How to install Secure Gateway on Windows Server Core edition of Windows Server OS?
Description
Windows Server Core edition of Windows Server OS is the minimal installation option, containing only the core features required to execute server roles and run applications. These machines are designed for applications which requires minimal user interaction and hence do not have a GUI. The nonexistence of a GUI in Server Core, reduces the disk space and memory usage, apart from requiring limited maintenance. As setting up a Secure Gateway (Forwarding server) does not require an extensive GUI usage, the Server Core is a serviceable option. Administrators can manage Server Core using command-line interface, PowerShell, Remote Server Administration Tools (RSAT), Windows Server Manager or Windows Admin Center.
To establish secure connection between the MDM server and third-party cloud resources, you can install a Secure Gateway on the Server Core machine. Follow the steps given below:
Steps
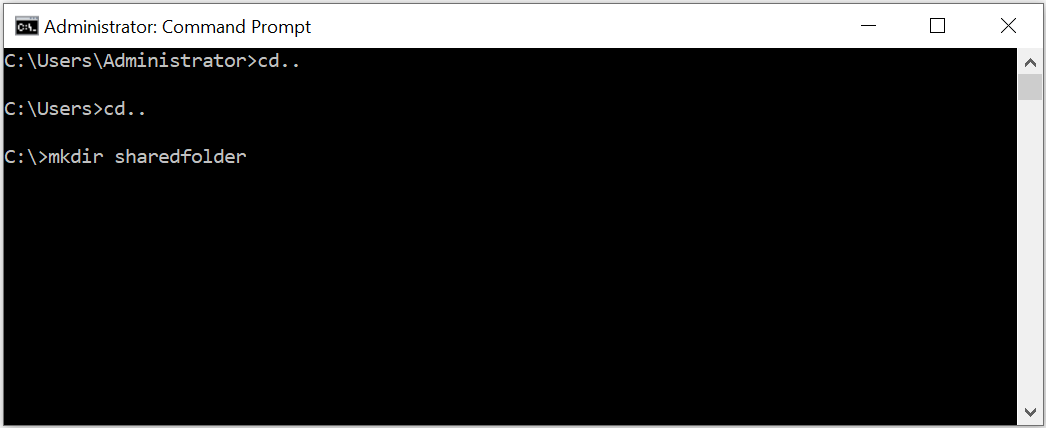
- Open command prompt in the server machine.
- Create a folder called sharedfolder in the server machine.
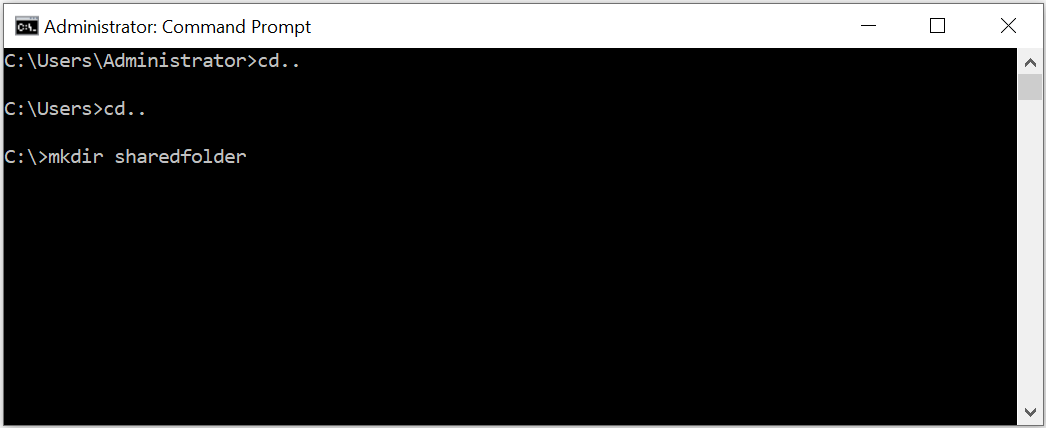
-
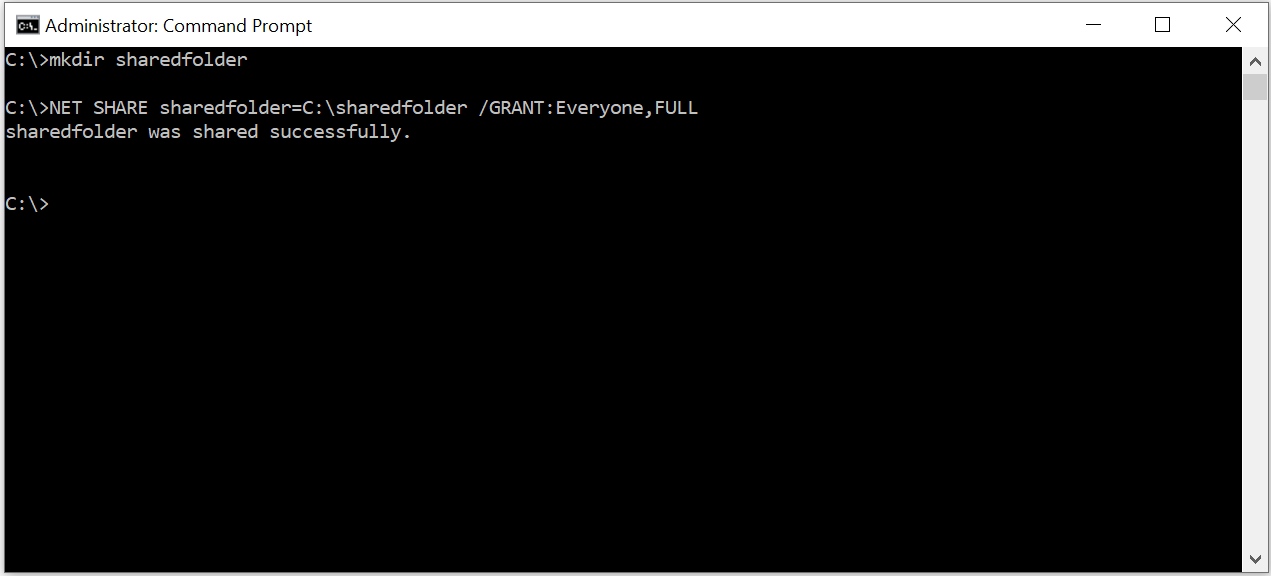
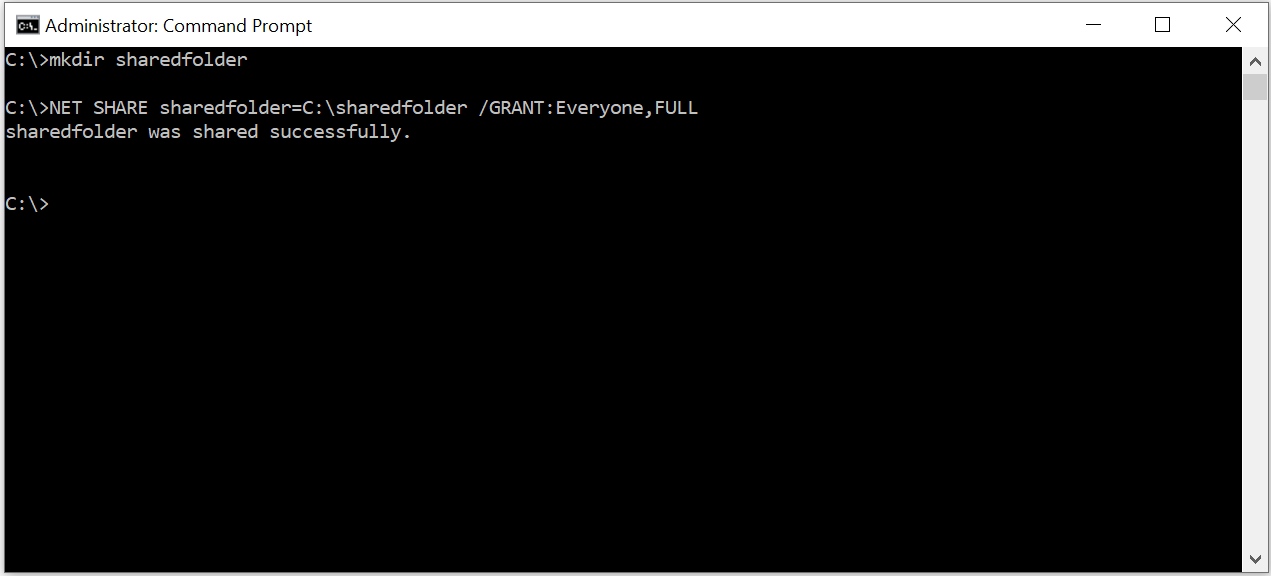
Share the folder using the following command:
NET SHARE sharedfolder=C:\sharedfolder /GRANT:Everyone,FULL
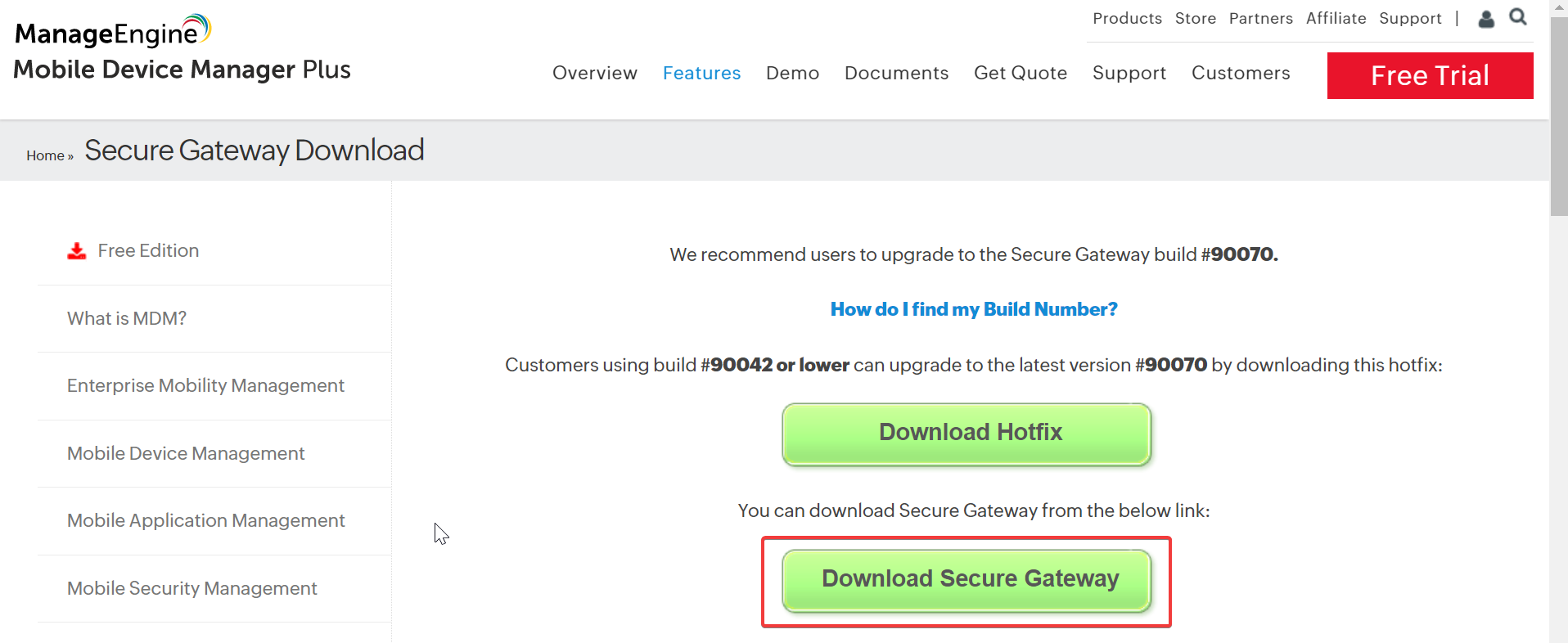
- Visit this page from another computer in your network and click on "Download exe":
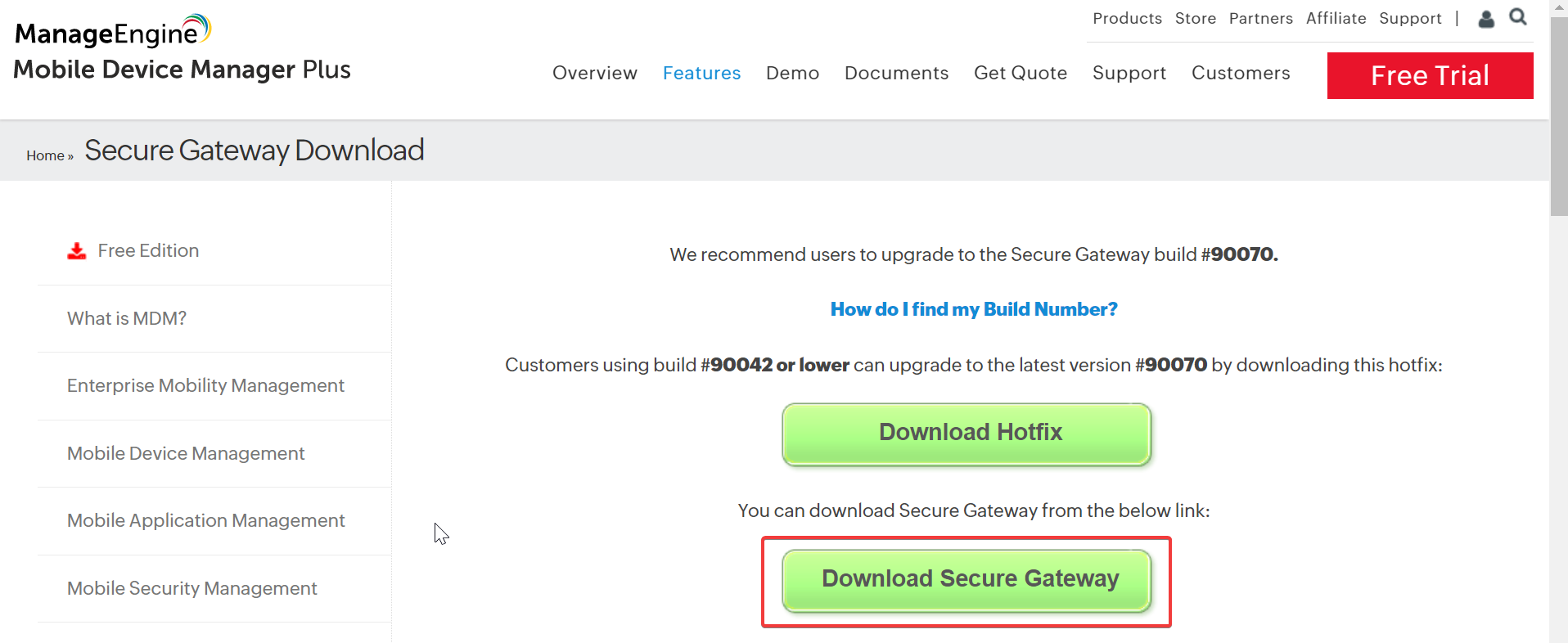
MDMSecureGatewayServer.exe will be downloaded on the machine.
- Copy MDMSecureGatewayServer.exe to the folder "sharedfolder" created in step 2.
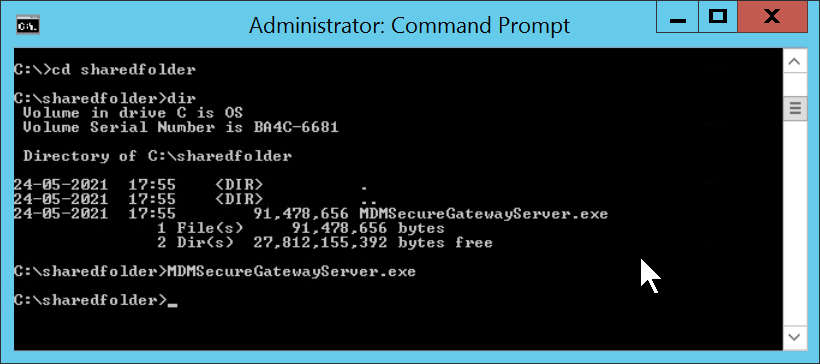
- In Windows Server core navigate to "sharedfolder" in command prompt and run the following command:MDMSecureGatewayServer.exe
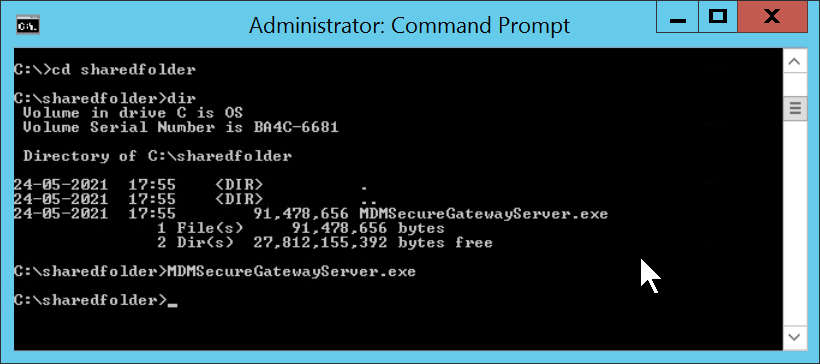
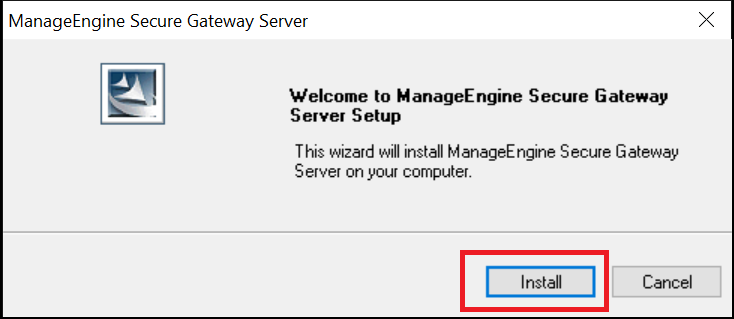
An installation wizard will be launched.
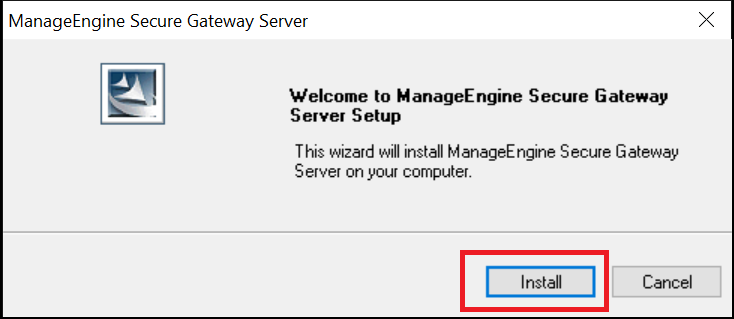
- Once the installation wizard is launched, click on the Install option.
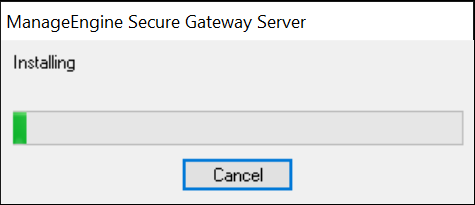
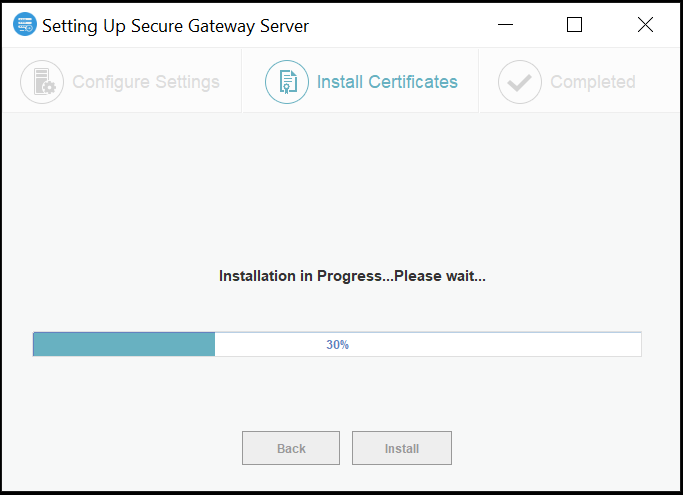
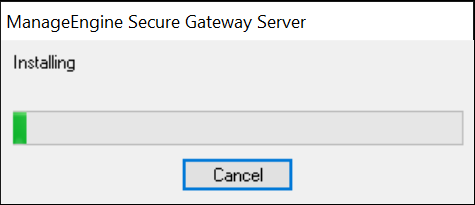
- Wait for the installation process to be completed.
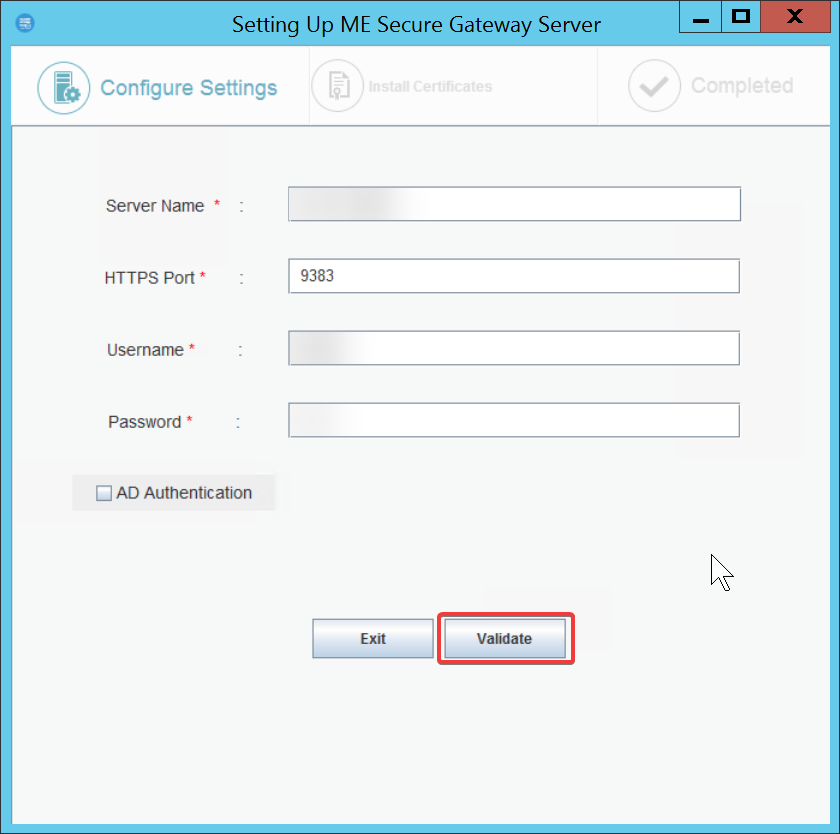
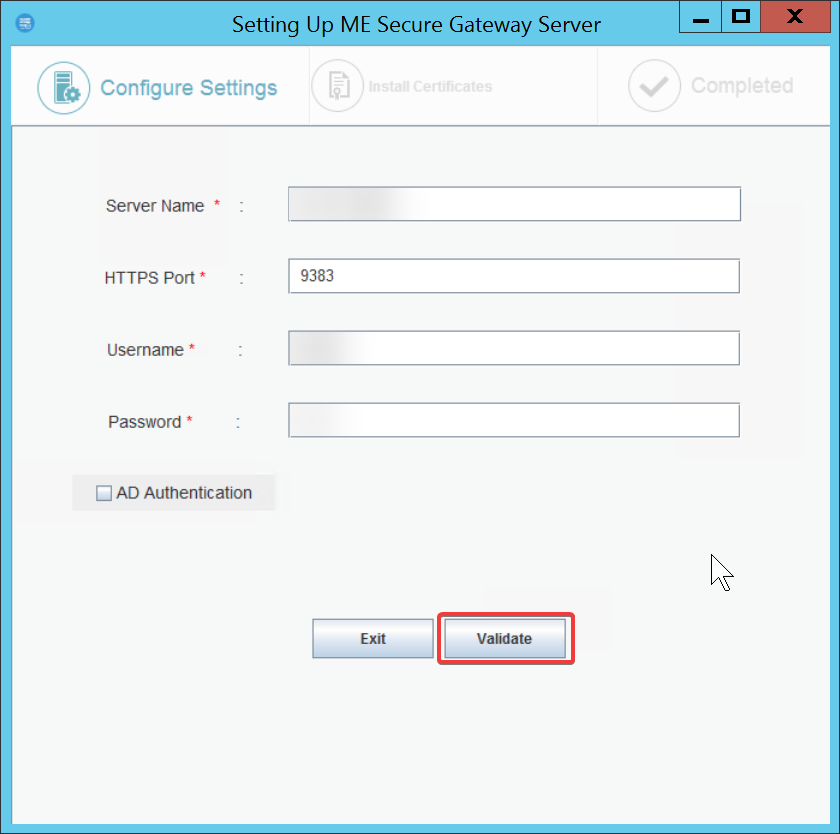
- After installation is complete, a pop-up will be displayed, to set up the Secure Gateway. In the Setting Up ME Secure Gateway Server pop up, enter the Server name, the HTTPS port number, and the user's credential which has administrative privilege in the product's server, as shown below, and click on Validate
Note:If the pop-up does not open, go to C:\ManageEngine\ME_Secure_Gateway_Server\bin\ using Command Prompt and run FSConfigure.bat
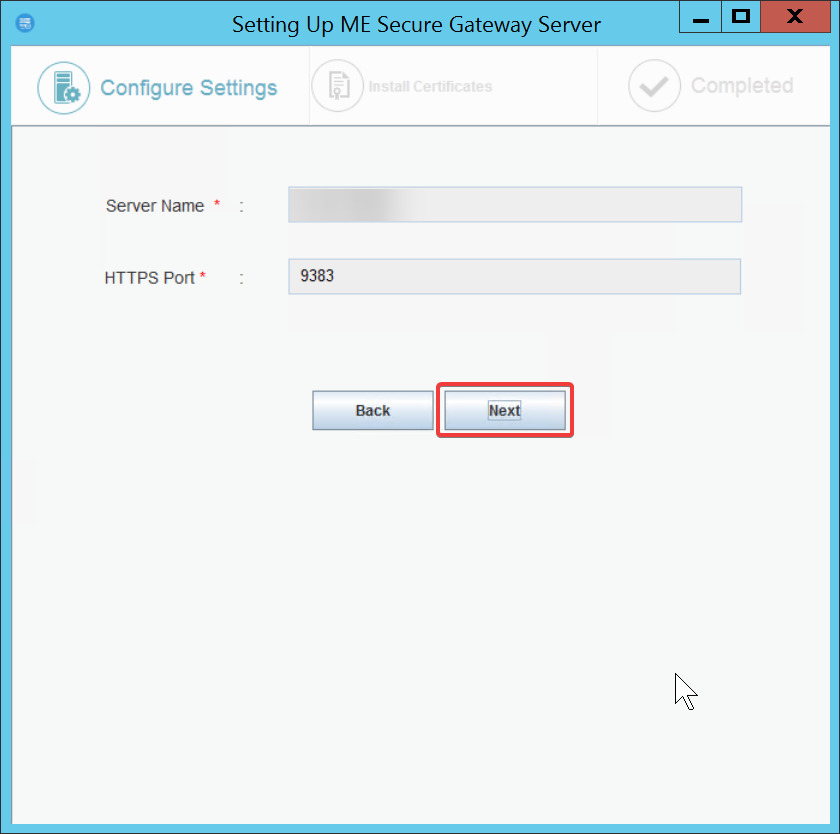
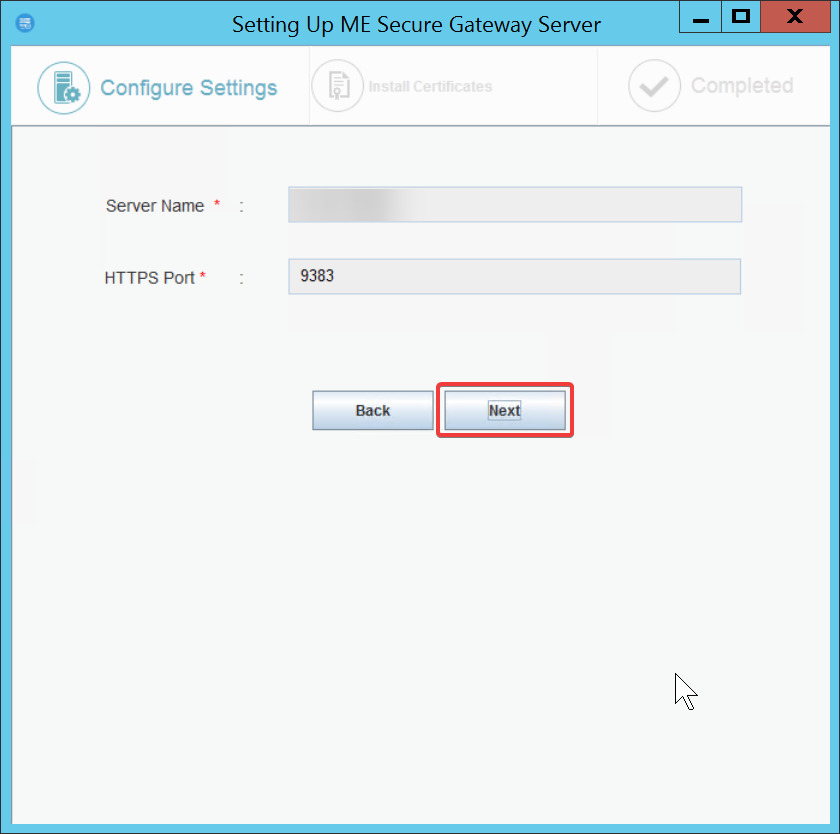
- Click on Next:
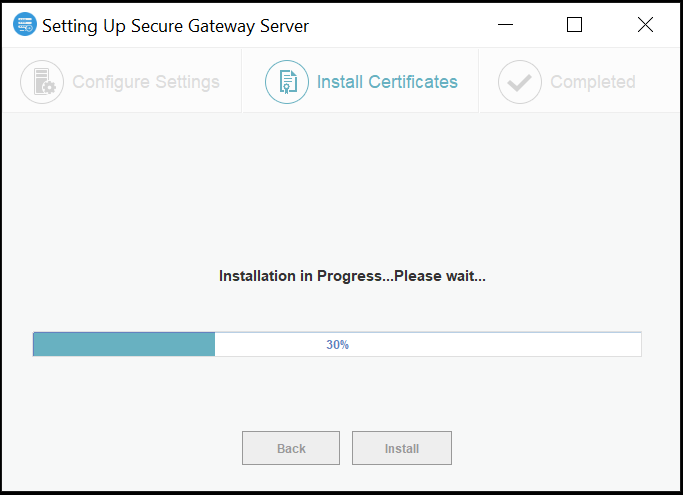
- Wait for the installation process to be completed:
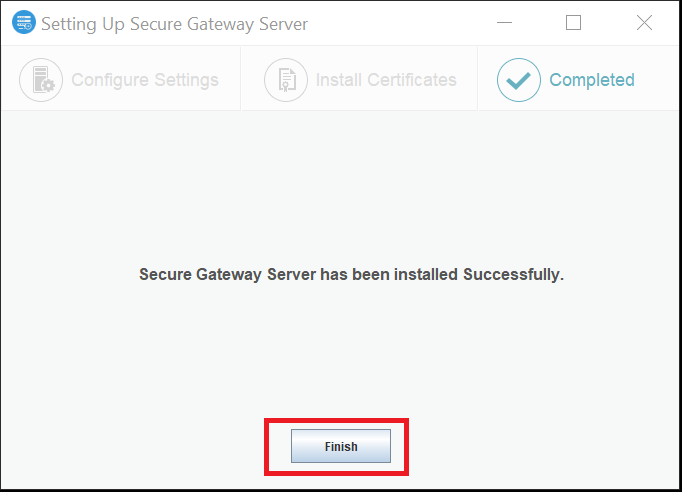
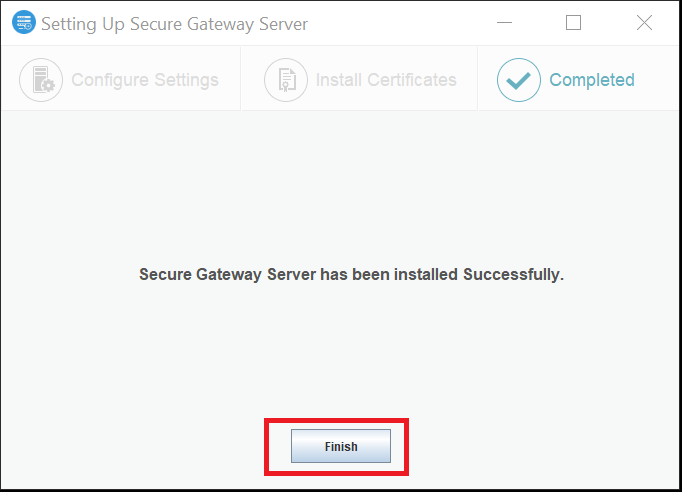
- Click on Finish
Note: For the Secure Gateway to work, the inbound port, 9383 needs to be open on the Firewall.
To open ports on the Firewall:
- Open Task Manager and go to File -> Run New Task -> type Powershell and press the Enter key.
- Run the following command on the PowerShell window: New-NetFirewallRule -DisplayName "FS" -Direction Inbound -Action Allow-Protocol TCP -LocalPort 9383