Integrating Firewall Analyzer with Splunk for Centralized Log Analysis
Firewall Analyzer integrates with Splunk to forward critical firewall events, access logs, audit logs, and alerts to the Splunk platform in real time as syslogs. This integration allows Firewall Analyzer to act as a centralized log monitoring solution that collects, analyzes, and forwards security event data to external platforms, enabling efficient threat detection, incident response, compliance auditing, and improved network security visibility.
Configure Firewall Analyzer — Splunk Integration
This integration allows Firewall Analyzer to forward access logs and audit module entries to Splunk for improved security monitoring and correlation. Follow the steps below to set up and configure the integration.
Steps to Configure Firewall Analyzer’s Splunk Integration
- Go to Settings → General Settings → Integrations → Splunk
- Click Configure.
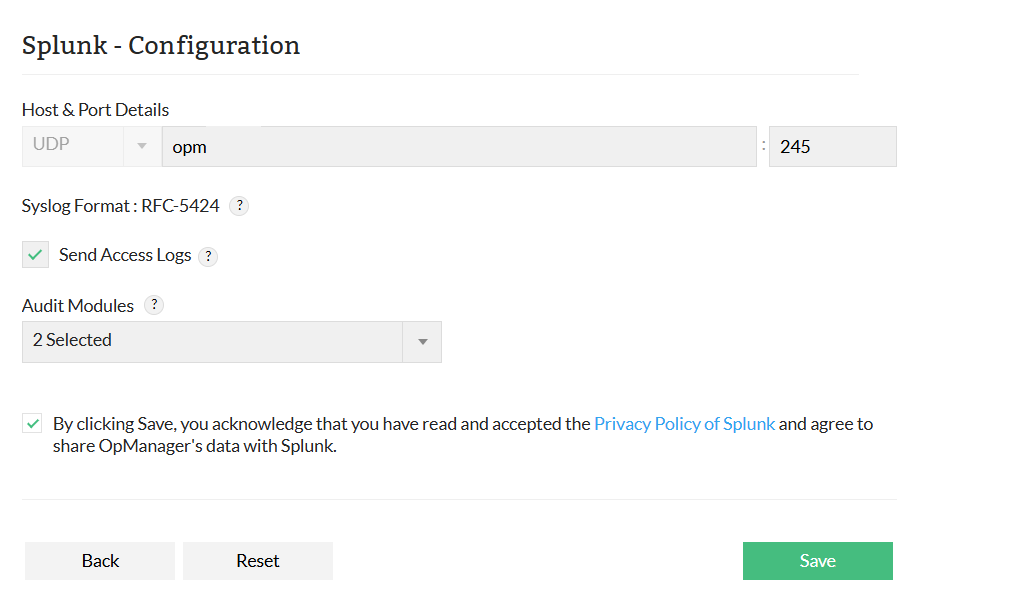
- Enter the Hostname / IP Address and Port Number of your Splunk server.
Note: The RFC-5424 syslog format is used to forward the logs.
- Select the types of logs you want to forward (for example: firewall logs, traffic logs, audit logs).
- Accept Splunk’s privacy policy.
- Click Save to complete the integration.
Note:
- Logs are forwarded using the UDP/syslog protocol.
- Ensure that your Splunk instance is configured to listen on the specified UDP port.
Configuring Notification Templates
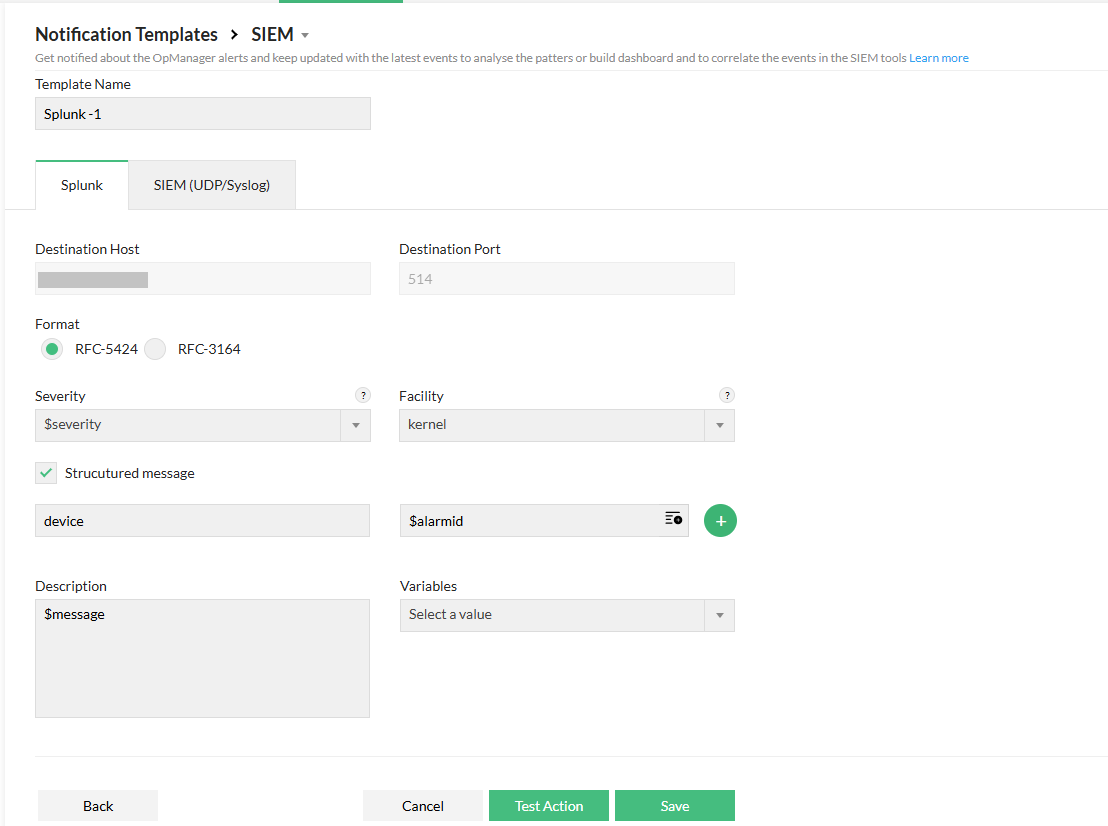
Firewall Analyzer allows you to define how alert messages are formatted and forwarded to Splunk when specific events occur.
- Go to Settings → Notifications → Notification Templates
- Click SIEM → Splunk.
- Enter the required parameters, including:
- Template Name
- Format
- Severity
- Facility
- Description
- Relevant Variables
- If you enable the Structured Message option, provide the appropriate key-value pairs to include in the syslog structure.
- To verify your configuration, click Test Action to send a sample syslog message to the configured host and port.
- Click Save.
Once configured, Firewall Analyzer continuously monitors firewall logs and alerts. When an event that matches a configured notification template is triggered, Firewall Analyzer formats the alert according to the template and forwards it to Splunk using the standard syslog protocol. Splunk can then ingest these logs for correlation, search, visualization, and advanced analysis.