Firewall change management should be used before making changes to firewall or IDPS rules that affect users. A concrete firewall change management and firewall configuration monitoring process helps ensure complete cohesion in managing changes in your network.
How does Firewall Analyzer act as a firewall configuration management tool?
1. Firewall configuration change monitoring
Firewall Analyzer fetches the firewall configuration using CLI or API from your firewall devices and enables you to keep an eye on the changes being made to the network security infrastructure. Administrators may commit an unintentional error or carry out an improper change while acting on a firewall configuration change request giving room for breaches. This feature ensures that all the configurations and subsequent changes made in the Firewall device are captured periodically and stored in the database. Firewall Analyzer's configuration change management reports precisely helps find out 'who' made 'what' changes, 'when' and 'why' to the firewall configuration.
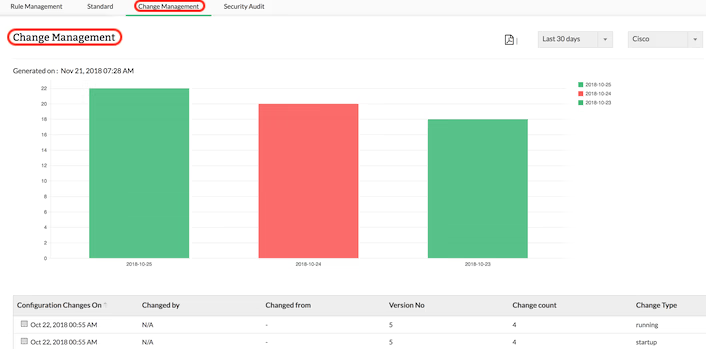
The following are the reports generated by this firewall configuration analysis tool.
Configuration change reports
- Running Configuration Changes Report - Report on difference between any two running configuration changes
- Startup Configuration Changes Report - Changes between running (current) configuration and startup (default) configuration
- Current Startup-Running Conflict Report - Conflict in configurations between startup and running
The Firewall Change Management reports can be scheduled and distributed via Email and can be exported to different formats. Not only that, you can also filter the firewall configuration change management report for known and recurring changes which clutters the report. Firewall Analyzer will exclude the lines in the report, matching the specified criteria (Exclude Criteria) for all or selected devices.
To know more about configuration change management, get a personalized demo.
Request Demo2. Firewall configuration change alerts
Firewall Analyzer (Firewall Change Management Software) generates alerts for the Firewall device configuration changes in real-time and it notifies via Email, SMS. Hence any change made to the firewall configuration is notified to the security admin and this beneficial in effective firewall change monitoring.
Monitor firewall changes securely and efficiently
- Monitor any changes with a structured process.
- Schedule routine checks to minimize disruption.
- Roll back changes easily in case of issues.
Firewall change management
In any organization, frequent firewall changes are a necessity when it comes to network security. Putting into place a streamlined firewall change management policy template reduces management time and also the chance of introducing new security or compliance issues with each change. A typical firewall change management process would include the following steps:
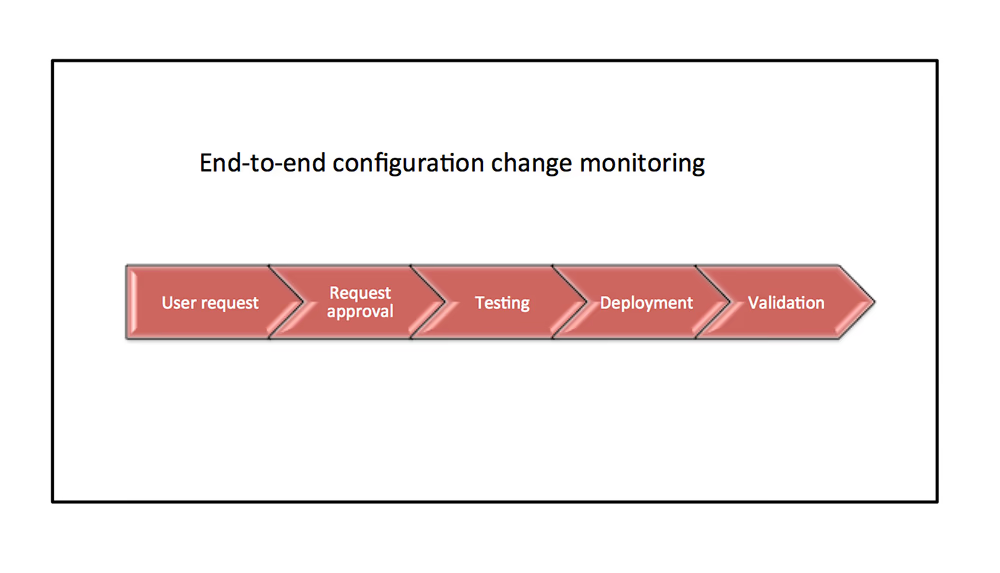
- Raise a request : A user initiates the process by raising a request for a specific firewall change. This request includes all necessary details, such as the purpose of the change, impacted systems, and expected outcomes.
- Request Approval : The request is reviewed and approved by the firewall or network security team. During this phase: The team evaluates the potential impact on security and compliance.Then, approves details, including the names of approving personnel and timestamps, are meticulously recorded for audit and future reference.
- Configuration Testing :Once approved, the proposed configuration is tested in a controlled environment to confirm that the changes will achieve the desired effect and ensure no unintended threats or vulnerabilities are introduced into the existing network setup.
- Deploy Changes :Following successful testing, the approved changes are implemented in the production environment. Careful attention is given to minimizing downtime and disruption during deployment.
- Validation :A validation process is performed to confirm that the new firewall settings are operating as intended and to identify and address any issues that arise post-deployment.
- Documentation :Comprehensive documentation is essential for effective firewall change management. This includes: detailed records of all changes made, reasons for the changes, time stamps of each step, names of personnel involved in the process
Benefits of Firewall Change Management process
- Improved Security: Prevent unauthorized changes and mitigate risks.
- Operational Transparency: Maintain clear records to support audits and compliance.
- Reduced Downtime: Minimize disruptions with pre-deployment testing and validation.
- Enhanced Efficiency: Save time and resources through a structured approach.
To get a complete list of supported vendors, click here to get a complete list of supported vendors. Firewall Analyzer also uses the firewall configuration to generate firewall policy management, security audit and compliance standards reports.