ManageEngine OpUtils offers a reliable port scanner tool that enables you to effectively scan your network switch ports and the system's TCP and UDP ports. With ports being the enablers of network communication, it is important that you keep track of how your ports are being utilized. This has made port scanners online and offline, a go-to tool for network admins to scan port, monitor them, and secure their IT infrastructure. Port scanning not only helps you understand port utilization but also enables you to secure your network from unauthorized access and enhance capacity planning. A port scanner acts as a detective, allowing network administrators to explore the network landscape to identify potential vulnerabilities.
On this page, we will be looking into,
- The need for a port scanner
- Scanning ports: A look into OpUtils' sample port scan results
- OpUtils' port scan reports
- Securing network access with the integrated Rogue Detection module
- How does OpUtils simplify port scanning in complex IT infrastructures?
The need for a port scanner
Network admins rely on port scanners to scan and inspect their network endpoints, which includes switch ports and system ports. These endpoints allow various network components and users to access and communicate with your network. Scanning ports helps you enhance security by ensuring your network hosts are configured to run only approved network services, and block ports from allowing any unauthorized traffic. A real-time port scanner continuously monitors open and closed ports, allowing admins to promptly identify and respond to suspicious activities. Hence, investing in the best port scanner is essential to fortify network security, identify vulnerabilities, and proactively safeguard against potential cyber threats.
Without an effective network port scanner solution in place, your network can become vulnerable to the following:
Unauthorized network access
Network entities can easily scan and access services running in your network through open ports. Ports that remain continually open present themselves as a potential network vulnerability. An intruder can access an open port to wreak havoc in the normal flow of network operations. Hence, deploying an advanced port scanner can swiftly analyze your network's security posture by identifying open ports and potential malicious devices. You can use a port scanner for Windows and Linux to effectively monitor and secure your network infrastructure.
Data leakage
Since network components communicate using data flow through ports, it is important to closely monitor your network ports using port scanning solutions. Unauthorized and rogue agents accessing your network ports can lead to data leakage and compromise overall network security. Port scanning helps you detect connections to your network and secure the communications flowing in the network. With port scanner tool, you can conduct comprehensive scans to ensure robust network defense by detecting and addressing any exposed ports. Using an IP port scanner, you can specifically scan IP addresses and their associated ports to identify vulnerabilities and strengthen your network security posture.
Hindered network availability
Facilitating message transfer for any component willing to communicate with your network, ports are the gateway to your network. Tracking and managing switch port utilization helps you ensure that your network has enough available ports for any new devices attempting to connect. The services running in your system ports need to be constantly checked to ensure that only authorized services are running, since when one service is running on a port, no other service can utilize the port. These factors make it important to ensure that there are enough ports available for authorized applications to communicate with your network.
Enhanced network visibility with OpUtils Port Scanner
- Quickly identify open ports and vulnerabilities.
- Scan and analyze TCP/UDP ports for security risks.
- Generate detailed reports for network audits.
Scanning ports with OpUtils: A look into OpUtils' sample port scan results
OpUtils' effective port scanning capability enables full-fledged network scanning to help you detect open ports in your network and identify the services running on them. With switch port scanning, OpUtils helps you gain in-depth insights into how your network switch ports are connected and the end device accessing each of them. To better understand how you as a network admin can take advantage of this capability, let's have a look into one of OpUtils sample port scan results.
Initiating a port scan in OpUtils
For system ports: Network admins can trigger an open port scan using the Port Scanner tool available under OpUtils' comprehensive network toolset. Using this tool, network admins can scan ports associated to a single IP address or range of IP addresses by specifying the starting and ending IP. Once the IP details and port range requirement is specified, OpUtils starts scanning all the ports within the specified range. An open port scanner is crucial for detecting open ports and addressing potential vulnerabilities to strengthen network security.
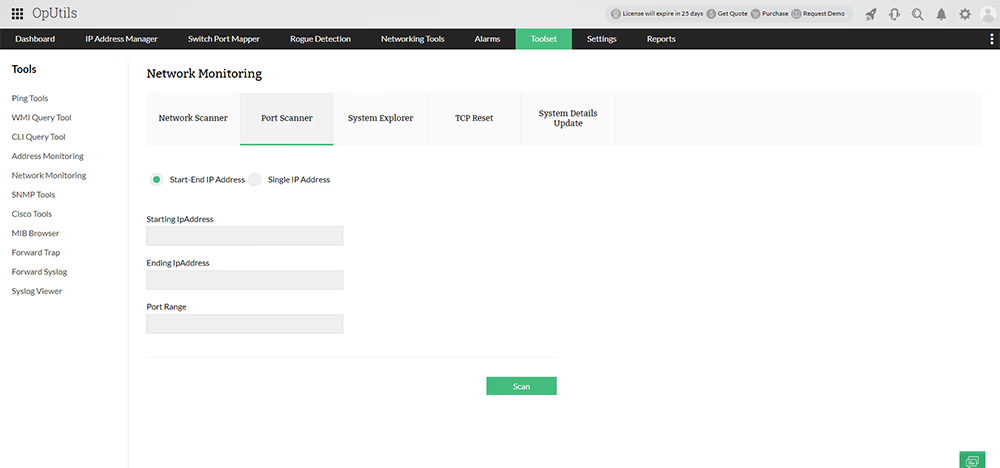
For switch ports: OpUtils offers flexible switch port discovery options, enabling you to get started with monitoring your entire network's switch ports within minutes. You can choose to add your switches for port scanning through network discovery, importing from a CSV file, or by specifying the switch addresses for switch discovery.
Open port scanner results
Upon running an open port scan, OpUtils displays the list of scanned ports, their response time and status, and the service currently running in the port. This helps network admins get insights into all the services currently accessing their network ports. Admins can validate this list with the authorized services and block all any malicious services communicating with their systems. Not just that, with the list of all open ports in the network, network admins can also choose to close these open ports to enhance network security and reduce the pathways of possible malicious network access.
Some of the common port services scanned by OpUtils’ port scanning software are,
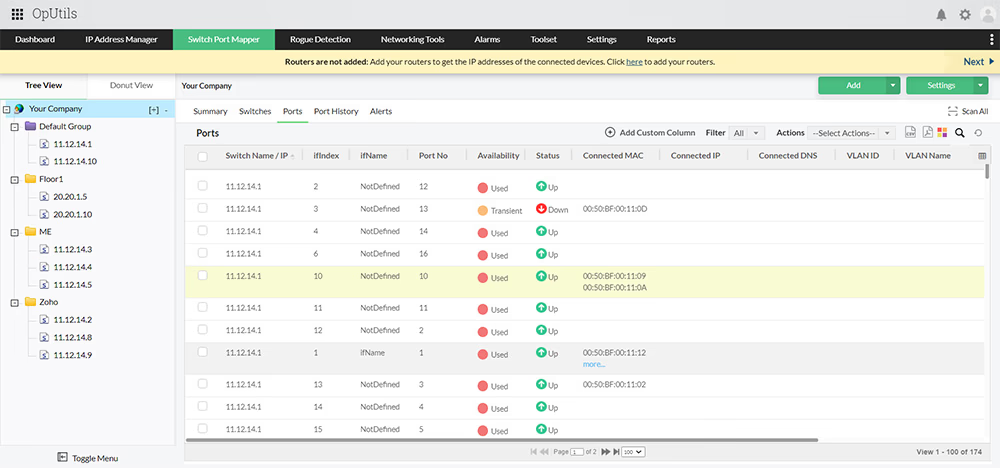
Switch port scanning and insights into network communication
OpUtils' switch port scanner enables network admins to scan and map network switches to ports and their connected devices. Scanning switch ports with this end-to-end port scanning tool gives network admins real-time insights into the following:
- Switch port mapping: OpUtils' port scanning tool displays a list of managed switch ports and all their connected ports. Network admins can view details such as the switch name, interface index, interface name, port number, and port status. Network admins can also choose to visualize the port scan results using the Port View capability available with OpUtils.
- Port connectivity details: Using the switch port scan results, network admins can inspect the network connection aspects of the scanned switch port. This includes details such as whether the port is stacked, connected to multiple devices, or connected to a device with a virtual IP.
- Connected device details: With the switch port scanner's tight integration with OpUtils' IP Address Manager module, network admins can easily view the IP details of the end devices connected to the switch ports. From the switch port scan results, network admins can view details of each connected device, such as its IP address, DNS name, device type, VLAN ID, and VLAN ID.
OpUtils' port scan reports
OpUtils' port scanning solution generates granular network reports on the managed switch ports. The ability to track the port usage over time not only enables network admins to predict and avoid issues such as resource exhaustion, but also enables them to enhance capacity planning, thereby reducing hardware procurement costs.
With OpUtils, you can generate diverse reports specific to switch ports, allowing you to understand how, and by who, your switch port resources are being used. It also provides reports on the scanned ports, offering you insights into different aspects of the ports, such as which devices have connected and how they were associated with the switch ports. It also automatically logs the historical port operations in your network under Port History.
Some of the port scanning reports in OpUtils switch port mapper include:
- Switch ports by interface speed
- Switch Ports by interface type
- Devices with Virtual IP
- Stacked Port Details
- Administratively Disabled Ports
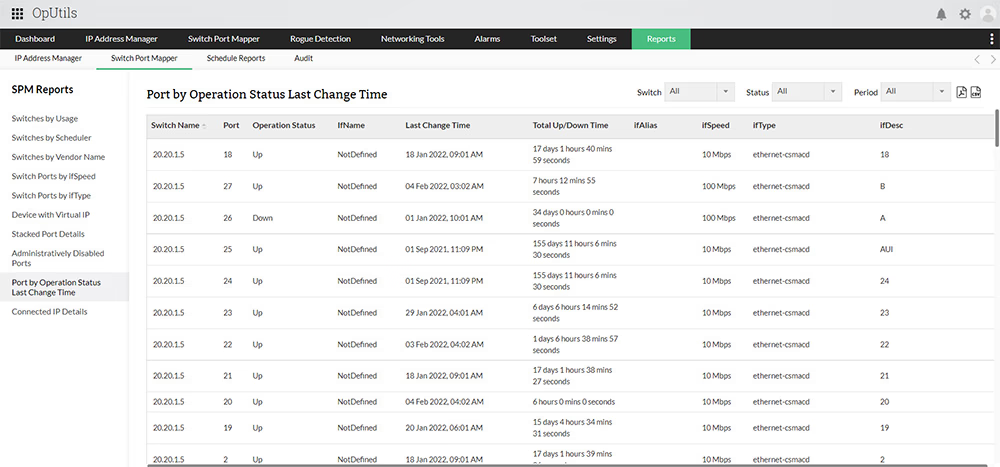
Port scanner report scheduling: You can configure OpUtils to automatically generate these reports at specified intervals using the report scheduling option. You can download the generated reports directly from the console or have the reports sent to you via email.
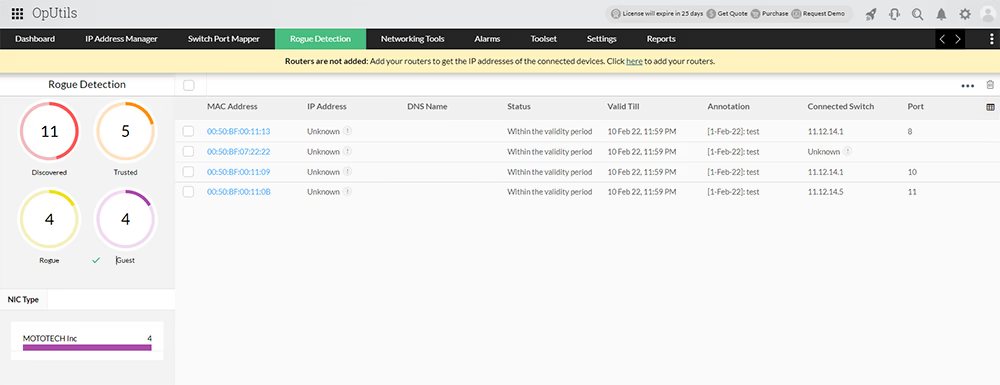
Securing network access with the port scanner's integrated Rogue Detection module
As cyber threats continue to grow, having a port scan solution is essential to protecting network infrastructure. Staying in the know of who is using your network resources is important to avoid running into network issues such as resource exhaustion. As said earlier, exploitation of open ports can lead to service outage, hindering any authorized devices trying to use your ports. This makes it crucial to keep tabs on all the newly connecting network devices, ensuring your ports are only being used by authorized network components.
OpUtils simplifies this process with its tightly integrated Rogue Detection module that scans your managed IPs, routers, and switch ports to detect newly connecting network devices. Upon identifying the list of devices, OpUtils allows you to block or unblock ports that might be facilitating unauthorized network services. This helps you secure your network resources from being used by intruders or rogue agents.
How does OpUtils simplify port scanning in complex IT infrastructures?
When deploying a port scanner, it is important to identify an effective port scanning tool that enables you to efficiently avoid the risk vector of malicious agents exploiting your network. An ideal Port Scanner software should provide you with real-time and accurate results, offer customizable scanning options and deliver comprehensive reports. While deploying Port Scanner for Windows and Linux OS, it is crucial to identify an effective tool that seamlessly operates across both platforms, ensuring comprehensive network security by efficiently avoiding the risk vector of malicious agents exploiting vulnerabilities. OpUtils' port scanner offers various features that enable you to test all ports, which is vital for achieving in-depth security verification. As a complete port scanning solution, OpUtils enables you to gain a holistic view of your network ports and its associated devices. Being an intuitive, code-free port scanner with powerful scanning capabilities, OpUtils enables:
- Simplified discovery: Get started with the tool in minutes. With quick network discovery, OpUtils offers end-to-end coverage and visibility into your network switch ports.
- Centralized inventory: Track all your switch ports right from your web console. With OpUtils' centralized switch port inventory, you'll enjoy simplified grouping, tracking, and mapping of switch ports.
- Real-time utilization metrics: Remotely monitor switch port statuses and other utilization metrics. Get in-depth insights with OpUtils' comprehensive switch snapshots.
- Staying ahead of issues: Receive instantaneous alerts whenever a problem occurs with OpUtilis' one-click enabled alert scenarios.
- An expanded scope of port scanning: Go beyond simple port scanning with OpUtils' built-in network tool set that contains more than 30 free networking tools.
- Automated and periodic port scans: Save time with OpUtils' scan scheduling option. Set up appropriate scan schedules for your switch ports, with scans happening on an hourly, daily, weekly, or monthly basis.
Getting started with OpUtils’ port scanning capabilities
OpUtils' scanning port feature allows you to efficiently probe for open ports across your network infrastructure. OpUtils offers you more than just a best port scanner. It is in-depth IP address and switch port management software that provides various capabilities such as rogue device detection, wake on LAN, and more. OpUtils also has an efficient IP scanner which might interest you.
If you are new to OpUtils, schedule a live demo with one of our product experts, who will uncover for you all the advanced port scanning and switch port management features OpUtils has to offer.
Want to try OpUtils' port scanner tools firsthand and see how it could work for your network? Download a 30-day, free trial and get started with OpUtils in less than an hour!
More on port scanner
What are network ports?
+Is port scanning illegal?
+What is the difference between a sniffer and a port scanner?
+What is a port scanner?
+What is port scanning?
+What does a port scanner do?
+Why is port scanner important?
+What are the types of network scans used in port scanning?
+
The effortless approach to port scanning: OpUtils' advanced port scanner tool
Download a free, 30-day trial!Feature pages
More on OpUtils' port scanner tool
Don't just take our word for it.
Hear directly from our customers as they share their thoughts on our reliable port scanner.
- The Capterra logo is a service mark of Gartner® Inc. and/or its affiliates and is used herein with permission. All rights reserved.
- Gartner Digital Markets reviews constitute the subjective opinions of individual end users based on their own experiences and do not represent the views of Gartner or its affiliates.