In July 2019, researchers at the U.S. cybersecurity firm FireEye discovered that Iran-based cyber espionage group APT34 has been sending phishing invites via LinkedIn. APT34, also known as Helix Kitten or OilRig, has been known to attack regional corporations in the Middle East since 2014.
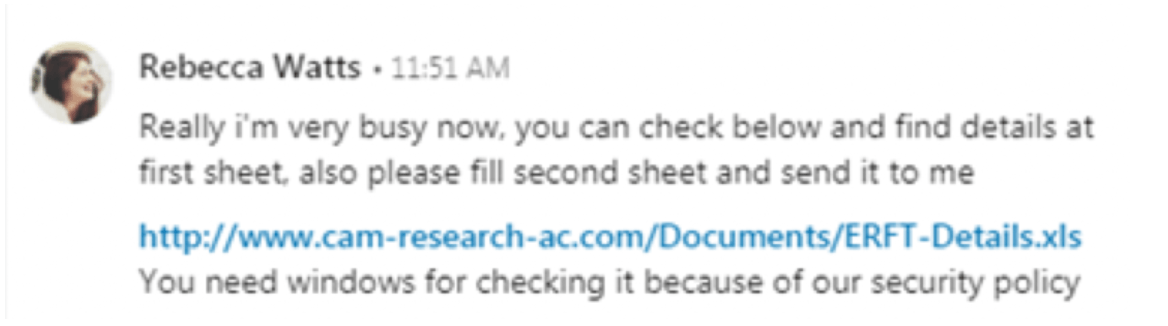
The phishing invites appeared to be sent from a Cambridge University researcher going by the name Rebecca Watts. The group has targeted organizations belonging to financial, energy, and government entities in the Middle East.
Screenshot of the message sent from the attacker:
According to research by FireEye, "This is not the first time we’ve seen APT34 utilize academia and/or job offer conversations in their various campaigns. These conversations often take place on social media platforms, which can be an effective delivery mechanism if a targeted organization is focusing heavily on email defenses to prevent intrusions."
The malware was identified as a backdoor, Tonedeaf, which communicated with the command-and-control (C2) server using HTTP GET and HTTP POST requests. The malware is configured to collect system information, upload and download files, and execute arbitrary operating system (OS) commands. FireEye was able to identify three additional malware families in the code: ValueVault, Longwatch, and Pickpocket, a browser credential-theft tool.
Hackers are evolving, and so are their attack techniques. Social media messages and invites are the new medium through which threat actors like APT34 are reaching their targets. Staying alert and revamping security protocols regularly is the only way government agencies and organizations can stay ahead of attackers.
You will receive weekly cybersecurity news soon!
© 2025 Zoho Corporation Pvt. Ltd. All rights reserved.