- Syslog device vulnerabilities can be overlooked: Vulnerabilities in the devices sending the logs might impact the efficiency of syslog monitoring. If a monitoring solution doesn't adequately track the device telemetry, vulnerable syslog sources, such as outdated firmware or a misconfigured network device, can be overlooked. This makes the entire network susceptible to compromise.
It is crucial to ensure that the syslog monitoring tool is capable of tracking the device's health and issuing periodic firmware updates.
- Too many devices bring in too much noise: As organizations scale up, their networks expand along with the volume and velocity of their syslog data. Analyzing such huge volumes of data can be overwhelming for analysts and cause alert fatigue. These analysts might also fail to address critical events while dealing with low priority alerts, leading to negligence and human error.
Alert triaging and prioritization is a critical factor to consider in modern syslog monitoring tools.
- Syslog formats can be incompatible with monitoring tools: While the syslog protocol provides a standard header, the actual content is often unstructured and inconsistent. Different vendors such as Cisco, Palo Alto, and Microsoft use their proprietary formats to create bottlenecks while parsing and formatting syslog.
Identifying vendor-agnostic syslog monitoring tools that have a custom log parser as well as support for various syslog formats is highly critical and nonnegotiable.
Why is syslog monitoring critical?
Syslog monitoring plays a significant role in determining the operational efficiency of syslog devices and eliminating potential errors that hinder the performance of the devices. In a security perspective, syslog monitoring is an essential component of network security that reinforces the cybersecurity posture of the network. Some crucial aspects of syslog monitoring when it comes to network security are given below:
Comprehensive visibility on all syslog sources
Syslog monitoring tools provide a single, unified view across the entire infrastructure of syslog devices, including firewalls, routers, servers, and applications. This centralization eliminates blind spots, streamlines reporting, and provides complete visibility on all events indicative of a security threat. This allows analysts to troubleshoot a breach as a single incident rather than investigating isolated events one at a time.
Ensure network and device security
Logs generated by network devices like firewalls and intrusion detection systems (IDS) are the first indicators of perimeter breaches. Syslog monitoring immediately flags such critical events at their early stages before they escalate into advanced breaches. Some of the critical Indicators of Attack (IoAs) that can be identified using syslog monitoring are:
- Multiple failed logons
- MFA bypass
- Unauthorized access via restricted ports
- Network security misconfigurations
- Unusual traffic trends
Once identified, these can be immediately addressed through integrated incident response workflows, allowing security teams to contain the threat and isolate the compromised systems.
Proactive threat detection and hunting
Syslog monitoring tools enable investigation of a security event by generating alerts and detailed reports on the security breaches. With inbuilt detection rules and alerting engines, these tools allow analysts to detect potential signature threats and attacks. These tools also help perform root cause analysis and analyze the attack kill chain to hunt down the Indicators of Compromise (IoCs) and take remedial actions.
Compliance and auditing
Although organizations stay vigilant to compliance breaches with active syslog monitoring, syslog monitoring tools enable them to demonstrate their adherence through detailed audit trails and reports. Since many regulatory frameworks such as HIPAA, PCI DSS, and GDPR mandate the retention of log data of critical security events, having a syslog monitoring tool in place eases log auditing, forensic analysis, and compliance management.
What is a syslog monitoring tool?
A syslog monitoring tool is typically a software application that collects and analyzes logs from syslog devices to provide granular details on security events associated with syslog devices. Some monitoring tools also serve as syslog servers that store time-stamped logs from various syslog devices to provide comprehensive dashboards and detailed reports alongside threat alerting capabilities.
One such tool is the ManageEngine EventLog Analyzer, a SIEM solution built with syslog server capabilities. EventLog Analyzer comes with syslog monitoring functionalities that secure your network against security breaches and ensure compliance across various regulatory mandates.
Syslog monitoring: Architecture
Syslog monitoring involves a client-server architecture wherein the devices that transmit logs act as clients and the syslog monitoring application works as the server. Here is a detailed breakdown of the log collection and analysis process that follows:
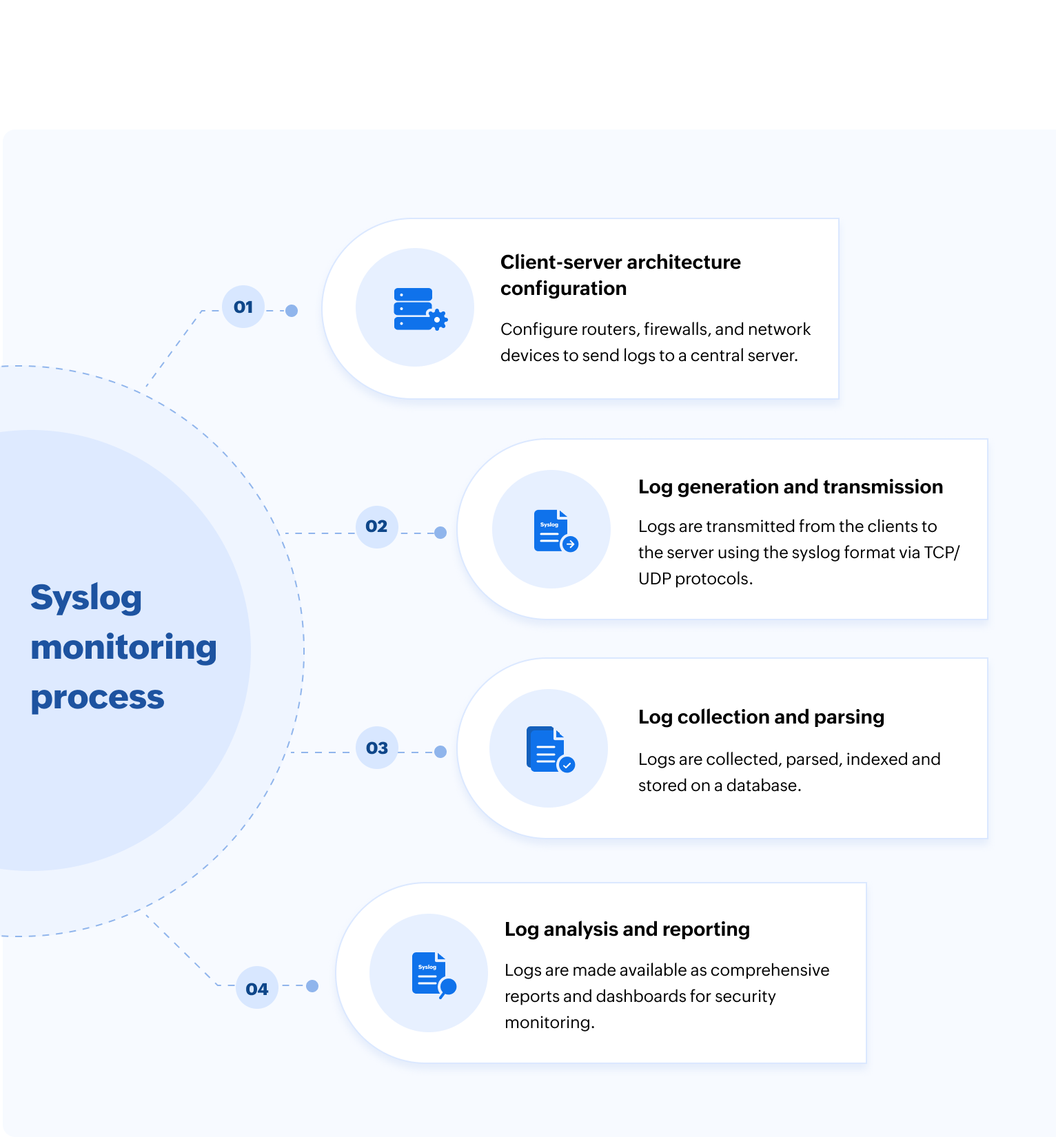
Client-server architecture configuration
Network devices such as routers, firewalls, and servers (clients) are the log generators that feed data to the central collector (server) for syslog monitoring. The syslog monitoring tool acts as the central repository for storing and analyzing the log data. The process begins with the configuration of clients for logging on the server and configuring the server to collect logs from those client devices.
Log generation and transmission
The logs are generated and sent from the clients to the server as messages in the Syslog protocol format. This format typically includes the header with a timestamp, hostname, IP, and Priority value which indicates the message source and severity. The messages are sent over TCP/UDP on specific ports assigned for syslogs.
Log collection and parsing
The syslog monitoring tool or the collector is configured to listen for incoming logs through specific listener ports. Listening for logs usually happens in real time, facilitating real-time monitoring. But there are also some cases of batch monitoring where the logs are collected during specific periods and analyzed in batches. The central server validates the key fields from the incoming log message and parses useful information such as the timestamp, severity, facility, hostname, and the actual message content. The logs are then indexed and stored on a database made available for monitoring and analysis.
Log analysis and reporting
The parsed and indexed logs are leveraged to create dashboards and reports that help security analysts monitor syslog activities. As the logs are stored in a structured database, they can be easily searched and filtered despite the volume of data. Most monitoring tools also come with correlation rules or alerting conditions that enable security analysts get notified on specific log patterns or breaches in real time. It also helps analysts troubleshoot complex events by linking related log entries to visualize a complete event chain, crucial for threat detection and incident response.
Functions of syslog monitoring
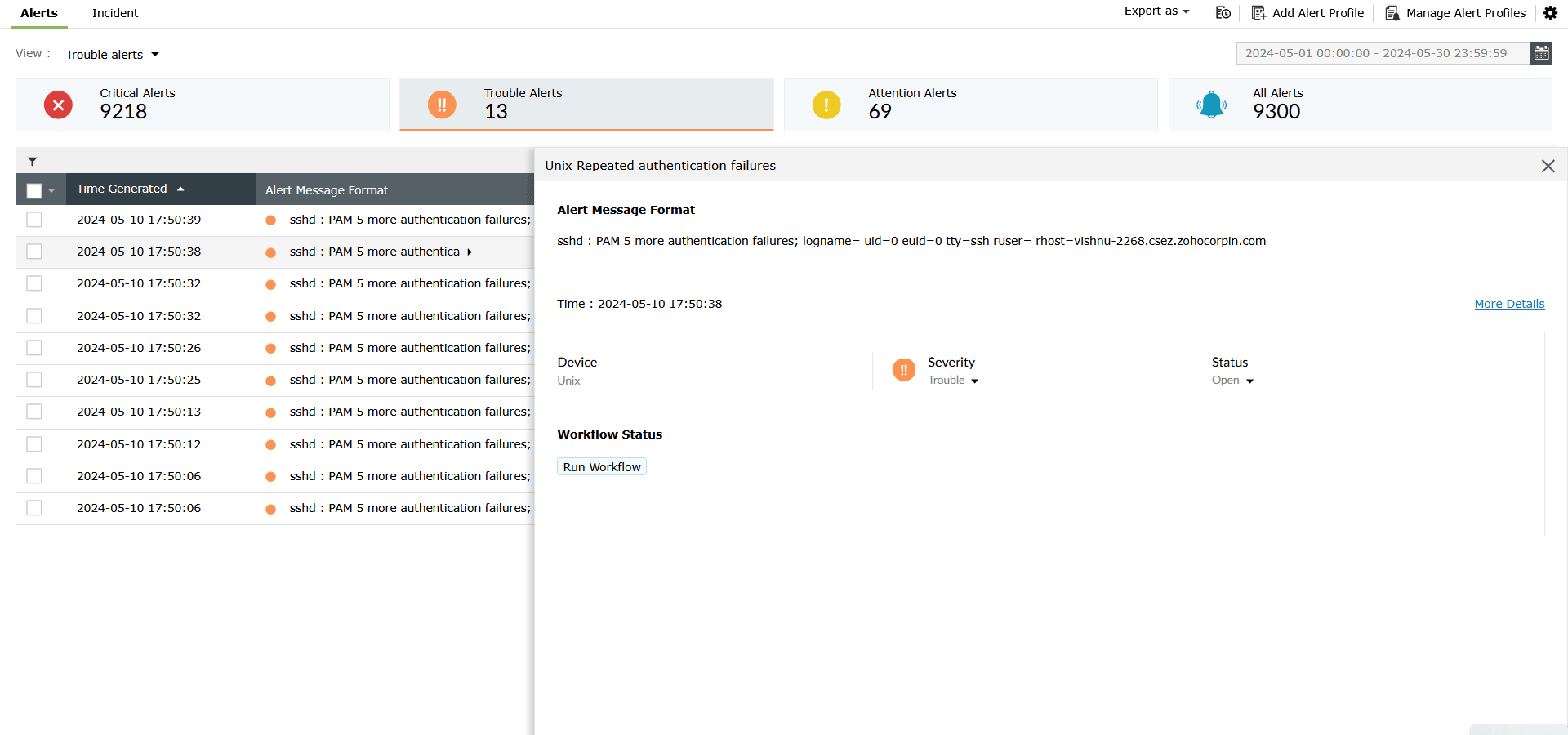
Proactive alerting
Syslog tools enable real-time monitoring of incoming log data against predefined or dynamic thresholds. When critical events such as multiple failed logons, unauthorized file access, or MFA bypass occur beyond the defined frequency, the syslog monitoring tool flags these events as suspicious. It then notifies the security analysts via email, SMS, or integrated ticketing systems to enable rapid incident response.
Figure 2 displays EventLog Analyzer's alerting module where you can view and filter syslog alerts based on their severity. You can further view and analyze the individual alerts, assign technicians, and run incident response workflows all from a single window.
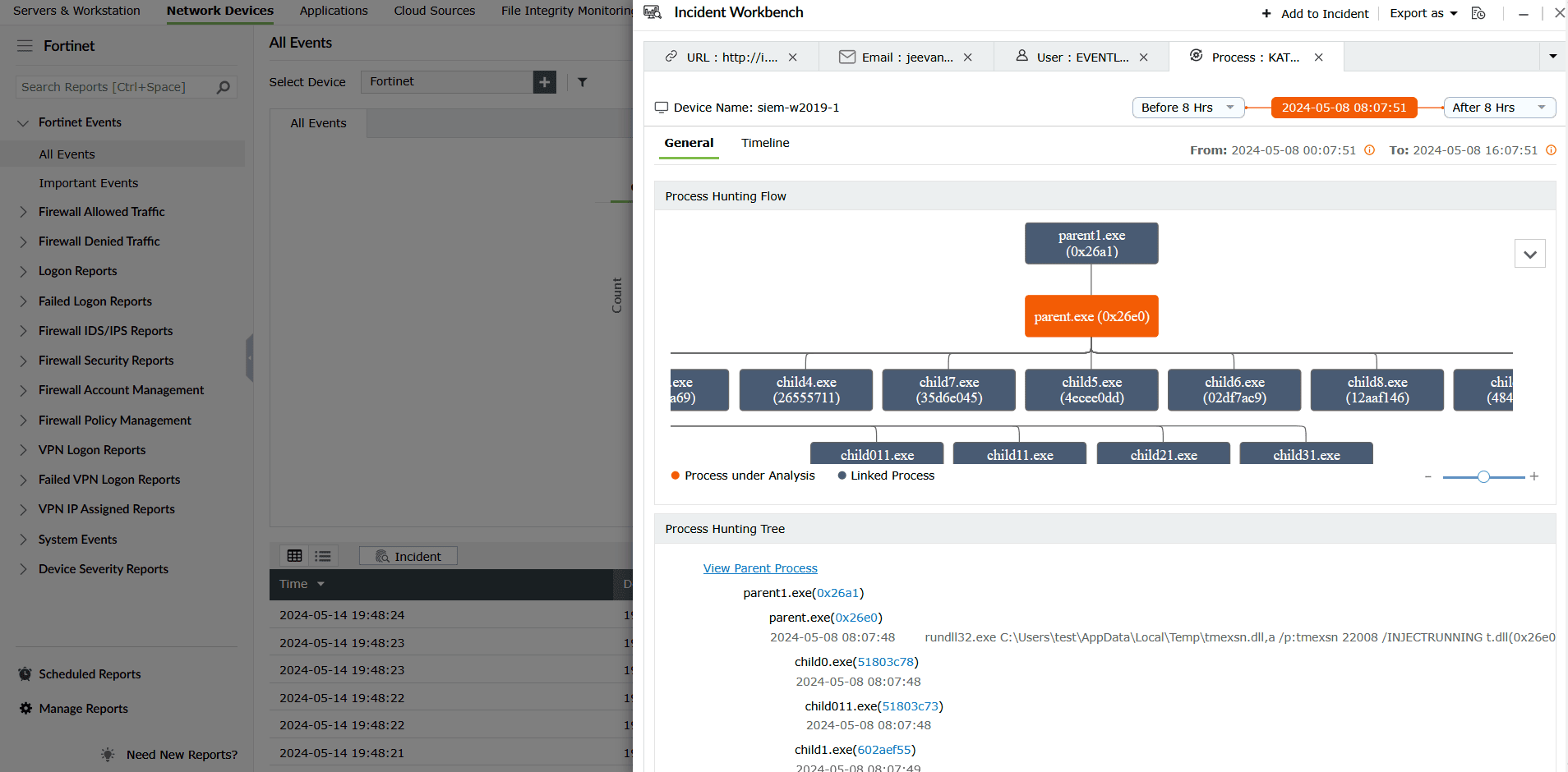
Rule-based threat detection and investigation
Syslog monitoring tools leverage predefined correlation rules to identify known malicious patterns or abnormal sequences of events across different logs. Once a pattern is identified, the individual events are drilled down to their initial point of breach using process hunting trees to uncover IoCs and IoAs. Some monitoring tools further enrich these indicators with advanced threat intelligence to detect sophisticated APTs and cyberattacks like ransomware.
Figure 3 displays EventLog Analyzer's threat detection and investigation module which enables you map suspicious IoCs with advanced threat intelligence data. You can also identify the root cause of an attack using the process hunting tree and process timelines to contain an attack before a potential compromise.
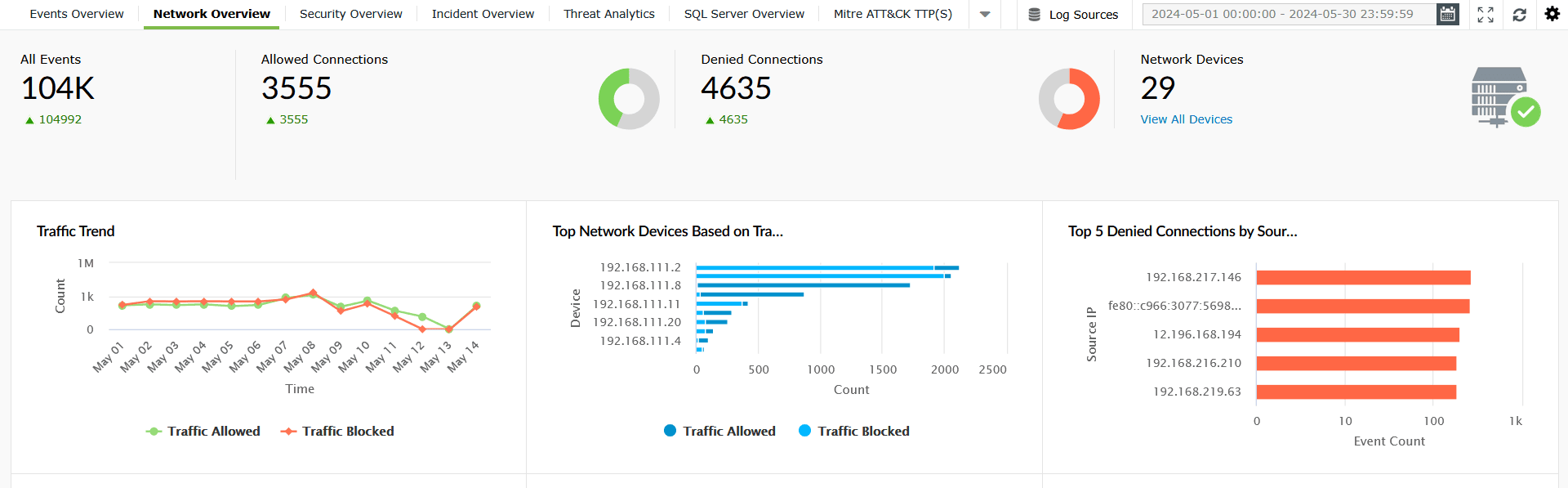
Comprehensive dashboards and reports
Syslog monitoring tools offer intuitive dashboards and reports that provide centralized, visual summaries of syslog trends and traffic using charts and graphs. They transform billions of raw log entries into comprehensible metrics that show allowed connections, denied connections, traffic trends, and more, enabling security teams to gain 360-degree visibility across syslog devices.
Figure 4 displays EventLog Analyzer's dashboard that provides a complete overview of all syslog-critical data as intuitive widgets and graphs.
Reporting and compliance
Syslog monitoring tools generate pre-built reports that offer granular details on all syslog activities. These reports can be scheduled or obtained in real-time to detect suspicious activities and data breaches. They can also be documented and retained for demonstrating critical controls mandated by regulatory bodies. This feature is essential for compliance management, ensuring adherence to mandates like PCI DSS, HIPAA, or GDPR through tamper-proof log storage and archiving.
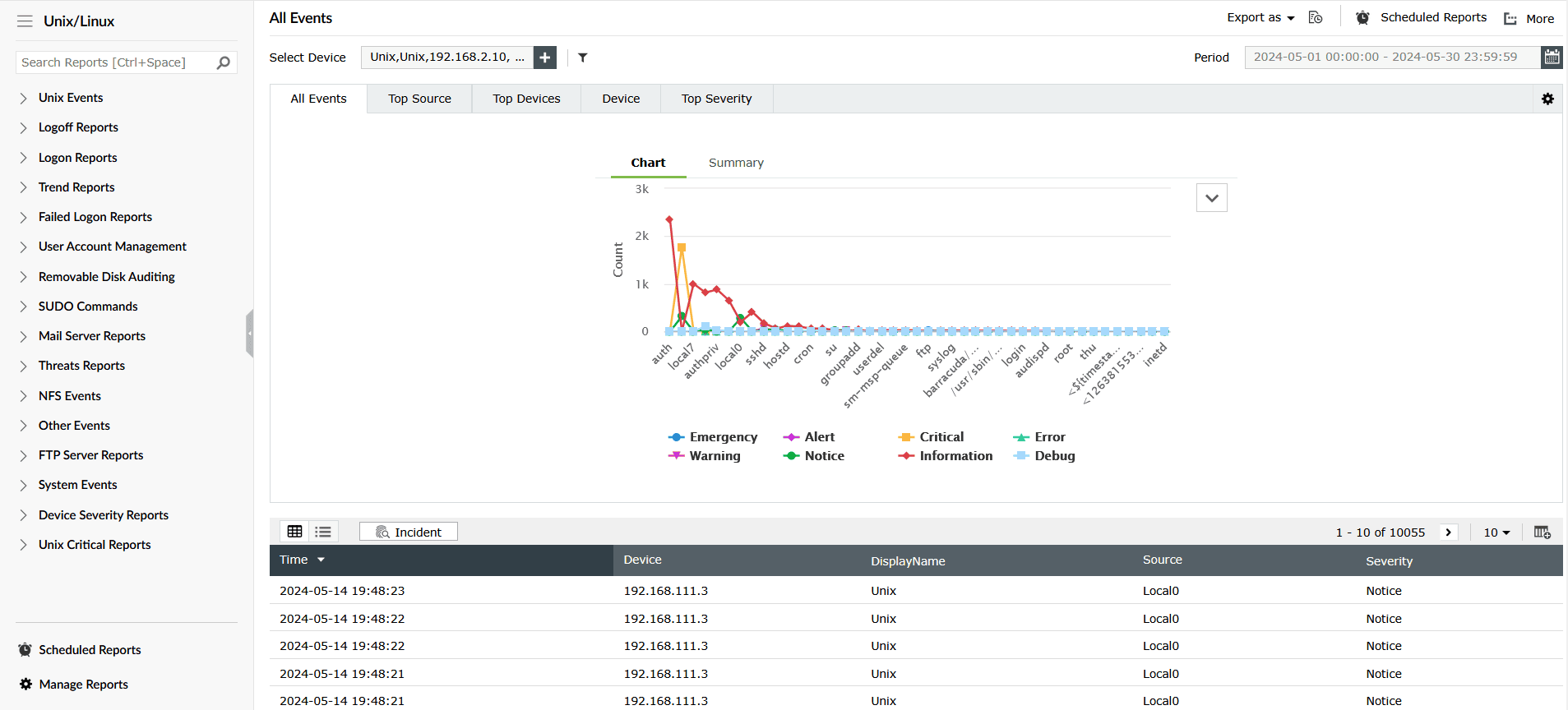
Figure 5 displays EventLog Analyzer's Unix log report that provides details on all types of Unix events. The reports also provide granular data including the IP address, source, timestamps, and the syslog level of the event.
EventLog Analyzer is not just an ordinary monitoring tool but a complete package of advanced syslog monitoring, threat hunting, and incident response features.
How to choose a syslog monitoring tool
Here are some key parameters that need to be considered when choosing a syslog monitoring tool.
Scalability
This parameter determines the capacity and long-term reliability of the monitoring system. The tool must be resource-efficient and capable of handling huge volumes of log data without impacting performance. It should be capable of managing unpredictable spikes in log velocity that may occur during peak hours or in the event of a security incident.
Security and access control
Syslog data often contains highly sensitive information, PII, and security event details. Without granular access control and secure transmission, the risk of internal data breaches and regulatory penalties are very high. It is mandatory that the syslog tool enforces role-based access controls to ensure the safety and integrity of the log data.
Compliance and audit trails
It is highly essential to choose a monitoring tool that inherently supports compliance management, access governance, and risk mitigation requirements. While storage is an important aspect, mandatory features like pre-built reporting, log retention, and tamper-proof audit trails not only help comply with security mandates but also reinforce the credibility and integrity of the business.
Data retention and archival
Storing and managing syslog data in a secured location and reproducing the data on demand is critical for compliance. Because this is a highly resource-intensive process, the syslog monitoring tool should possess secured archival features that enable log encryption, storage, and instantaneous log retrieval whenever required.
High availability and disaster recovery
Selecting a tool with robust high availability and disaster recovery capabilities ensures the continuous flow of log collection and processing, even if servers or collectors crash. The monitoring tool should include automatic backup features that provide redundancy when there is a major network disaster or failure of syslog servers. The tool should also be capable of fast recovery and remediation after a critical outage.
Ease of use
In spite of efficiency and performance, monitoring tools with complex features and highly sophisticated capabilities that are difficult to use impact productivity. A tool with an intuitive user interface and logical workflow minimizes the time spent learning and operating the software. Thus, it is important to consider the usability and ease of navigation before choosing a tool.
Deployment flexibility
Choosing a tool with the necessary deployment flexibility is essential to cope with the architectural complexity of the network. The syslog monitoring tool should be adaptable to the deployed environment, capable of operating in cloud, on-premises, or hybrid infrastructure. This flexibility ensures that the logging solution aligns with the security policies and requirements of the network, allowing seamless integration and collaboration with advanced monitoring tools like UEBA and SOAR.
Top syslog monitoring tools: A comparison
Here is a detailed comparison of some of the top syslog monitoring software in the market.
| Criteria | EventLog Analyzer | Kiwi Syslog Server | Graylog | Splunk |
|---|---|---|---|---|
| Architecture | Distributed | Single Windows server instance | Distributed | Distributed |
| Deployment | On-premises or managed cloud | Windows server installation | Self-hosted Linux or hybrid | Hybrid |
| Usability | Easy-to-use web console | Intuitive Windows desktop app | Intuitive web interface | Complex |
| Access control | Strong granular RBAC | Basic Windows user control | Robust RBAC | Granular RBAC |
| Reporting | Pre-built and enriched reports and dashboards | Basic reports with view and filter options | Customized dashboards | Report generation using search language |
| Alerting | Real-time correlation and alerting via SMS and email notifications | Rule-based notifications | Real-time alerts and notifications | ML-driven anomaly detection and alerting |
| Compliance | Built-in audit reports with archival and retention features | Basic log archival assistance | Compliance packs available | Compliance support available |
| Availability | High availability via distributed architecture | Low availability | High availability and component clustering | Very high availability and redundant component clustering |
| Scalability | Highly scalable via distributed components | Limited to a single server | Highly scalable using clustering | Very high scalability using horizontal indexing clusters |
Why choose EventLog Analyzer for syslog monitoring?
ManageEngine EventLog Analyzer is a comprehensive SIEM tool that goes beyond traditional syslog monitoring software.
It acts as a centralized syslog server, collecting and storing syslogs from a wide range of network devices, servers, and applications.
Learn moreIt monitors syslog activities in real-time and generates audit trails for effective threat detection and compliance assurance.
Learn moreWhat's next?
Streamline syslog management with EventLog Analyzer—the syslog server built for monitoring, alerting, and compliance auditing.











