Switch ports are fundamental components of your IT that enable network communication. These wired hardware devices are responsible for connecting and allowing data transfer between different devices and parts of your network that are connected to their ports. As they playing a critical role in ensuring network connectivity and availability, it is important that network admins have a clear understanding, mapping, and visibility into their network switch ports.
"Access ports vs. trunk ports" is a discussion that needs to be clearly understood and evaluated to leverage effective switch port deployment and overcome several switch port management challenges in your network. On this page, we'll explain the key differences between access ports and trunk ports including:
Access ports are network switch ports that are configured to carry network traffic for a specific virtual LAN (VLAN) only. These switch ports are connected with devices such as end user devices within a specified VLAN. This ensures that traffic from these components within the configured VLAN does not interrupt traffic from other VLANs. This in turn isolates the VLAN components from other network VLANs.
Access ports facilitate communication between components using untagged data packets. Since the VLAN for a particular access port is pre-assigned, the access port does not rely on VLAN identifying 802.1Q or Inter-Switch Link (ISL) tags.
When traffic enters the access port, the switch adds an VLAN tag to the processed data frames to identify which VLAN the traffic belong to.
For instance, when an end device such as a user computer connected to the access port sends a untagged frame through the access port, the switch processes the frames to attach a VLAN tag to the frame. The VLAN tag identifies the appropriate VLAN the data frames are to be forwarded to.
These type of switch ports are configured to carry traffic and enable network communication between different VLANs. By default, trunk ports allow traffic from all VLANs in the network. However, network admins can prune or remove the required VLANs to restrict their traffic through the trunk ports. Trunk ports are often used to connect different switch ports in a hierarchical network design. They can also be used to connect switch ports to other network components such as DHCP servers and firewalls.
Trunk ports facilitate communication between different network components using tagged data frames. Relying on protocols such as IEEE 802.1Q and ISL, trunk ports tag each packet with a VLAN ID. The switch ports processing these data frames use the VLAN ID to forward the packet to its intended destination VLAN.
Since trunk ports process tagged data frames only, it is important to ensure that two neighboring trunk ports are configured the same. That is, if a trunk port is configured to allow traffic from VLAN A to VLAN B, the neighboring trunk port should also be configured to allow traffic from VLAN A to VLAN B.
For instance, trunk ports can be used to connect a core switch to multiple distribution switches, which are then connected to different access switches. This enables better scalability and increased networking efficiency.
Understanding the core data frame processing capability, functionalities, and key differences is critical to effectively configuring access and trunk switch ports in your network switch ports. With the fundamental difference between these ports being the number of VLANs they support, network admins should also consider the following key differences.
| Factor | Access port | Trunk port |
|---|---|---|
| Device connectivity |
|
|
| Configuration |
|
|
| Troubleshooting | Less complex, since access ports only affect a single VLAN. | Difficult, since trunk ports extend support for and affect multiple VLANs. |
| Layer 2 Vs. Layer 3 switching | Used in Layer 2 switching since they do not offer cross subnet data transfer. However, they still can be used in conjunction with Layer 3 switches for providing Layer 2 connectivity to devices on the same VLAN. | Offering cross IP subnet and VLAN data transfers, trunk ports can be used in both Layer 2 and Layer 3 switching. |
| Spanning Tree Protocol (STP) | Configured network STP implementation is supported on a per-VLAN basis. | Configured network STP is implementation is supported on a per-port basis. |
| Security | Offers better security and communication isolation, since access ports are typically configured with port security features, such as MAC address filtering and 802.1X authentication. Also, access ports reduce the chances for a rogue attacker to penetrate the network. | Since it enables communication between multiple VLANs with different security reinforcements, a trunk ports is comparatively less secure. |
| Broadcast domain | Supports only a single broadcast domain. | Supports multiple broadcast domains. |
When choosing between access ports and trunk ports, along with understanding the core differences, it's also important to consider the specific requirements of the devices being connected and the overall network hierarchy.
Here are a few use case examples of when to use which switch port type:
ManageEngine OpUtils is a powerful switch port mapping and management software that provides a comprehensive set of tools for network administrators to manage their access and trunk switch ports with ease. Here are some feature highlights of OpUtils' reliable switch port mapping capabilities:
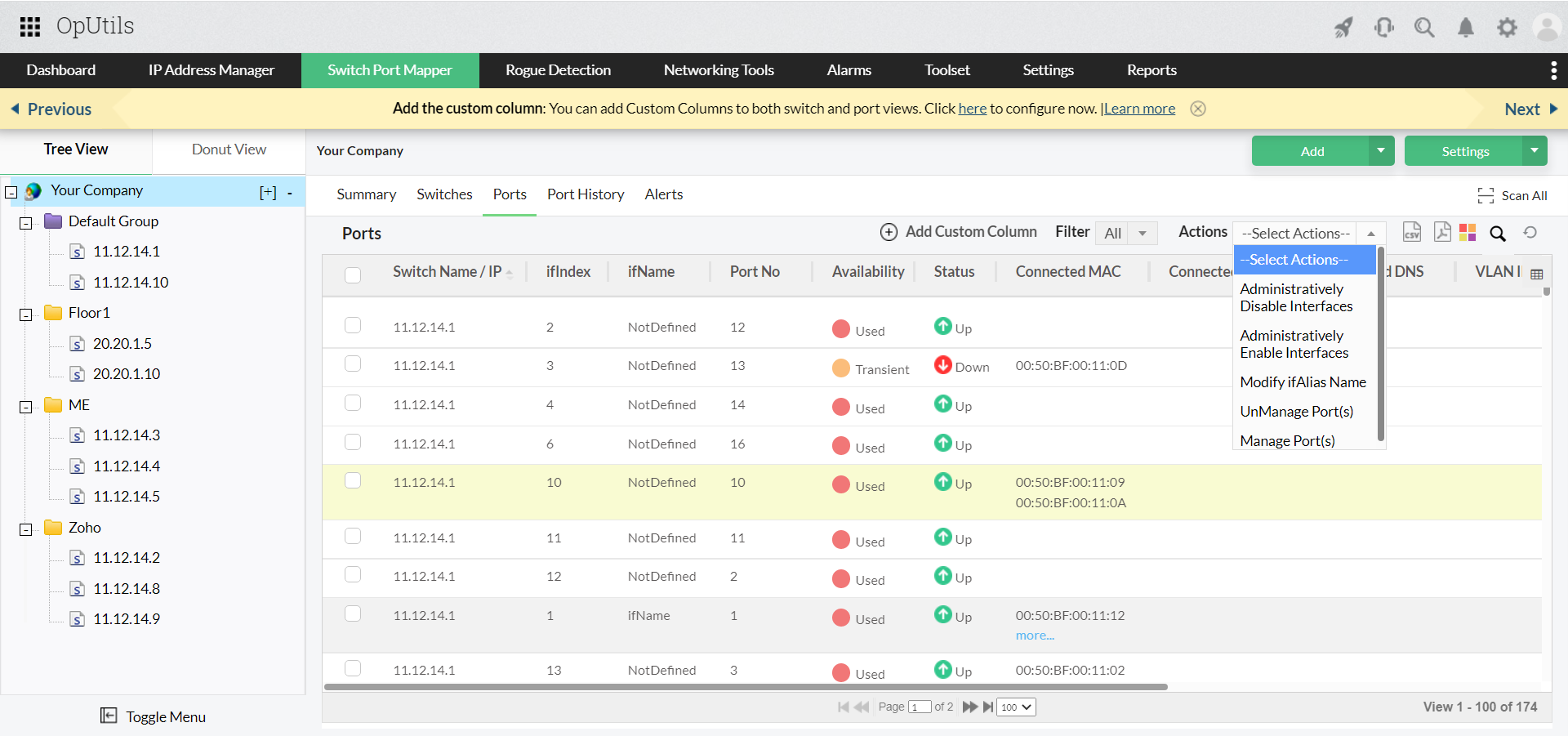
Overall, OpUtils is a reliable choice for switch port mapping and management, providing network administrators with accurate, up-to-date, and customizable information about their network, while also providing a user-friendly interface and seamless deployment with no additional requirements.
So why wait? Download a free, 30-day trial of OpUtils or schedule a personalized live demo with one of our product experts.