Palo Alto configuration management: ManageEngine Firewall Analyzer
How Palo Alto firewall configuration management impacts network security
Firewalls secure your company network from external threats, and firewall configurations control device functions. The stronger the firewall configuration, the stronger the network security; it's because of this that efficient firewall configuration management plays an important part in tightening network security.
A best practice is to analyze the configuration periodically and fix the security holes to prevent any threats. Imagine that you have recently found that your company network is getting repeatedly attacked, but the cause is unknown. In this case, the first thing you check is the device configurations; if they're sub-optimal, it may make the network vulnerable to attacks. To address this issue, you need to have a tool that will continuously audit device security and analyze the configurations.
Additionally, even if you have a strong firewall configuration, frequent and unapproved changes to device configurations may weaken their security. Manually, you cannot keep track of who is making what change, when, and why; instead, you should manage the firewall configuration changes automatically. Imagine you find that a security administrator made a configuration change to a device. You do not know why or when they made the change, or what device commands they executed. The change may have opened unsecured traffic, which will make the firewall vulnerable. To monitor and prevent unwanted changes, you need an efficient tool to manage the firewall configuration change.
Firewall Analyzer is best suited to manage Palo Alto firewall configuration
The Palo Alto next-generation firewall secures your network, but manually managing the configuration of devices is a daunting task. To combat this, you need an efficient tool for Palo Alto configuration management.
Firewall Analyzer is an ideal tool for Palo Alto config management. It has two functions:
- Change management
- Security auditing and configuration analysis
Keep track of configuration changes in real time
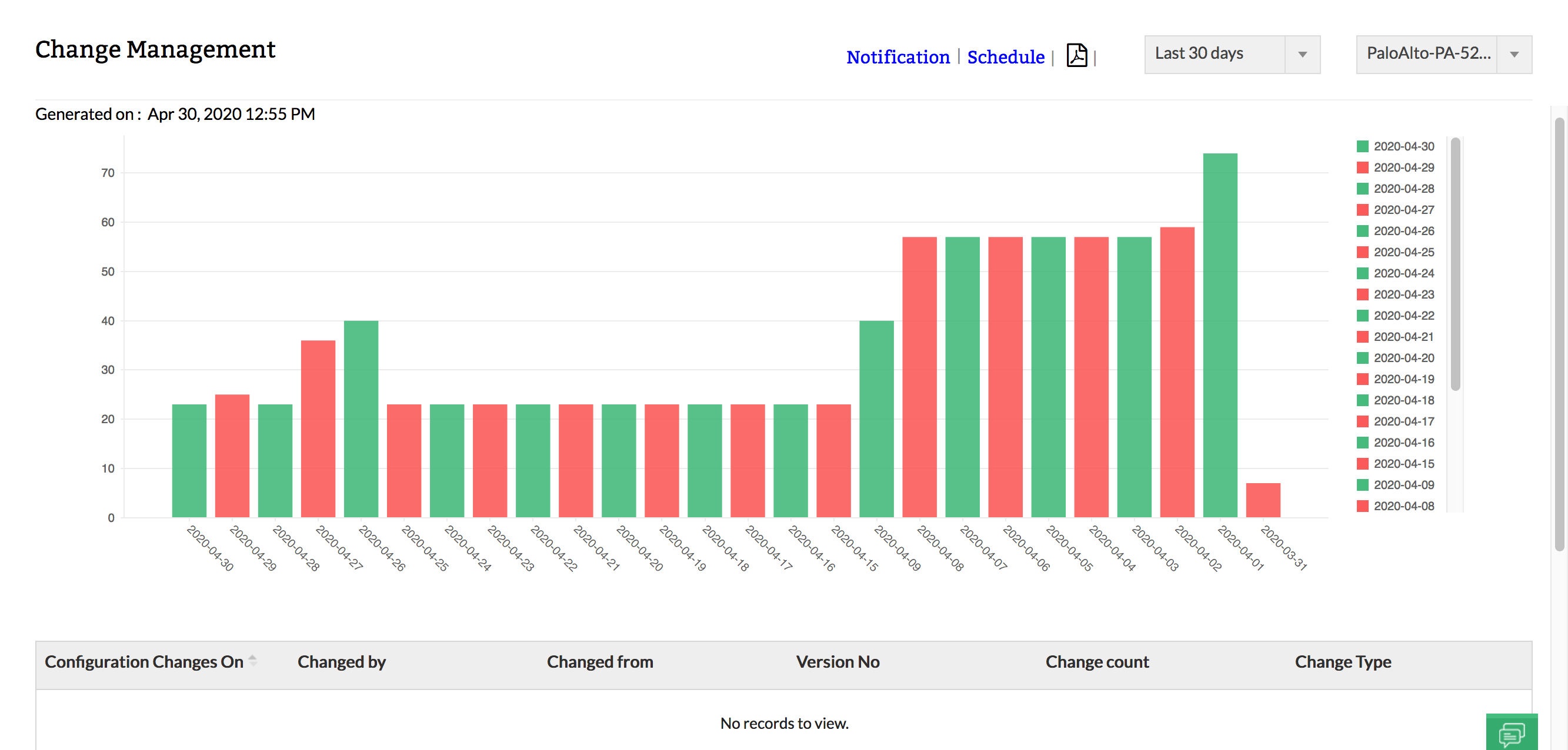
To address the challenge of change management, Firewall Analyzer alerts you in real time about changes done to the firewall configuration with notifications from both email and SMS. It also provides an elaborate Change Management report from which you can get the complete details of the changes, such as:
- Who has done the change?
- What was the change?
- When was the change done?
- Version number of the change
- Number of changes done
This report also offers details about the change, with the option to drill down further into each change. The line-wise details include:
- Configuration added
- Configuration modified
- Configuration deleted
- Only difference
It also provides the difference in configuration between Startup and Running configuration types and configuration versions. With the Change Management report, you gain ample information on each configuration change, enabling you to manage device configurations efficiently to keep your network secure. With this Firewall Analyzer report, Palo Alto firewall config is easy.
Analyze device configurations to tighten security controls
Firewall Analyzer provides exhaustive Palo Alto networks config audit report called Security Audit and Configuration Analysis report for each device. With these reports, you can get details about misconfiguration and sub-optimal configuration, with information like the configuration issue, its impact on security, the ease of a fix, and recommends steps to apply a fix. With these reports, you can tighten device configurations and fulfill your network security strategy requirements.
Sample Security Audit and Configuration Analysis report is available in this page.
Apart from the above functions, Firewall Analyzer collects logs to monitor all the firewall administrator activities. You can view the commands executed by administrators, along with importantly denied logon attempts.
Other important reports are the Standards reports, which cover various industry regulatory compliance standards. These reports enable you to meet regulatory compliance requirements by monitoring and analyzing log data from all firewall devices. Firewall Analyzer generates Palo Alto firewall compliance reports easily by monitoring your firewall data in real time.
The Standards reports available include:
- PCI-DSS
- ISO-27001
- NERC-CIP
- NIST
- SANS
You can efficiently manage Palo Alto firewall with Firewall Analyzer, making it easier than ever to secure your network. Try Firewall Analyzer for free.
Featured links
Firewall Reports
Get a slew of security and traffic reports to asses the network security posture. Analyze the reports and take measures to prevent future security incidents. Monitor the Internet usage of enterprise users.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Rule Management
Manage your firewall rules for optimum performance. Anomaly free, properly ordered rules make your firewall secured. Audit the firewall security and manage the rule/config changes to strengthen the security.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Firewall Alerts
Take instant remedial actions, when you get notified in real-time for network security incidents. Check and restrict Internet usage if banwidth exceeds specified threshold.
Manage Firewall Service
MSSPs can host multiple tenants, with exclusive segmented and secured access to their respective data. Scalable to address their needs. Manages firewalls deployed around the globe.