
On January 24, 2020, a water supplier in Greenville, North Carolina revealed that its utility services had been compromised in a security incident. Spokesperson Emerald Clarke mentioned that the company’s online and pay-by-phone systems were affected.
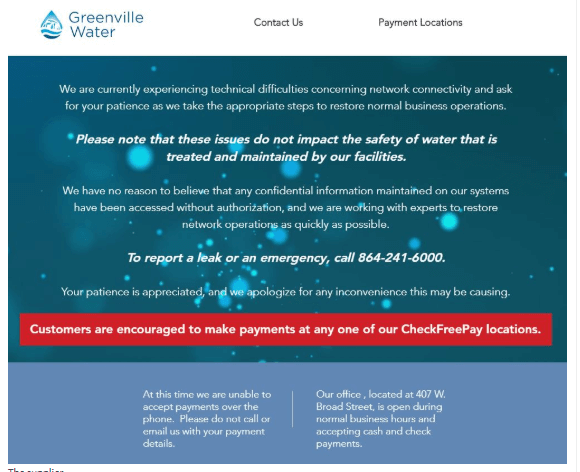
Greenville Water did not give details regarding the attack, but notified its customers that services were temporarily suspended due to a technical glitch.
Greenville Water CEO David Bereskin said, “We have been preparing for potential attacks for years and put specific protections in place to ensure the safety of our data and the integrity of our water. While this has caused a temporary disruption, we are fairly certain that our data has not been compromised. It has created a situation where we have lost access for a brief period of time, but we anticipate normal business operations being restored in the next two-three business days."
The company estimates that around 200MB of data, including employment application information on 1,987 people, employee information on 4,566 people, and information on 1,569 retired employees of affiliated companies has been compromised in the attack. The authorities and affected customers have been notified about the breach.
The firm supplies water to around 50,000 residents. It has notified government officials and the regulatory bodies in the area about the breach. According to Clark, the incident is being investigated with the help of security experts, and the company is reinforcing existing security measures to mitigate future attacks.
Protect yourself against cybersecurity disasters like this by investing in a tool that will protect your network from brute-force attacks, ransomware threats, and denial-of-service (DoS) attacks. Download ManageEngine Log360, a tool that helps combat both internal and external security attacks.
Log360, our comprehensive SIEM solution, can help your organization by:
Download a free trial of Log360 to see the tool in action for yourself.
© 2025 Zoho Corporation Pvt. Ltd. All rights reserved.