- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
The modern day IT security landscape is so volatile that security teams are often grappling to keep up. Using a legacy intrusion detection system (IDS), which is signature-based, organizations can detect and thwart threats with patterns similar to already known threats.
However, these systems struggle to spot new types of threats with never-before-seen patterns. To bridge this gap, organizations should use a security tool that can integrate with a threat repository that is constantly updated with all the recent incidents spotted across the globe.
Empowering EventLog Analyzer by integrating with Webroot's threat feed
EventLog Analyzer, a log management tool, has several features that make it a potent security tool. One is its correlation engine, able to preempt network security threats and integrate with Webroot's threat database.
Despite the availability of open source threat feeds, third-party ones like Webroot's contain a more refined list of threats as they constantly receive updates from endpoint software around the globe. Each malicious IP, URL, or domain updated in the feed is assigned a reputation score that denotes how severe the potential threat caused by it could be.
EventLog Analyzer leverages the information in threat feeds by correlating it with the log information collected. This ensures that administrators are alerted when a malicious IP address or URL in the feed initiates a connection with their network.
Analyzing threats in-depth using EventLog Analyzer
EventLog Analyzer has a dedicated tab that lists all malicious IPs, URLs, and domains that have been detected. If an administrator is suspicious about a particular malicious source and wants to investigate it further, EventLog Analyzer provides more context by fetching crucial data from the feed such as the first and the last time it was detected, the number of times it was detected, and its reputation score.
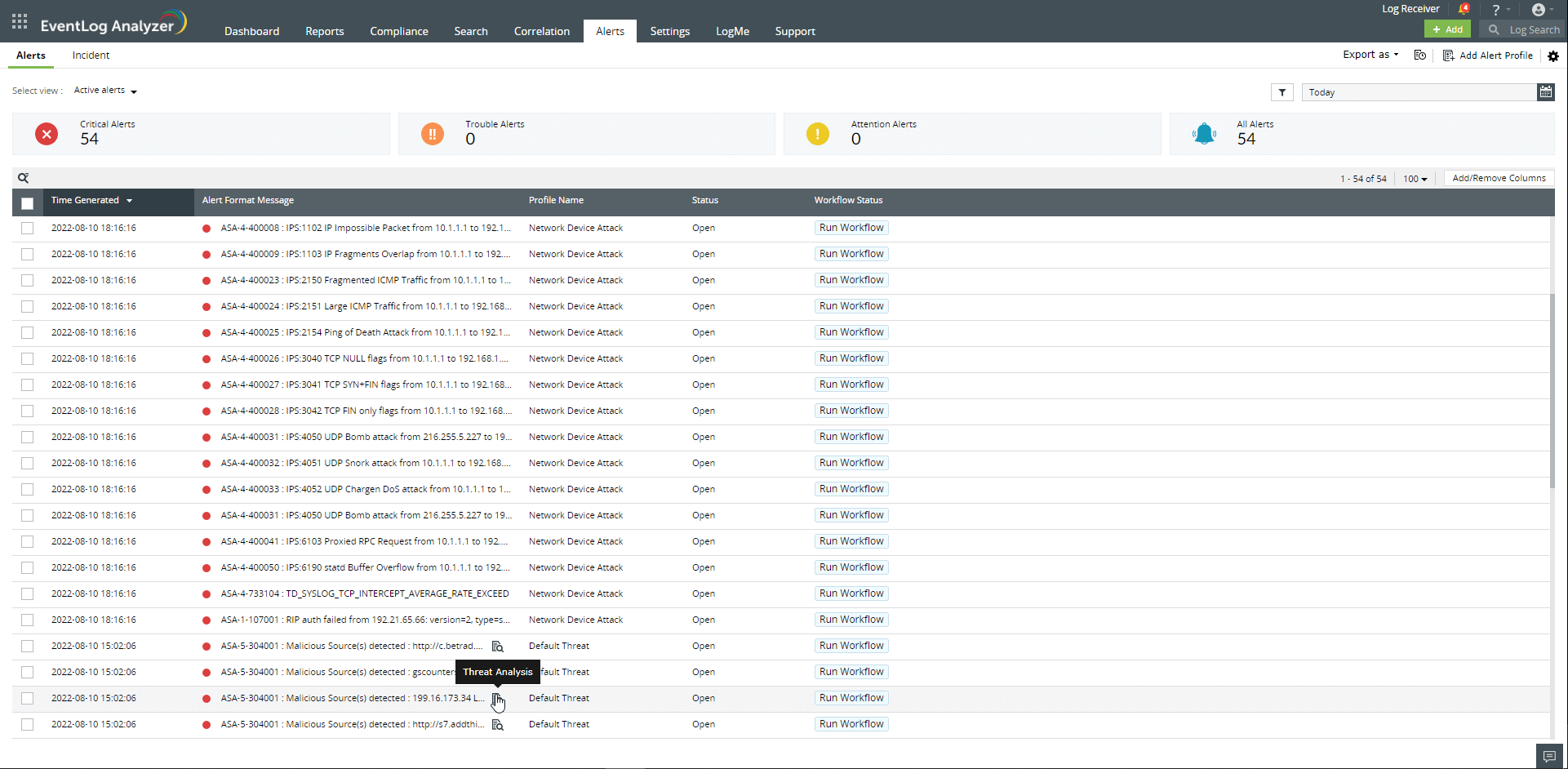
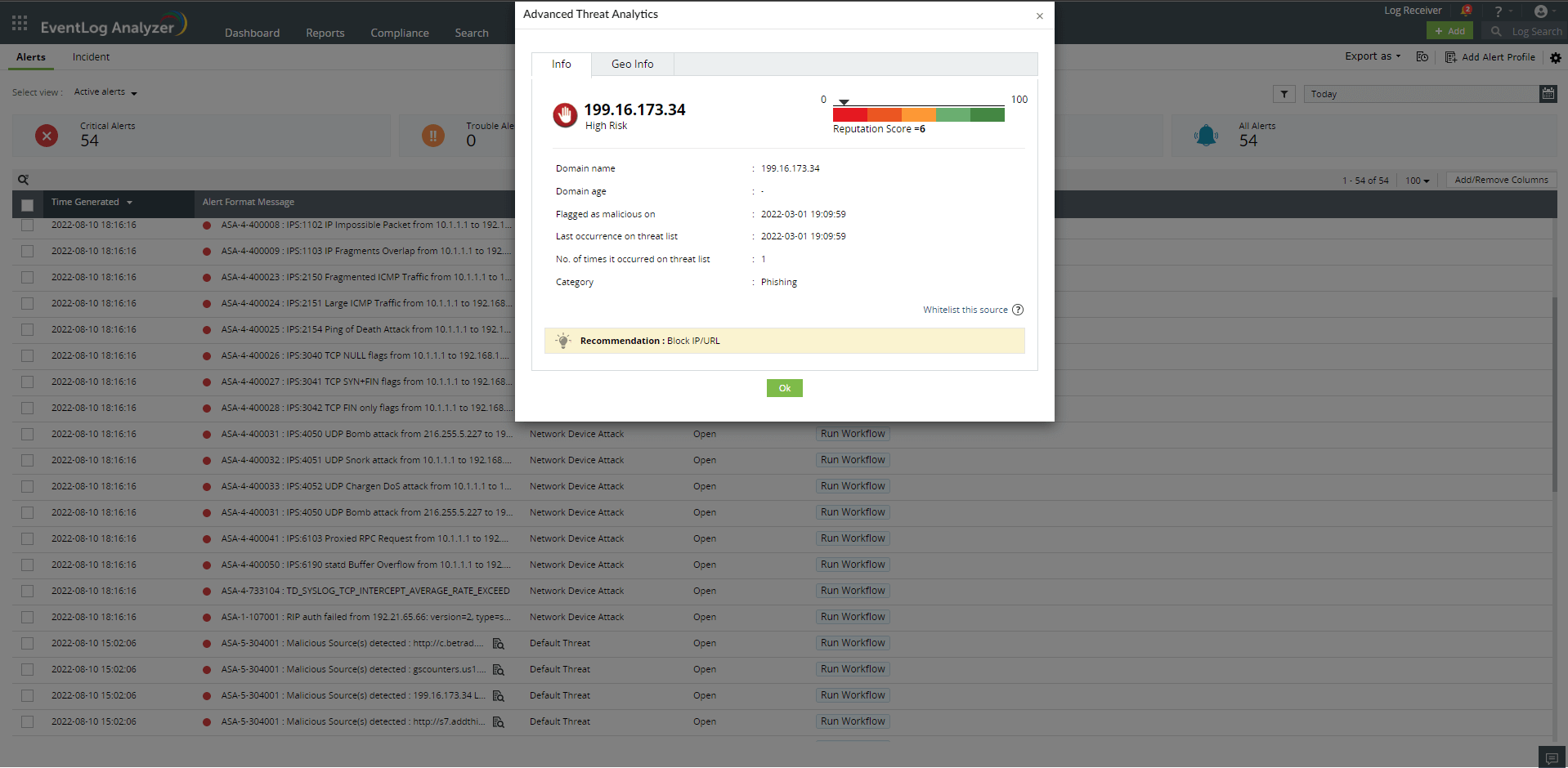
It also provides a suggestion on how to deal with the malicious source. With all this information in hand, administrators can prioritize sources based on their severity levels, and decide on the next course of action.
By combining the wealth of information from the collected logs and the database of global threat feeds, EventLog Analyzer gives security teams all the information they need to take preemptive action against network security threats.
Other features
Syslog server management
EventLog Analyzer collects and analyzes log data from Linux/Unix servers to provide on-the-fly reports that help detecting suspicious behaviors, anomalous syslog activities, and more.
Application log analysis
Analyze application log from IIS and Apache web servers, Oracle & MS SQL databases, DHCP Windows and Linux applications and more. Mitigate application security attacks with reports & real-time alerts.
Active Directory log monitoring
Monitor all types of log data from Active Directory infrastructure. Track failure incidents in real-time and build custom reports to monitor specific Active Directory events of your interest.
Privileged user monitoring
Monitor and track privileged user activities to meet PUMA requirements. Get out-of-the-box reports on critical activities such as logon failures, reason for logon failure, and more.
Print server Management
Monitor and audit print server with detailed reports on documents printed, attempts to print documents without proper permission, failed print jobs and their causes, and more
IT compliance management
Comply with the stringent requirements of regulatory mandates viz., PCI DSS, FISMA, HIPAA, and more with predefined reports & alerts. Customize existing reports or build new reports to meet internal security needs.
Need Features? Tell Us
If you want to see additional features implemented in EventLog Analyzer, we would love to hear. Click here to continue












