Securing USB Devices | User Configuration
Table of Contents
What is secure USB configuration?
Users and computers can use the Secure USB setup to prevent unauthorized users or malicious devices from accessing any endpoints in the organization that stores sensitive data. No matter what type of computer a person uses, this setting is appropriate for them. In order to avoid hazards posed by unknown devices and booby-trapped USB drives that might damage your network and corrupt user accounts, you must configure Secure USB. Blocking and unblocking devices enhances USB security and fosters a secure environment for the organization.
How to enable secure USB configuration?
- In Endpoint Central Console, navigate to Configurations tab --> Add Configurations --> Configurations--> Windows.
- Select Secure USB configuration and choose User.
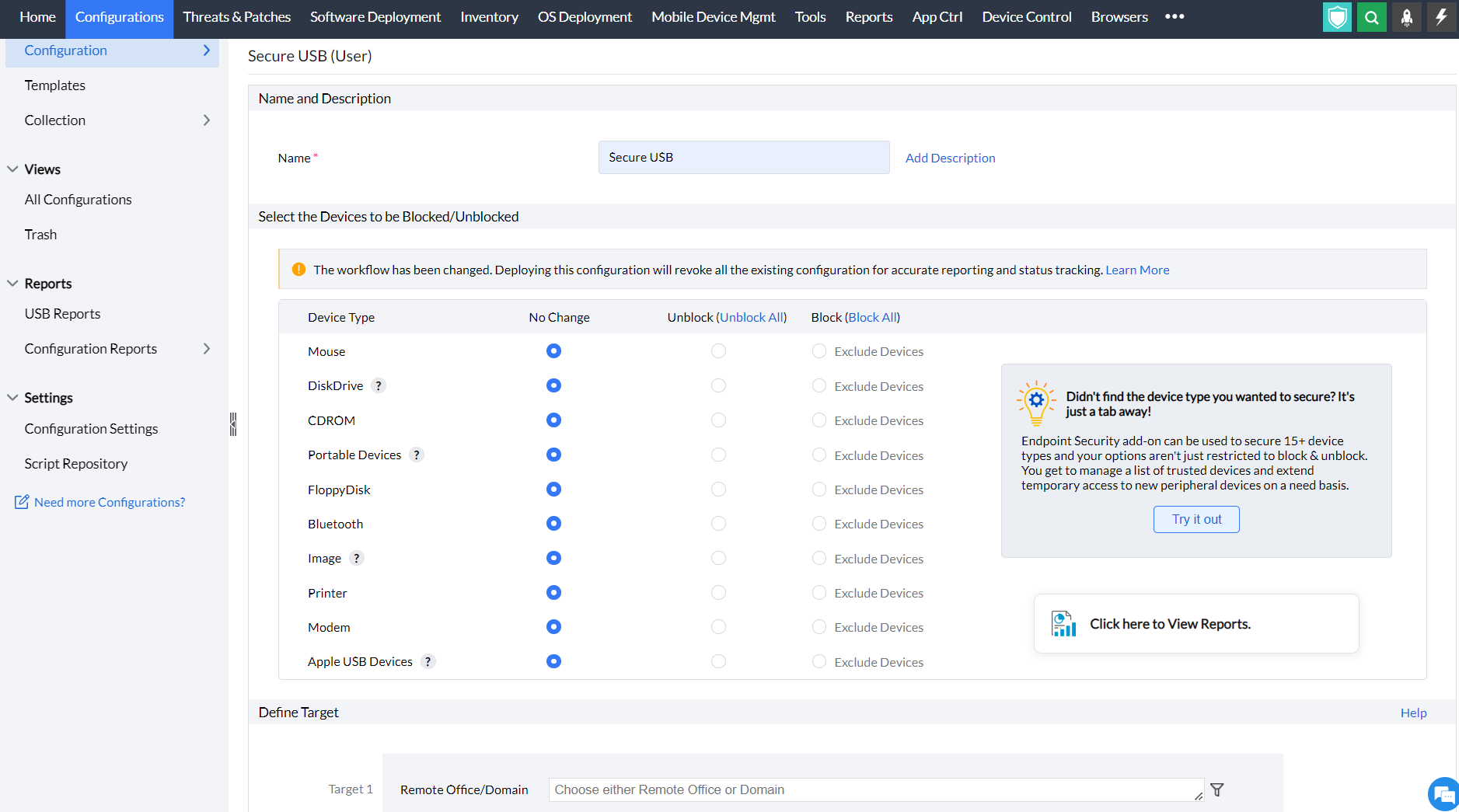
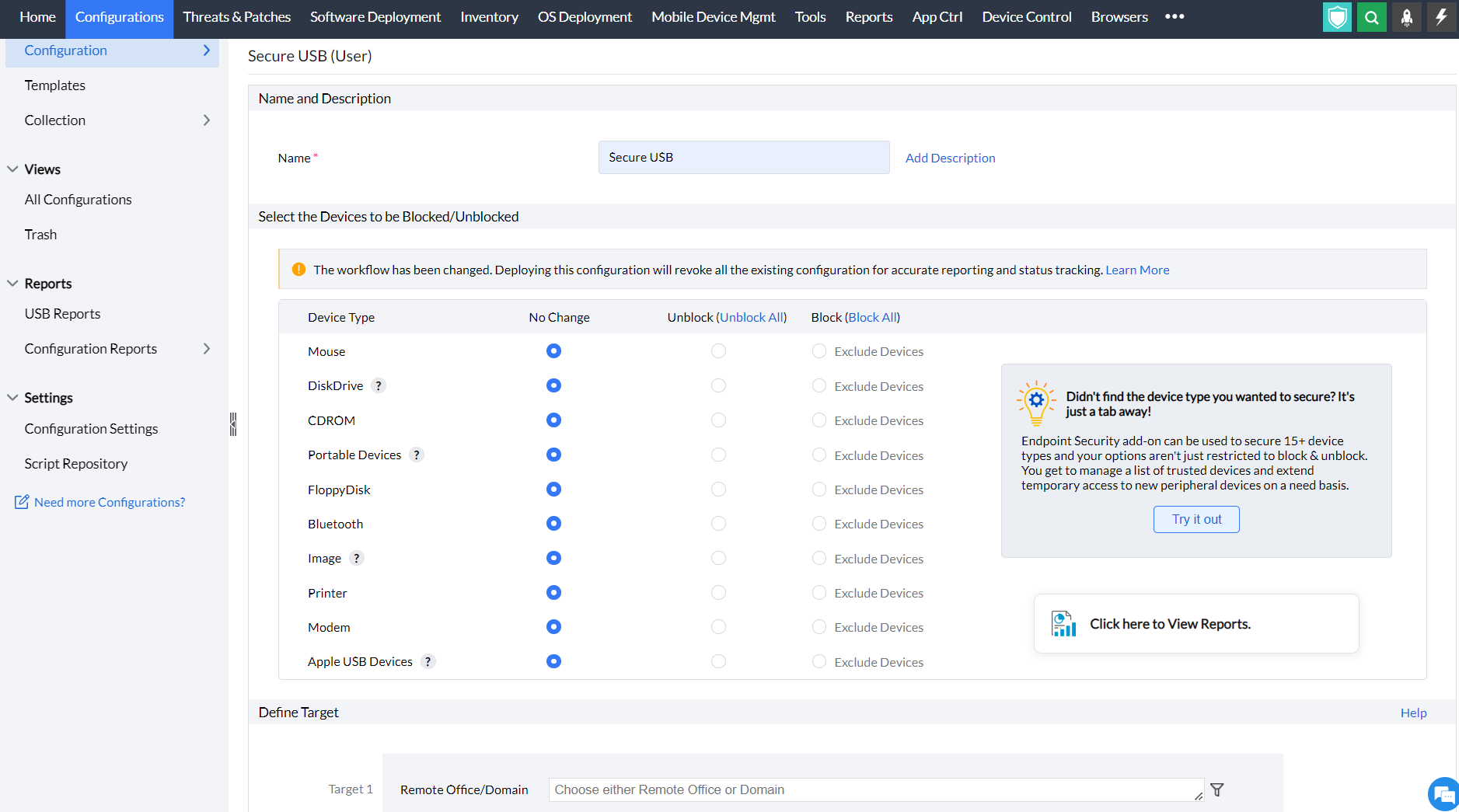
- Specify the Name and Description for the configuration.
- In the Select the Devices to be blocked/unblocked criteria, select the devices that you want to block and unblock. The devices that can be blocked/unblocked using this configuration are as follows:
- Mouse
- Disk drives (for example: USB drives and external hard-disk drives)
- CD ROMs
- Portable devices (for example: mobile phones, digital cameras and portable media players)
- Floppy disks
- Bluetooth devices
- Images (for example: USB cameras and scanners)
- Printers
- Modems
- Apple USB devices(for example: iPhone, iPad and iPod touch)
- You can also exclude devices from being blocked by clicking Exclude Devices. Devices to be excluded can be added to or selected from the existing list. New devices can be defined by their Device Instance ID or Vendor ID. To exclude all instances of a particular vendor, such as SanDisk or Kingston, specify the corresponding Vendor ID or Device Instance ID.

Devices to be excluded can also be selected from the existing list of devices.

Note: The USB devices will be listed in the Select from List only when the device is connected to the machine which is in the network.
- Define the Target.
- Specify retry options if required and deploy the configuration.
- You can also enable notifications to receive emails based on the specified frequency.
- Click on the Deploy button to deploy the configuration in all the target machines.
- To save the configuration as draft, click Save as.
You have successfully learnt to enable the Secure USB configuration in Windows machines.
Note: Refer to this page to learn more about configuring settings for USB Auditing
For more information about device control, check this page.