Cisco log analyzer
As a network security administrator, monitoring and analyzing your Cisco firewall logs in real time is of utmost importance. For a secure network, you need to:
- Detect various network attacks, and pinpoint the source and type of attack (Cisco real time log viewer).
- Keep track of unauthorized login attempts on your Cisco firewall.
- Get details on active VPN user sessions and historic usage metrics.
- Examine the usage trend for Cisco firewall rules.
- Closely monitor the incoming and outgoing traffic to spot bandwidth inefficiencies.
- Discover traffic trends and efficiently manage network capacity.
- Track web applications and internet sites accessed by end users.
However, doing these tasks manually by exporting logs is extremely cumbersome and hence the need for a Cisco syslog analyzer tool.
Cisco log analysis for network security administrators.
Firewall Analyzer can analyze, report, and archive logs received from Cisco firewalls. Once the Cisco firewall is configured to direct log streams to the Firewall Analyzer server, Firewall Analyzer starts to generate in-depth Cisco log reports (Log Analyzer Cisco).
Cisco security log reports.
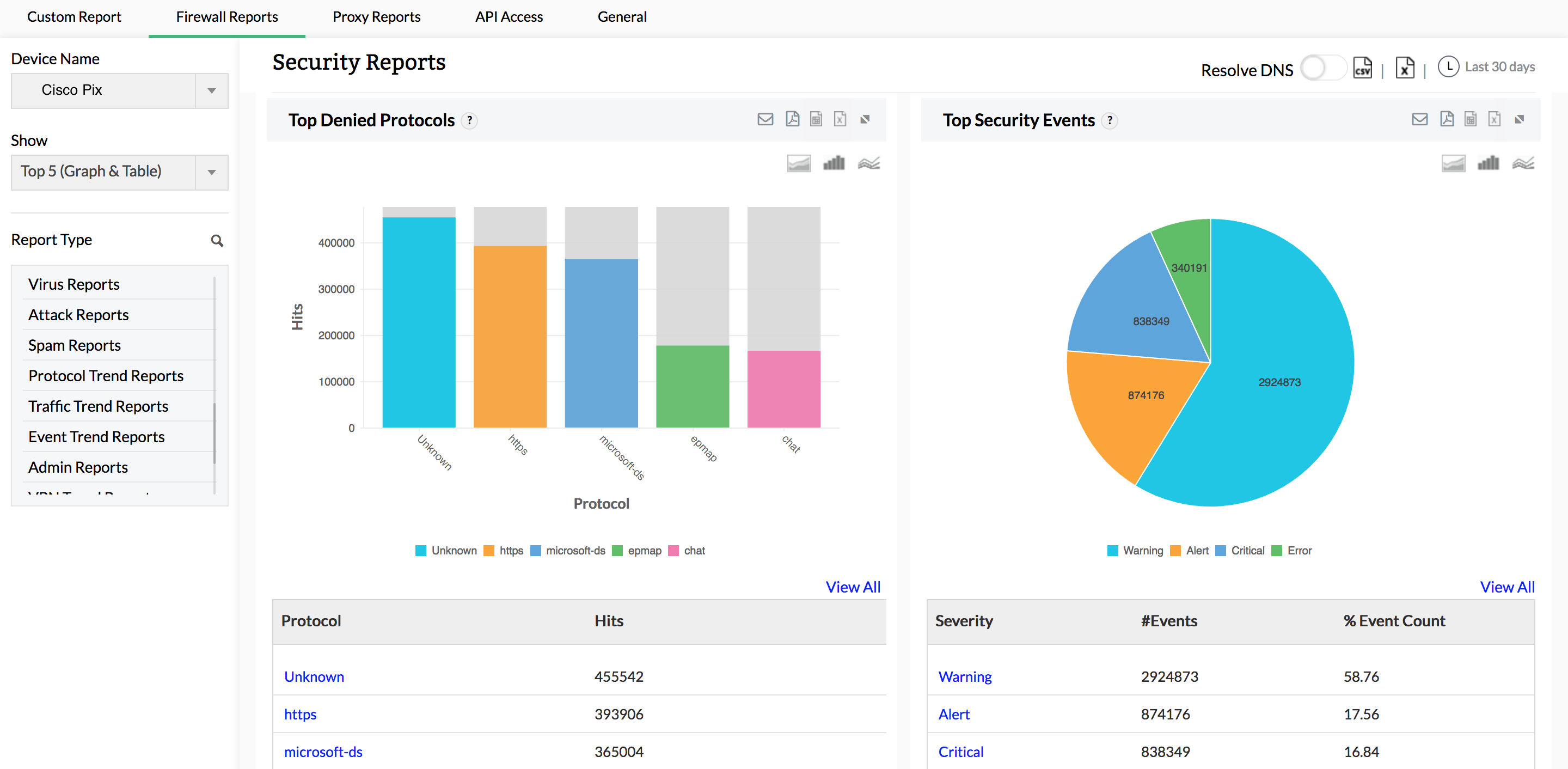
This Cisco firewall syslog analyzer generates reports on possible security threats and provides in-depth information on virus attacks in your network. Monitor failed logins, denied hosts, denied protocols, spam generators, spam receivers, and rules allowing spam. View comprehensive details on raw logs related to viruses to help pinpoint the origin of any specific attack.
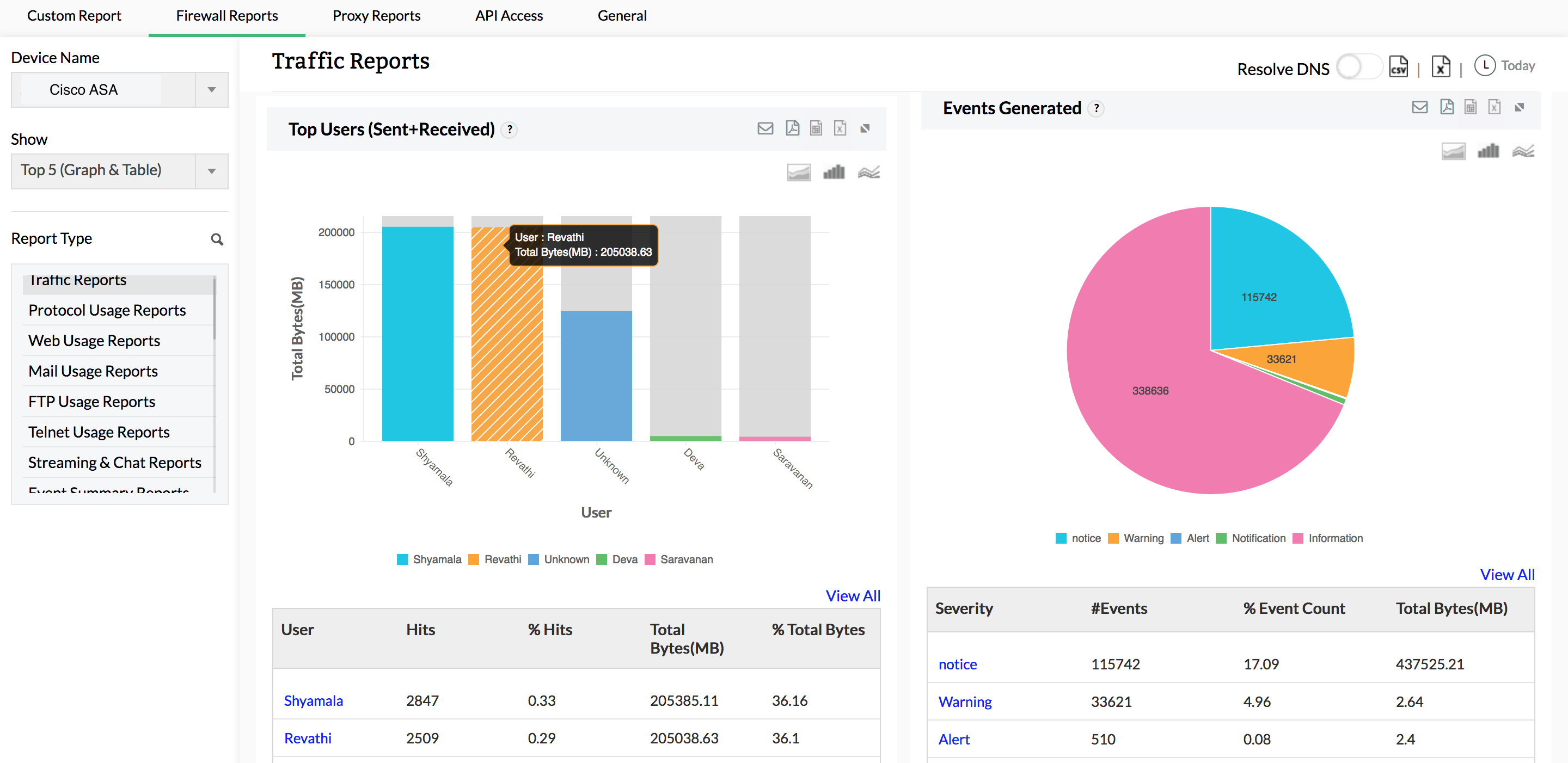
Cisco traffic log reports
Firewall Analyzer provides a unique way to analyze the traffic in your network. This Cisco log viewer measures network traffic by analyzing logs, and churns out different traffic reports for web usage, mail usage, FTP usage, Telnet usage, intranet usage, internet usage, URLs visited, inbound traffic, and outbound traffic. As a security administrator, you can visualize behavior patterns for network traffic from these reports, and optimize bandwidth accordingly.
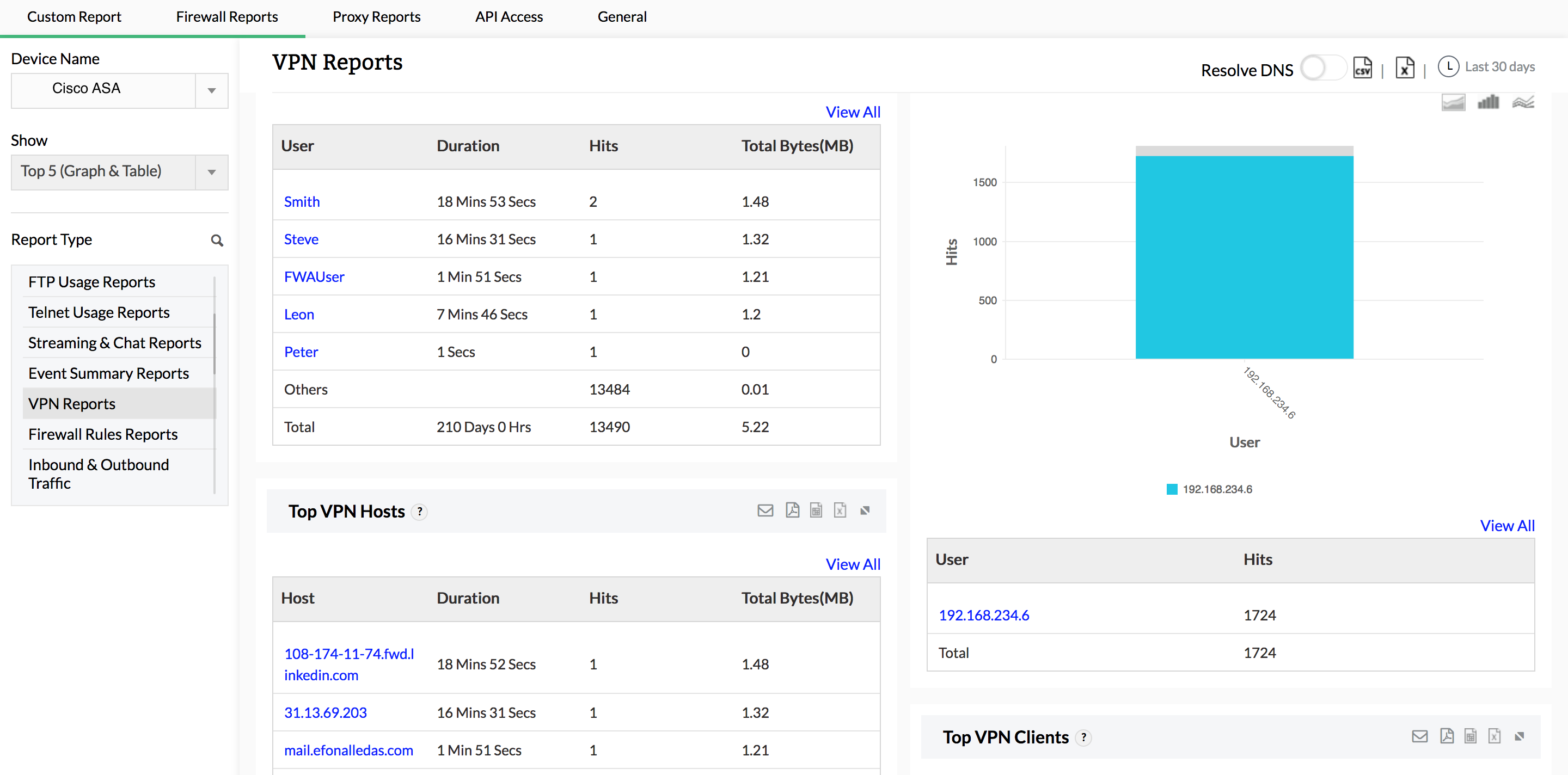
Cisco VPN log reports.
Get complete visibility on VPN hosts and protocols, as well as bandwidth used by VPN users during peak and off-peak hours. These reports provide information on the active users connected to your VPN, along with all failed VPN login attempts. Information on failed VPN logins is useful for identifying unauthorized login attempts.
Cisco syslog-based alerts.
Apart from exhaustive firewall reports on network security, Firewall Analyzer offers a comprehensive alarm management module. Alarms are generated for anomalous security and bandwidth events. Any alarm that is generated is recorded in Firewall Analyzer, and these alarms can be sent to stakeholders in real time via email and SMS. Alarms can also trigger scripts to mitigate security events the very moment an attack is detected.