- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Construct Crime Scenes to Find Root Cause of Security Breach
Most often companies fail to track down the network intruder who initiated the network breach. It is impossible to protect your network against every attack in spite of taking the best precautions to mitigate the attacks from happening. All attackers leave traces and your event log data and syslog data is the only thing that can help you identify the cause of the breach and even narrow down to tell you who initiated the breach. Log data forensics analysis report can be used as evidence in the court of law.
Your network infrastructure comprising of network devices such as routers, switches, firewalls, servers, etc. generate event log data and syslog data every time an activity occurs on your network. Event log data and system log data activity records are like digital fingerprints left by everyone who accessed the network devices and applications. These digital fingerprints can tell you at what time the network activity was initiated, what happened after that and who initiated that activity. These digital fingerprints will help you in constructing the entire crime scene.
Doing forensics manually on your event log data and syslog data without proper log forensics tools is painful and time consuming. Also, you need to ensure that the log data is kept secure and tamper proof for accurate log forensic analysis.
EventLog Analyzer for Log Forensics
EventLog Analyzer allows you to centrally collect, archive, search, analyze and correlate machine generated logs obtained from heterogeneous systems, network devices and applications, and generates forensic reports (like user activity reports, system audit reports, regulatory compliance reports, etc...)
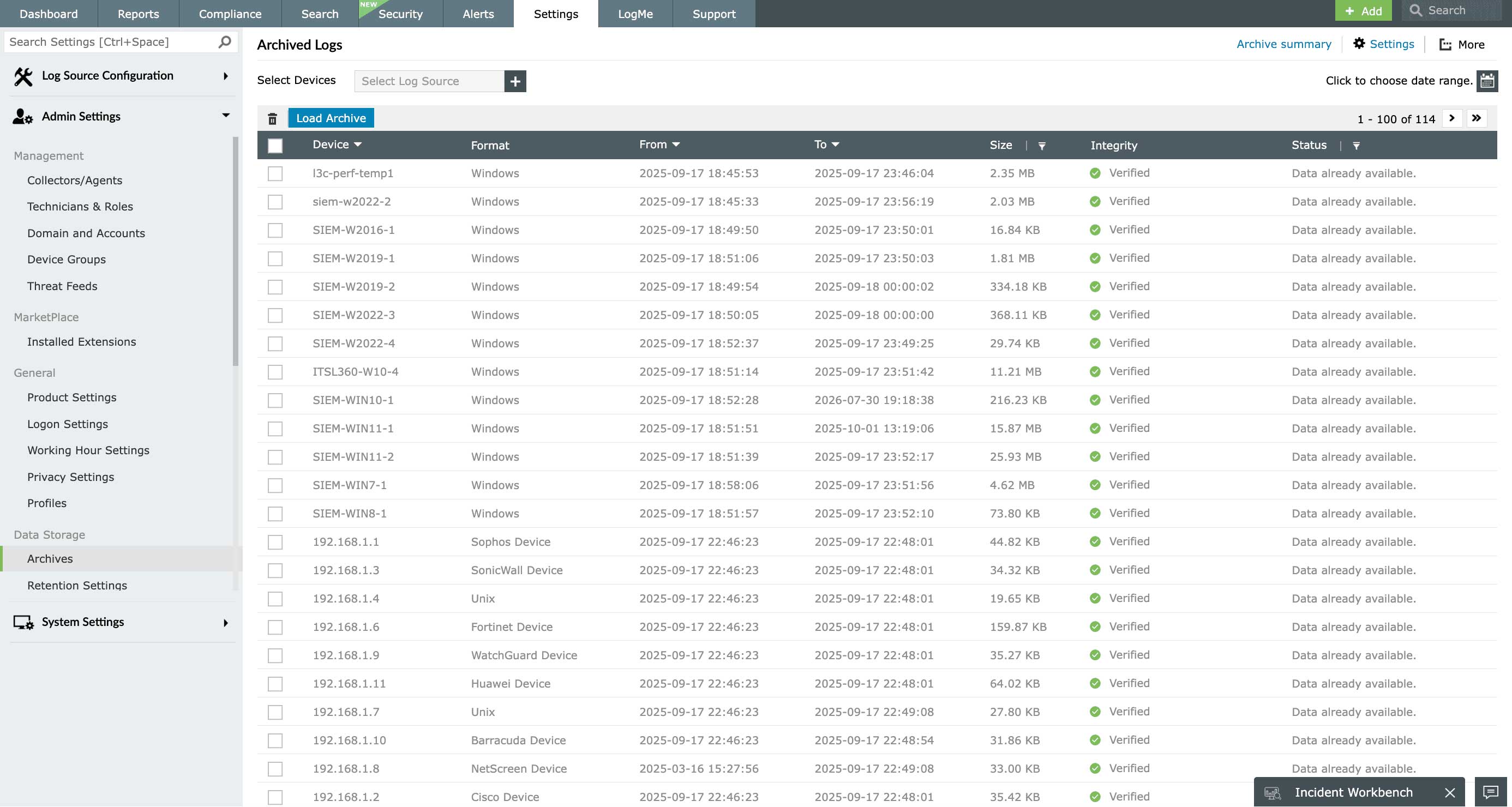
This log analytics and compliance reporting software helps you conduct network forensics on these collected logs and detect network or system anomalies. These machine generated event logs and syslogs are archived, for future forensic analysis, and also encrypted to ensure that the collected system logs are not tampered with and are secure. You can drill down to the raw log events and do a root cause analysis within minutes.
Forensic Analysis using Log Search
EventLog Analyzer makes forensic investigation very easy by allowing you to use its powerful log search engine to search on both the raw and formatted logs and instantly generate forensic reports based on the search results. This log forensics software enables network administrators to search the raw logs to pinpoint the exact log entry which caused the security activity, find the exact time at which the corresponding security event had happened, who initiated the activity and also, the location from where the activity originated.
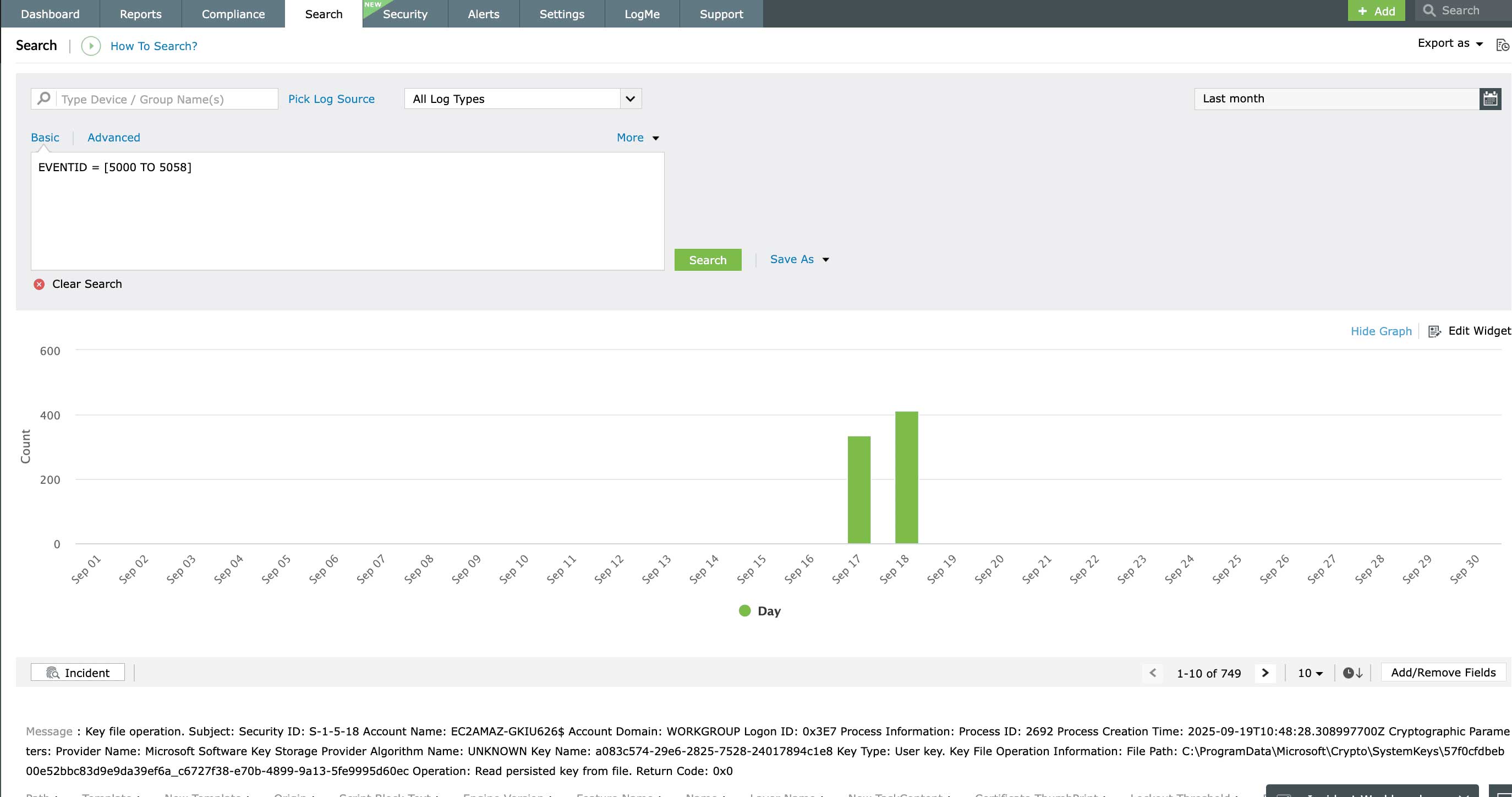
This search feature in EventLog Analyzer will help you to quickly track down the network intruder and is quite useful to law enforcing authorities for forensic analysis. Archived logs can be imported and security incident mining can be carried out by searching the raw logs. This makes forensic investigation easy, which is otherwise a task with huge manually effort.
Forensic analysis using correlation reports
EventLog Analyzer takes forensic analysis a step further with its powerful correlation module. The aggregated incident reports help you conduct forensic investigations on attack attempts or on-going attacks. These reports provide detailed timelines of the suspicious incidents and review the activities related to the device and user accounts involved, thus allowing you to backtrack the incidents in seconds.
Other features
SIEM
EventLog Analyzer offers log management, file integrity monitoring, and real-time event correlation capabilities in a single console that help meeting SIEM needs, combat security attacks, and prevent data breaches.
IT Compliance Management
Comply with the stringent requirements of regulatory mandates viz., PCI DSS, FISMA, HIPAA, and more with predefined reports & alerts. Customize existing reports or build new reports to meet internal security needs.
Windows event log monitoring
Analyze event log data to detect security events such as file/folder changes, registry changes, and more. Study DDoS, Flood, Syn, and Spoof attacks in detail with predefined reports.
Syslog server management
EventLog Analyzer collects and analyzes log data from Linux/Unix servers to provide on-the-fly reports that help detecting suspicious behaviors, anomalous syslog activities, and more.
IIS log monitoring
Centrally monitor & audit IIS web server logs. Secure IIS servers by detecting anomalous events with instant email/SMS alerts. Get predefined reports on server errors and attacks.
Privileged user monitoring
Monitor and track privileged user activities to meet PUMA requirements. Get out-of-the-box reports on critical activities such as logon failures, reason for logon failure, and more.
Need Features? Tell Us
If you want to see additional features implemented in EventLog Analyzer, we would love to hear. Click here to continue











