
Firewalls, along with IDS/IPS, are your first line of defense against malicious attacks on your network. Regardless of which type of perimeter security devices are being used, monitoring these devices are critical to ensure that they function smoothly and you are alerted in advance of any suspicious user activities, network anomalies, or device mis-configuration.
Firewall Security Management involves monitoring:
Most security solutions offers one of the two. Ignoring one aspect of the security monitoring will leave your network vulnerable. Firewall Analyzer is the only vendor agnostic monitoring solution which can analyze both logs and configurations of network security devices, as described below.
Monitor Security Logs
Firewall Analyzer provides Security Log Management capabilities to:
- Get the details about the denied accesses (including DoS attacks)
- Identify the VIRUS senders, targets, generators and files
- Who is attacking what resource in your network
- Get to know the who is spamming your network
- Monitor attempts to access blocked URLs
- Monitor firewall administrator activities
Firewall Analyzer provides elaborate reports on the security log management. They are:
- Security reports
- Virus reports
- Attack reports
- Spam reports
- URL reports
- Admin reports
Security Log Management Reports
Security Reports
The security reports give more insight into access denials and help IT department to prevent such attacks on the network in future. Reports include information on denied hosts, destiantions, protocols, and security events generated.
Virus Reports
Virus reports give in-depth information on virus attacks, hosts infected, severity of the attack, subtype, and more. With drillable reports, complete details of the virus related raw log is available. The raw log messages make troubleshooting and problem resolution faster and more efficient.
Attack Reports
Attack reports give detailed information on possible network attacks, peer-to-peer attacks, etc. Reports include information on attackers, targets, protocols used for the attack, etc. These reports gives the IT administrators with insight to counter such attacks.
Spam Reports
Spam reports give detailed information on spam activity in the netwrok. Reports include information on spam generators, receivers, and rules allowing spam. These reports give more insight into possible spam threats, and help IT department control the spam activity across the network.
URL Reports
URL reports give detailed information about the denied, allowed, URLs and URL categories. Reports can be drilled down to get accessed URLs, sources, destinations with number of hits to that URL and the access attempts to the denied URLs. You can identify potential users trying to access denied URLs and take corrective actions.
Admin Reports
Admin Reports provide detailed information on firewall administrator activities such as successful logons, successful logoffs, failed logons and the commands executed by the firewall users like security administrators, network administrators, etc. With this, the IT manager can control the admin access to the firewall devices and there by prevent intentional or unintentional device misconfiguration.
Monitor Firewall Configurations
Firewall Analyzer provides Firewall Security Management capabilities to:
- Audit the security of the firewall devices
- Analyze the configuration of the firewall devices to assess the security vulnerability of the device
- Track the configuration changes made on the firewall devices
- Monitor the effectiveness of the rules/policies/ACLs of the firewall devices
- Monitor the firewall user activities
- Diagnose the firewall connections in real-time
Firewall Analyzer provides elaborate reports on the firewall security and compliance. They are:
- Security Audit report
- Configuration Analysis report
- Configuration Change Management report
- Unused and Used Rules report
- Firewall Live Connection Diagnosis
Firewall Security Management Reports
Security Audit report
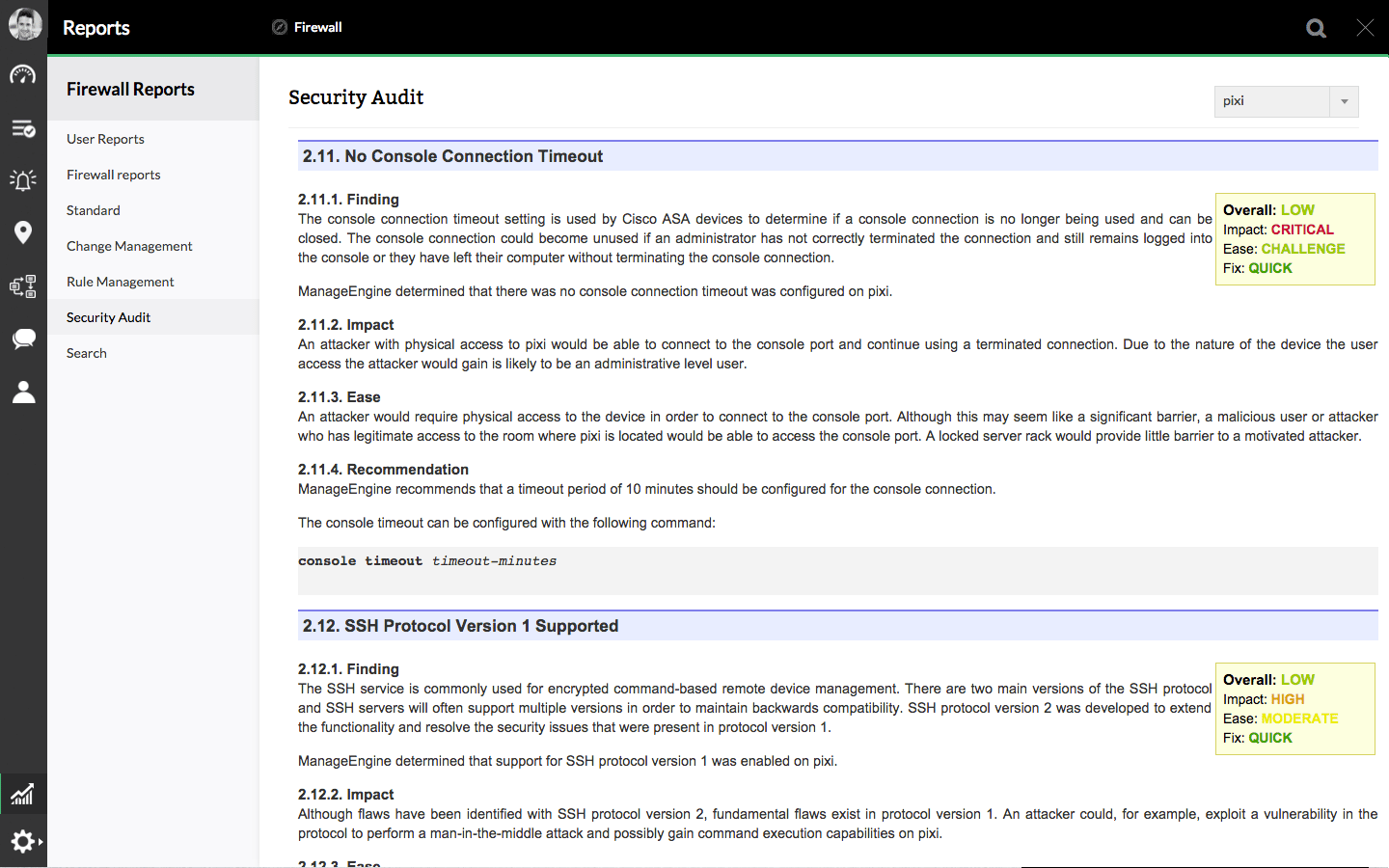
Firewall Analyzer audits the firewall security periodically and generates the firewall security audit report. The screen shot of the sample report is given below:
Configuration Analysis report
The complete configuration of the firewall device is listed in this report. This includes the firewall policies or ACLs or firewall rules.
Change Management report
Firewall Analyzer monitors the firewall configuration changes in real-time. It can trigger alerts for any change done. It generates elaborate change management report. The report addresses the question like who made the change, what was the change, and when was it made.
Unused and Used Rules report
Unused rules indicate that the rules are redundant and are not being used to the control or monitor the traffic through the firewall. Either the rules should tweaked to make the rule effective or removed entirely. This will help you manage your firewall policies/rules and strengthen the overall security of your network. In the case of used rules, if a particular rule is overused, that may be an indication that the rule is not so effective and may allow exploits in to the network. Those rules should be carefully analyzed and tweaked to tighten the security. Firewall Analyzer presents exhaustive reports about unused and used rules.
Live Diagnosis of Firewall Connections
Firewall Analyzer helps to identify current live connections / sessions (specific to IP address, range of IP addresses, Port / Protocol) established with the firewall device through it's Diagnose Connections feature. This will help firewall administrators to track the connections and ensure that the device is accessed properly in their network.
Customers
"Credit Union of Denver has been using ManageEngine Firewall Analyzer for more than four years for our external threat monitoring and firewall change management. Firewall Analyzer can rapidly be scaled to meet our dynamic business needs"
-Benjamin Shumaker, Vice President of IT/ISO, Credit Union of Denver
Firewall Customers
