- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
What is a syslog server?
Understanding syslog servers
The system logging protocol, or the syslog protocol, is a standard message format used by network devices, operating systems like Windows or Linux, and applications to send their event logs to a central location. A syslog server is a centralized log management system that collects, analyzes, and archives logs that are generated using the syslog protocol. Using the standardized syslog protocol (RFC 5424) and the widely used legacy RSC 3164, syslog servers act as a central repository where all network devices, servers, and applications send their event data.
Key components of a syslog server
- Syslog listener: Continuously listens to network ports and aggregates incoming log messages.
- Message parser: Breaks down and normalizes each log into its components (i.e., timestamp, severity, facility, and message).
- Storage engine: Efficiently stores millions of log entries with compression and indexing.
- Analysis engine: Enables searching, filtering, and correlation of syslog data.
- Alerting system: Triggers notifications based on predefined rules and thresholds.
How EventLog Analyzer can function as a syslog server
EventLog Analyzer is equipped with a robust syslog listener, built-in parser, and analytical capabilities that automatically listens and centrally collects syslog messages and SNMP traps in the IT environment through TCP and UDP ports.
Seamlessly receive and analyze syslogs from a wide array of devices, including Windows servers and workstations, Linux systems, routers, firewalls, switches, and various applications. Leverage real-time monitoring, security threat detection, compliance reporting, and efficient troubleshooting with a single comprehensive view of all network and system activity.
Free for up to five log sources.
Why organizations need syslog servers
Syslog servers are indispensable for several critical reasons:
Centralized visibility
Syslog servers provide a single console to access all syslog data, offering a holistic view of all applications, devices, servers, and endpoints in the IT environment. When centrally stored, gaining deeper visibility by correlating logs from different sources becomes easier.
EventLog Analyzer's centralized loggingSecurity monitoring and threat detection
Syslog servers such as EventLog Analyzer provide real-time visibility into security events across IT infrastructure. By correlating logs from firewalls, IDS and IPS solutions, and servers, admins can detect attack patterns and respond to threats before they cause damage.
EventLog Analyzer's security monitoringCompliance requirements
Regulatory standards like HIPAA, the PCI DSS, and the GDPR mandate log retention and monitoring. A syslog server automates the archiving of logs with proper timestamps and maintains audit trails required for compliance audits.
EventLog Analyzer's compliance managementEfficient troubleshooting
Instead of logging in to dozens of individual devices to check logs, administrators can diagnose issues from a single interface. This dramatically reduces mean time to resolution (MTTR) and improves operational efficiency.
EventLog Analyzer: Your complete syslog server solution
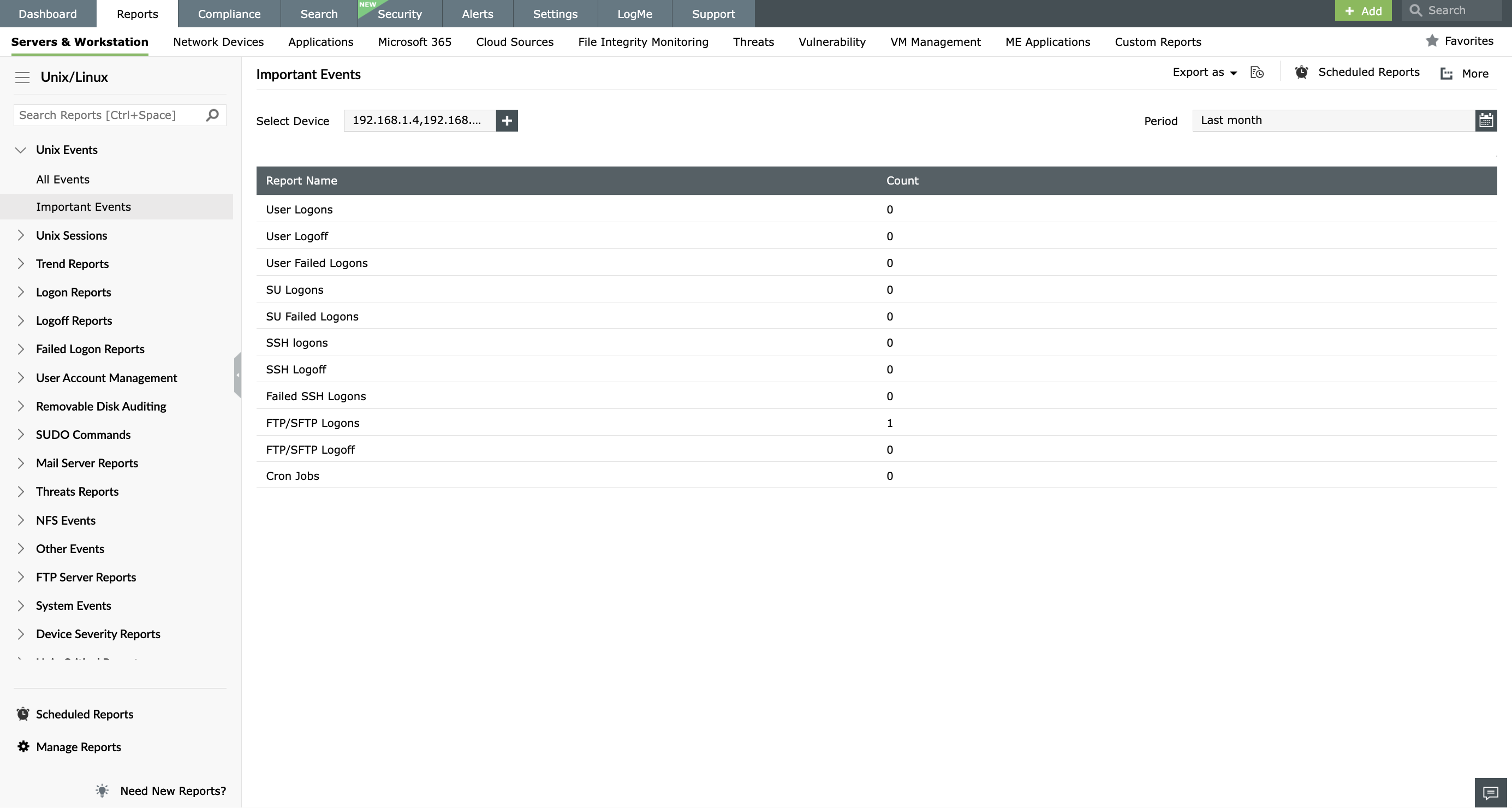
Syslog device auditing: Track events across all syslog devices with predefined security audit reports.
Learn moreSNMP monitoring: Collect and analyze SNMP traps from devices to troubleshoot errors.
Learn moreLinux syslog server: Centrally collect syslogs from Linux and Unix systems for effective auditing and compliance management.
Learn moreSyslog management: Ensure centralized and secured archival of syslogs for forensic analysis and IT compliance.
Learn moreWindows event log management: Manage and monitor Windows event logs from servers and workstations.
Learn moreSecured syslog archival: Ensure encrypted syslog transmission and secured storage for effective forensic analysis.
Learn moreHave less than five syslog devices to monitor?
How EventLog Analyzer functions as your Windows syslog server
Running a syslog server on Windows offers a convenient, efficient, and cost-effective solution for organizations that primarily use Windows-based systems. For organizations predominantly utilizing a Windows infrastructure, EventLog Analyzer offers a convenient solution for centralizing and analyzing syslog data from network devices. By eliminating the need for a separate Linux system, EventLog Analyzer streamlines the process of collecting and interpreting syslog information. Here’s how it functions to secure and manage your network logs:
Real-time listening
EventLog Analyzer actively listens to devices for syslogs once installed on a Windows system.
Comprehensive monitoring
It uses TCP and UDP protocols to receive syslogs in real-time and offers syslog monitoring through reports, alerts, and dashboards.
Multi-log support
Also supports Windows event logs and other application logs (supports over 750+ log sources) to ensure security and compliance.
Flexible access
Accessible through a web console from anywhere, and offers correlation and threat analytics capability.
Key syslog server capabilities of EventLog Analyzer
EventLog Analyzer offers a built-in syslog server that collects, processes, and analyzes syslog messages from across your network, providing deep insights into security events and network activity.
Centralized syslog management for Windows and Linux
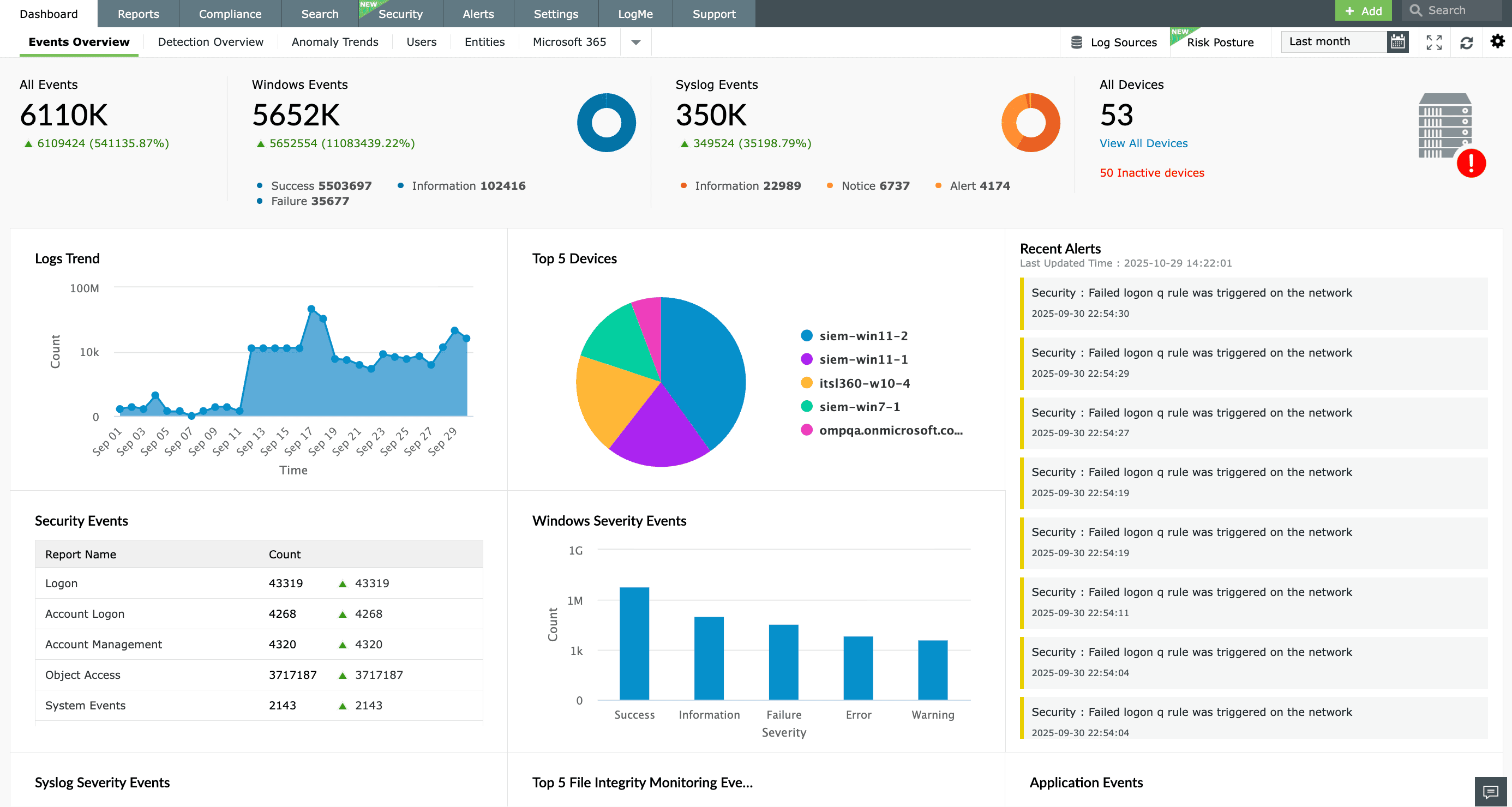
EventLog Analyzer unifies log management across Windows, Linux, and other environments, providing a holistic view of your IT infrastructure:
Windows event logs
Automatically collect, analyze, and manage event logs from Windows servers and workstations. Detect critical events like failed logons, system errors, and security changes.
Linux/Unix logs
Seamlessly gather syslog messages from Linux and Unix systems, including user activities, authentication events, and critical errors. Real-time monitoring enables efficient threat identification and system issue resolution.
Unified platform
Support for 750+ log sources, including applications and network devices, provides a central dashboard for comprehensive log management.
Comprehensive syslog monitoring
EventLog Analyzer provides real-time monitoring and analysis of critical system events to track security incidents, system changes, and potential threats:
User activity monitoring
Track failed logons and unauthorized access attempts across Windows and Linux systems. Also, detect brute-force attacks and credential misuse.
SUDO command auditing
Audit privileged operations and failed attempts on Linux/Unix systems. Identify unauthorized privilege escalations and enforce least privilege policies.
System and application event tracking
Monitor cron jobs, service states, and application logs from web servers and databases to detect system errors and security threats.
Threat detection and severity reporting
Built-in, severity-based categorization and anomaly detection identify potential risks and generate comprehensive reports on system events.
Secure storage and compliance
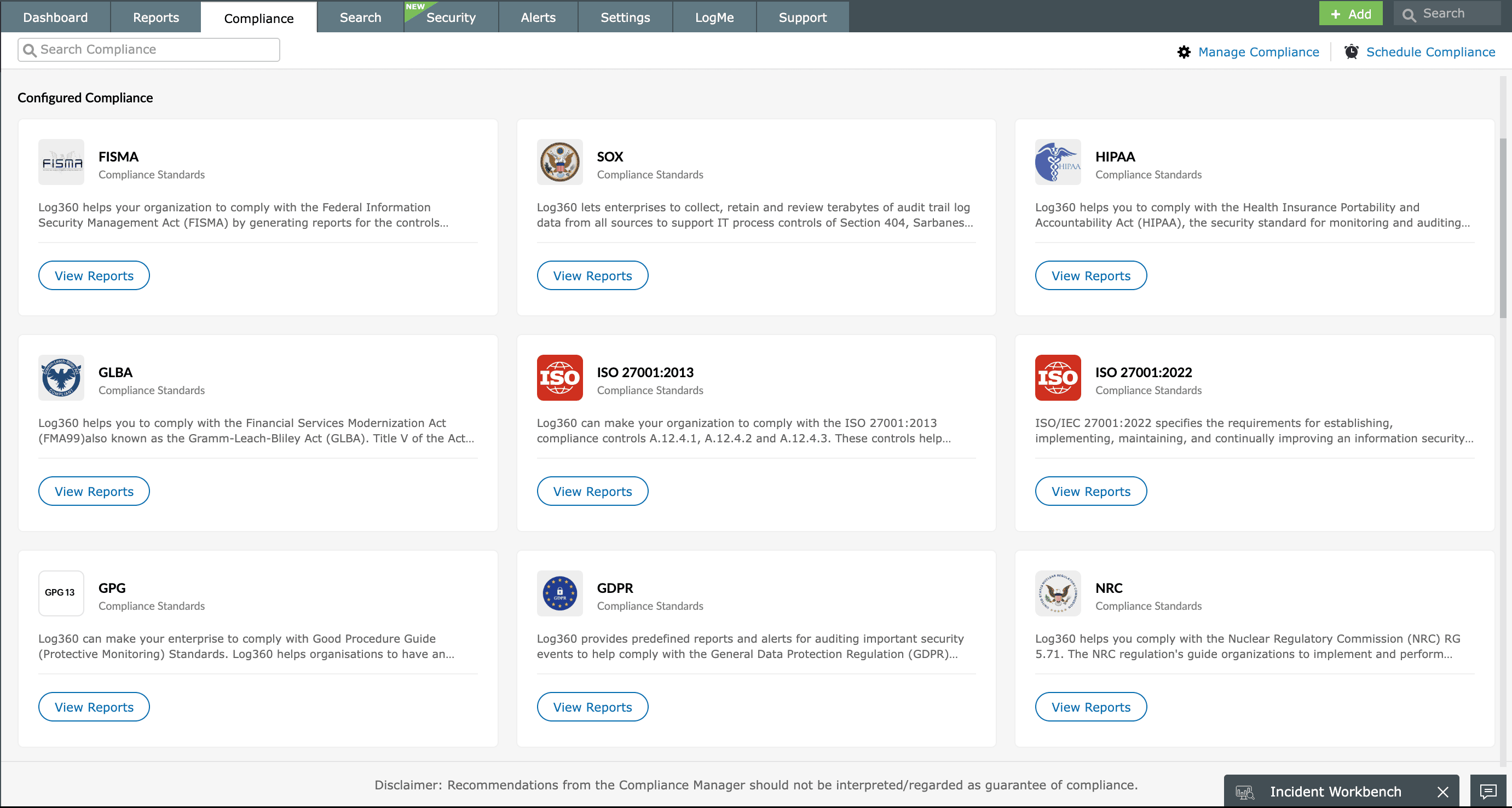
EventLog Analyzer ensures compliance-ready syslog management through secure log handling and comprehensive reporting:
Encrypted syslog transmission
Supports TLS/SSL encryption and certificate-based authentication to ensure secure data transport.
Compliance storage
Archive and compress syslog messages with configurable retention policies to meet compliance mandates.
Compliance reports
Preconfigured reports for PCI DSS, HIPAA, SOX, and GDPR enable quick compliance audits with ready-to-use templates.
Benefits of using EventLog Analyzer as your syslog server
- Centralized log management: Consolidate logs from diverse sources for easier analysis and storage.
- Enhanced security posture: Quickly detect and respond to security threats across your network.
- Streamlined compliance: Simplify audits with ready-to-use compliance reports and templates.
- Improved operational efficiency: Automate log collection, analysis, and reporting processes.
- Cost-effective: Reduce the need for multiple monitoring tools with our all-in-one solution.
Experience EventLog Analyzer with our 30-day trial without feature restrictions
Syslog servers: A comparison
EventLog Analyzer vs. Kiwi Syslog Server
While Kiwi Syslog Server offers basic collection capabilities, EventLog Analyzer provides the features needed for comprehensive security and compliance.
| Feature | Kiwi syslog server | EventLog Analyzer |
|---|---|---|
| Windows event log support | Requires manual log forwarding | Automated, agentless collection |
| Real-time correlation | Keyword-based filtering | Automated attack pattern detection |
| Compliance reporting | Manual reporting | Over 40 prebuilt reports |
| Threat intelligence | Not included | Built-in threat feeds |
EventLog Analyzer vs. open source (rsyslog/syslog-ng)
Open-source tools are powerful but require significant expertise and ongoing maintenance. EventLog Analyzer provides a GUI-based setup any IT professional can manage, includes built-in analytics that open-source tools lack, and comes with professional support and comprehensive documentation.
Other features
Log analysis
Analyze log data from sources across the network. Detect anomalies; track critical security events; and monitor user behaviors with predefined reports, intuitive dashboards, and instant alerts.
Windows event log monitoring
Analyze event log data to detect security events such as file or folder changes, registry changes, and more. Study DDoS, flood, SYN, and spoof attacks in detail with predefined reports.
Application log analysis
Analyze application log from IIS and Apache web servers, Oracle and Microsoft SQL databases, DHCP Windows and Linux applications, and more. Mitigate application security attacks with reports and real-time alerts.
IT compliance management
Comply with the stringent requirements of regulatory mandates like the PCI DSS, FISMA, and HIPAA with predefined reports and alerts. Customize existing reports or build new reports to meet internal security needs.
Getting started with EventLog Analyzer
Get your free, 30-day trial of EventLog Analyzer
Set up log sources and customize your dashboard
Start gaining insights from your network logs immediately
Frequently asked questions
A syslog server is a centralized log management system that uses the standard syslog protocol to receive event messages from across your IT infrastructure. In this client-server model, network devices, servers, and applications act as clients, sending their logs to the central syslog server. The server's job is to collect these logs—which are formatted using standards like RFC 5424 or RFC 3164—and then parse, store, and analyze them in a centralized location.
Syslog is the original protocol standard for log message transmission. Rsyslog and syslog-ng are modern implementations of syslog daemons with enhanced features. Rsyslog maintains backward compatibility with traditional syslog while adding features like TCP support and database storage. Syslog-ng offers a complete rewrite with advanced filtering and flexible configuration. EventLog Analyzer seamlessly collects logs from all three implementations.
Read about the differences in detail here.
Yes, EventLog Analyzer excels as a Windows syslog server. It runs on Windows Server platforms and collects both Windows event logs and syslog messages from network devices. Unlike traditional syslog servers that require complex configuration on Windows, EventLog Analyzer provides native Windows integration with automatic event log collection.
EventLog Analyzer scales from small businesses to large enterprises. There's no hard limit on device count—the system architecture supports thousands of devices with proper sizing. Licensing is based on device count, allowing you to start small and expand as needed.
EventLog Analyzer supports all major syslog formats, including RFC 3164 (BSD syslog) and RFC 5424 (modern syslog with structured data). The intelligent parser automatically recognizes formats from popular vendors like Cisco, Juniper, Palo Alto, and Fortinet. Custom log parsers can be created for unsupported or proprietary formats.
Logs are stored in an optimized database with automatic compression and indexing. Retention policies can be configured per device type or compliance requirement. Archived logs remain searchable, and automated cleanup prevents database bloat while maintaining compliance.
Yes, EventLog Analyzer can act as a syslog forwarder, forwarding filtered messages to other syslog servers or SIEM systems. This enables integration with existing monitoring tools while benefiting from EventLog Analyzer's collection and analysis capabilities.











