SOX compliance with EventLog Analyzer
ManageEngine EventLog Analyzer acts as a SOX compliance software that conducts in-depth auditing across the network to help you comply with Section 404 of SOX concerning IT process controls. The solution also provides SOX compliance reports to simplify regulatory procedures.
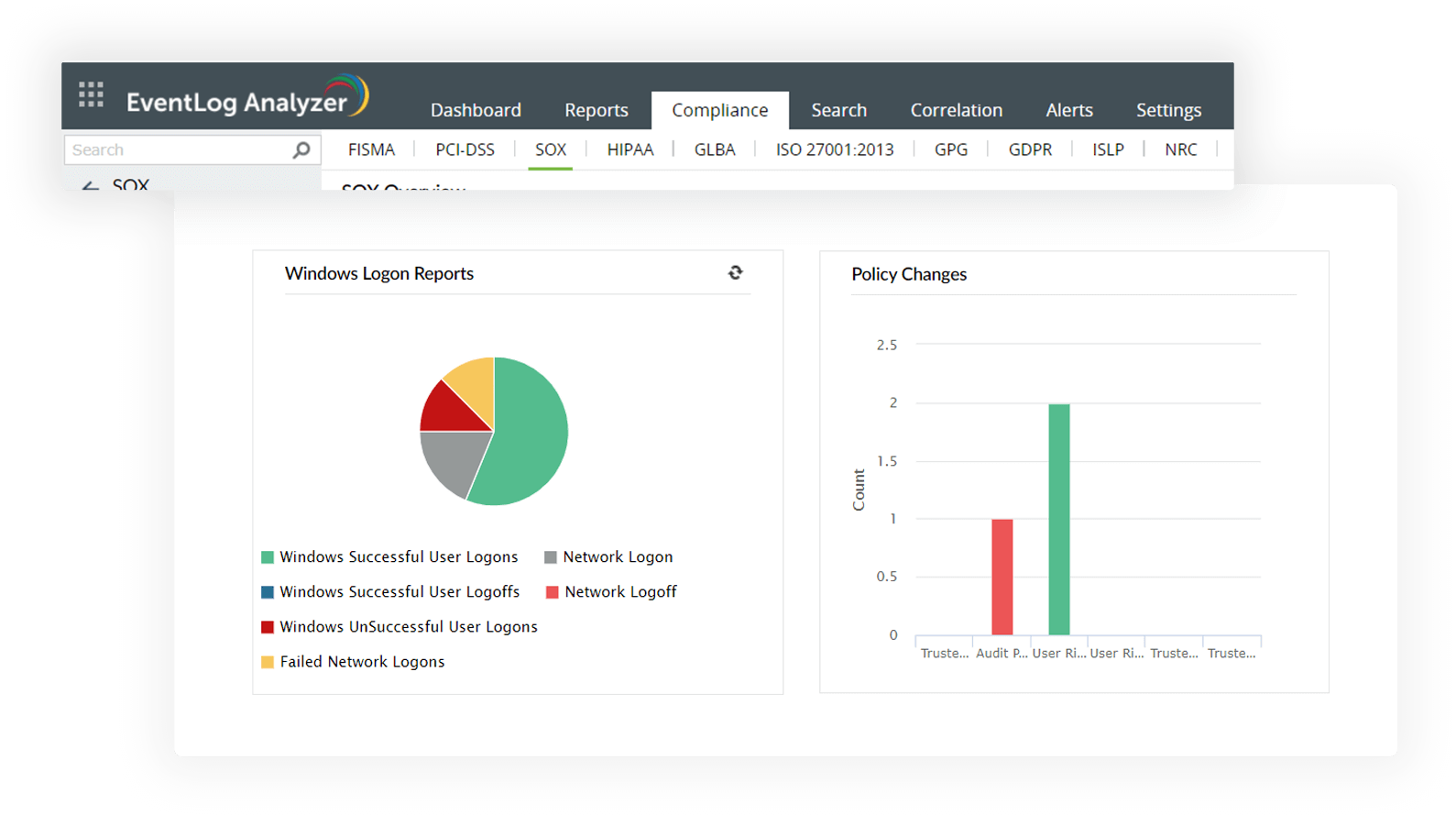
Monitor user access to systems and detect possible abuse
Satisfy Section 302 (a) (4) (A), (C) & (D) of SOX that mandates close monitoring of user access to systems and detect abnormal user behavior. EventLog Analyzer tracks logon and logoff activities, privileged user access, unsuccessful logon attempts, system events, successful or unsuccessful user account validations, and terminal service sessions across the network.
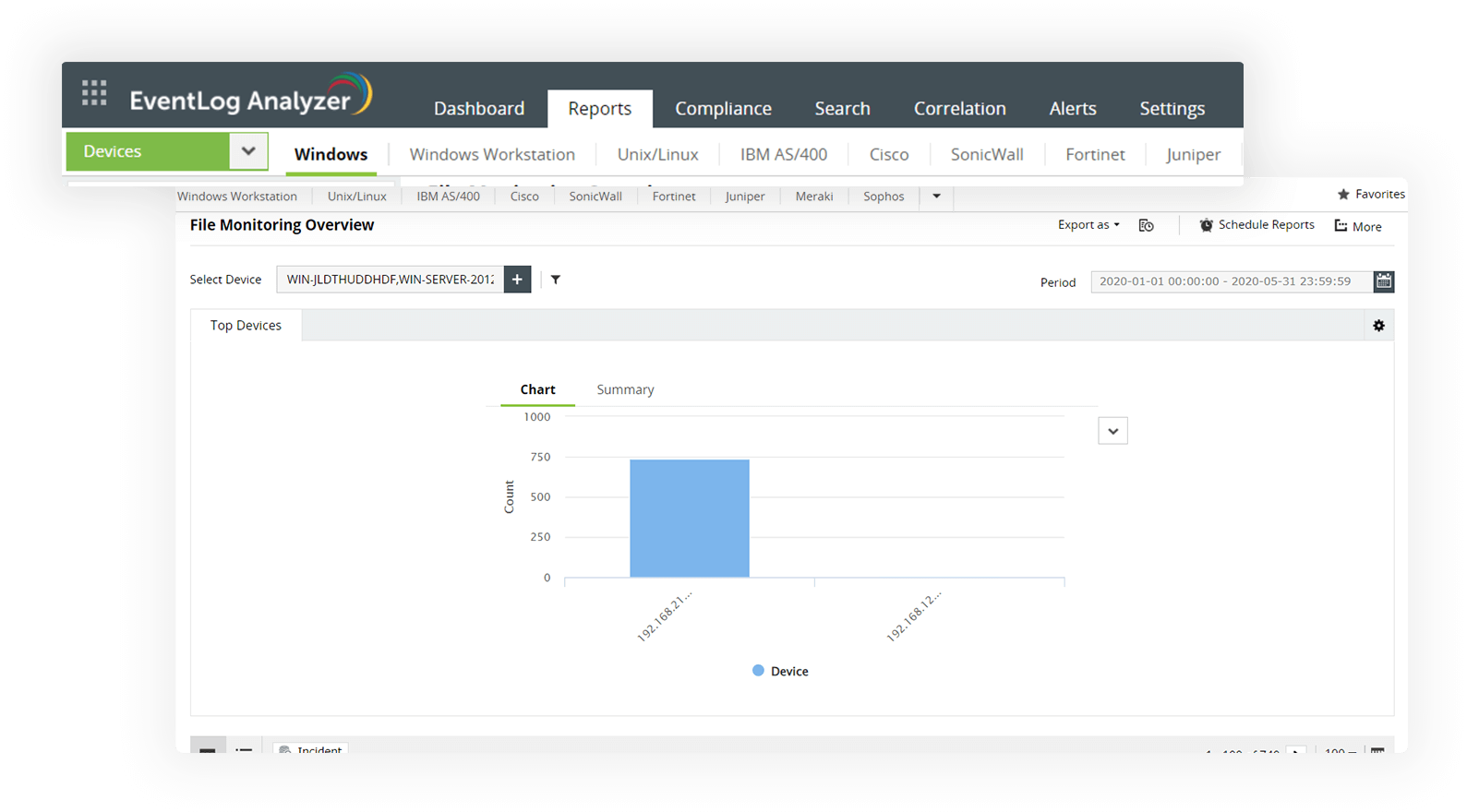
Audit object and log access to spot malicious activities
Easily drill down to the root cause of critical network events like log clearance or confidential object modification by unauthorized users. The file integrity monitoring module of EventLog Analyzer enables you to probe and receive a detailed overview about who or what accessed your organization's confidential data.
The solution also facilitates forensic analysis and conducts exhaustive SOX compliance audit trails for log accesses to find out if any logs have been tampered with. You will also comply with SOX's section 302 (a) (4) (A), (C) & (D) by monitoring these activities.
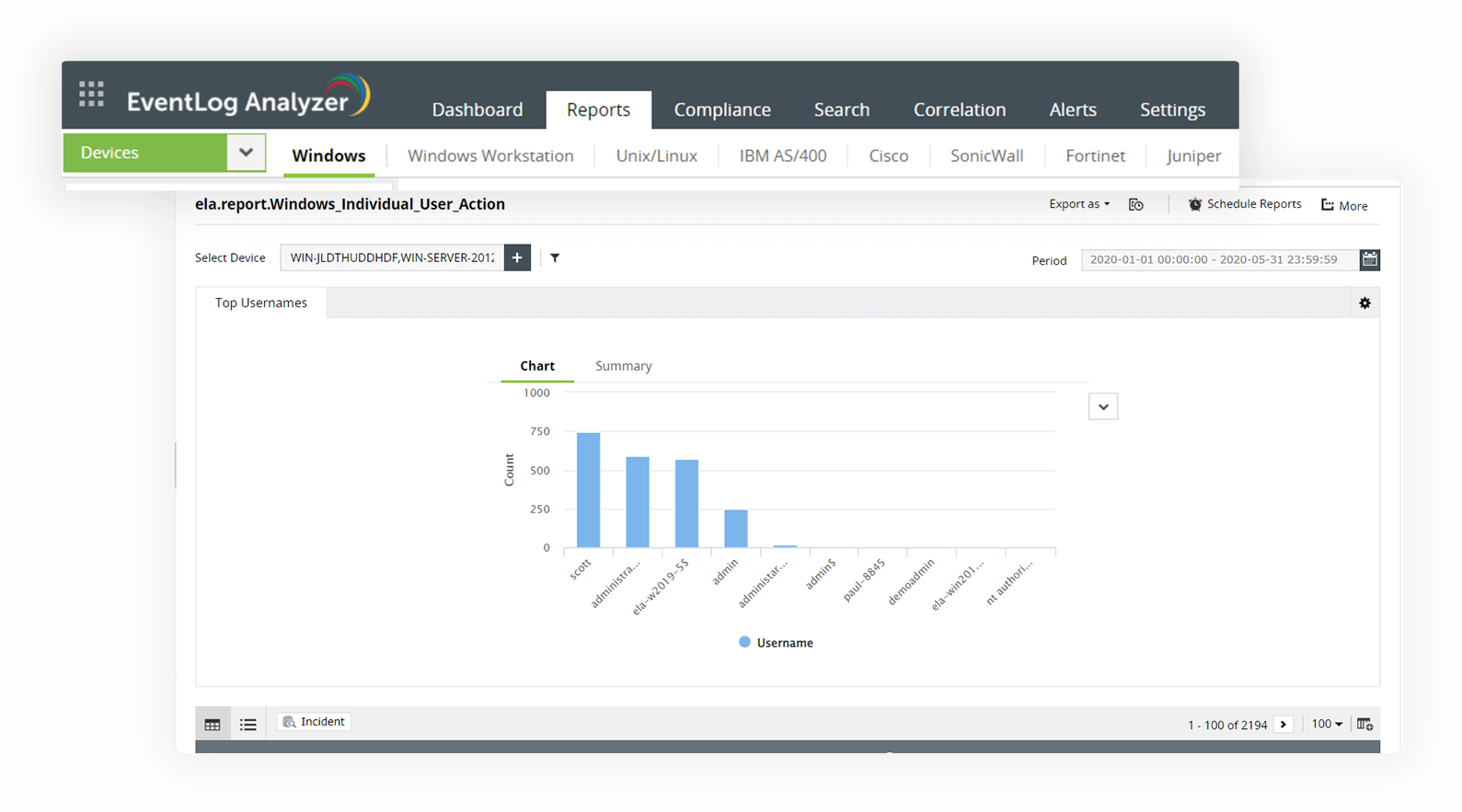
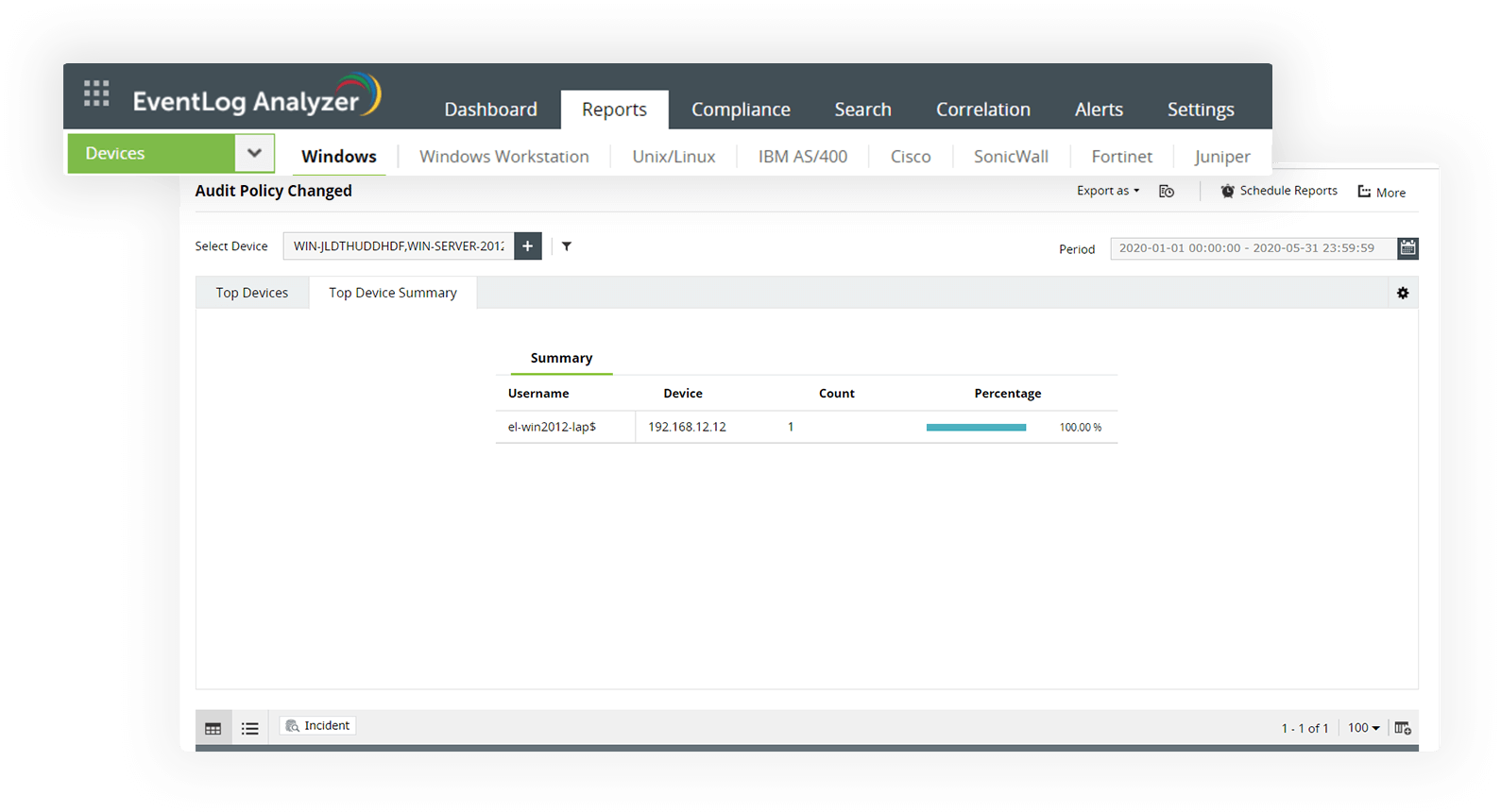
Track individual user actions and policy changes
SOX Section 302 (a)(5) expects organizations to implement procedures to audit internal controls and user management policies. EventLog Analyzer's individual user action report allows you to keep track of users' logons and logoffs, session activities, file or directory accesses, privileged user activities, and more. The solution conducts SOX compliance audits to notify users about security level changes to the audit policies.
Review user account and group changes in the network
Adhere to SOX Section 302 (a)(6) by monitoring and tracking all security configuration changes at the user and group levels as well as computer and user account management changes. Described here is the process for Unix systems, but this approaching is generally applicable to other systems. EventLog Analyzer sends instant alerts via email or SMS when critical changes are made to user and group accounts, such as adding or removing groups, user accounts, and members.
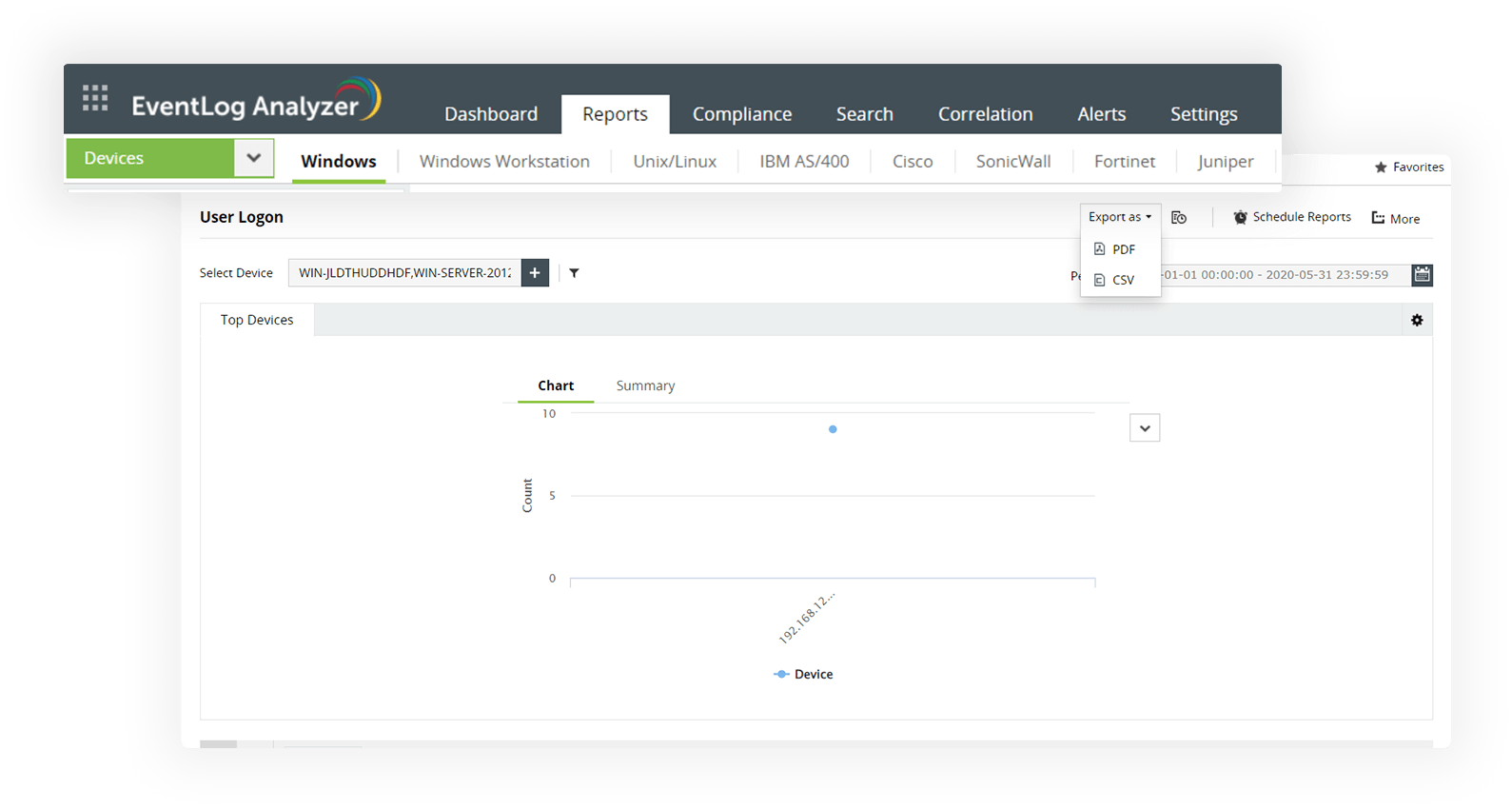
Generate out-of-the-box reports to easily demonstrate compliance
EventLog Analyzer is a comprehensive log management tool that monitors network logs at a granular level to facilitate out-of-the-box SOX compliance reporting. The solution triggers instant alerts when compliance violations are observed in the network. You can also handle occurrences efficiently with an incident management system that assigns tickets automatically to the relevant team and speeds up incident resolution.