How to Search
EventLog Analyzer provides a dedicated section for log data search, where you can search the raw logs and detect network anomalies like mis-configurations, viruses, unauthorized access, applications errors, etc. Click the 'Search' tab in the UI.
The procedure to search th logs is given below:
Select specific Host(s), Host Group(s) for log search
To narrow down the search to a specific host(s) or group of hosts, type in the host name(s) or group(s) name in the text box provided or else use the 'Pick Host' link to select the host(s) or host group(s). If host(s), Host group(s) are not selected, log search will be carried out across all available hosts.
Select specific Log Type(s) for log search
You can narrow down the search to the type of log (example: Windows Event Log, Syslog, Oracle Logs), by selecting it from the Log Types list. If log type is not selected, log search will be carried out on all available log types.
By default (if the host name(s) or group(s) name are not provided, and 'All Log Types' option remains unchanged), you can search across all hosts and all log types.
Types of Search
EventLog Analyzer supports both 'Basic' and 'Advanced' search. You can perform Wild-card search, Phrase search, Boolean search, Grouped search, and Range search
Basic Search
If you want to manually type-in your own search string (search criteria) and search the logs, use the 'Basic' search link.
Search for field values
Type the field value directly in to the Search box.
Search with fields
Type the field name and value directly in to the Search box. The expression for field name and value pair is <field name> = <field value>
Example: EVENTID = 7036
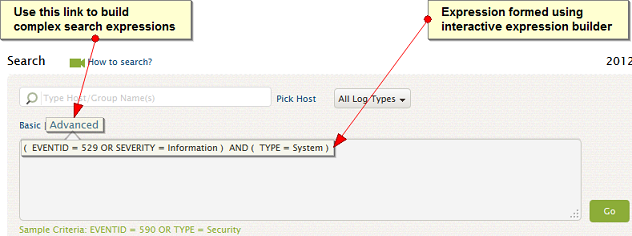
Advanced Search
To build complex search expressions with the aid of an interactive search builder, use the Advanced link.
Set criteria to search
You can have one or more fields in a group and one or more groups to specify criteria filters for search. The fields in a group are related using Boolean operator and the groups are also related in the same way.
If you have defined the criteria, click 'Apply' button.
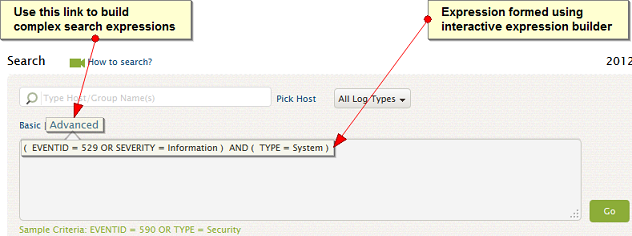
The search criteria expression appears in the text box. Click 'Go' button to preview the search results.
It is displayed in a graph 'Result Graph' and the entries are listed below. The result graph is displayed for a period of two weeks only.
Note: If the upgrade to the latest version is less than two weeks, the graph is displated only for the period from the date of upgrade
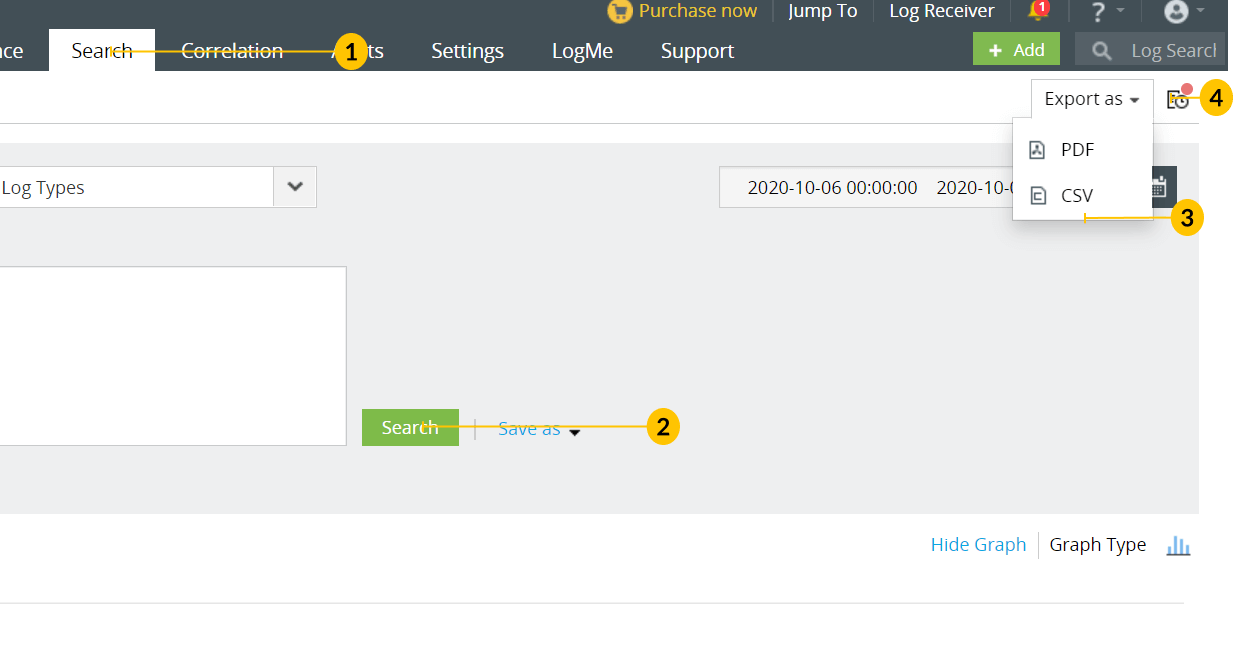
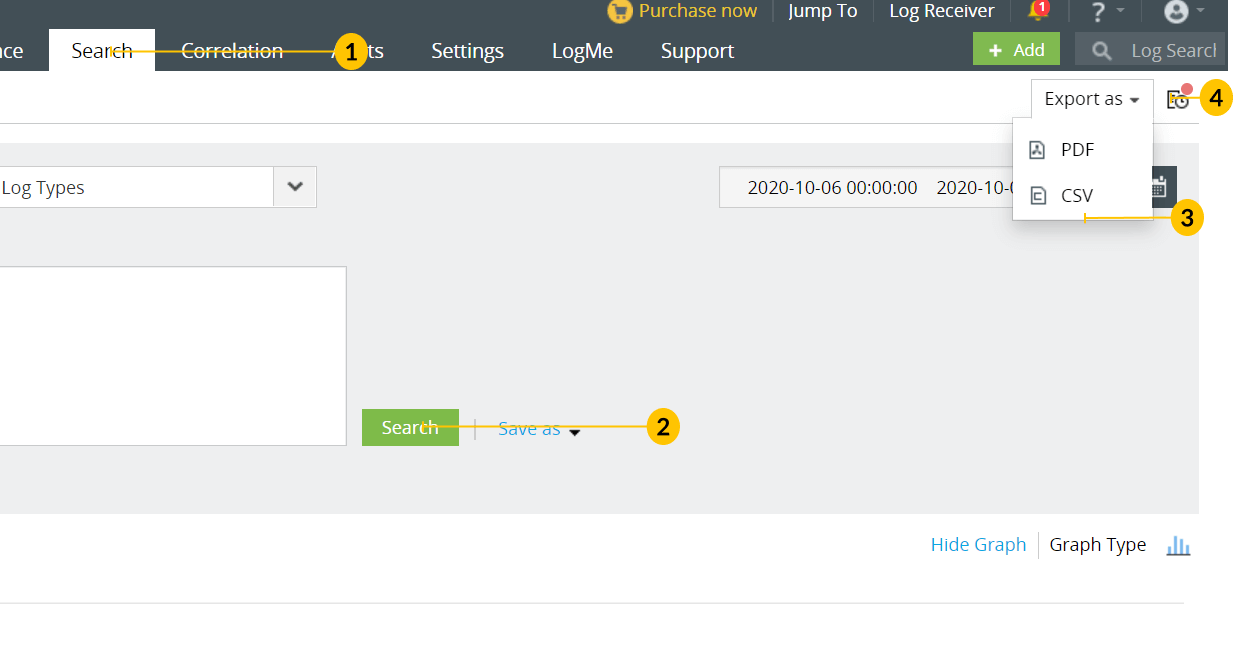
How to clear and save Search?
Clear the search
'Clear Search' clears the search query.
Save the search
If you are satisfied with the preview of the search result, you can save the search query by clicking 'Save Search' and the corresponding search result as a report profile.
More Search Examples - Basic Search
Use boolean operators to search
The expression with boolean operator is <field name> = <field value> <boolean> <field name> = <field value>. You can use the following boolean operators: AND, OR, NOT.
Example: HOSTNAME = 192.168.117.59 AND USERNAME = guest
Use comparison operators to search
The general syntax for using comparison operator is <field name> <comparison operator> <field value>. You can use the following comparison operators: =, !=, >, <, >=, <=.Example: HOSTNAME != 192.168.117.59
Use wild-card characters to search
The general syntax for using wild-card character is <field name> = <partial field value> <wild-card character>. You can use the following wild-card characters: ? for single character, * for multiple characters.
Example: HOSTNAME = 192.*
Use phrase to search
The general syntax for using phrase is <field name> = <"partial field value">. Use double quotes ("") to define phrase in the field value.
Example: MESSAGE = "session"
Use range to search
The general syntax for searching a range of values is <field name> = [<from-value> TO <to-value>]. Use square brackets '[]' to define 'from' TO 'to' range of field values.
Example: USERNAME = [k To z]
Use grouped fields to search
The general syntax to search with grouped fields is (<field name> = <field value> <logical operator>.<field name> = <field value>) <logical operator>.<field name> = <field value>. Relate the field value pairs logically and group them using brackets '()' and relate the grouped fields logically.
Example: (SEVERITY = debug or FACILITY = user) and HOSTNAME = 192.168.117.59