Squid proxy log analysis
In today's data-driven world, network security is paramount. However, traditional firewalls often lack visibility into internal network activities. This is where Squid proxy logs come in. These logs contain a wealth of data that, when analyzed, provides the insights you need to make informed security decisions and bolster your network security posture.
Why analyze Squid proxy logs?
Squid proxy servers serve as critical components in managing and optimizing internet traffic within organizations. Squid proxy logs contain valuable information about user activities, web traffic patterns, and potential security threats. Analyzing Squid proxy logs is essential to gaining insights into network usage, detecting anomalies, and ensuring compliance with regulations.
Challenges of legacy Squid proxy log monitoring
Analyzing Squid proxy logs using legacy methods is labor-intensive and time-consuming.
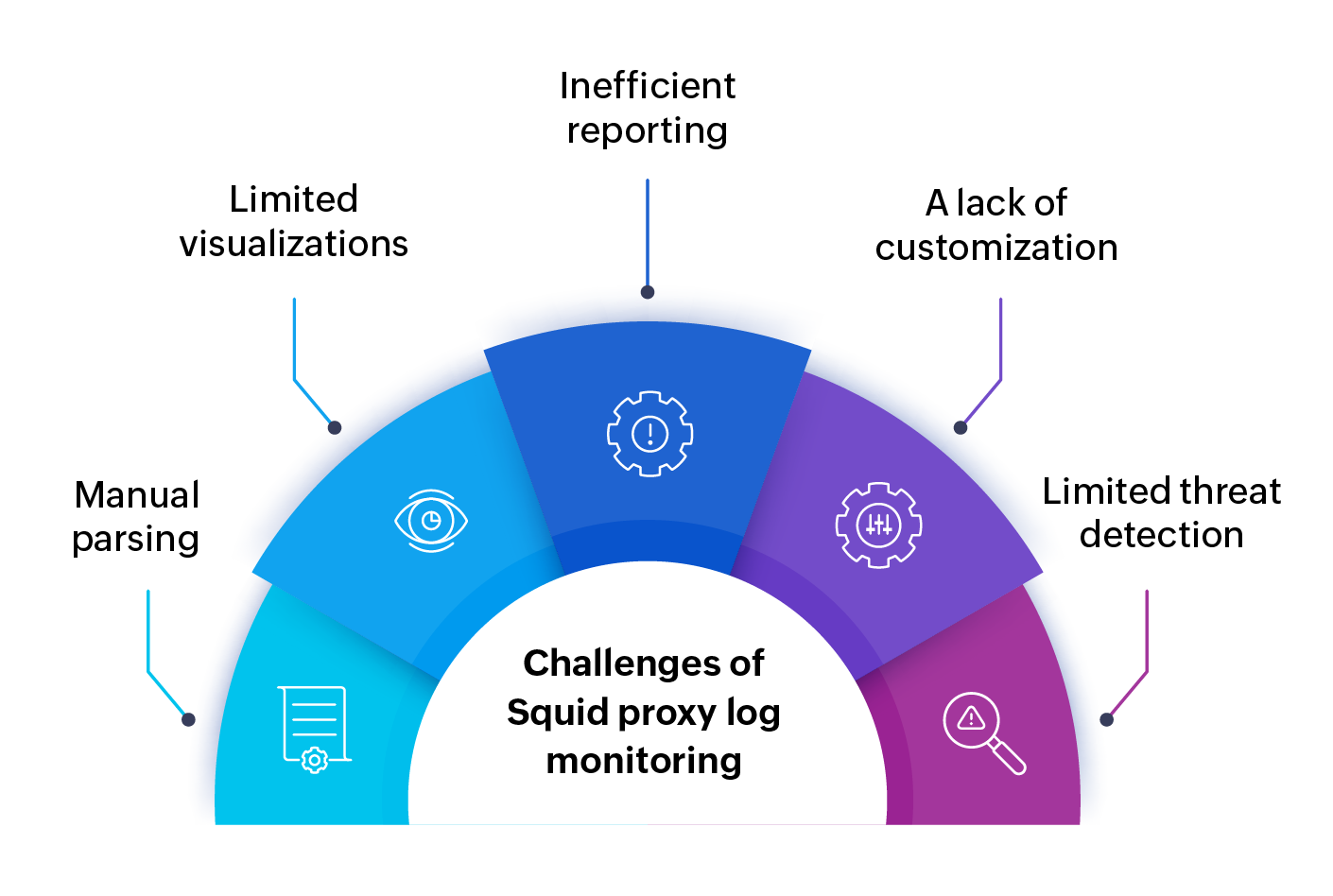
- Manual parsing and filtering: Extracting meaningful insights from complex, high-volume text logs is a time-consuming, error-prone process. Identifying specific user behavior, time frames, or types of traffic requires tedious manual filtering and searching.
- Limited context and visualizations: Raw log data lacks the context and visual representations needed to understand trends or identify security threats. Without tools for correlation with other security events and without visualization features like charts and graphs, pinpointing suspicious activities becomes extremely difficult.
- Inefficient reporting: Generating reports on user activities, bandwidth consumption, or security incidents without dedicated reporting features is a laborious task. Manually compiling data and creating reports is time-consuming and error-prone.
- A lack of customization: Tailoring analysis to your specific needs is difficult without dedicated tools. You can't easily focus on specific aspects of network traffic that are relevant to your organization, limiting the insights gained.
- Limited threat detection: Without automated analysis tools, spotting unusual activities or potential security threats within logs becomes a significant challenge. Manual analysis requires extensive expertise, and you may miss subtle indicators of malicious activities.
Key features of ManageEngine Firewall Analyzer for Squid proxy logs
While Squid logs provide valuable data, manually analyzing them is a tedious, error-prone task. ManageEngine Firewall Analyzer empowers you to better harness Squid logs with:
- Comprehensive log analysis: Parse, analyze, and visualize Squid proxy logs effortlessly with Firewall Analyzer's robust log analysis capabilities.
- Real-time monitoring: Stay ahead of security incidents with real-time monitoring of Squid proxy logs. Receive instant alerts for suspicious activities, policy violations, or unusual network behavior.
- Customizable reports: Generate customizable reports based on Squid proxy logs to gain actionable insights into web usage, user behavior, and security threats. Choose from a variety of predefined report templates or create your own to meet your specific requirements.
- Traffic analysis: Analyze web traffic patterns, accessed URLs, and bandwidth usage using Firewall Analyzer's traffic analysis tools. Identify potential security threats, bandwidth hogs, or unauthorized access attempts so you can implement proactive security measures.
- Policy enforcement: Enforce security policies and ensure compliance with regulations and standards by analyzing Squid proxy logs for policy violations. Identify and remediate security risks, enforce access controls, and maintain a secure network environment.
Advantages of using Firewall Analyzer for Squid proxy logs
With Firewall Analyzer, you can:
- Enhance security: Gain deeper insights into network traffic and user activities to detect and mitigate security threats effectively.
- Improve compliance: Generate compliance reports and enforce security policies to ensure adherence to regulations such as the GDPR, HIPAA, and the PCI DSS.
- Maximize efficiency: Analyze bandwidth utilization and application traffic patterns to boost network efficiency, elevate user satisfaction, and limit operational expenditures.
- Monitor threats proactively: Stay proactive with real-time monitoring and alerts for suspicious activities, ensuring timeliness in responding to and mitigating security incidents.
Firewall Analyzer is an all-in-one solution for analyzing Squid proxy logs and strengthening your network security defenses. With its comprehensive features, customizable reports, and real-time monitoring capabilities, Firewall Analyzer empowers you to take control of your network security. Sign up for a free demo or download the free, 30-day trial to experience the power of Squid proxy log analysis with Firewall Analyzer.
Featured links
Firewall Rule Management
Manage your firewall rules for optimum performance. Anomaly free, properly ordered rules make your firewall secured. Audit the firewall security and manage the rule/config changes to strengthen the security.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Log Management
Unlock the wealth of network security information hidden in the firewall logs. Analyze the logs to find the security threats faced by the network. Also, get the Internet traffic pattern for capacity planning.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Thank you for your feedback!