Monitor and Analyze VPN reports
With organizations embracing dynamic work culture stakeholders now access the company intranet from the comforts of their home or from public networks or subsidiary sites through VPNs. Network administrators now need to monitor the activities being performed over the VPN and report on VPN. From the compliance and auditing perspective, you would like to see who connects, when, and what are the activities being performed. There is also a necessity for regular VPN audit reports.
Firewall Analyzer will be very handy for the above such requirements since you will be able to obtain Security Reports like "Denied Attempts", "Compromising Attempts", "Attacks", and "Port Scans", as well as auditing reports like "Top VPN Users", "Top failed vpn logins" etc.
The VPN reporting capability of Firewall Analyzer supports both Remote Host VPNs (PPTP,L2TP, and IPSEC) and Site-to-Site VPNs from vendors like Cisco, SonicWALL, WatchGuard, NetScreen, and others.
VPN Reports
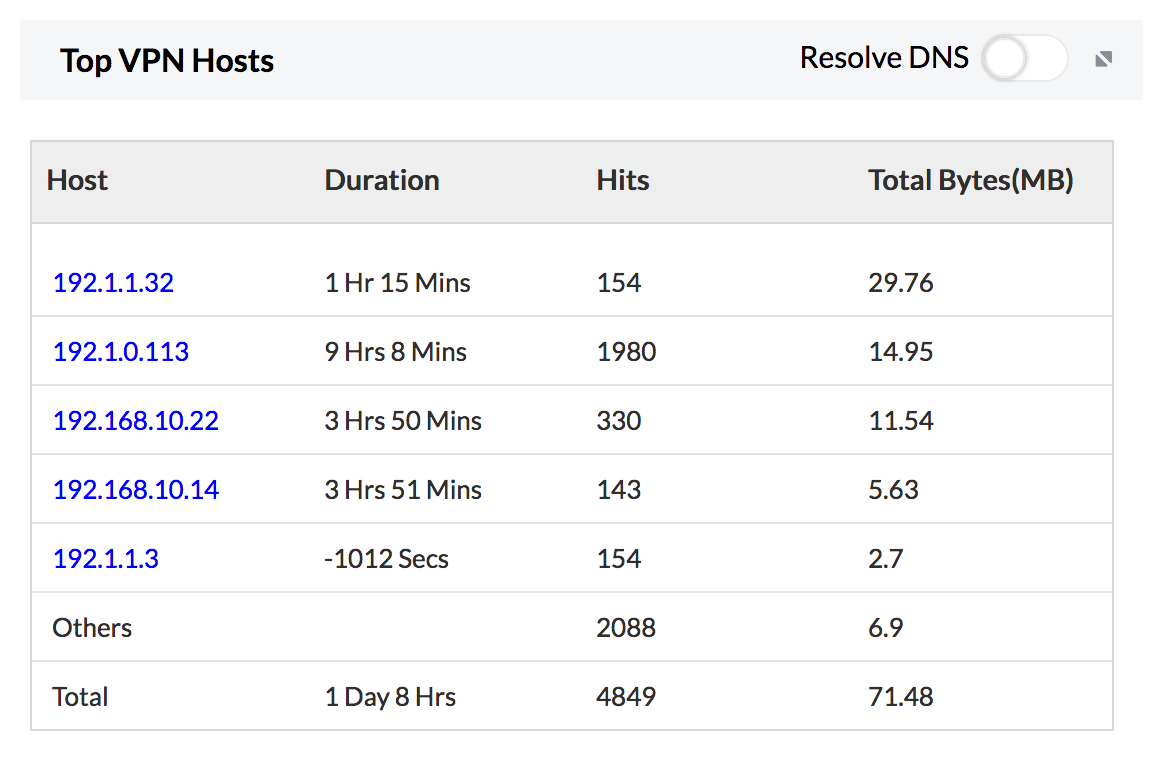
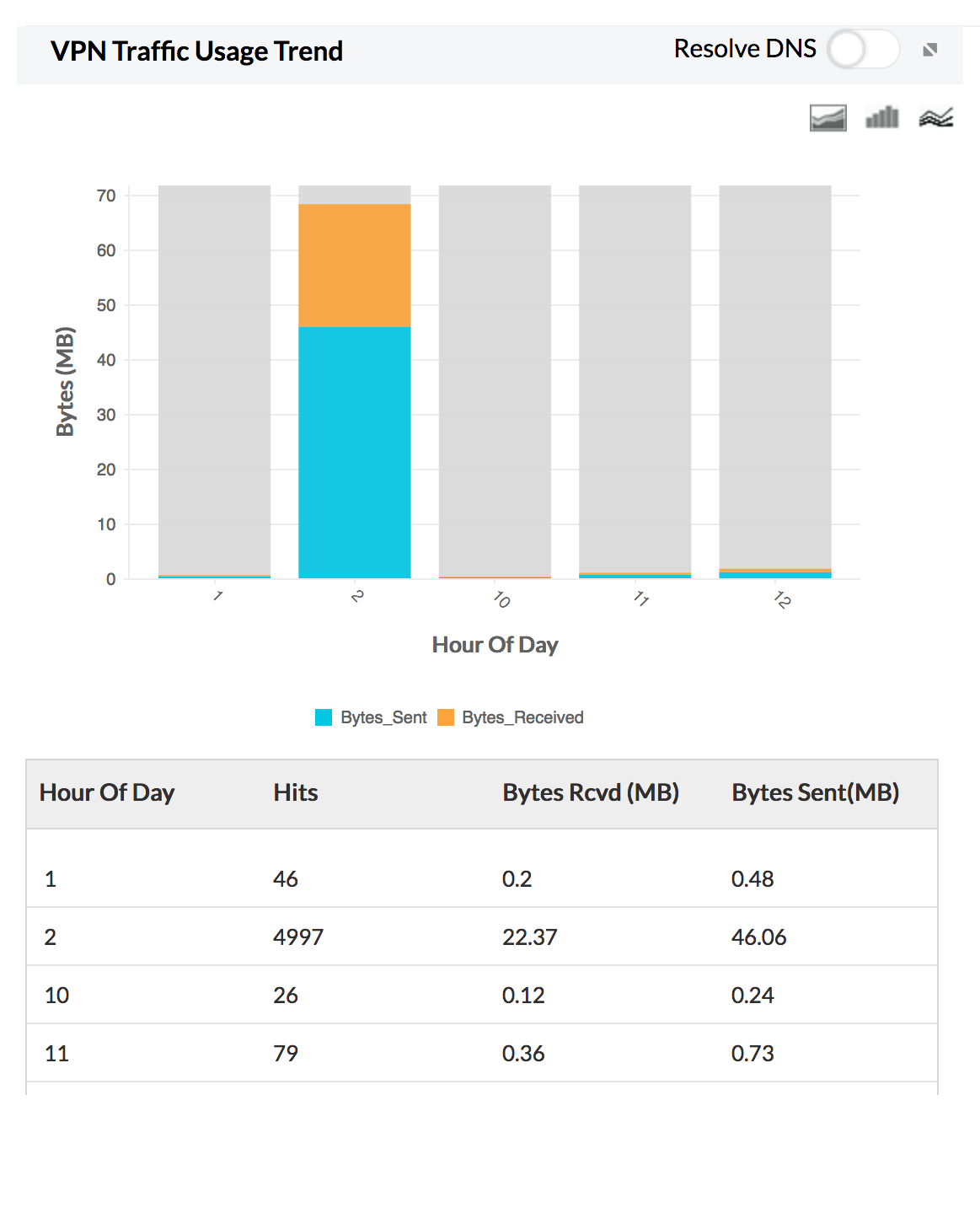
VPN Reports give detailed statistics on VPN usage, thus Firewall Analyzer acts as a VPN Monitor. VPN usage reports include drill down details on top VPN hosts, top protocols used by the VPN, and bandwidth used by the VPN during peak and off-peak hours. Trend reports show you VPN usage trends over time."
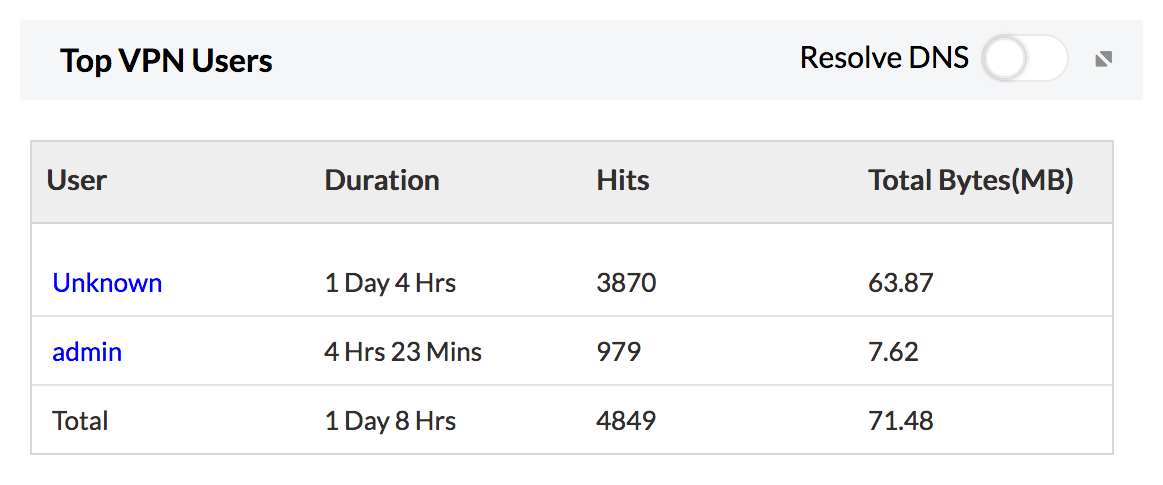
Top VPN users reports will be very handy if you have Remote Host VPNs configured in your environment. It basically gives you the users connected to your VPN and the amount of traffic consumed by them.
Top Failed VPN users will be very useful when somebody is trying to compromise your VPN network. Repeated or abnormal failed connections would require a closer look as it might result in attacks.
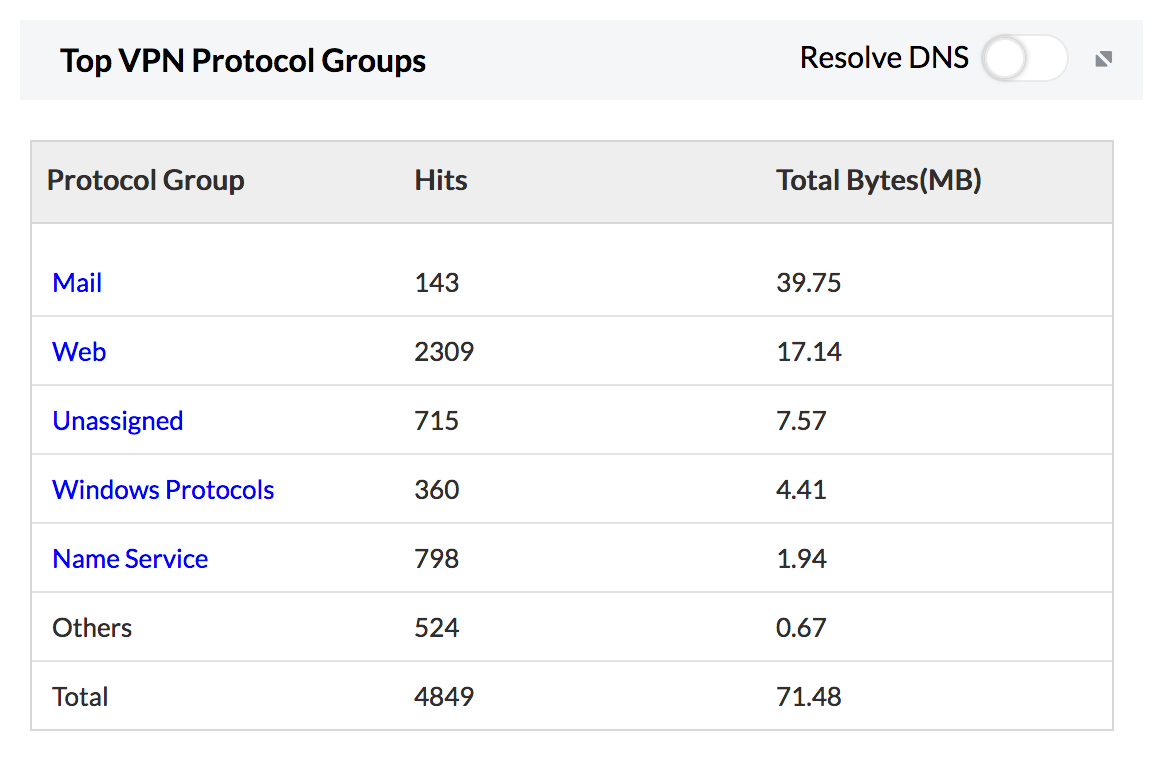
Top Protocol Groups, gives you an overview of what kind of protocol is used in your VPN network. This will be very useful in the case of Site To Site VPN. Some firewalls produce application layer protocol information in the VPN logs and some might not. For the firewalls that are producing protocol information in the logs, this report can give excellent insights.
When you have multiple VPNs in your network, you will be interested in seeing the amount of traffic that is going to search VPN. VPN usage reports (Site to Site VPN Monitoring) exactly addresses this requirement.
Request for a free personalized demo
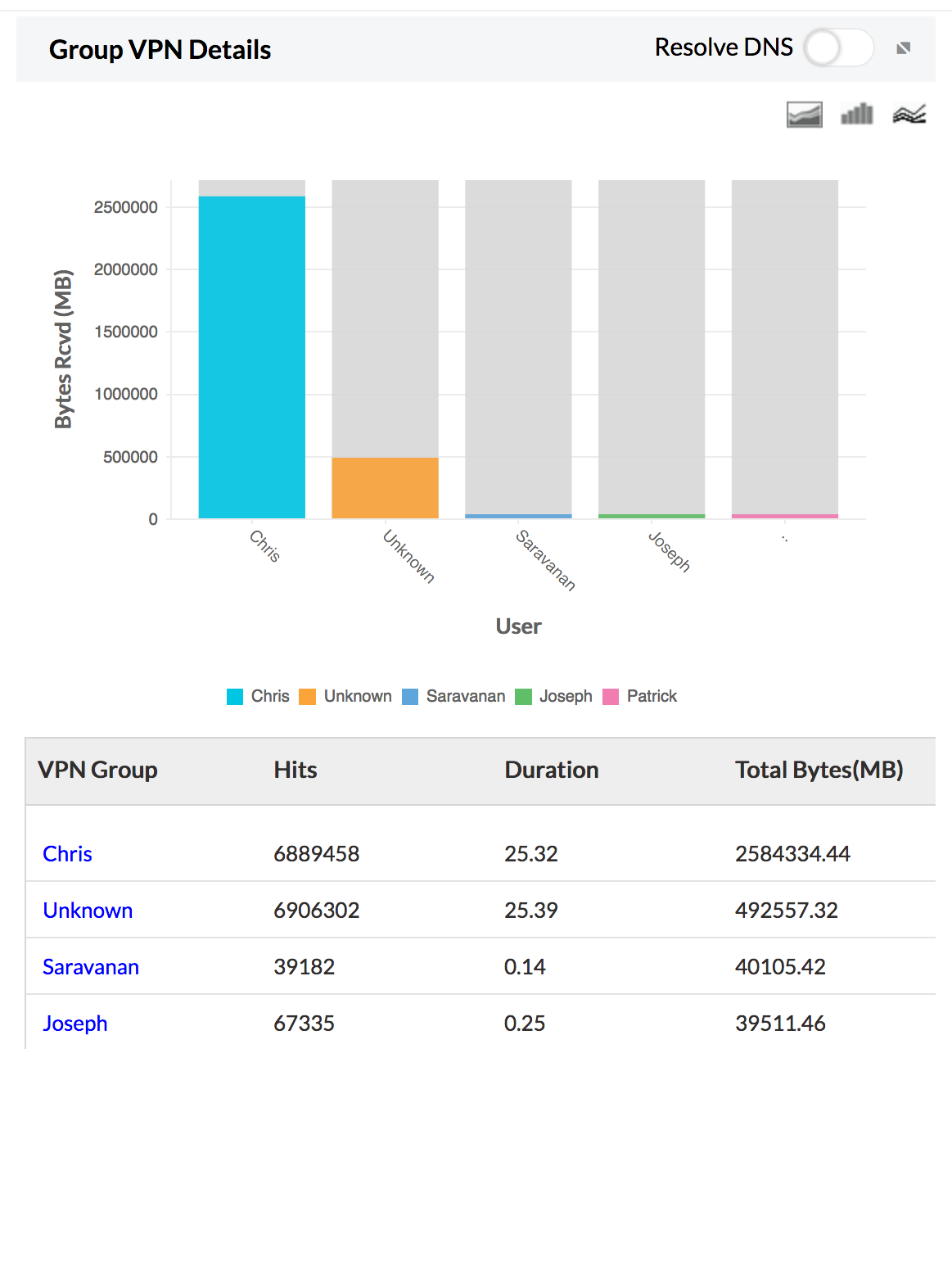
User-group VPN Reports
Provides VPN usage details for a group of users with details on number of hits, duration of usage, and total bytes of VPN traffic.
Featured links
Firewall Rule Management
Manage your firewall rules for optimum performance. Anomaly free, properly ordered rules make your firewall secured. Audit the firewall security and manage the rule/config changes to strengthen the security.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Log Management
Unlock the wealth of network security information hidden in the firewall logs. Analyze the logs to find the security threats faced by the network. Also, get the Internet traffic pattern for capacity planning.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Firewall Alerts
Take instant remedial actions, when you get notified in real-time for network security incidents. Check and restrict Internet usage if banwidth exceeds specified threshold.
Manage Firewall Service
MSSPs can host multiple tenants, with exclusive segmented and secured access to their respective data. Scalable to address their needs. Manages firewalls deployed around the globe.
With these VPN reports (VPN tracker), security administrators can easily plan an efficient VPN infrastructure that provides the ideal platform for remote employees to work without any hassle. A well-planned VPN infrastructure enables your company to retain its productivity and gain a competitive edge in today's challenging marketplace. Download a free trial of Firewall Analyzer,and get the best out of your VPN infrastructure.
Featured links